The document discusses the challenges of managing employee mobility and security in today's business environment. As smartphone and mobile device usage increases, IT departments are tasked with managing access to enterprise networks and applications from a variety of mobile platforms. However, mobile devices present unique security risks, such as data breaches from lost or stolen devices, that can result in high costs or regulatory noncompliance for businesses. The document advocates adopting a platform approach to balance mobile access, control, and security.









![key Findings
Conventional Wisdom:
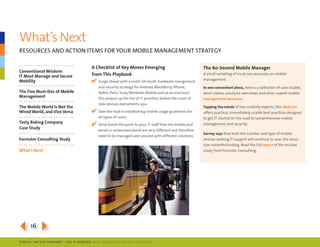
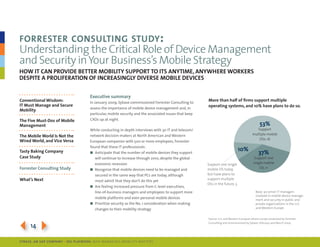
forrester’s study yielded four key findings:
IT Must Manage and Secure
Mobility n despite tightening budgets as a result of the
global economic recession, 28 out of the 30 it
The Five Must-Dos of Mobile professionals interviewed anticipate that the number
Management of mobile devices they support will increase
through 2010.
The Mobile World Is Not the n firms are increasingly embracing more than just one
Wired World, and Vice Versa mobile platform, making it critical that they invest in tools
that can support mobile devices powered by BlackBerry,
Tasty baking Company
Windows mobile, symbian, mac os X and Windows ce.
Case Study
n With the changing workforce, it is feeling intense pressure
from c-level executives, line-of-business managers and
Forrester Consulting Study
employees to support personal devices and applications,
making security a major concern.
What’s Next
n companies are increasingly investing in mobile device
management and security solutions that will help auto-
mate support tasks, streamline the operations of enterprise
mobility and secure data.
This report is from a commissioned study conducted by
Forrester Consulting on behalf of Sybase.
[ ClICk Here For THe FUll STUDy. ]
3154
SybaSe, aN SaP CoMPaNy | I DG Playbook: Why ManagI ng Mob I lIty MatterS](https://image.slidesharecdn.com/whymanagingmobilitymatters-13054947178215-phpapp01-110515163100-phpapp01/85/Why-Managing-Mobility-Matters-15-320.jpg)