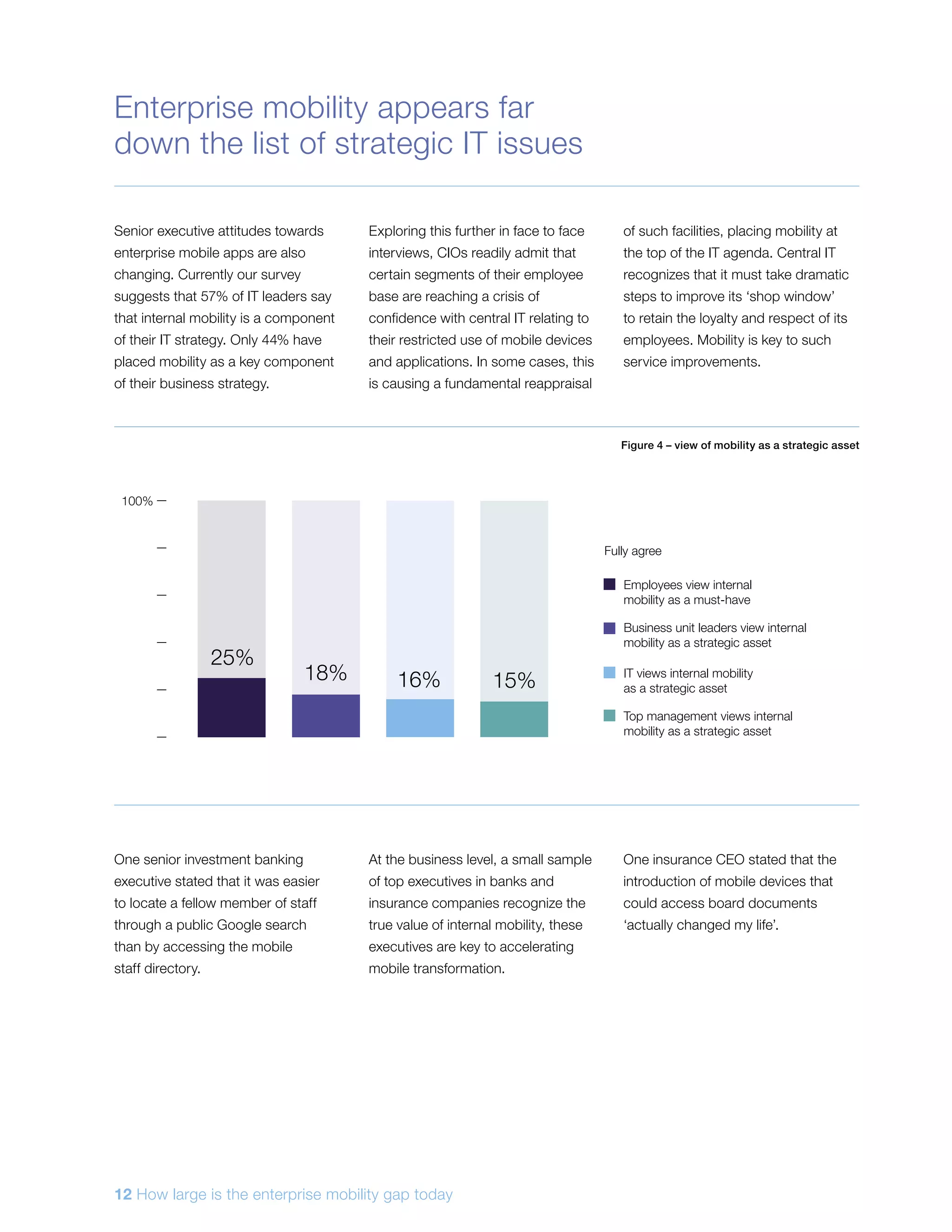
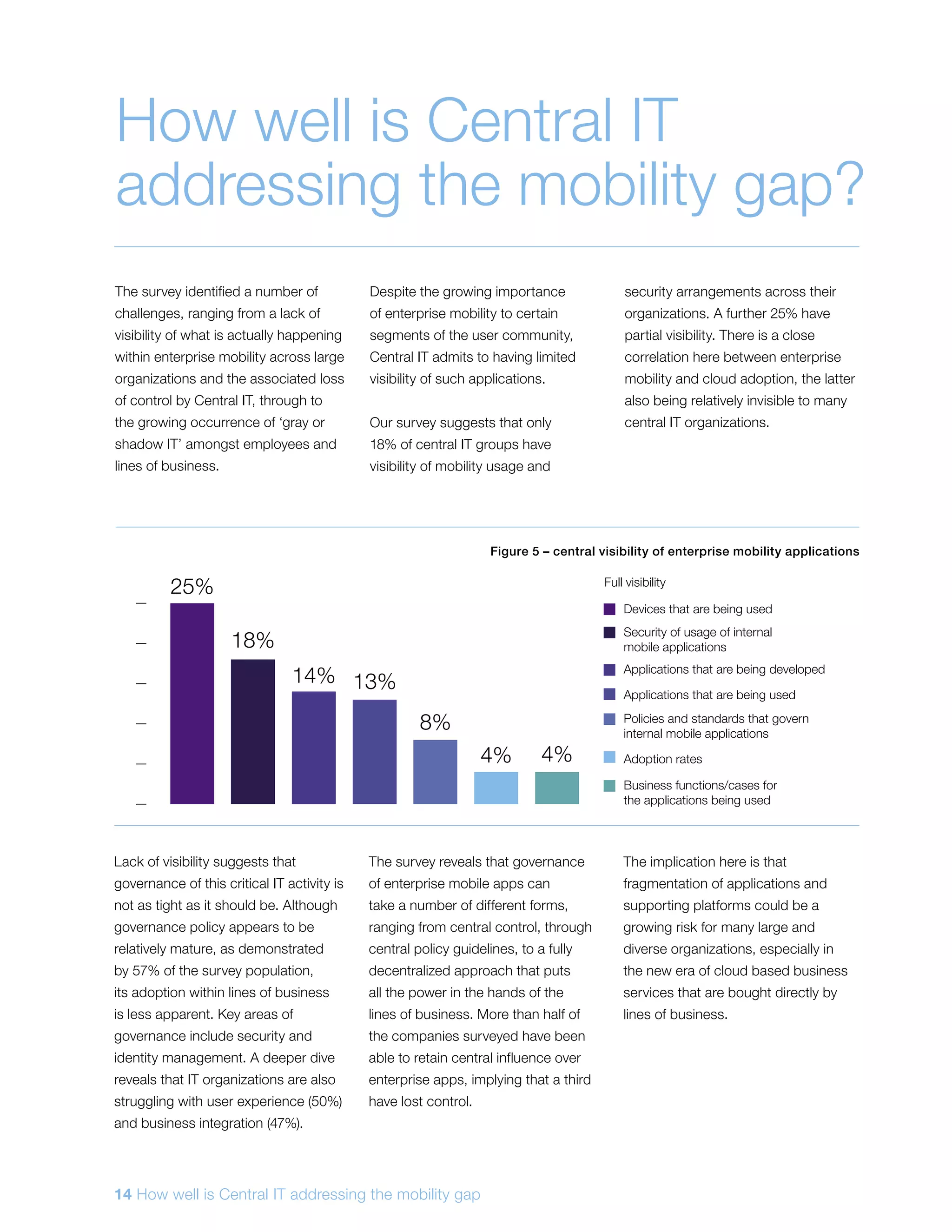
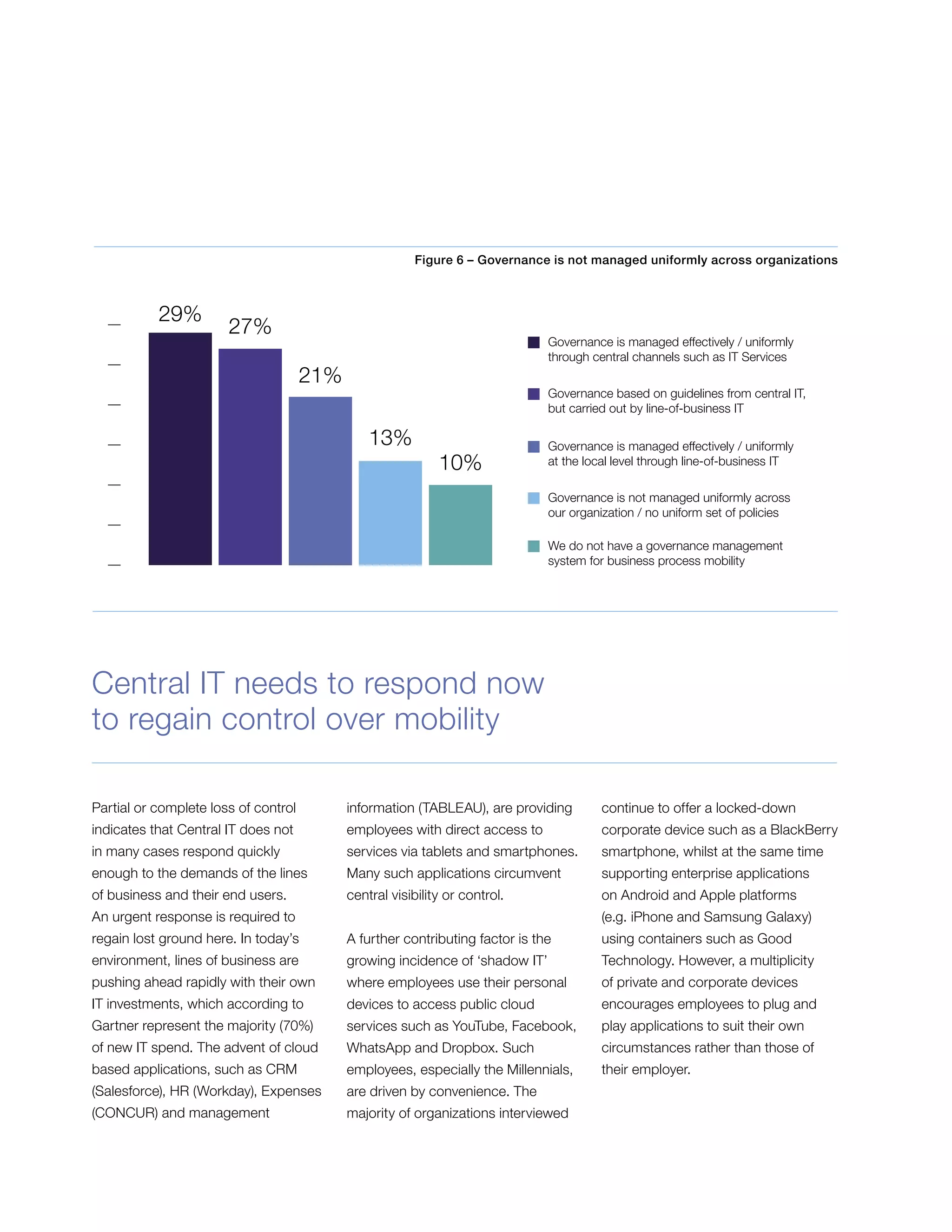
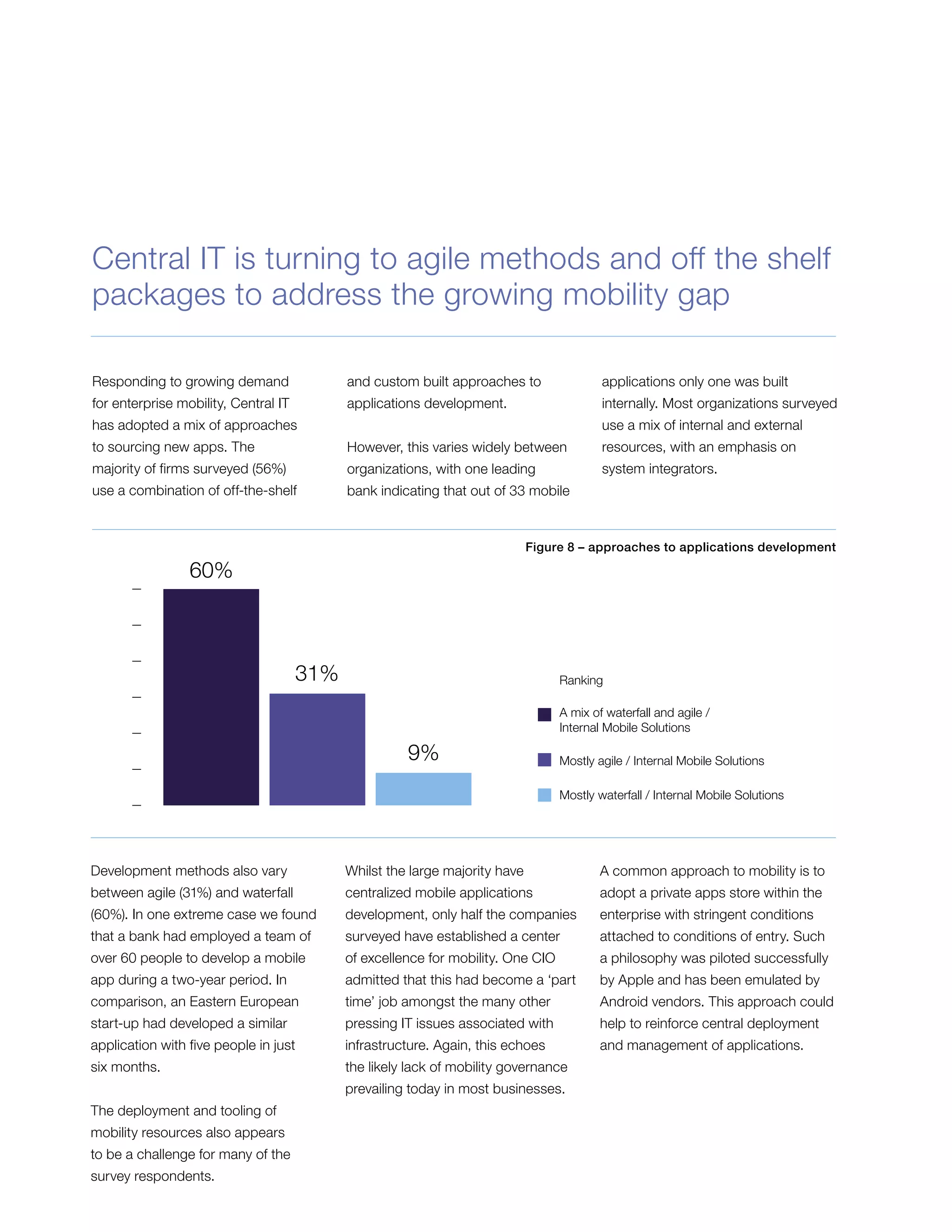
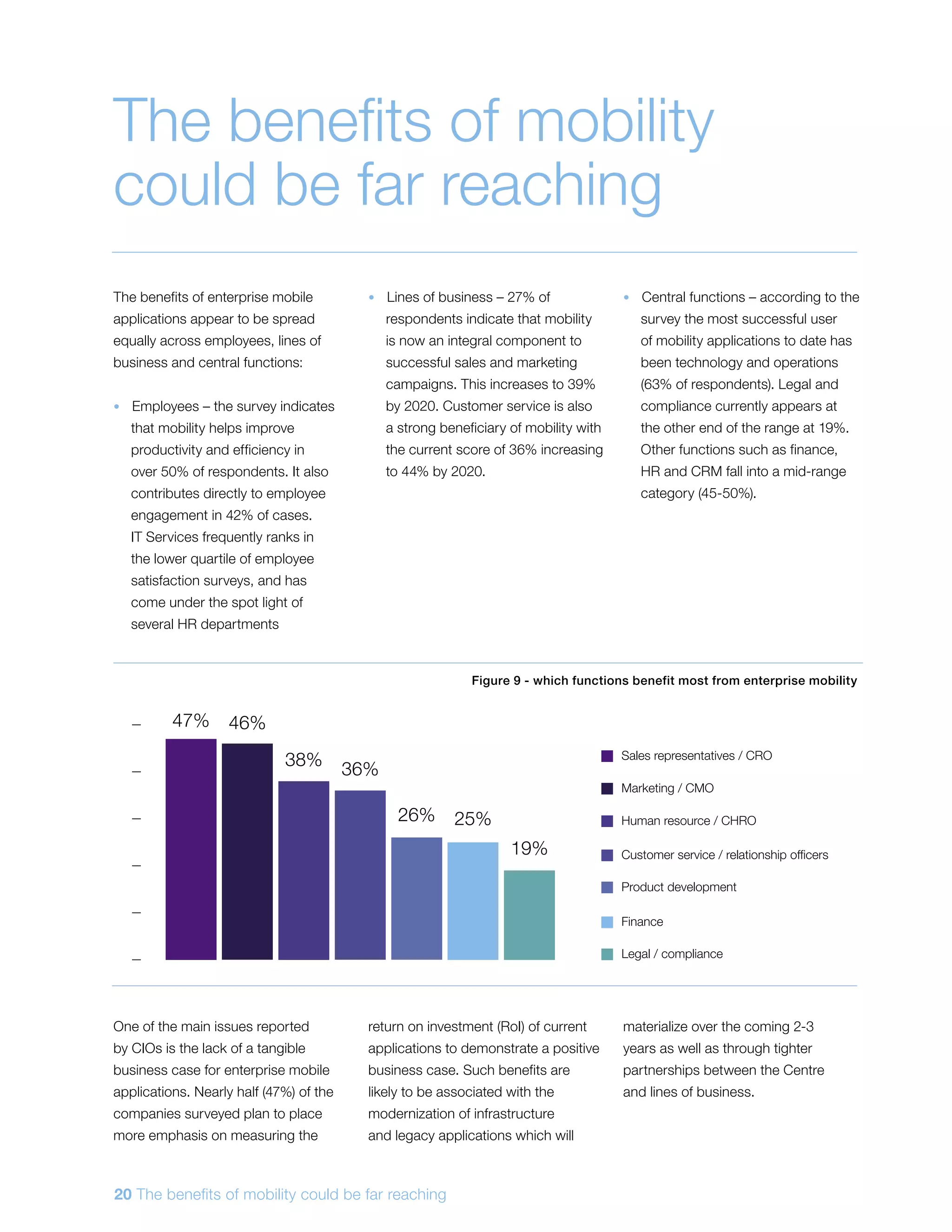
The report highlights a significant enterprise mobility gap between central IT and line-of-business IT, particularly affecting millennial employees who face frustrations with current mobility solutions. Despite the potential benefits of improved productivity and collaboration, enterprise mobile applications are still in their infancy, with only a quarter of employees able to access them, while shadow IT is on the rise due to insufficient support from central IT. The document advocates for a strategic shift toward integrating mobility into corporate IT agendas to enhance employee engagement and operational efficiency.