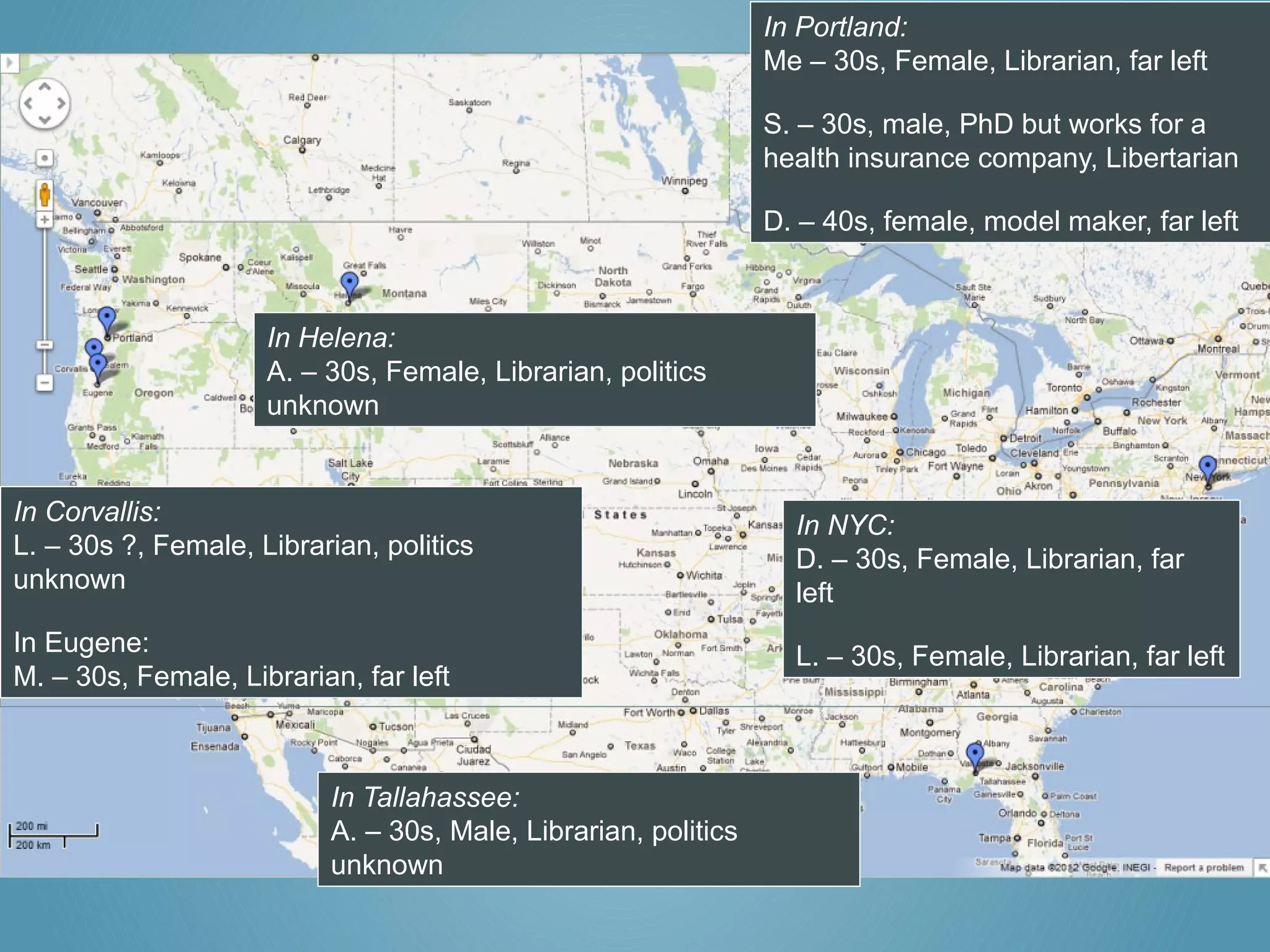
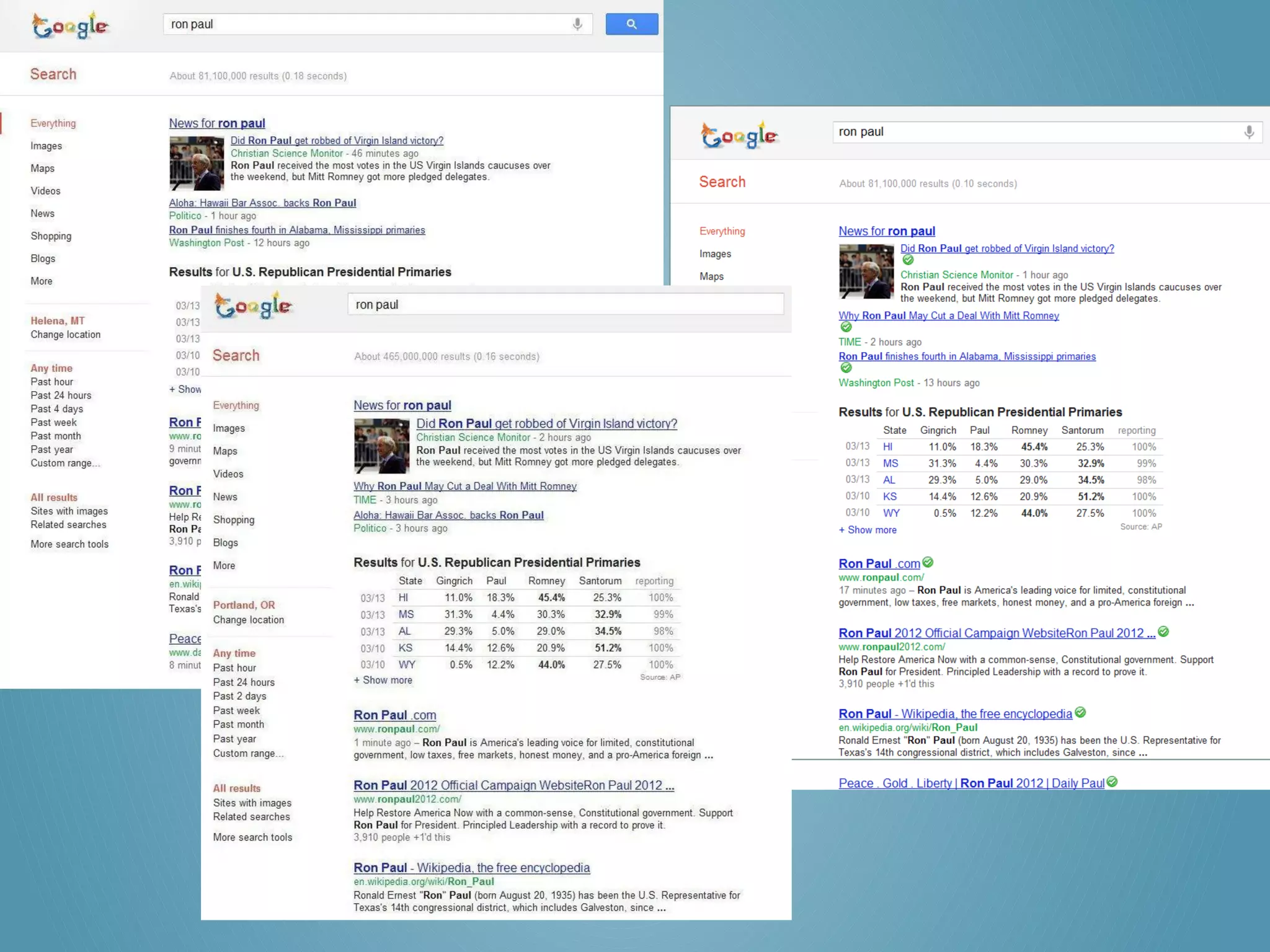
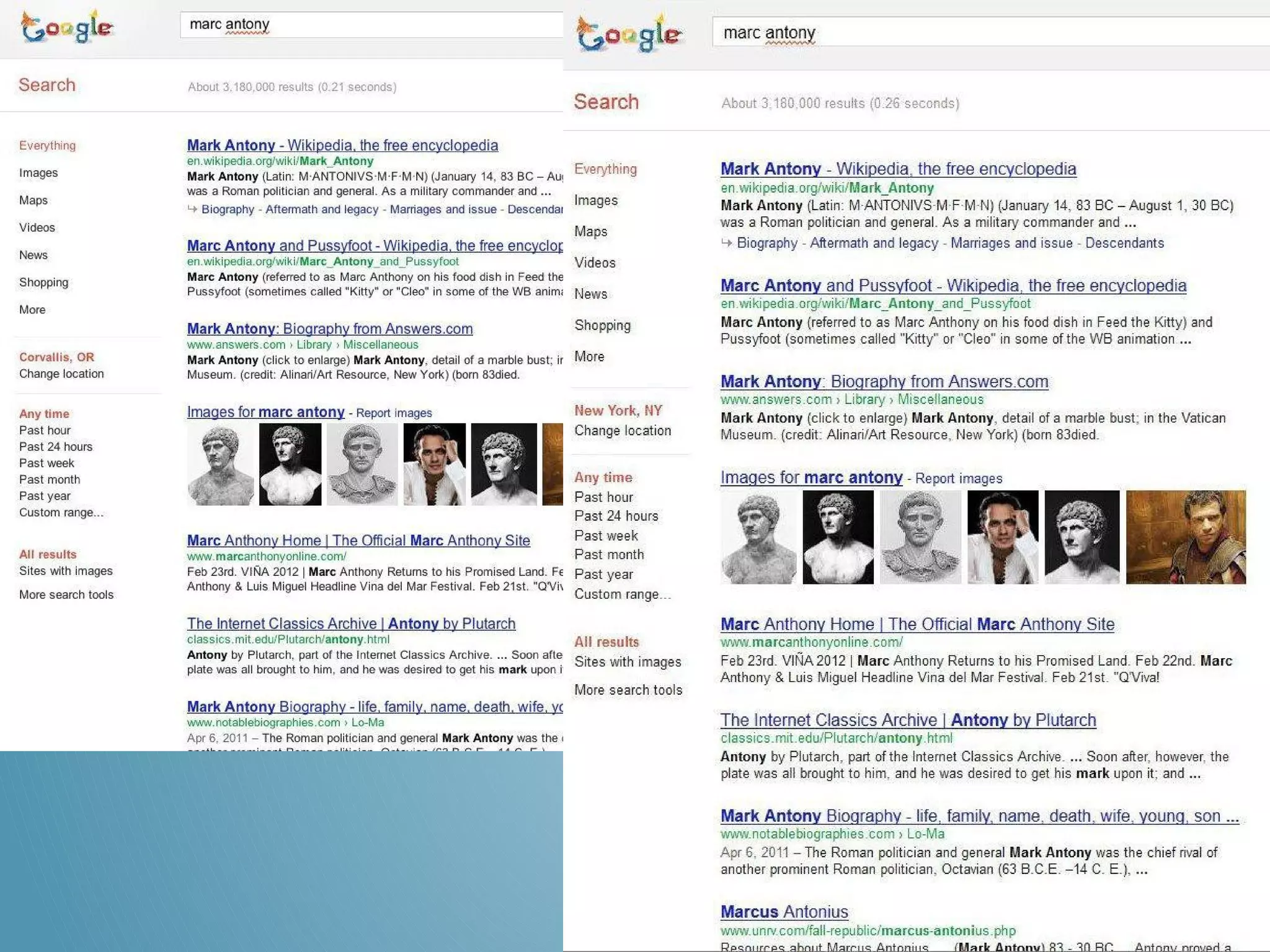
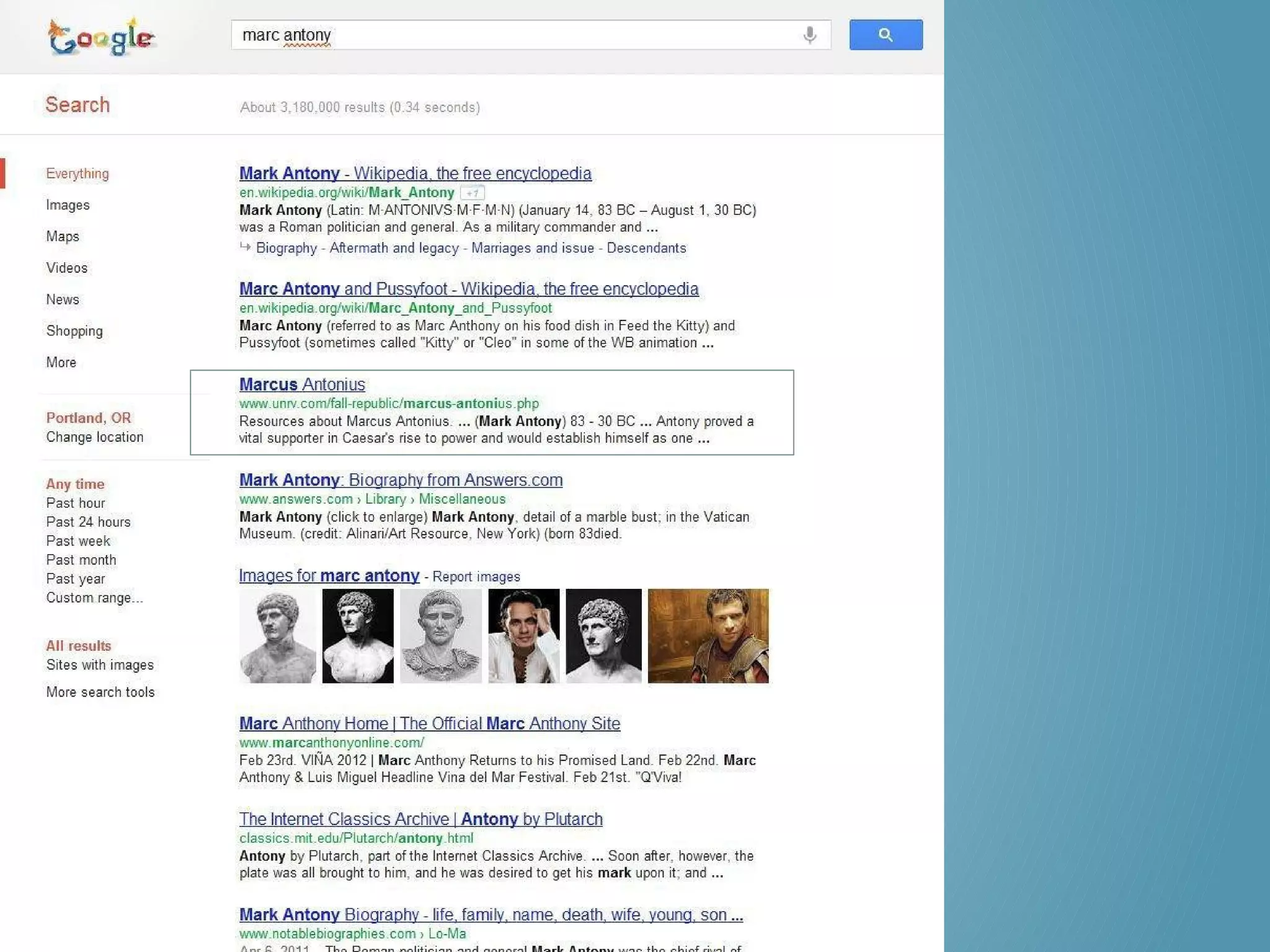
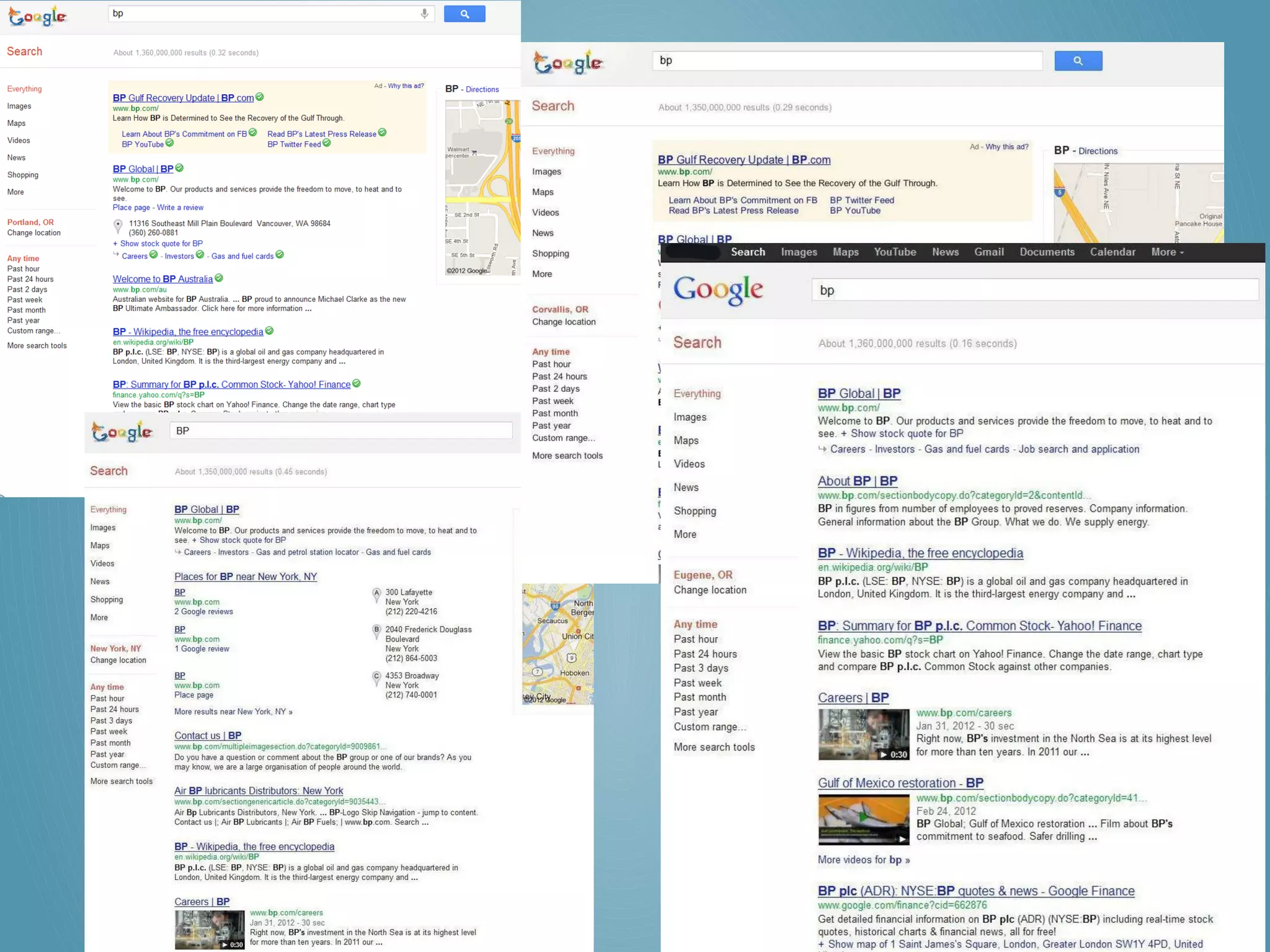
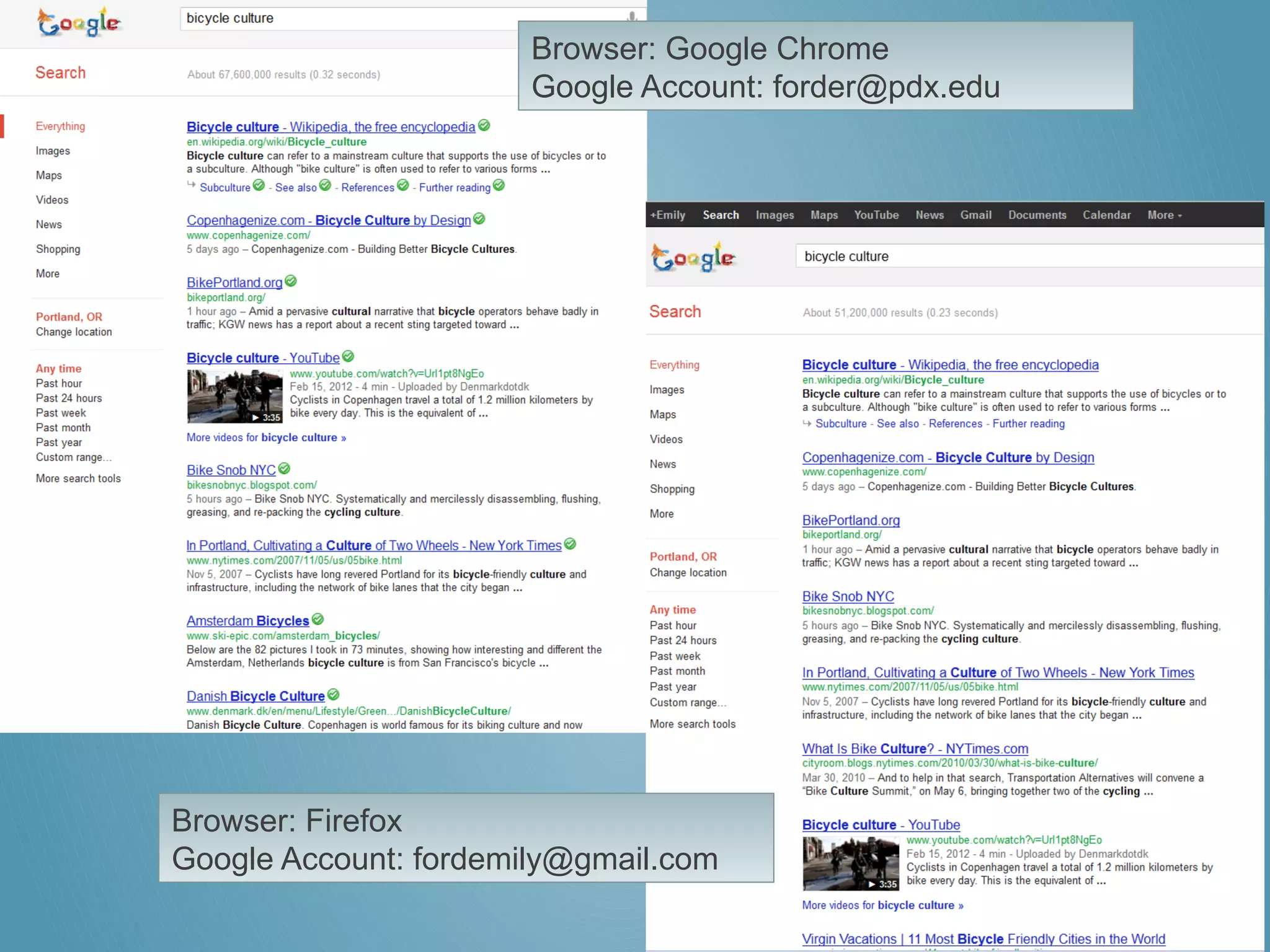
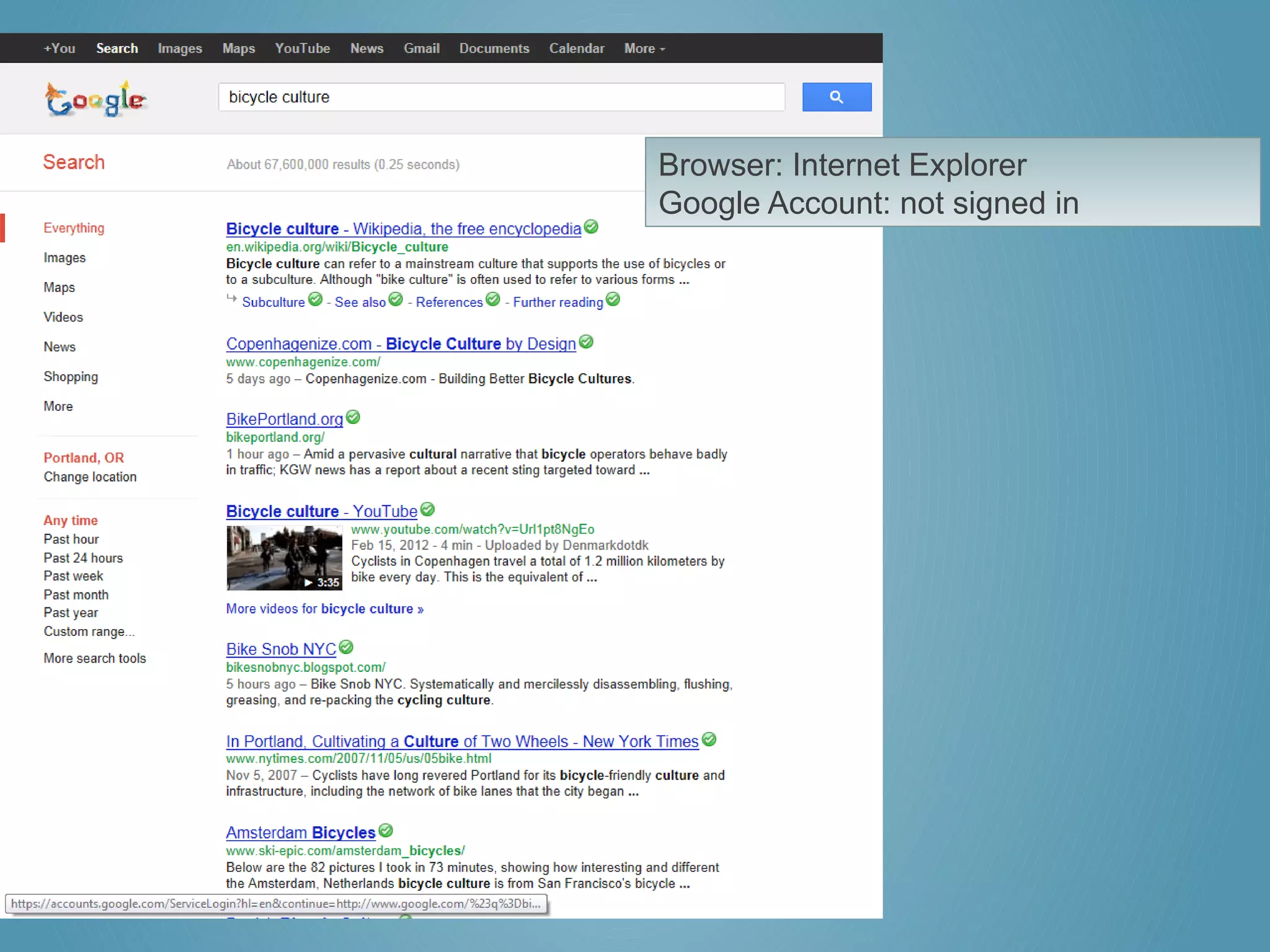
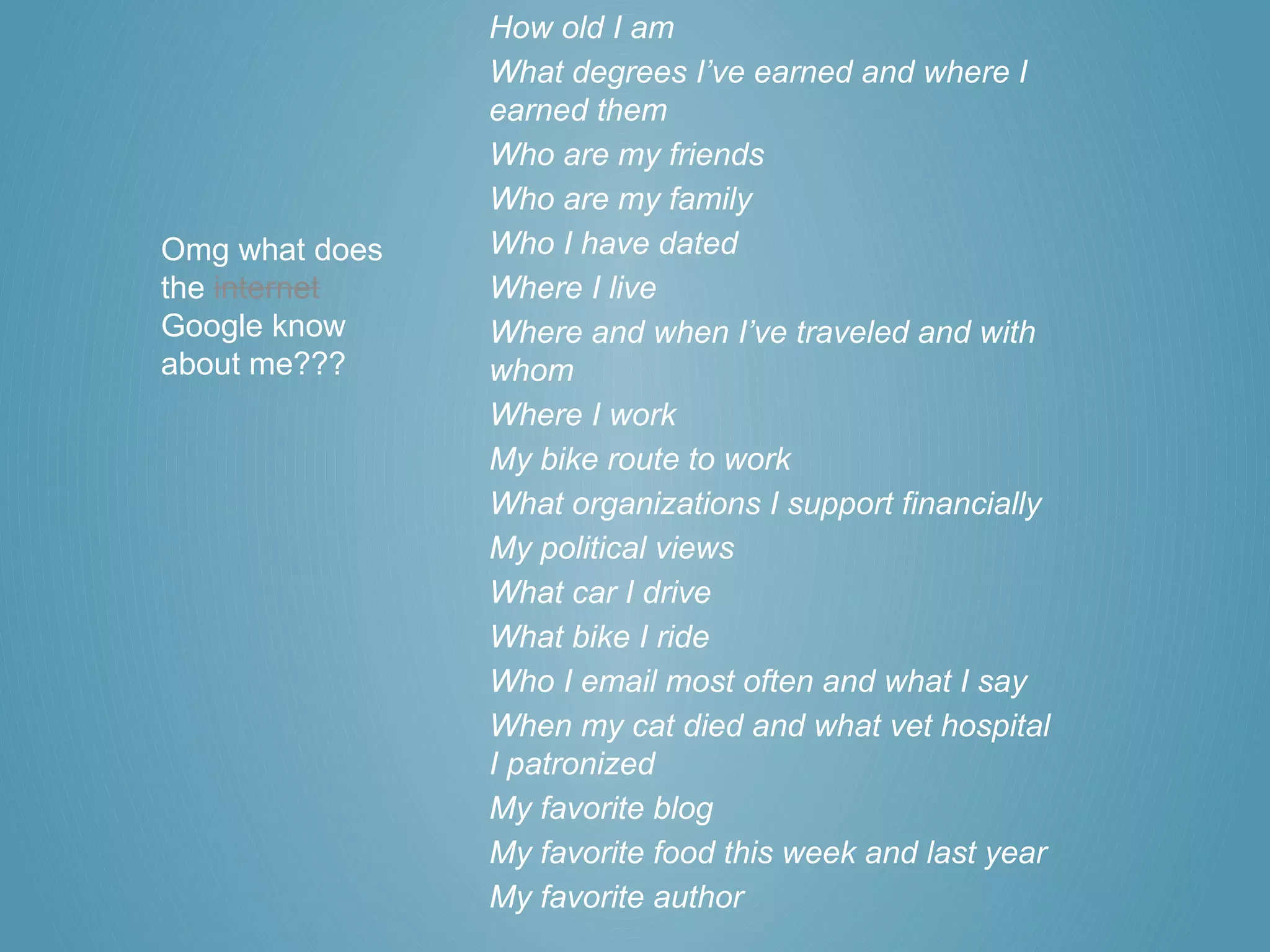
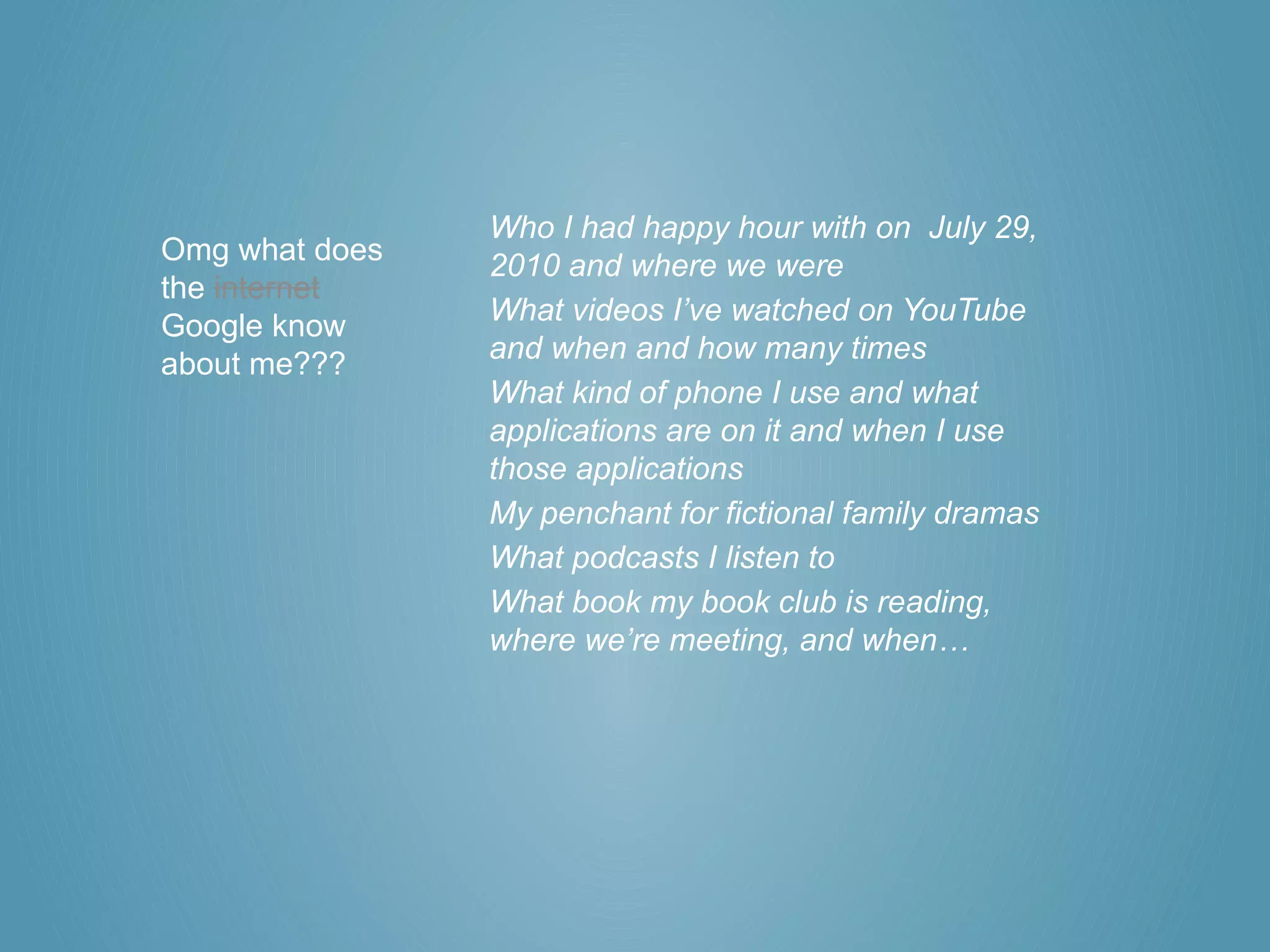
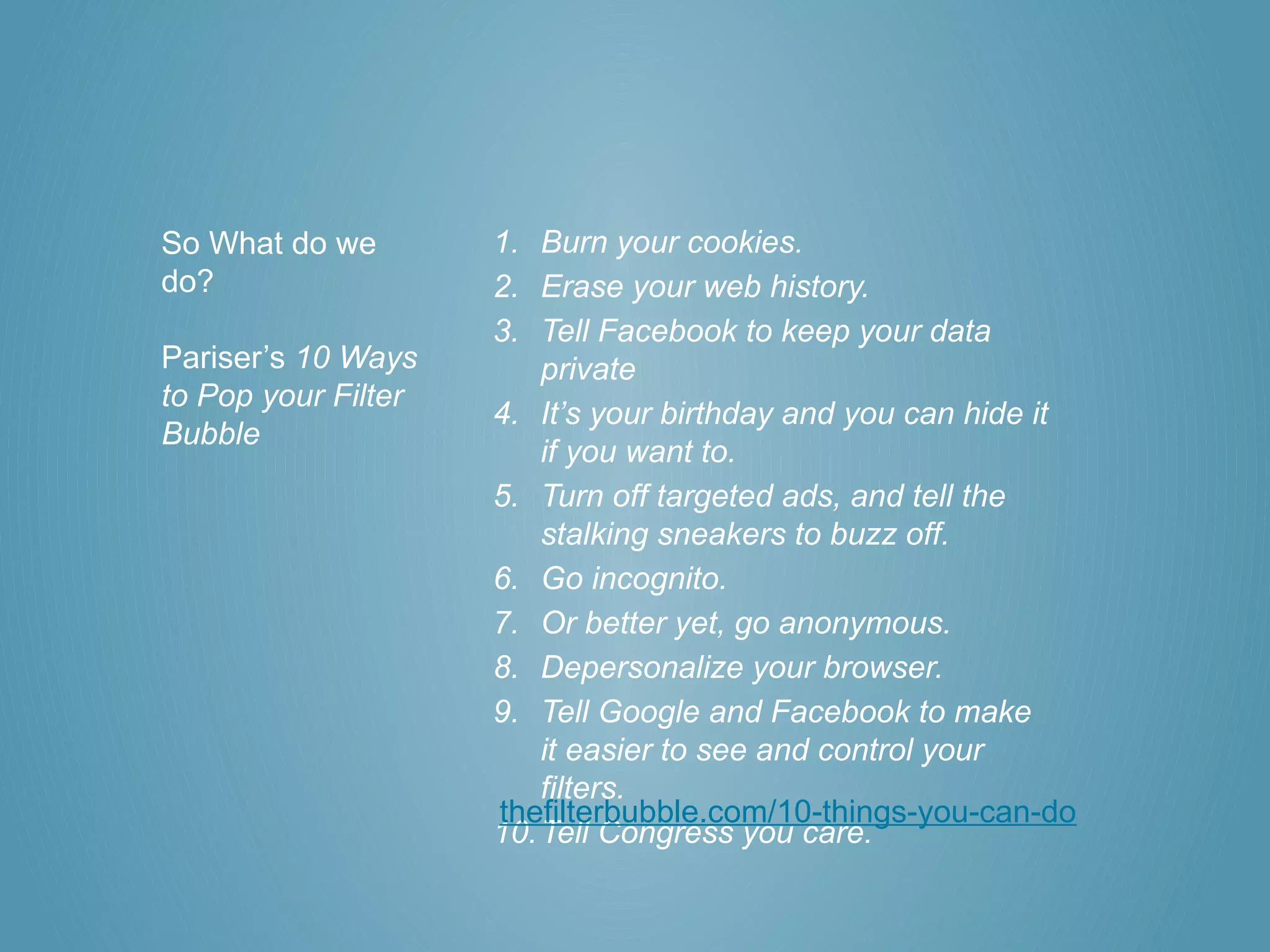
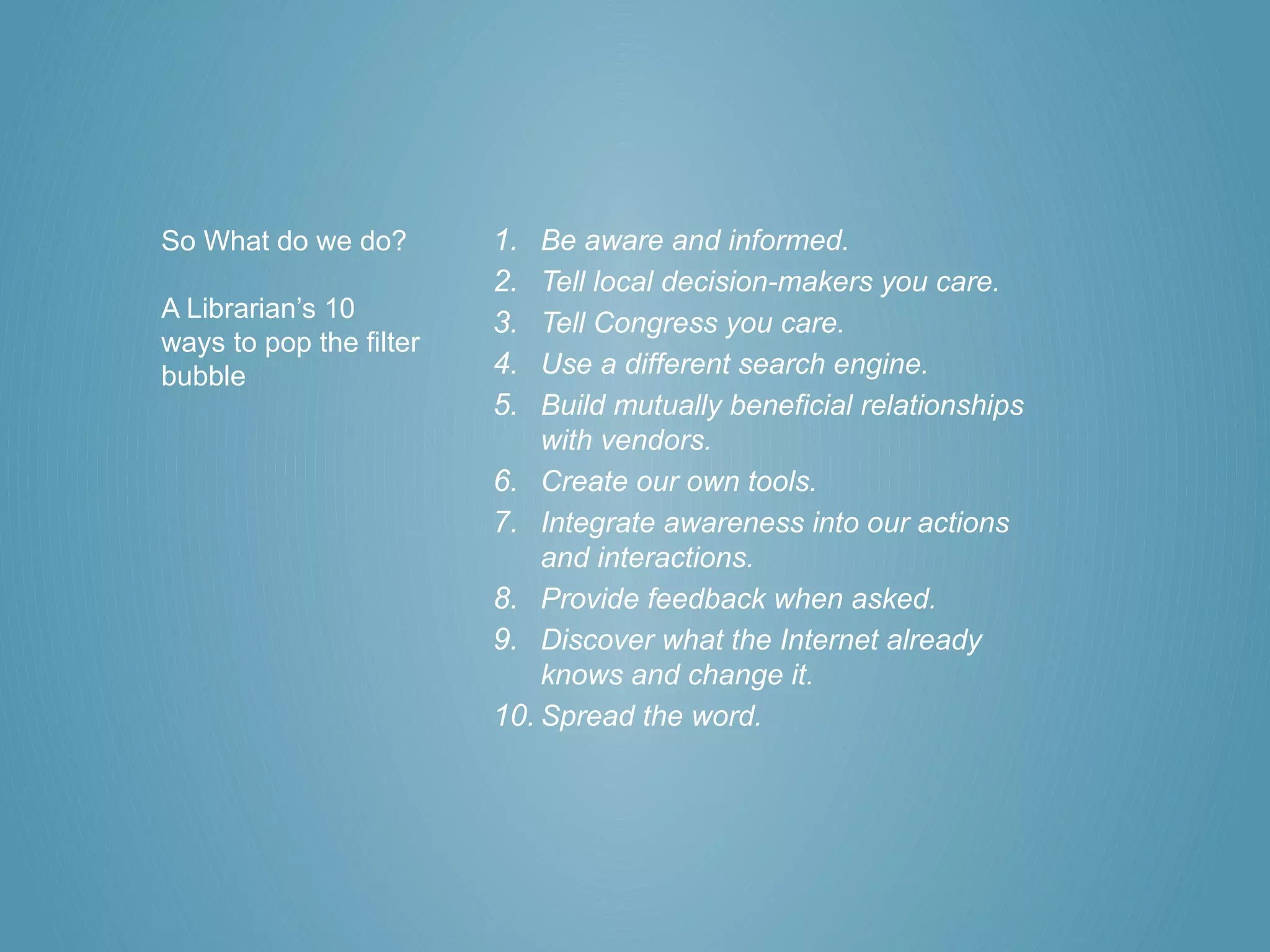
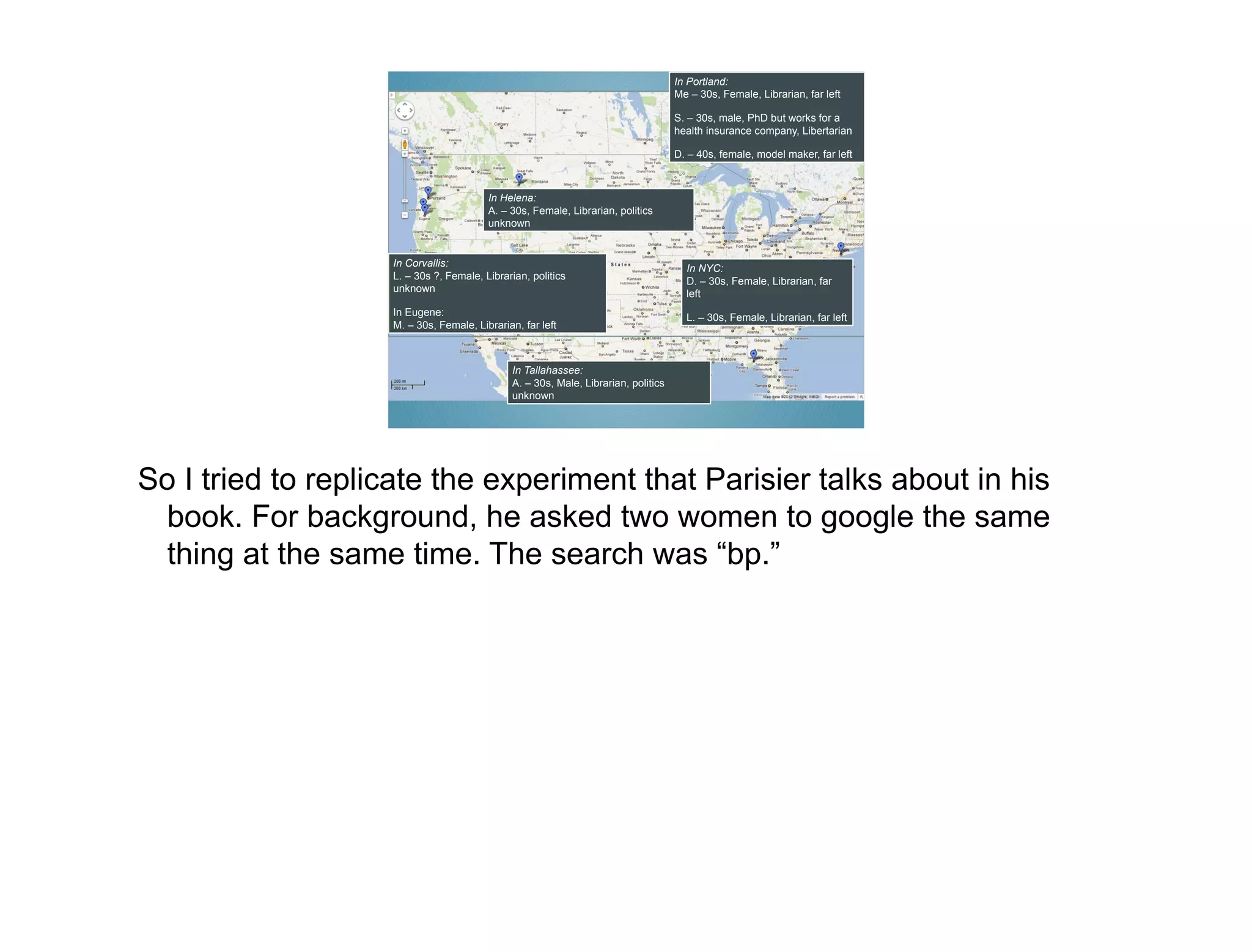
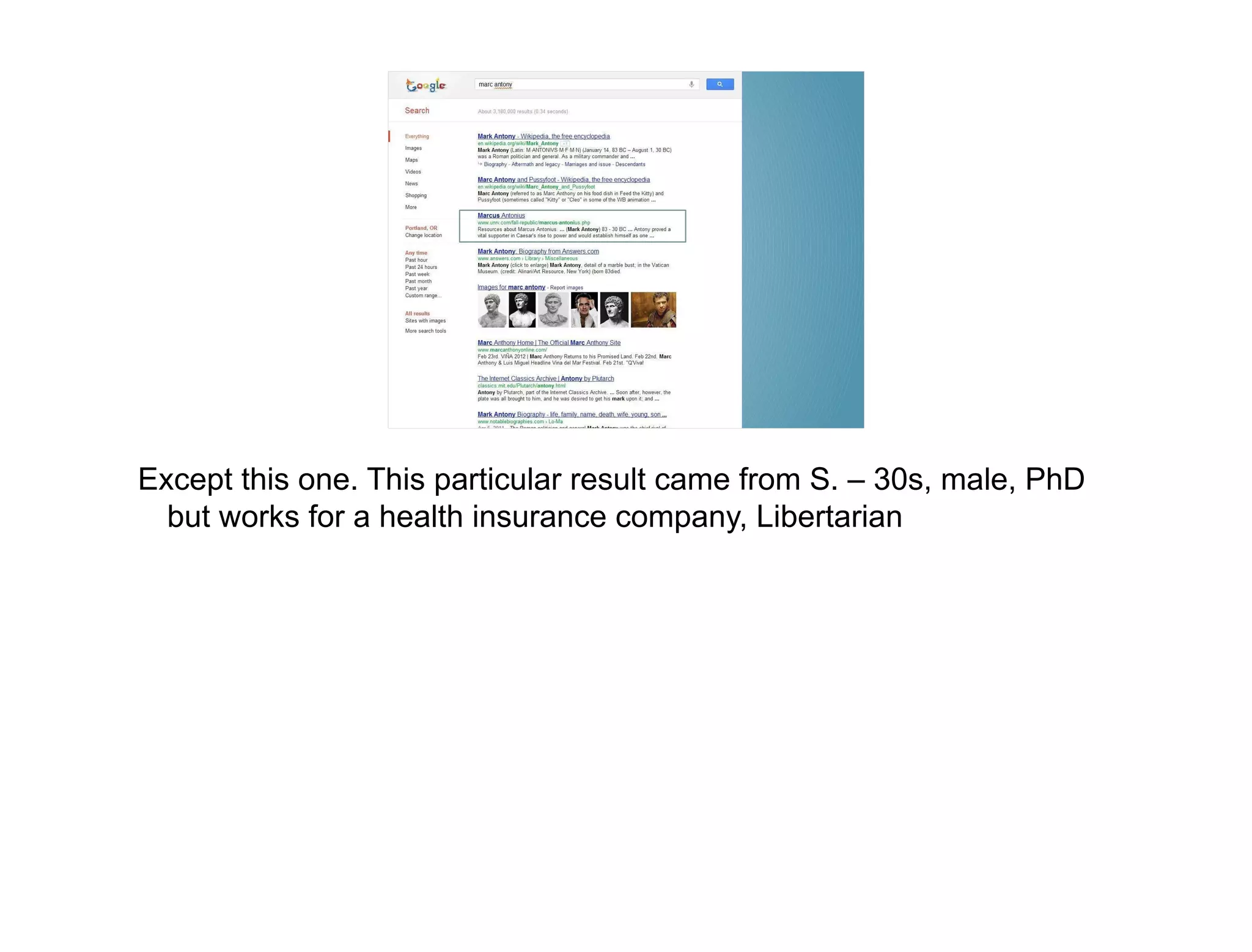
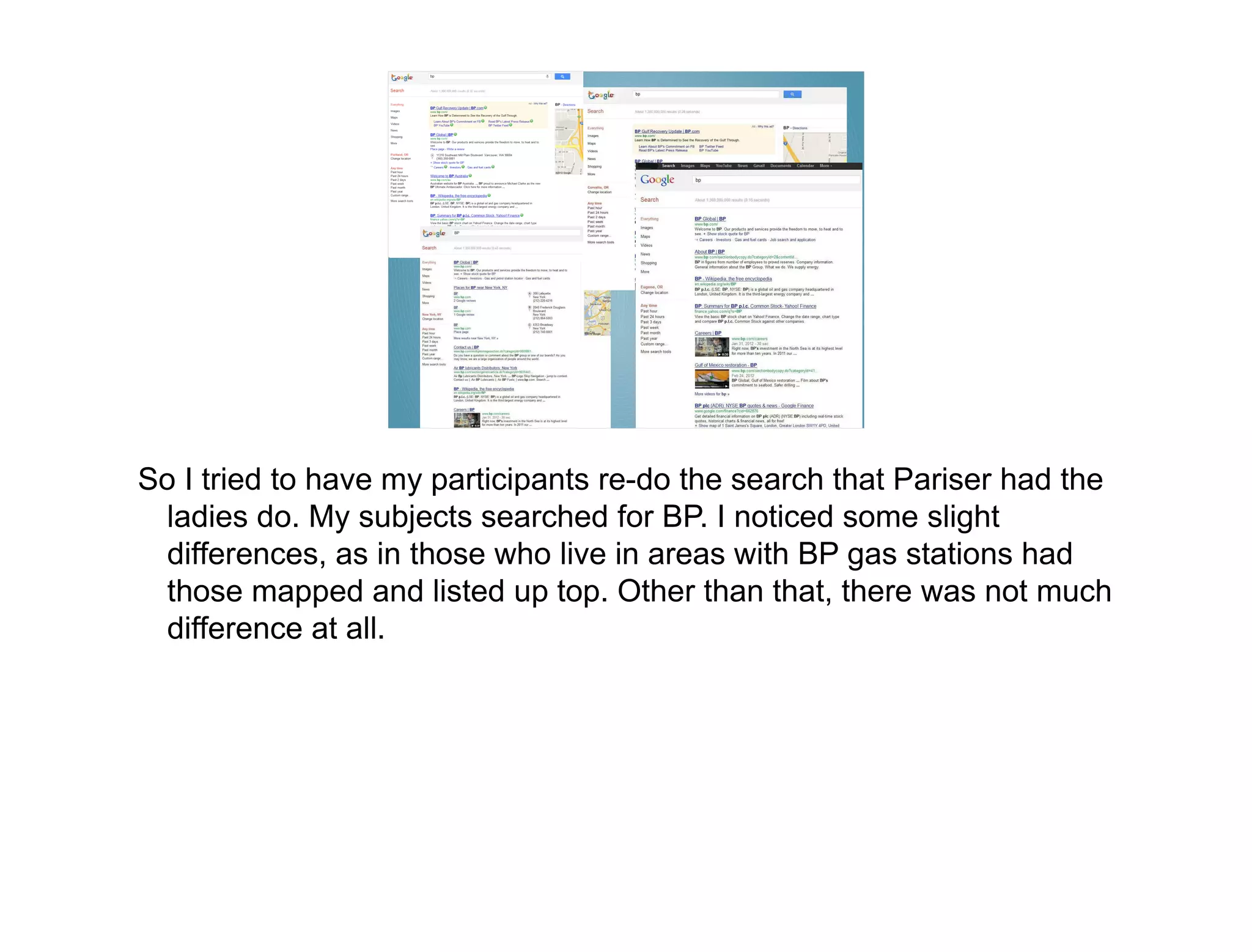
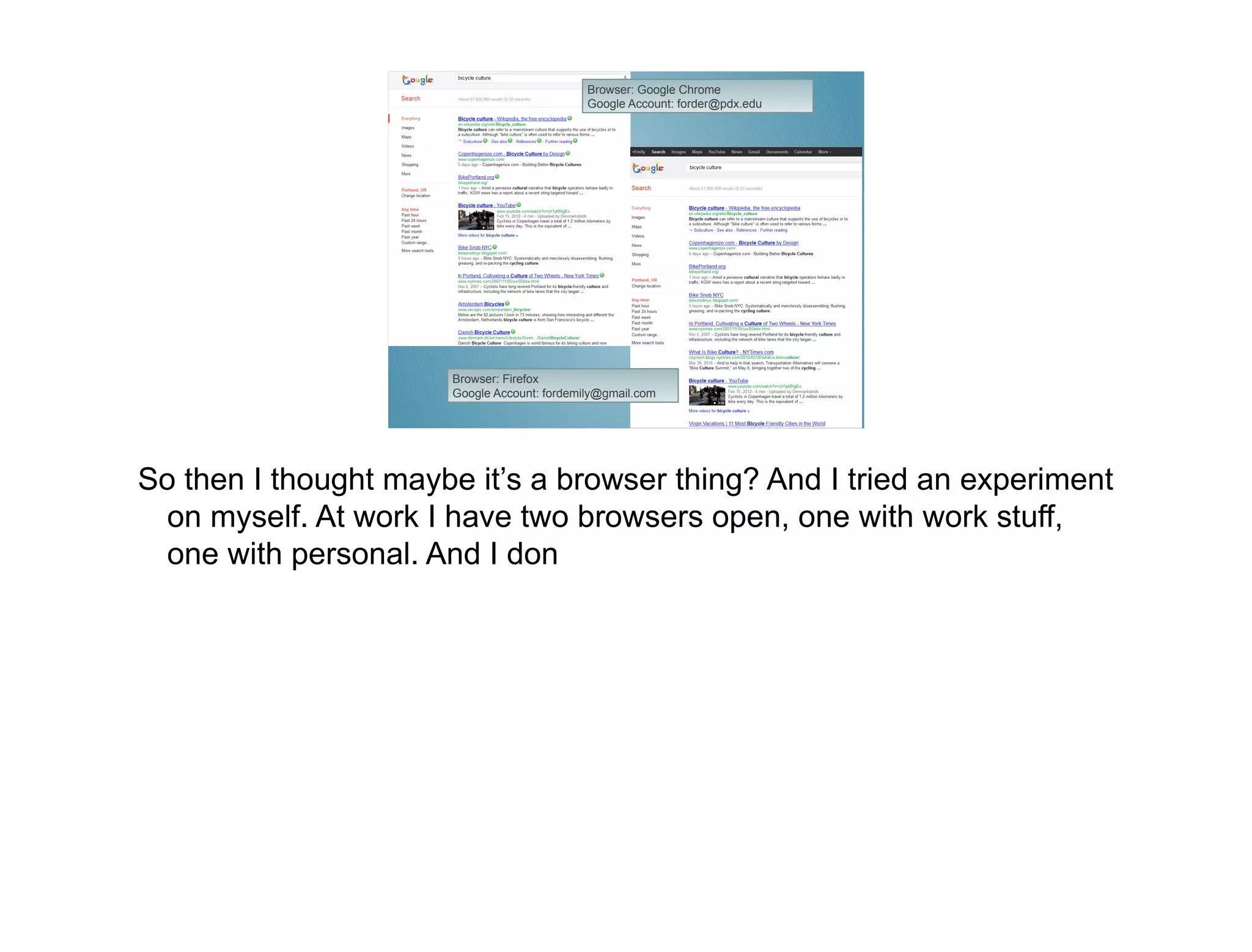
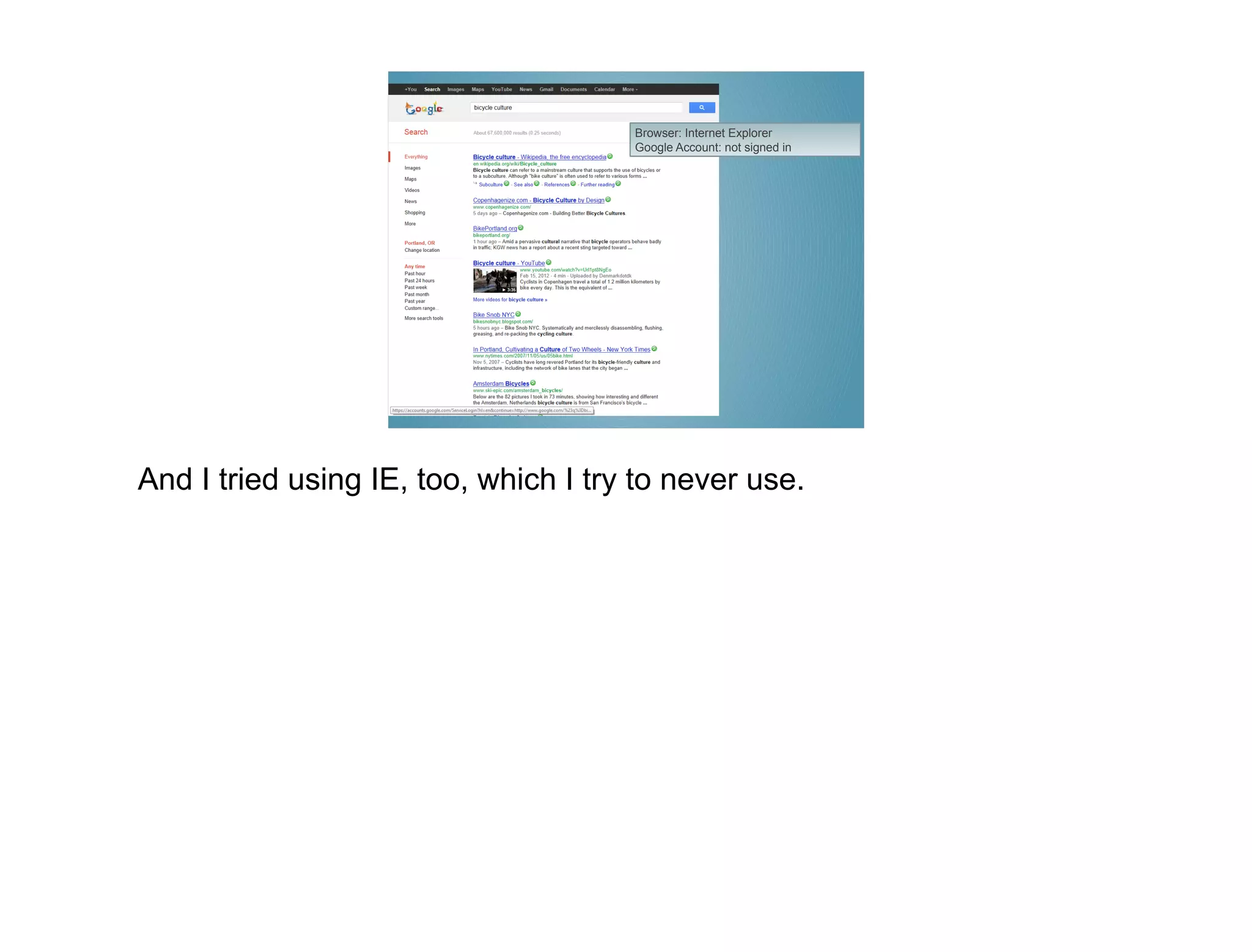
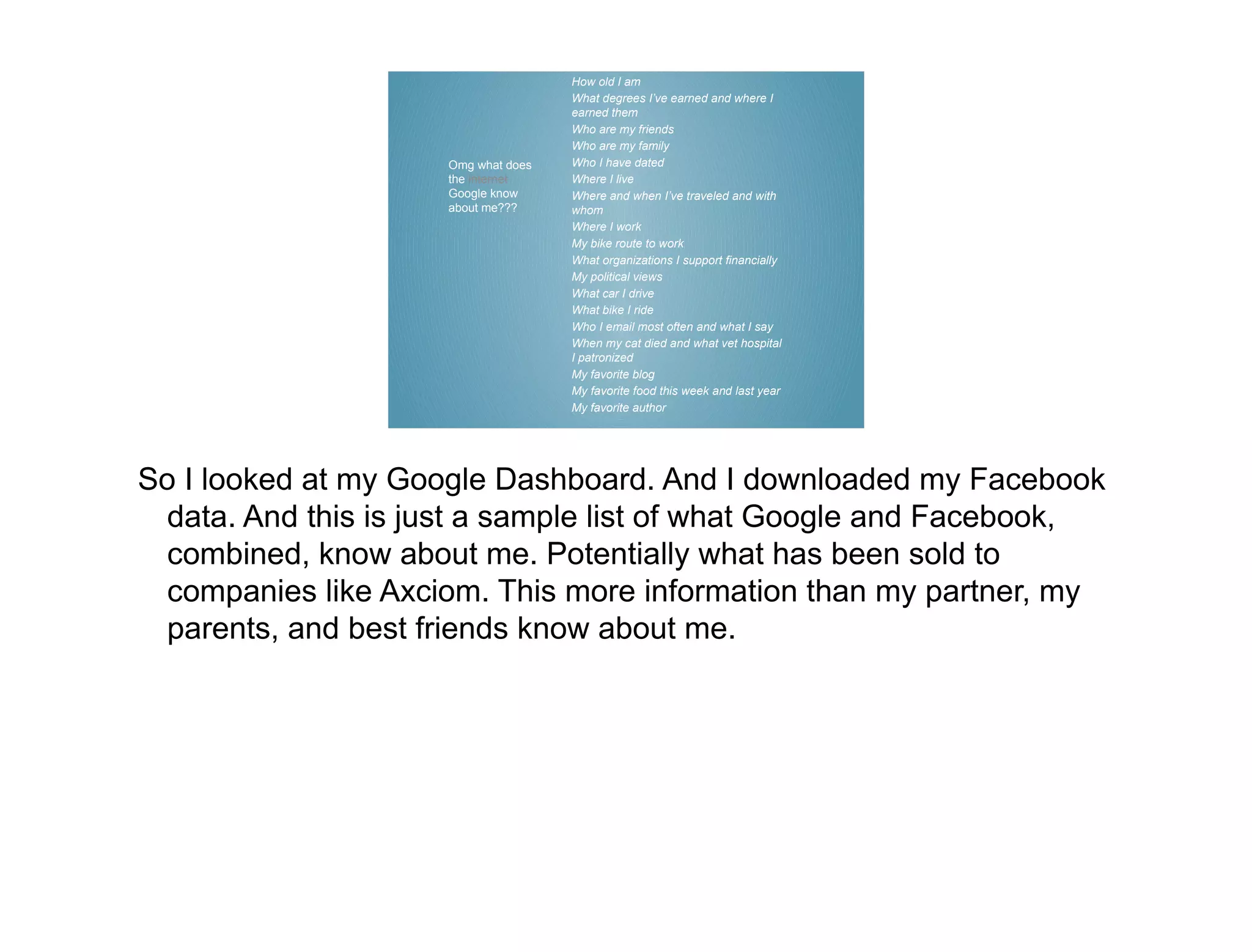
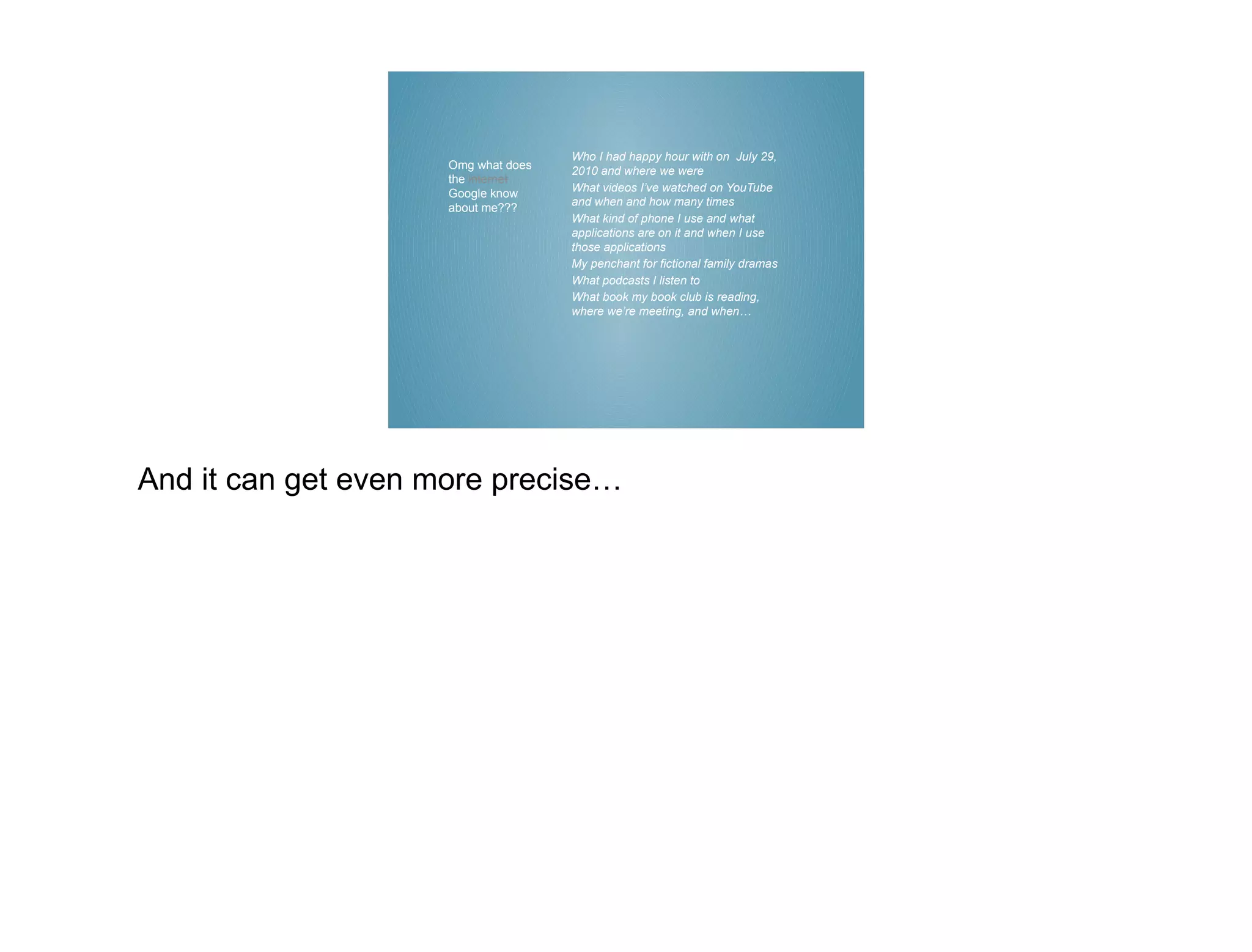
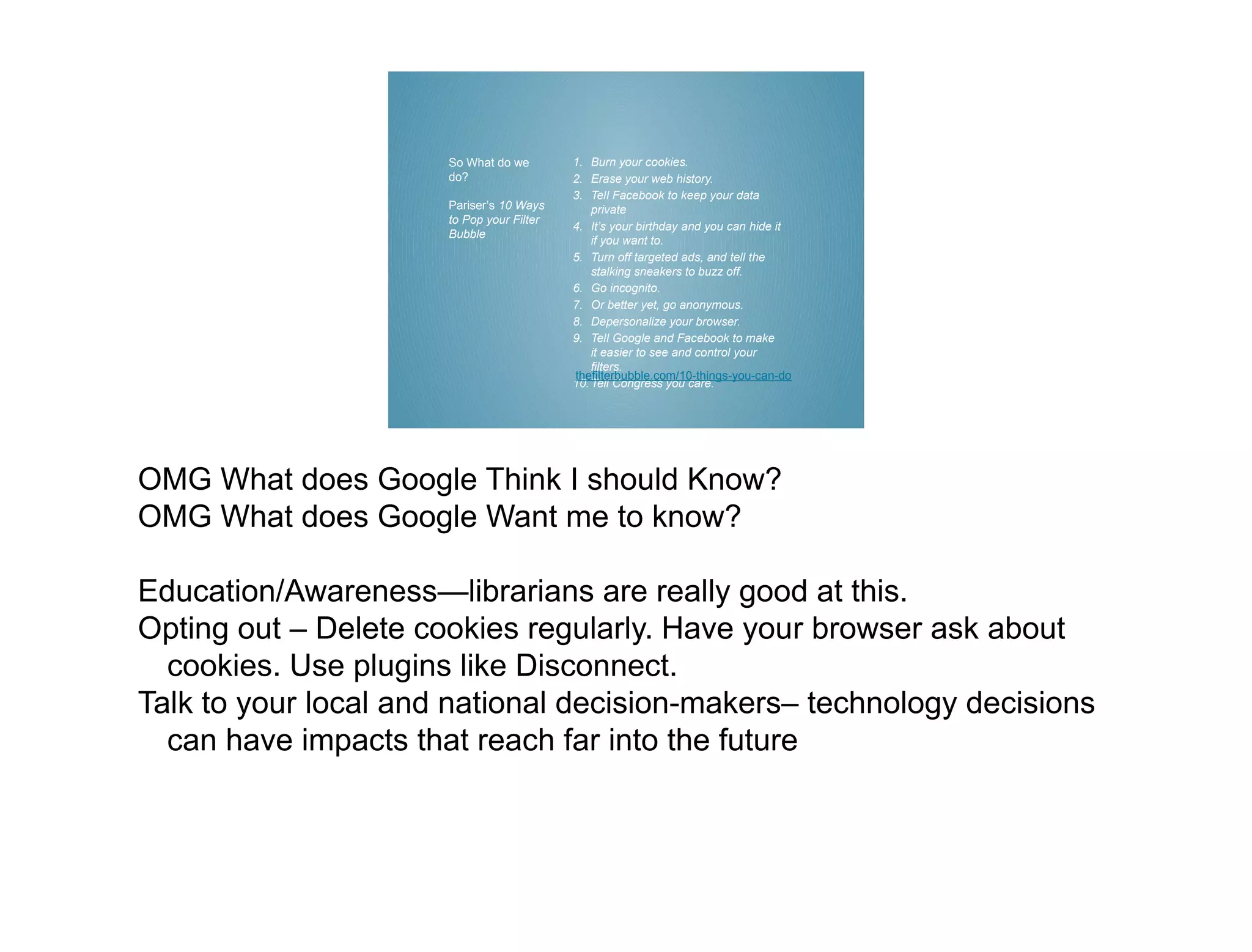
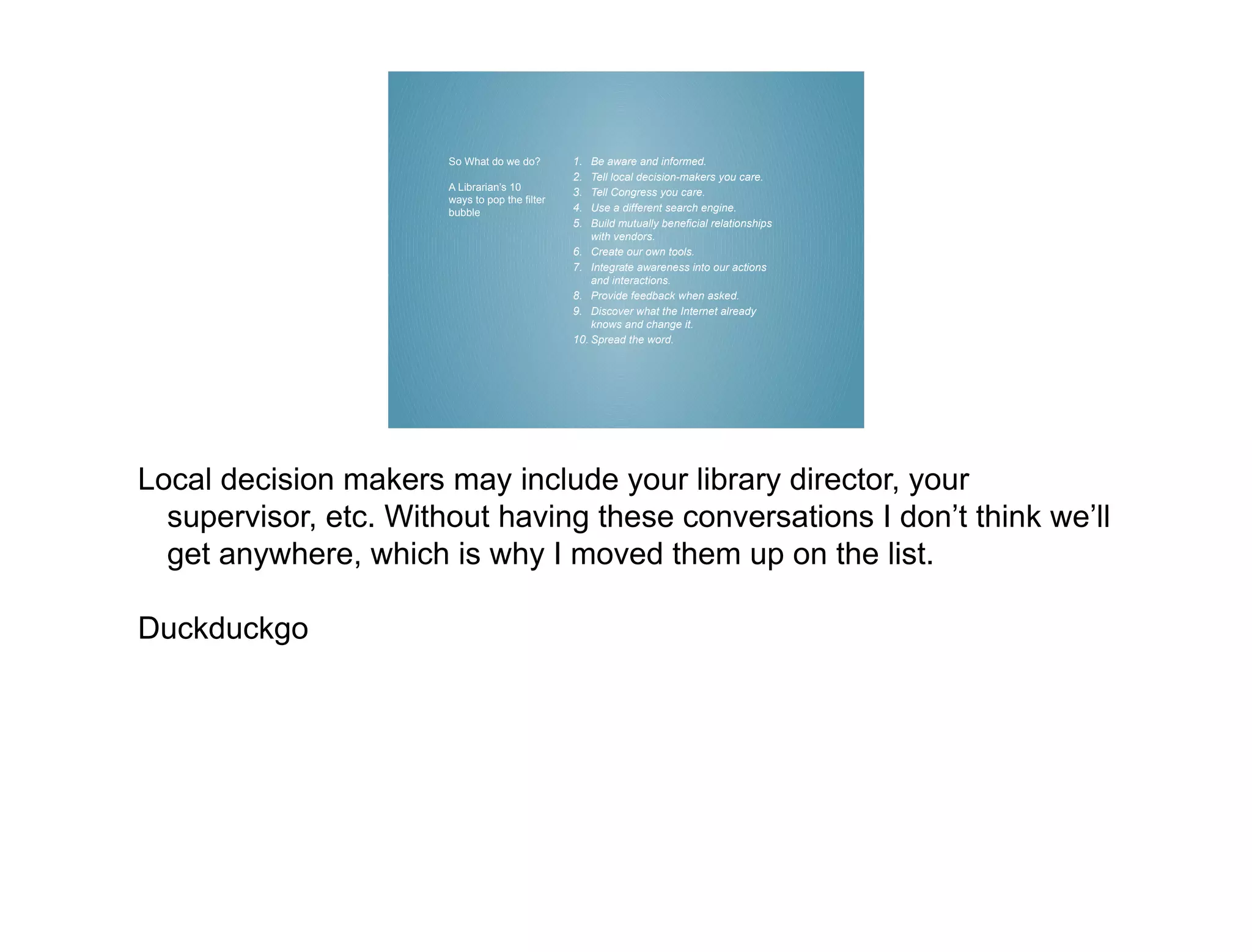
This document summarizes an experiment attempting to investigate personal filter bubbles on the internet. The author describes testing different search engines, browsers, and search terms both alone and with others. Few differences were found initially. However, a targeted ad later suggested to the author raised concerns about how much data companies like Google collect. The author realizes her own bubble has been aided by personalization. Ways to promote awareness and opt out of personalization are discussed.