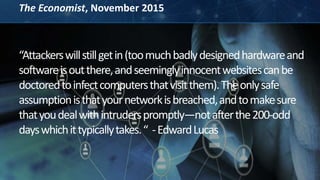
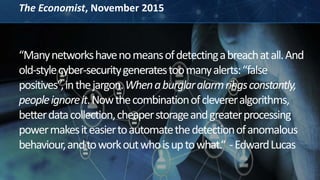
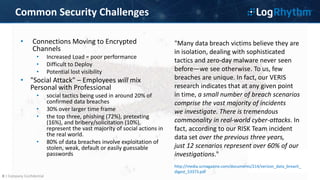
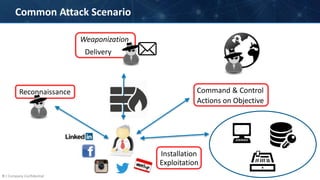
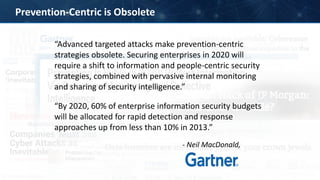
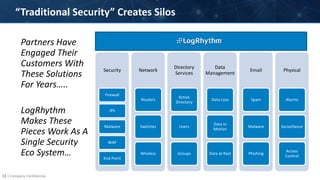
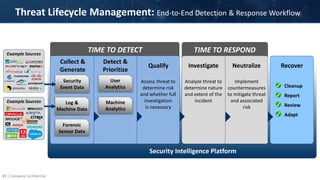
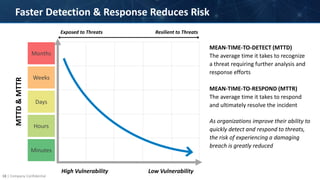
The document discusses the modern cyber threat landscape, highlighting how prevention-centric security strategies are becoming obsolete against advanced targeted attacks. It argues that effective security now requires rapid threat detection and response capabilities through security intelligence platforms that can analyze big data, detect anomalies, and orchestrate incident response workflows. Such platforms allow organizations to gain a broader view of threats, improve mean time to detect from months to minutes, and reduce the risk of experiencing damaging breaches by quickly neutralizing threats over their lifecycle.