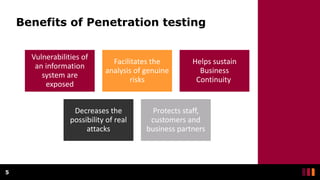
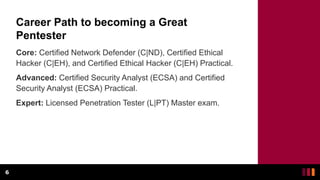
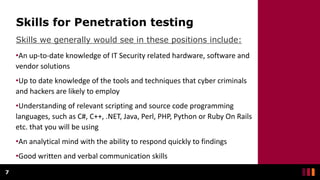
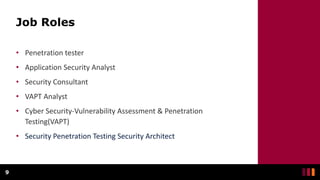
Penetration testing (pentest) involves authorized cyberattacks to identify vulnerabilities in information systems, helping organizations mitigate risks. Penetration testers, also known as ethical hackers, analyze security levels, identify gaps, and play a crucial role in protecting sensitive information. The career path includes various certifications and emphasizes skills in IT security, programming languages, and communication.