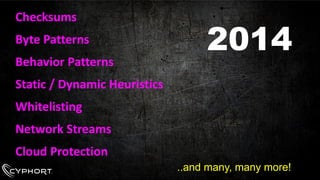
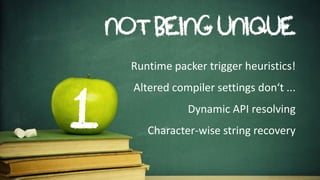
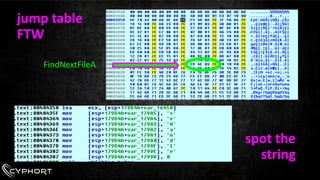
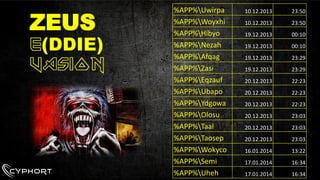
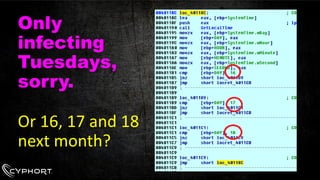
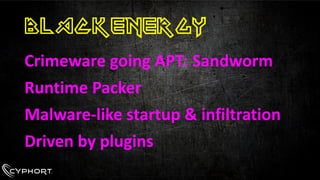
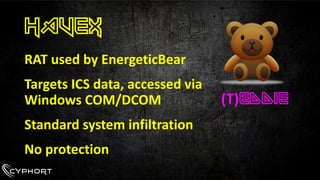
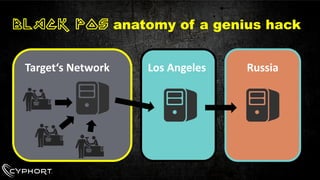
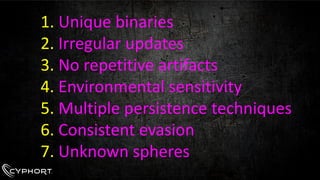
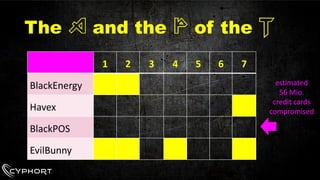
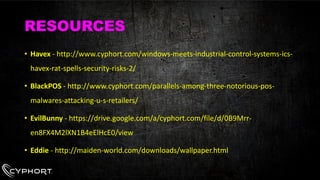
This document discusses advanced persistent threats (APTs) and their evolution over time. It notes that early detection of threats was based on knowing binary signatures and behaviors, but APTs now use unique and regularly updated binaries, lack repetitive artifacts, are environmentally sensitive, use multiple persistence techniques, and employ consistent evasion methods to avoid detection. Examples of prominent APTs discussed include BlackEnergy, Havex, BlackPOS, and EvilBunny, which were able to successfully compromise millions of records by evolving their tactics.

![ADVANCED [ədˈvɑ:n(t)st]
PERSISTENT [pəˈsɪstənt]
we don‘t understand it
we detected it too late](https://image.slidesharecdn.com/viennabsidesmarionapt-141124005258-conversion-gate02/85/The-A-and-the-P-of-the-T-3-320.jpg)