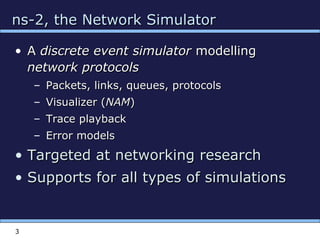
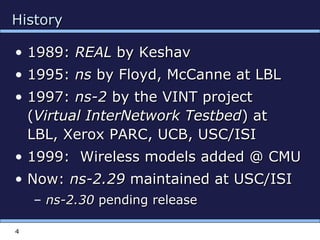
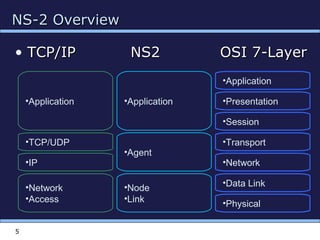
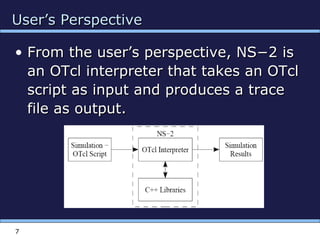
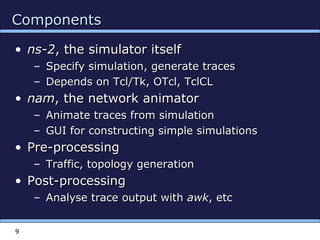
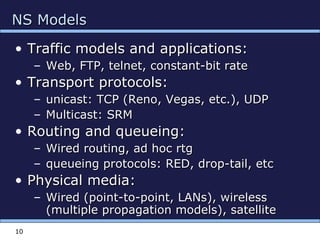
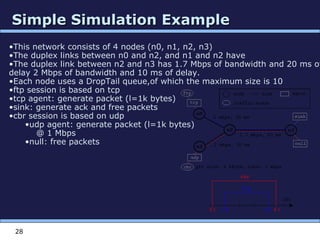
NS-2 is a discrete event network simulator for modelling network protocols and traffic. It models packets, links, queues and supports protocols like TCP and IP. NS-2 allows simulation of different network scenarios and is widely used for networking research. Simulations are created using OTcl scripts which interface with the C++-based simulator core. The document provides an overview of NS-2 architecture, usage and programming and includes an example simulation script.
![8
NS-2 EnvironmentNS-2 Environment
•Simulation
Scenario
•Tcl Script
•C++
Implementation
•1 •2
•set ns_ [new Simulator]
•set node_(0) [$ns_ node]
•set node_(1) [$ns_ node]
•class MobileNode : public Node
•{
• friend class PositionHandler;
•public:
• MobileNode();
• •
• •
•}](https://image.slidesharecdn.com/venkatns2-190413141107/85/Venkat-ns2-8-320.jpg)
![16
Basic TclBasic Tcl
# Variables:# Variables:
setset x 10x 10
setset xx
putsputs “x is $x”“x is $x”
# Functions and expressions:# Functions and expressions:
setset y [pow x 2]y [pow x 2]
setset y [expr x*x]y [expr x*x]
# Control flow:# Control flow:
ifif {$x > 0} {{$x > 0} { returnreturn $x }$x } elseelse {{
returnreturn [expr -$x] }[expr -$x] }
whilewhile { $x > 0 } {{ $x > 0 } {
putsputs $x$x
incrincr x –1x –1
}}
forfor {{setset i 0} {$i<10} {i 0} {$i<10} {incrincr i} {i} {
putsputs “$i == $i”“$i == $i”
}}
# Procedures:# Procedures:
procproc pow {x n} {pow {x n} {
ifif {$n == 1} {{$n == 1} { returnreturn $x }$x }
setset part [part [powpow x [x [exprexpr $n-1]]$n-1]]
returnreturn [[exprexpr $x*$part]$x*$part]
}}
# Files:# Files:
setset file [file [open “open “nstrace.txt” w]nstrace.txt” w]
setset line [line [getsgets $file]$file]
puts –nonewlineputs –nonewline $file “hello!”$file “hello!”
closeclose $file$file](https://image.slidesharecdn.com/venkatns2-190413141107/85/Venkat-ns2-16-320.jpg)
![Creating Simulation environmentCreating Simulation environment
21
Create event scheduler
set ns [new Simulator]
Schedule events
$ns at <time> <event>
<event>: any legitimate ns/tcl commands
Start scheduler
$ns run](https://image.slidesharecdn.com/venkatns2-190413141107/85/Venkat-ns2-21-320.jpg)
![Creating nodes, links and queuesCreating nodes, links and queues
23
Nodes
set n0 [$ns node]
set n1 [$ns node]
Links and queuing
$ns duplex-link $n0 $n1 <bandwidth> <delay>
<queue_type>
<queue_type>: DropTail, RED, CBQ, FQ, SFQ,
DRR](https://image.slidesharecdn.com/venkatns2-190413141107/85/Venkat-ns2-23-320.jpg)
![Creating connection :UDPCreating connection :UDP
24
UDP
set udp [new Agent/UDP]
set null [new Agent/Null]
$ns attach-agent $n0 $udp
$ns attach-agent $n1 $null
$ns connect $udp $null](https://image.slidesharecdn.com/venkatns2-190413141107/85/Venkat-ns2-24-320.jpg)
![Creating Traffic : on top of UDPCreating Traffic : on top of UDP
25
CBR
set src [new
Application/Traffic/CBR]](https://image.slidesharecdn.com/venkatns2-190413141107/85/Venkat-ns2-25-320.jpg)
![Creating connection : TCPCreating connection : TCP
26
TCP
set tcp [new Agent/TCP]
set tcpsink [new Agent/TCPSink]
$ns attach-agent $n0 $tcp
$ns attach-agent $n1 $tcpsink
$ns connect $tcp $tcpsink](https://image.slidesharecdn.com/venkatns2-190413141107/85/Venkat-ns2-26-320.jpg)
![Creating Traffic : on top of TCPCreating Traffic : on top of TCP
27
FTP
set ftp [new Application/FTP]
$ftp attach-agent $tcp
Telnet
set telnet [new
Application/Telnet]
$telnet attach-agent $tcp](https://image.slidesharecdn.com/venkatns2-190413141107/85/Venkat-ns2-27-320.jpg)
![Script structureScript structure
29
# parameters and options
set ns [new Simulator]
# [Turn on tracing]
# Create topology
# Setup packet loss, link dynamics
# Create routing agents
# Create:
# - protocol agents
# - application and/or setup traffic sources
# Post-processing procs
# Start simulation](https://image.slidesharecdn.com/venkatns2-190413141107/85/Venkat-ns2-29-320.jpg)