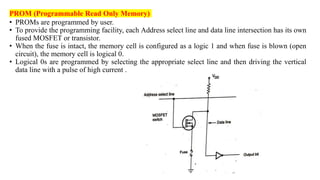
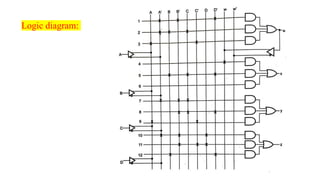
This document discusses different types of memory and programmable logic devices. It begins by explaining error detecting and correcting codes, including parity bits which allow detection of errors during transmission. It then discusses Hamming codes, which allow for both error detection and correction by including parity bits at specific bit locations. The document goes on to describe different types of read-only memory (ROM) - masked ROM, programmable ROM (PROM), erasable programmable ROM (EPROM), and electrically erasable programmable ROM (EEPROM). PROMs can be programmed by the user, EPROMs can be erased by ultraviolet light to be reprogrammed, and EEPRO