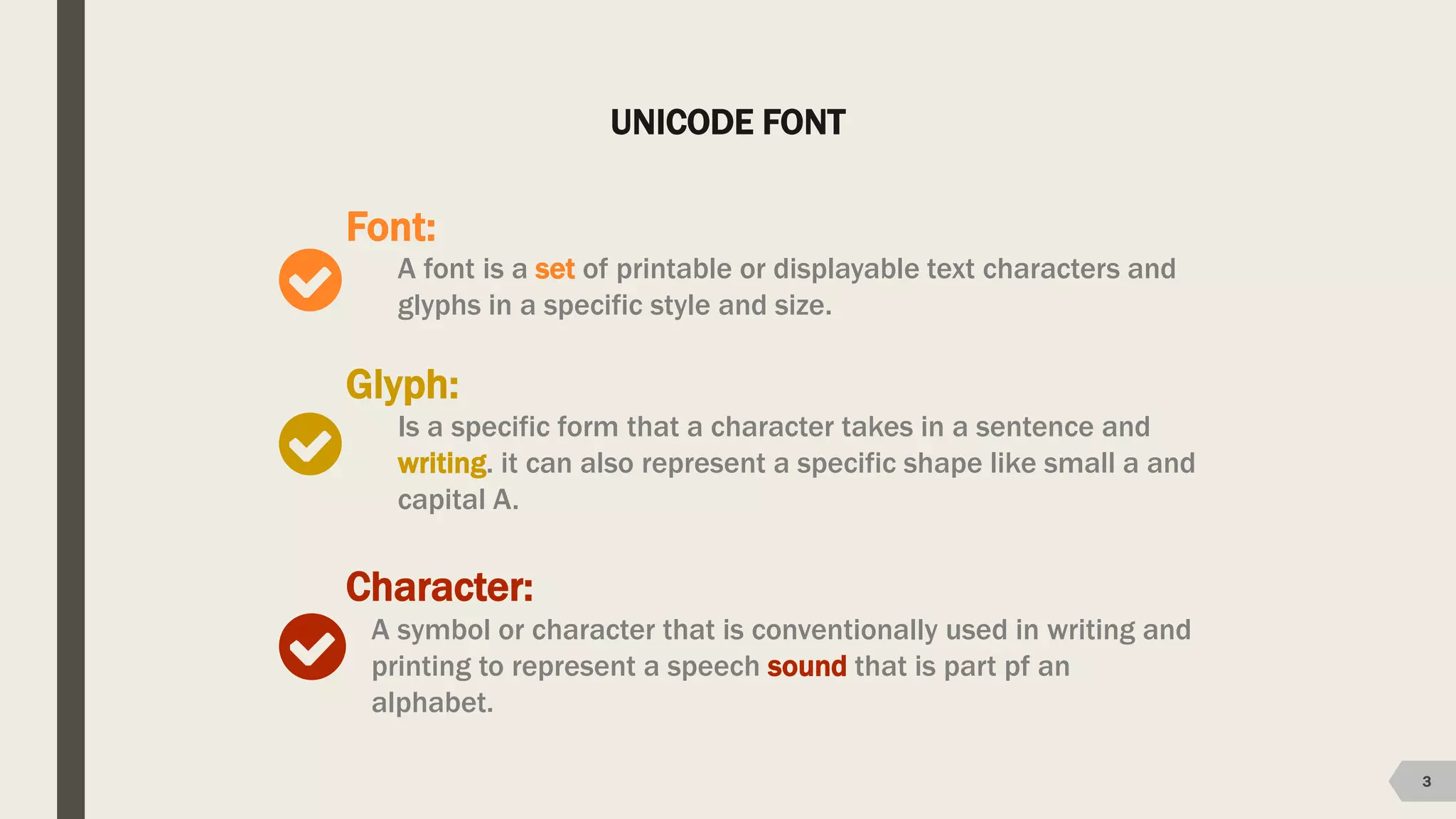
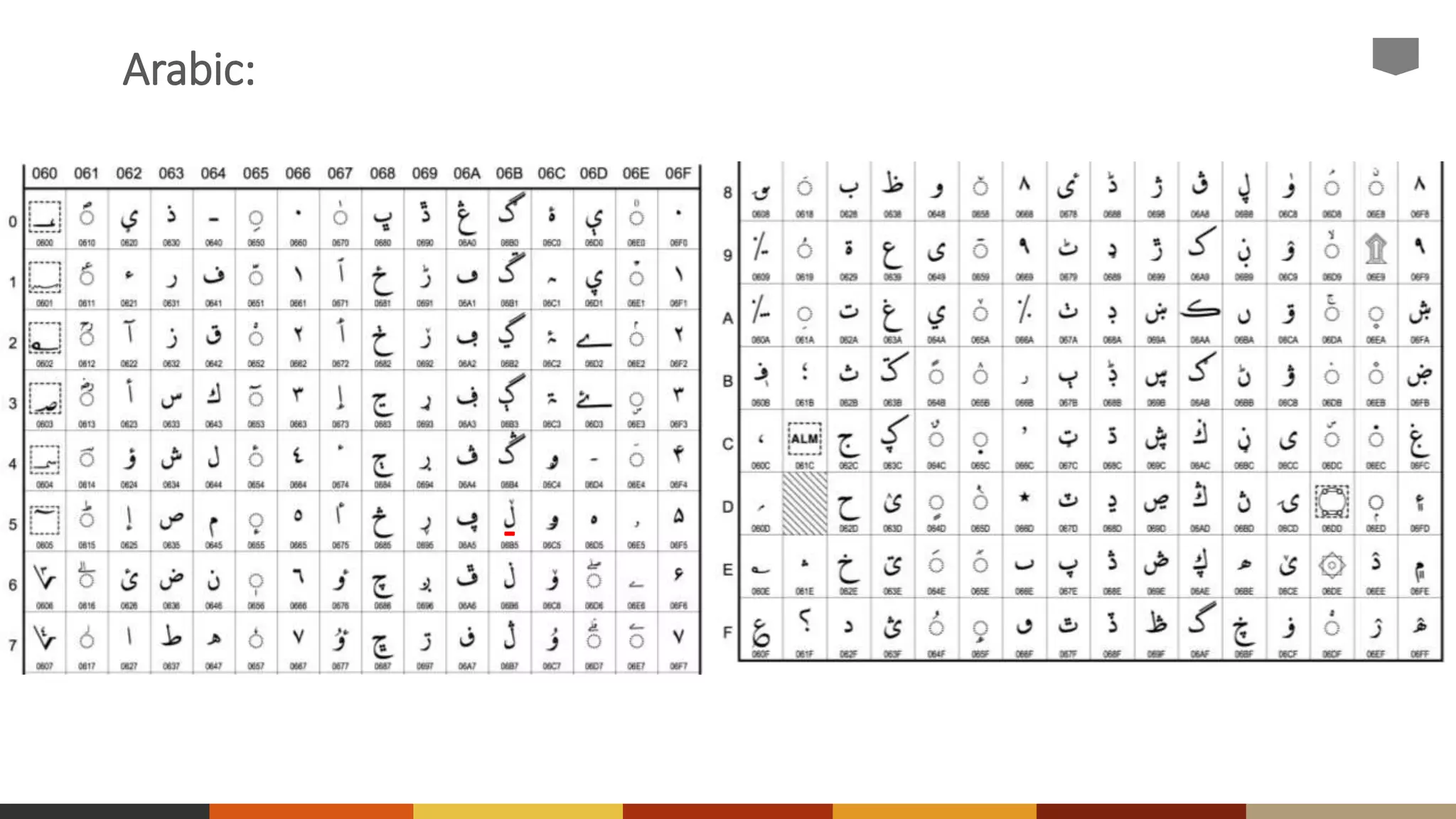
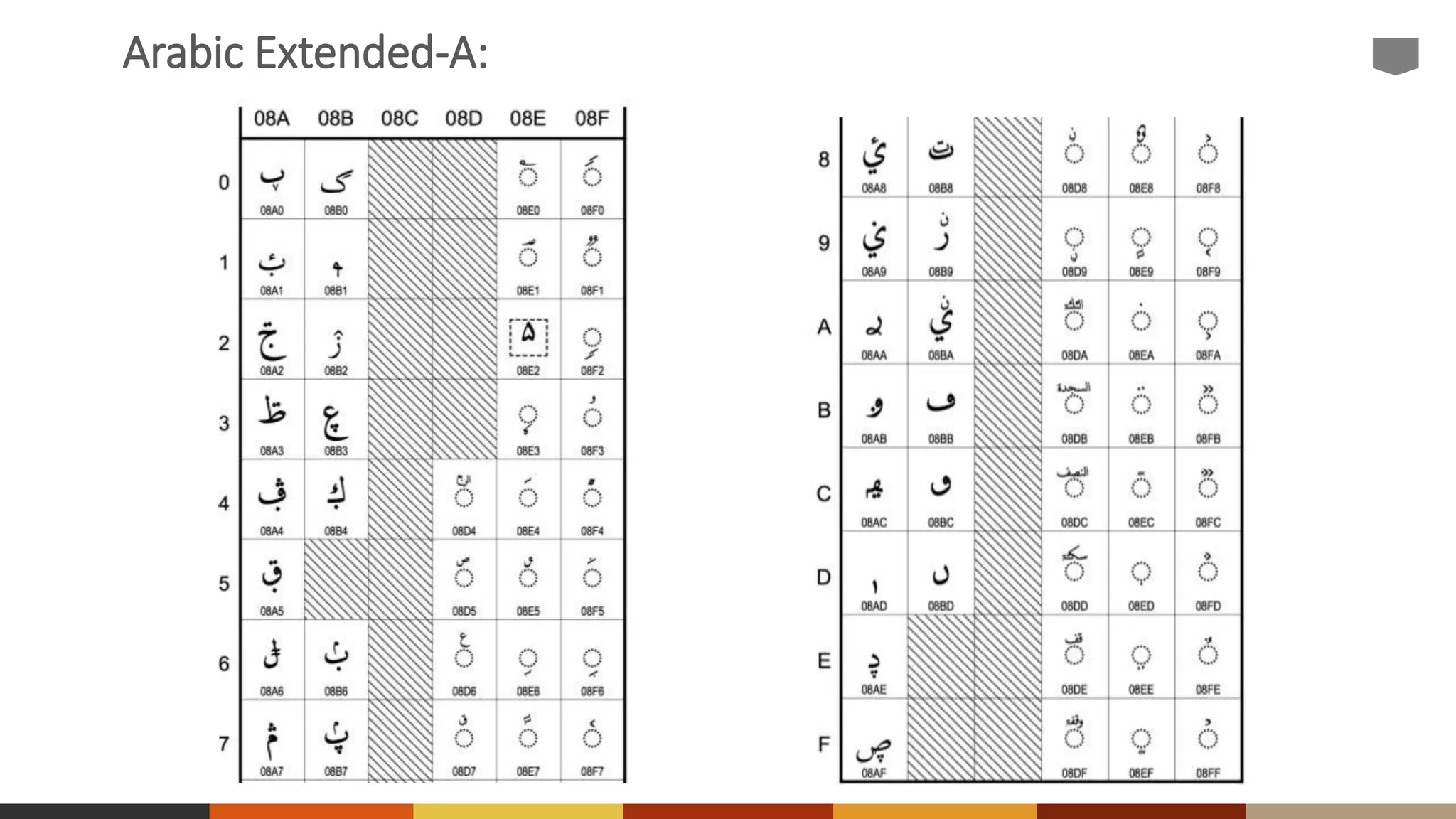
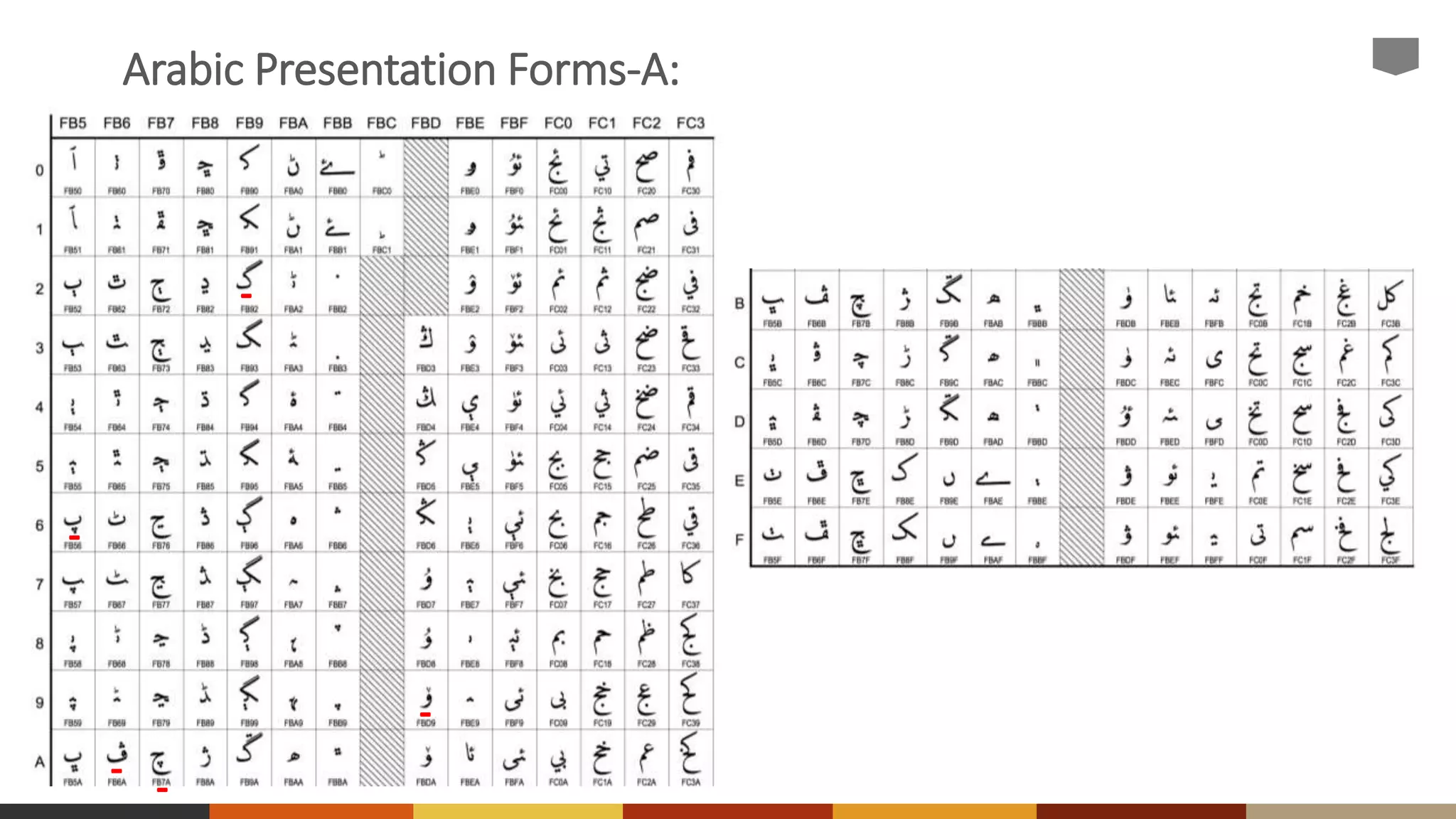
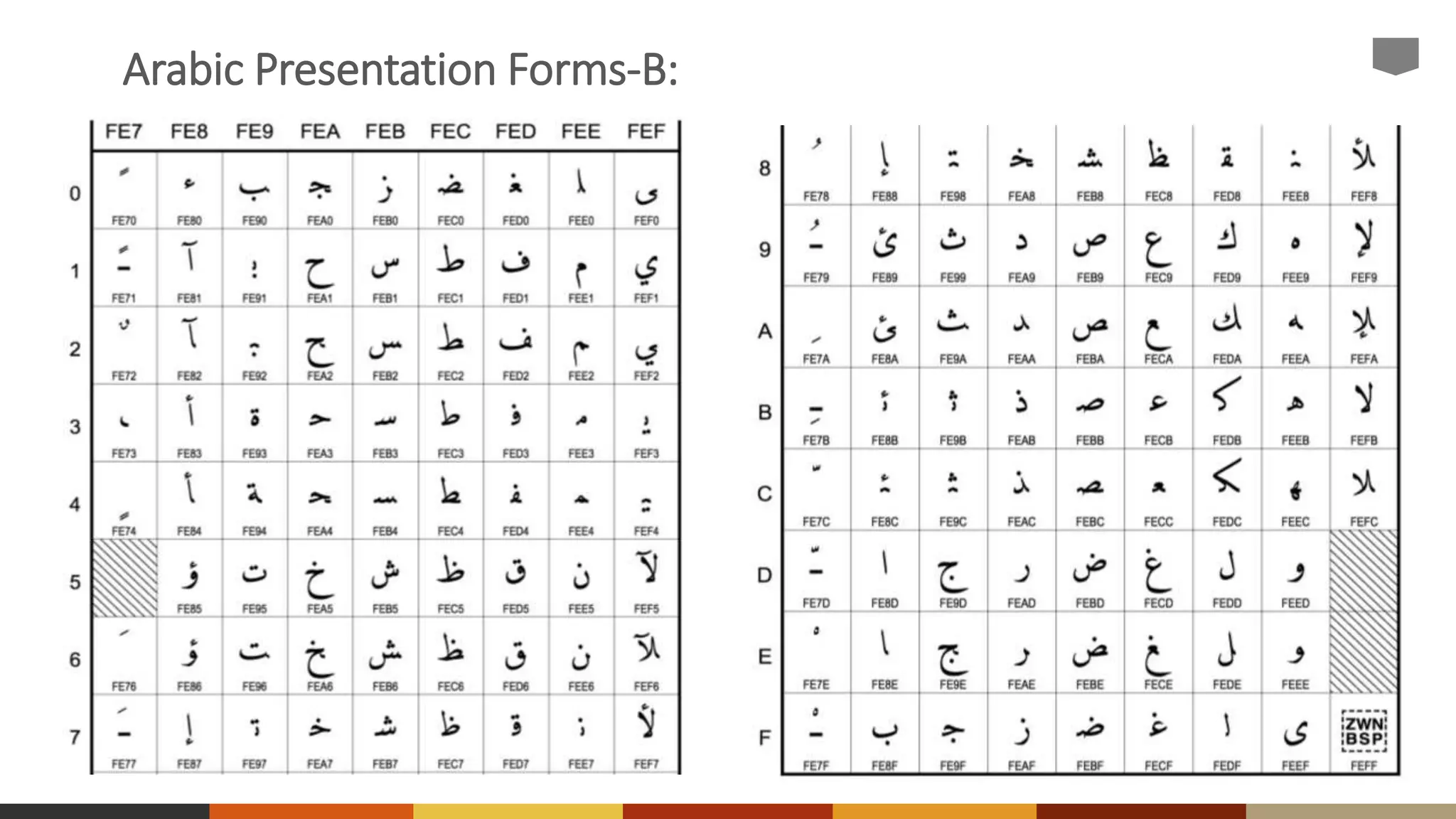
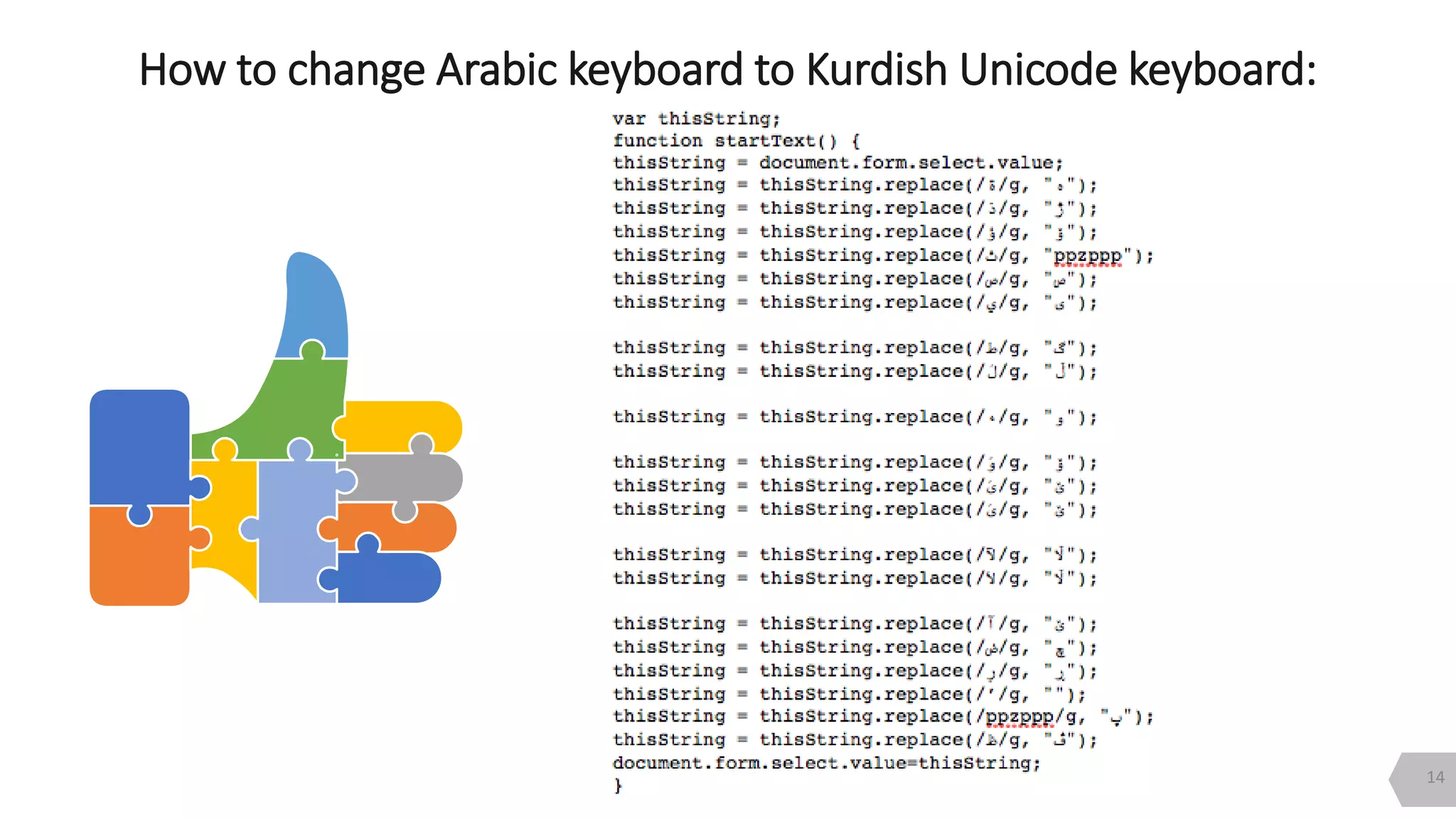
The document discusses the concepts of Unicode and Kurdish fonts, explaining the definitions of fonts, glyphs, and characters. It details the Unicode standard, including the encoding methods and character sets for various scripts, specifically highlighting Arabic and Kurdish Unicode. Additionally, it offers insights on how to change an Arabic keyboard to a Kurdish Unicode keyboard.