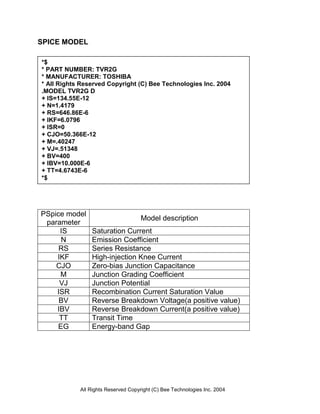
This document provides a SPICE model for the TVR2G general purpose rectifier diode manufactured by Toshiba. It includes the model parameters, simulation results comparing the diode's forward and reverse characteristics to measurements, and evaluation of the reverse recovery time constant.