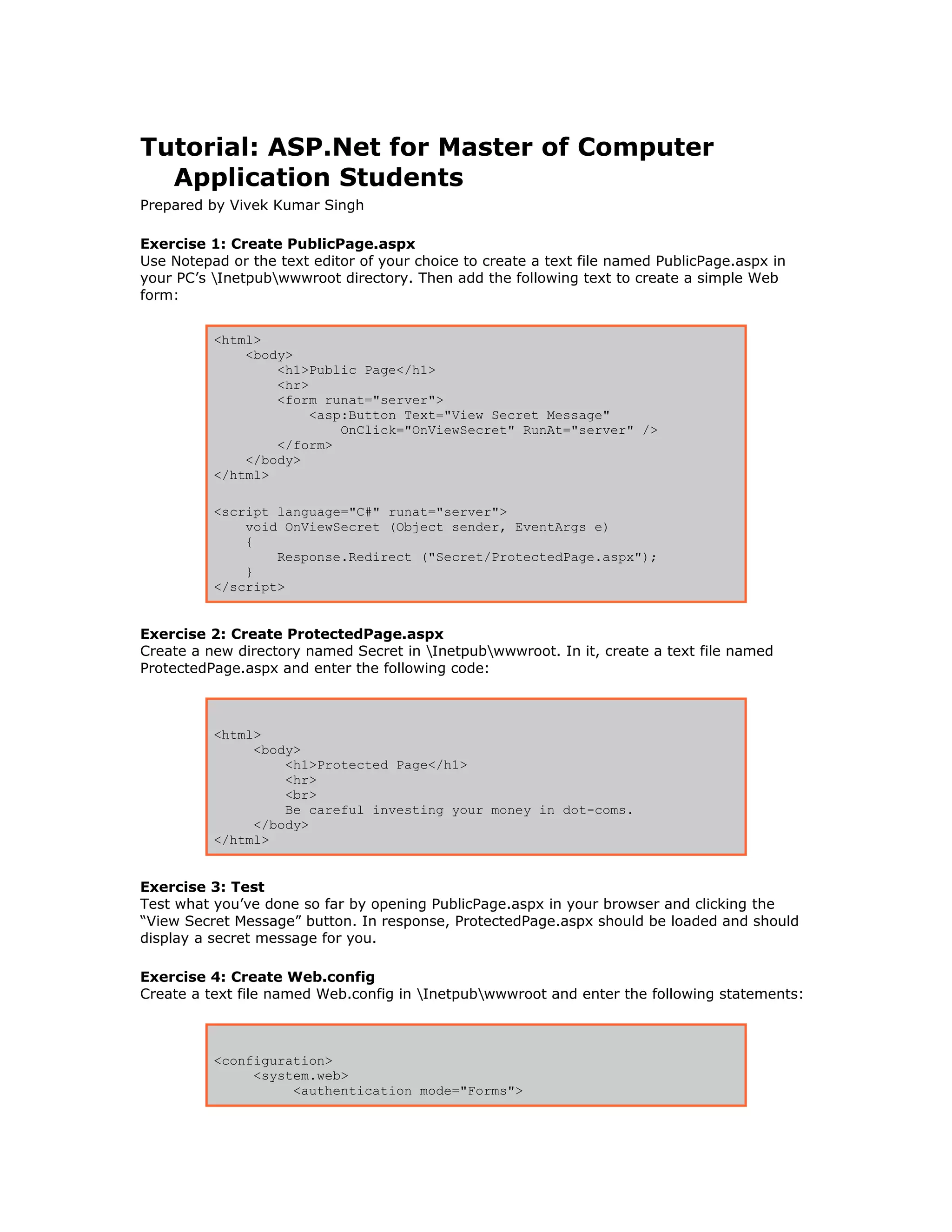
This document provides a tutorial with 15 exercises to teach how to create a basic ASP.Net web application with user authentication and authorization. The exercises guide the user to create web forms, configure authentication using web.config files, add a login page that authenticates against a SQL database, and customize the user experience including remembering user logins.



![Before proceeding, use the SQL Server Query Analyzer (or the tool of your choice) to verify
that the database was properly created and initialized.
Note: Weblogin.sql assumes that SQL Server is installed on drive C: on your PC. If you
installed SQL Server on a different drive, open Weblogin.sql and edit the statement
FILENAME = 'C:program files...weblogin.mdf'
to include the correct drive letter.
Exercise 11: Add a CustomAuthenticate method and modify OnSubmit
Add the following statements to the top of LoginPage.aspx:
<%@ Import NameSpace="System.Data" %>
<%@ Import NameSpace="System.Data.SqlClient" %>
Then add the following method to the <script> block:
bool CustomAuthenticate (string username, string password)
{
SqlDataAdapter adapter =
new SqlDataAdapter ("select password from credentials " +
"where username = '" + username + "'",
"server=localhost;uid=sa;pwd=;database=weblogin");
DataSet ds = new DataSet ();
adapter.Fill (ds);
DataTable table = ds.Tables[0];
foreach (DataRow row in table.Rows) {
string pw = row[0].ToString ().TrimEnd (new char[] { ' ' });
if (String.Compare (password, pw, false) == 0)
return true;
}
return false;
}
Finally, modify the OnSubmit method so that it calls CustomAuthenticate instead of
FormsAuthentication.Authenticate:
void OnSubmit (Object sender, EventArgs e)
{
if (CustomAuthenticate (UserName.Text, Password.Text))
FormsAuthentication.RedirectFromLoginPage (UserName.Text, false);
else
Output.Text = "Invalid login";
}
CustomAuthenticate uses ADO.NET to perform a database query and validate the user name
and password provided to it.
Exercise 12: Test
Restart your browser again. Then test the application again by clicking the “View Secret](https://image.slidesharecdn.com/tutorial-asp-net-130309091234-phpapp02/85/Tutorial-asp-net-5-320.jpg)


