ASP.Net Presentation Part3
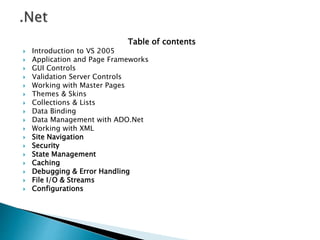
- 1. Table of contents Introduction to VS 2005 Application and Page Frameworks GUI Controls Validation Server Controls Working with Master Pages Themes & Skins Collections & Lists Data Binding Data Management with ADO.Net Working with XML Site Navigation Security State Management Caching Debugging & Error Handling File I/O & Streams Configurations
- 2. We can access an aspx web application by means of virtual path. http://localhost/VirtualDirectoryName/Defau lt.aspx If Default.aspx file exists in the application, this URL would open the file in browser. We can also give any other valid aspx file name in the browser to view that file
- 3. Threats faced by an application ◦ Spoofing ◦ Tampering ◦ Repudiation ◦ Information disclosure ◦ Denial of Service ◦ Elevation of privilege
- 4. Security in the context of ASP.NET application involves 3 fundamental terms Authentication ◦ is the process of identifying users who can use the application (password checking) Authorization – Defining what operations the users can do and to what level (access rights check) Impersonation ◦ This is the technique used by a server application to access resources on behalf of a client
- 5. Authentication Modes ◦ Windows Authentication – IIS authentication ◦ Forms Authentication - Application credential verification ◦ Microsoft Passport Authentication Specifying Authentication Mode ◦ Can be specified in the Web.config file as follows <authentication mode=“Windows" /> <authentication mode=“Forms" /> <authentication mode=“Passport" />
- 6. Basic ◦ IIS instructs the browser to send the user's credentials over HTTP ◦ Credentials are Base64 encoded which are not that much secure Digest ◦ Digest authentication sends credentials across the network as a Message Digest 5 (MD5) hash (encrypted) Integrated Windows (Used in large organisation connected with Network) ◦ Uses either NTLM challenge/response or Kerberos to authenticate users with a Windows NT Domain or Active Directory account ◦ A Hash of the credentials is sent, password is encrypted and sent .NET Passport ◦ The credentials that are registered with Microsoft which can be used with any microsoft application like – hotmail, msn messenger or skydrive or windows Live etc
- 7. We can allow or deny Users using authorization tag in web.config file <authorization> <deny users="?"></deny> <allow users="*" /> <!-- Allow all users --> <!-- <allow users="[comma separated list of users]" roles="[comma separated list of roles]"/> <deny users="[comma separated list of users]" roles="[comma separated list of roles]"/> --> </authorization>
- 8. Can store credentials in web.config files For Login page, only if given the following credentials it will allow. <authentication mode="Forms"> <forms name="Login" loginUrl="Login.aspx"> <credentials passwordFormat="Clear"> <user name="smith" password="manager"></user> <user name="Smith" password="manager"></user> </credentials> </forms> </authentication>
- 9. Web forms are created and destroyed each time a client makes a request Page state is not retained ◦ For postbacks ◦ Between pages State management is implemented using ◦ Client side options Viewstate Cookies QueryString ◦ Server side options Application Session Database support
- 10. Stores information as hidden fields ViewState is enabled for every page by default Saving Arraylist in a view state protected void Page_PreRender(object sender, EventArgs e) { ViewState.Add("arrayListInViewState", PageArrayList); } We can access the same as follows ViewState[“arrayListInViewState”]
- 11. To store small amounts of information on a client To store user-specific information Store as key/value pair //Create a cookie HttpCookie uname = new HttpCookie("UserName"); uname.Value = txtUser.Text; //Add the cookie Response.Cookies.Add(uname); //Set the Expiry date for the cookie Response.Cookies["UserName"].Expires = d1.AddYears(2); //Retrive the value of cookie if(Request.Cookies["UserName"] != null) { //Display the value of cookie lblUser.Text = Request.Cookies["UserName"].Value; }
- 12. Easy way to pass information ◦ Between pages Way to pack information with URL The URL with a query string look like below http://localhost/Demo/Default.aspx?Uname=“guest” To send page data as query string Response.Redirect("welcome.aspx?category="+txtCategory.T ext) To retrieve data in next page lblCategory.Text=“We welcome” + Request.QueryString[“category”];
- 13. ◦ Can store information that we want to keep local to the current session (single user) ◦ We can store values that need to be persisted for the duration of a user ◦ Every user session will be assigned a unique SessionId protected void Session_Start(Object sender, EventArgs e) { Session["userName"] =“guest"; } protected void Session_End(Object sender, EventArgs e) { Session.Remove("userName"); }
- 14. Session state can be stored in three ways ◦ InProc Stores session data in the memory of the ASP.NET worker process Provides faster access to these values Session data is lost when the ASP.NET worker process is recycled Need to give in the Web.config file as follows <sessionState mode="InProc“/> ◦ StateServer Uses a stand alone window service (State Server) to store session variables Independent of IIS as it can run as separate service Better load balancing management as clustered servers can share their session information Need to give in the Web.config file as follows <sessionState mode=" StateServer“/>
- 15. ◦ SQLServer Similar to State Server, except that the information persists in MS-SQL Server database tables Need to give the following in Web.config file <sessionState mode=“SQLServer“/> Note: To use SQL Server as session state store, create the necessary tables and stored procedures .NET SDK provides us with a SQL script InstallPersistSqlState.sql
- 16. Provides a mechanism for storing data that is accessible to all users using the Web Application Are declared in a special file called as Global.asax void Application_Start() { Application["startTime"] = DateTime.Now.ToString(); } void Application_End() { Application["startTime"] = null; }
- 17. Database support may be used to maintain state of your Web site Advantages of Using a Database to Maintain State ◦ Security ◦ Storage capacity ◦ Data persistence ◦ Robustness and data integrity ◦ Accessibility ◦ Widespread support Disadvantages of Using a Database to Maintain State ◦ Complexity ◦ Performance considerations
- 18. ◦ In ASP.NET, page gets processed and is destroyed for every request ◦ Some times, dynamic contents of page may not change frequently ◦ ASP.NET holds such content in memory so that it can be delivered again efficiently without processing
- 19. Use the @OutputCache page directive to cache a Web form in the server’s memory ◦ The Duration attribute of @OutputCache directive’s controls how long the page is cached. Setting VaryByParam="None” caches only one version of the web form // Web form is Cached for 60 seconds <%@ OutputCache Duration="60" VaryByParam="None" %>
- 20. //This page sends item (Infopage.aspx) private void btnSubmit_Click(object sender, System.EventArgs e) { Response.Redirect("NextPageVaryParam.aspx?id="+drpTimeZone .SelectedItem); } // Web form is Cached for dropdownlistbox selected item //This page is cached depend on item selected from //infopage.aspx <%@ OutputCache Duration="60" VaryByParam=“id" %>
- 21. Cache regions of a page content Attribute used ◦ @ OutputCache ◦ VaryByParam -varies cached results based on name/value pairs sent using POST or GET ◦ VaryByControl -varies the cached fragment by controls within the user control <%@ OutputCache Duration="120" VaryByParam="none" VaryByControl="Category" %>
- 22. Data caching is storing of data internal to a web application This enables to use the cached object across all the pages of the application Cache is global to entire web application and is accessible to all the clients of that application The lifetime of such cached objects is that of the application itself If the application is restarted then all the cached objects are destroyed Expiry time can be set for cache objects ◦ Absolute Expiry (Absolute value) ◦ Sliding Expiry (relative value – from now onwards 5 seconds)
- 23. Visual studio 2005 provides a built in debugger. Breakpoint – Press F9 to insert break point at a location or Select Insert Break Point from Debug Menu We can Step Over using (F10 key) or Step Into using (F11 key) a function
- 24. .NET CLR provides structured Exception handling ◦ Using try catch block ASP.NET provides declarative error handling ◦ Automatically redirect users to error page when unhandled exceptions occur ◦ Prevents ugly error messages from being sent to users The Web.Config should have these lines <configuration> <customErrors mode=“On” defaultRedirect=“error.htm”> <error statusCode=“404” redirect=“adminmessage.htm”/> <error statusCode=“403” redirect=“noaccessallowed.htm”/> </customErrors> </configuration>
- 25. The mode attribute can be one of the following: ◦ On Error details are not shown to anybody, even local users If you specify a custom error page it will be always used ◦ Off Everyone will see error details, both local and remote users If you specify a custom error page it will NOT be displayed ◦ RemoteOnly Local users will see detailed error pages Remote users will be presented with a concise page notifying them that an error occurred Note : Local user means User browsing the site on the same machine where web applications are deployed
- 26. System.IO name space will have Methods and classes for File Handling FileInfo and DirectoryInfo class helps us in managing files and directory Both these classes are inherited from FileSystemInfo class
- 27. Used to discover general characteristics about a given file or directory. Properties - Attributes - Creation Time - Exists - Extension - Full Name - Last Access Time - Last Write time - Name
- 28. Methods - AppendText() - MoveTo() - CopyTo() - Open() - Create() - OpenRead() - CreateText() - OpenText() - Delete() - OpenWrite() Properties - Directory - DirectoryName - Length - Name
- 29. FileInfo FI = new FileInfo(@"form1.cs“) MessageBox.Show(FI.DirectoryName.ToString()); MessageBox.Show(FI.Extension.ToString()); MessageBox.Show(FI.LastAccessTime.ToString()); MessageBox.Show(FI.LastWriteTime.ToString());
- 30. Streams are channels of communication between programs and source/destination of data ◦ A stream is either a source of bytes or a destination for bytes. Provide a good abstraction between the source and destination Abstract away the details of the communication path from I/O operation Streams hide the details of what happens to the data inside the actual I/O devices. Streams can read/write data from/to blocks of memory, files and network connections Stream can be File or Console or Network or Hardware
- 31. Byte Stream ◦ FileStream – Works with File ◦ MemoryStream – Works with array ◦ BufferedStream - Optimized read/write operations Character Stream ◦ TextReader ◦ TextWriter
- 32. FileStream class is used to read from, write to, open, and close files on a file system The MemoryStream class creates streams that have memory as a backing store instead of a disk or a network connection ◦ encapsulates data stored as an byte array BufferedStream ◦ A buffer is a block of bytes in memory used to cache data ◦ reduces the number of calls to the operating system ◦ Buffers improve read and write performance.
- 33. Both are abstract classes used read and write data using characters from different streams TextReader ◦ Represents a reader that can read a sequential series of characters TextWriter ◦ Represents a writer that can write a sequential series of characters To read and write we use derived classes like StreamReader and StreamWriter
- 34. It can be used in the way StreamReader/Writer are used. The BinaryReader methods ◦ bool ReadBoolean() ◦ byte ReadByte() ◦ char ReadChar() ◦ float ReadSingle() ◦ double ReadDouble() ◦ int ReadInt32() The BinaryWriter method -void Write( any single primitive type argument )
- 35. These two files helps us in setting configurations Machine.Config – Machine level configuration Web.Config – Application level configuration
- 36. Configuration files can be stored in application folders ◦ Configuration system automatically detects changes Hierarchical configuration architecture ◦ Applies to the actual directory and all subdirectories Examples: <compilation defaultLanguage="c#“ debug="true“/> <sessionState> <!--- sessionstate subelements go here --> </sessionState>
Editor's Notes
- Softsmith Infotech
- Softsmith Infotech
- Softsmith Infotech
- Softsmith Infotech
- Softsmith Infotech
- Softsmith Infotech
