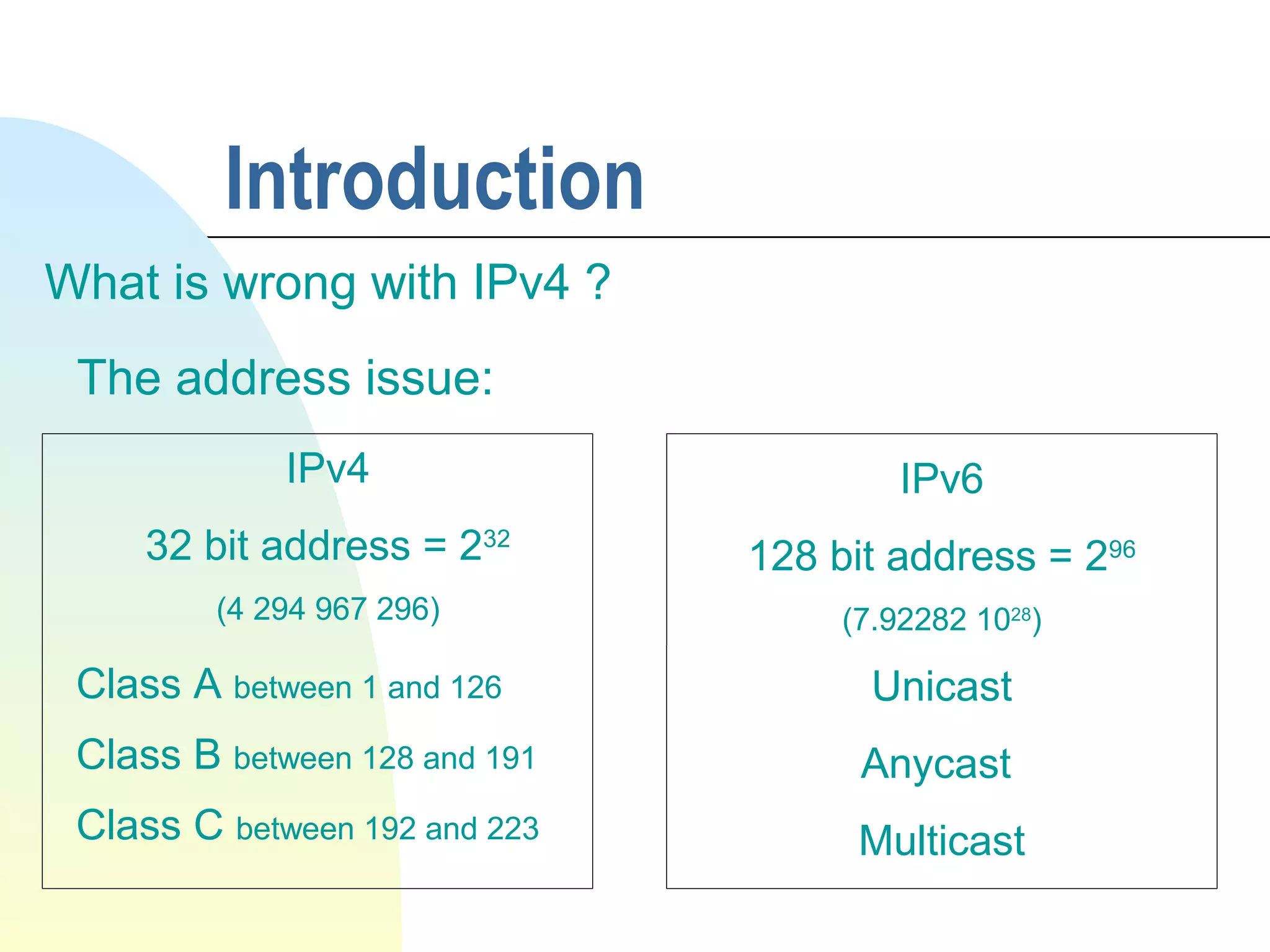
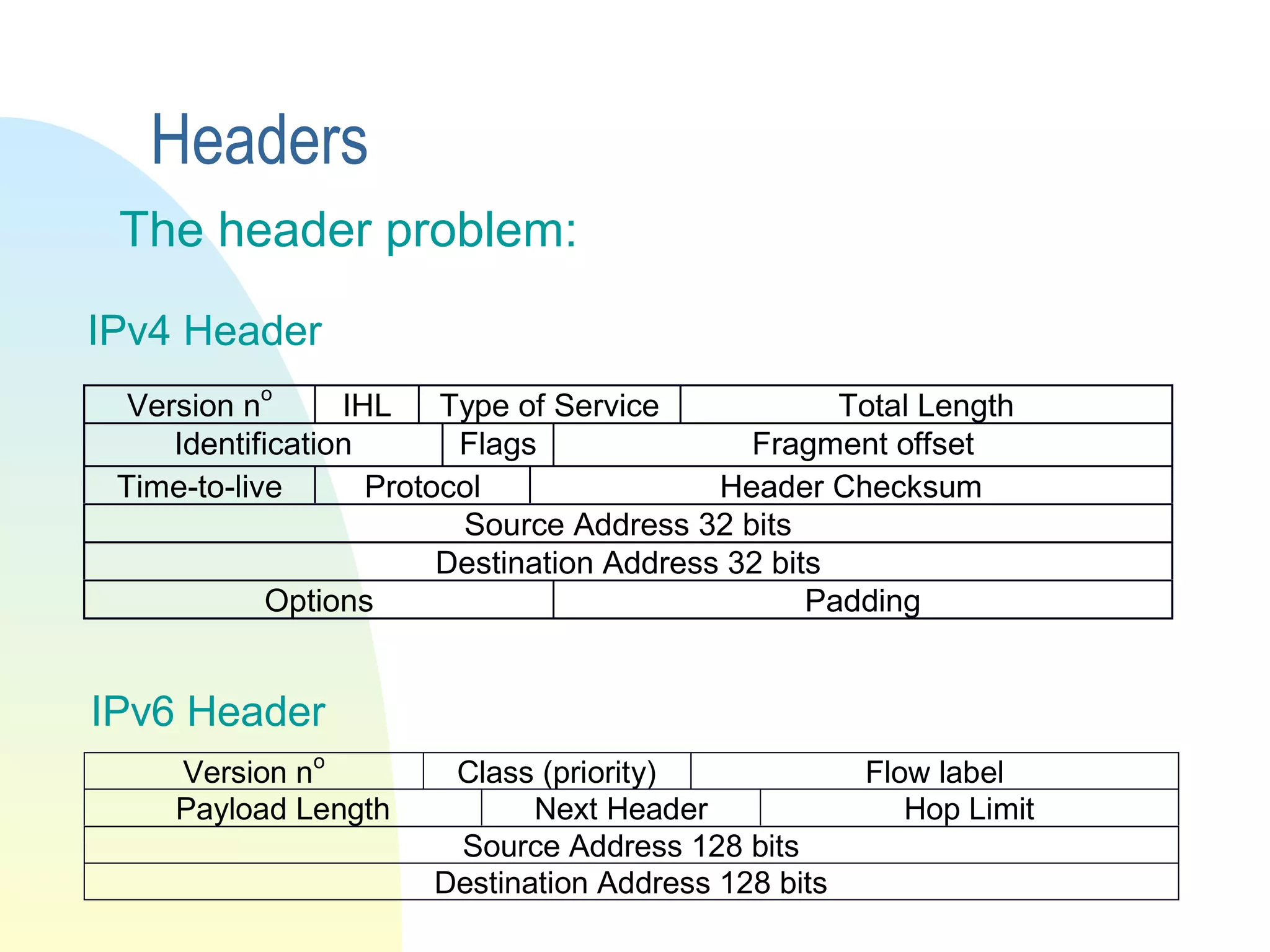
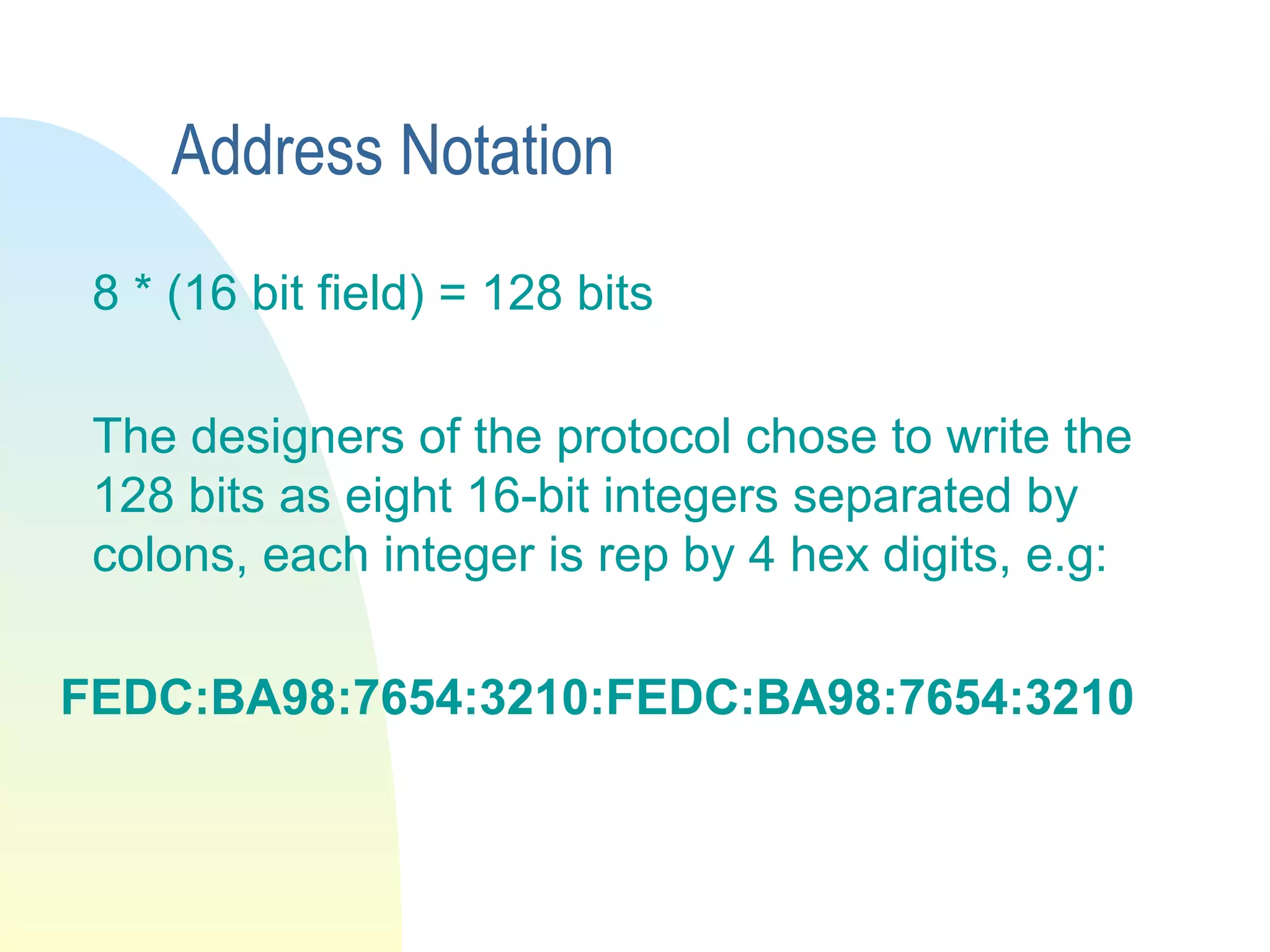
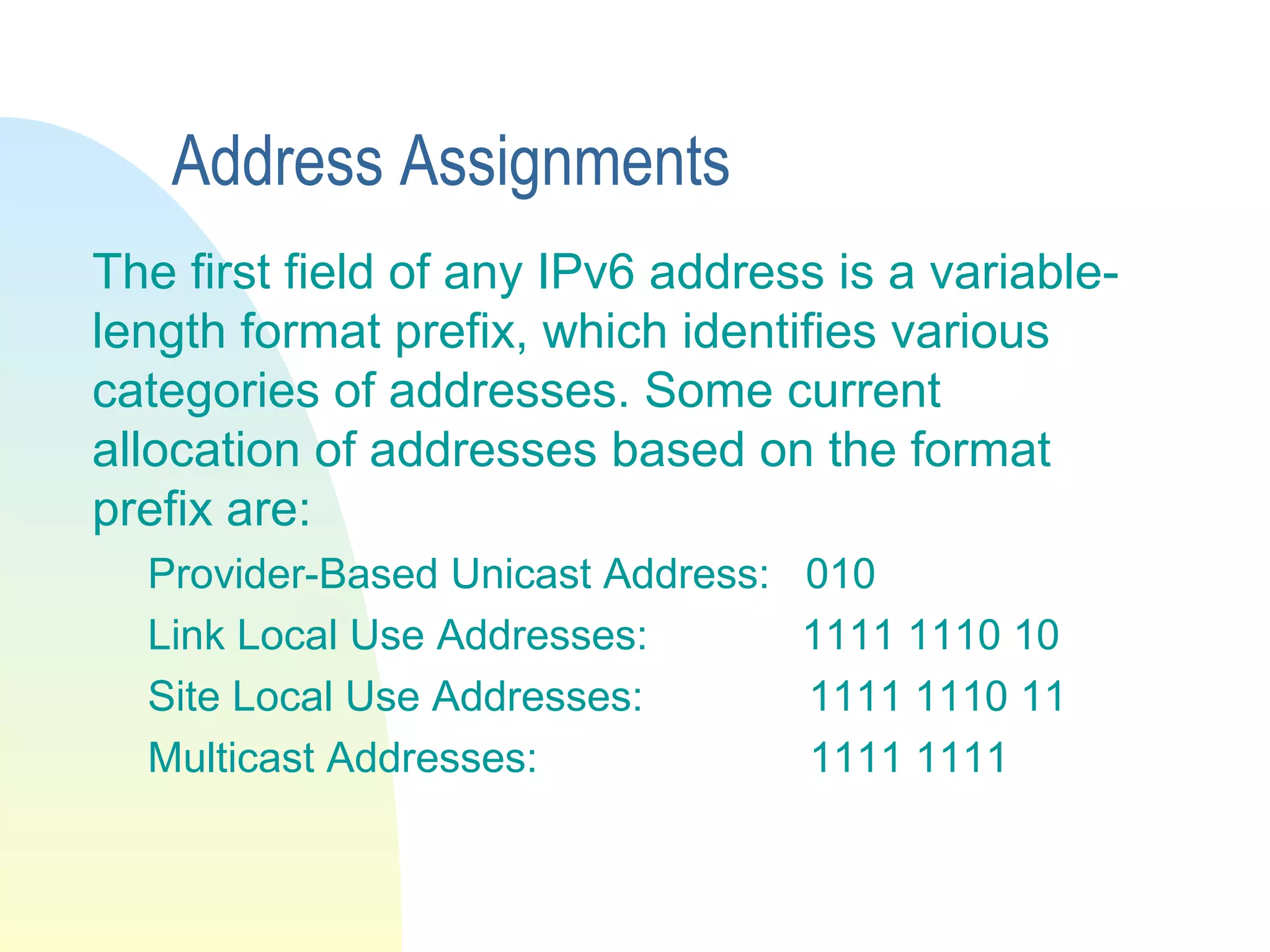
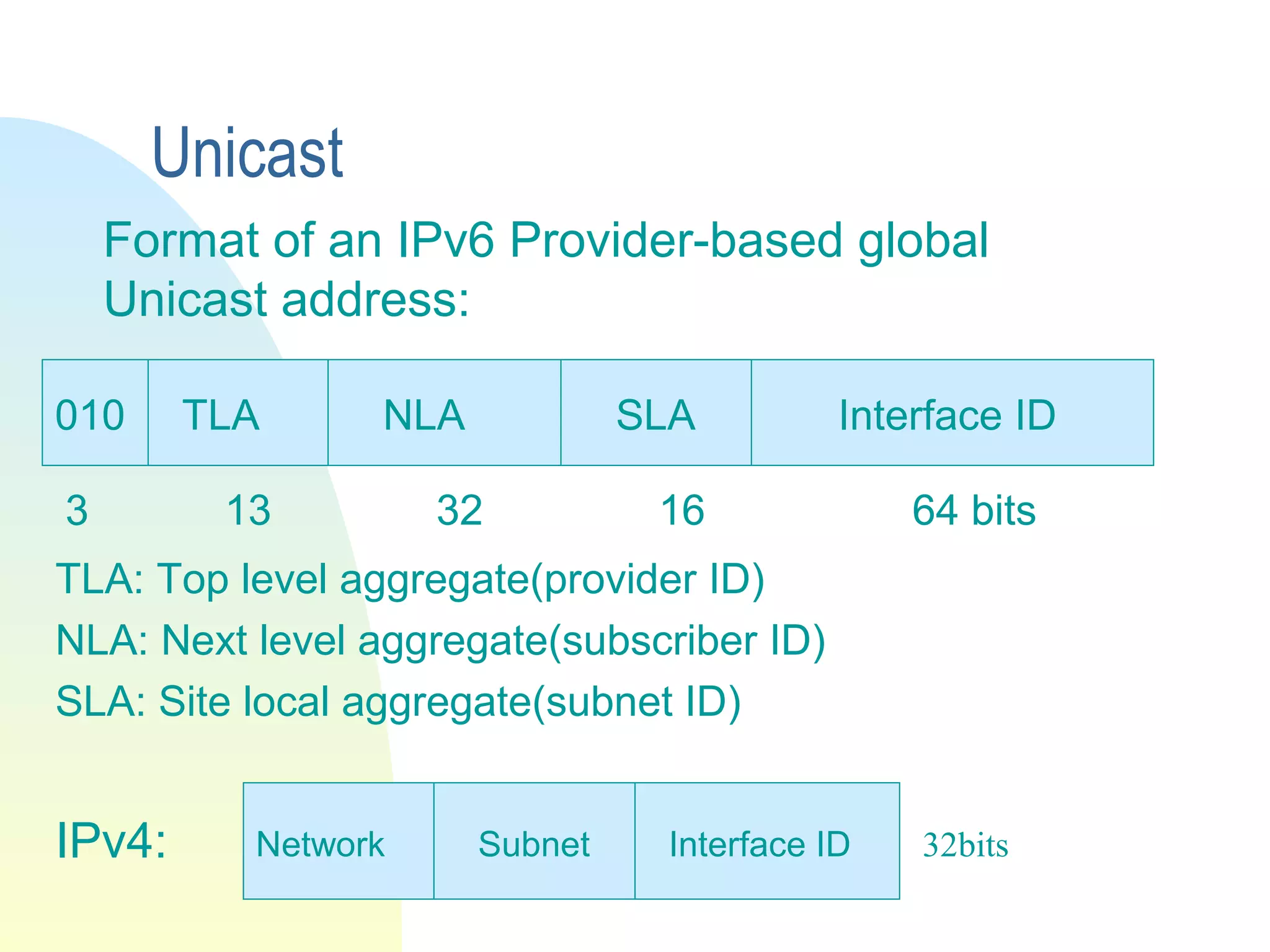
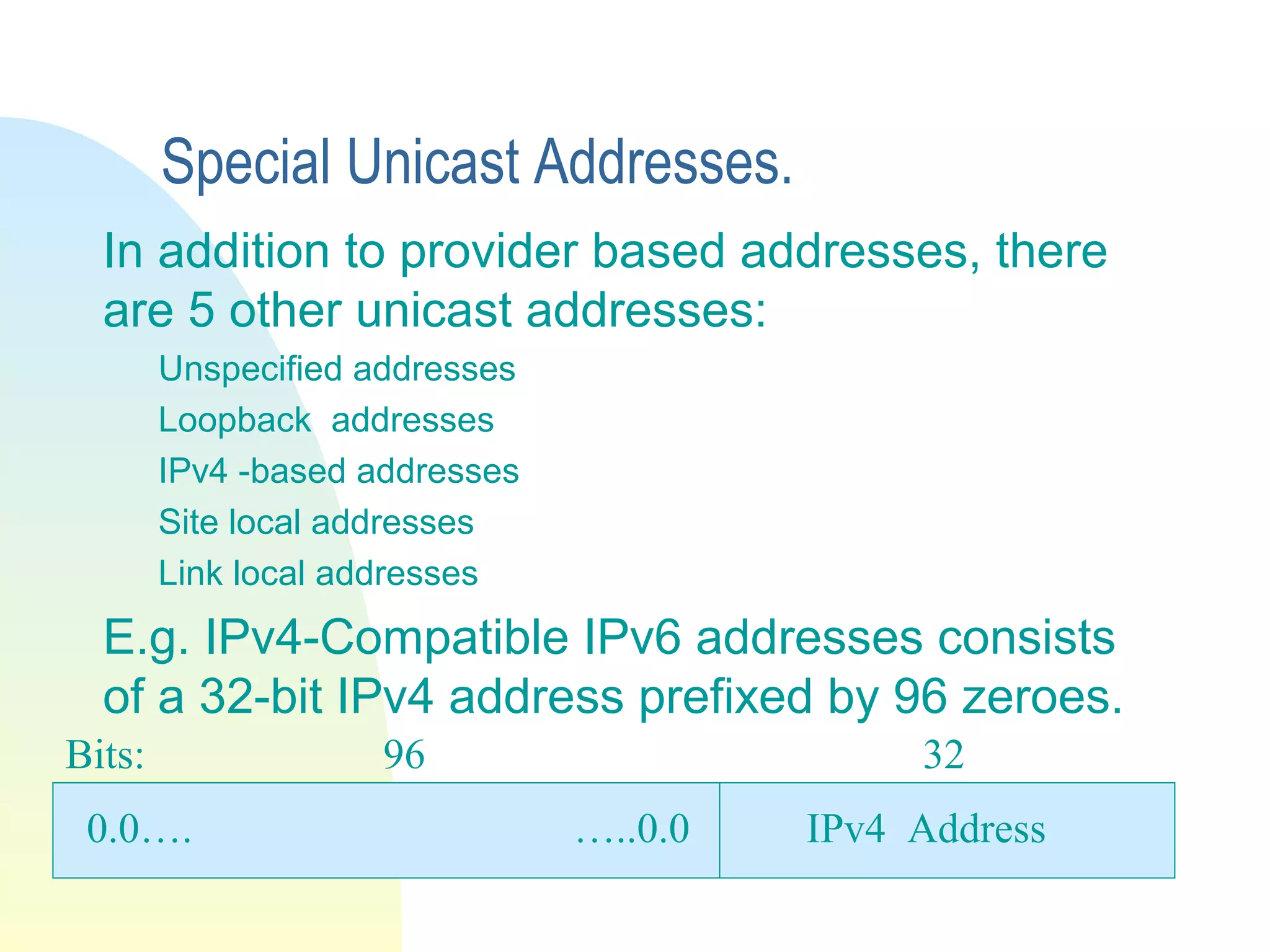
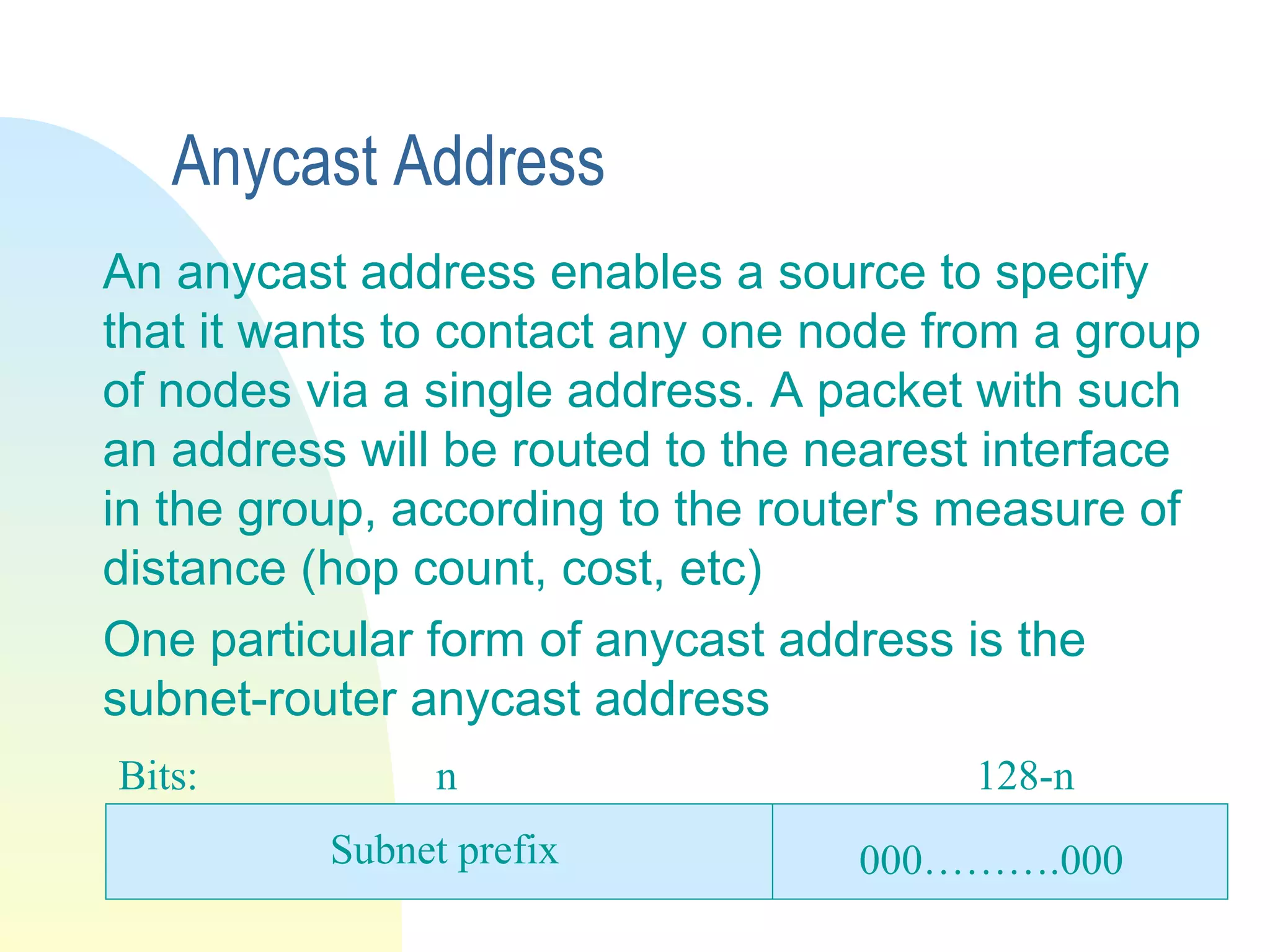
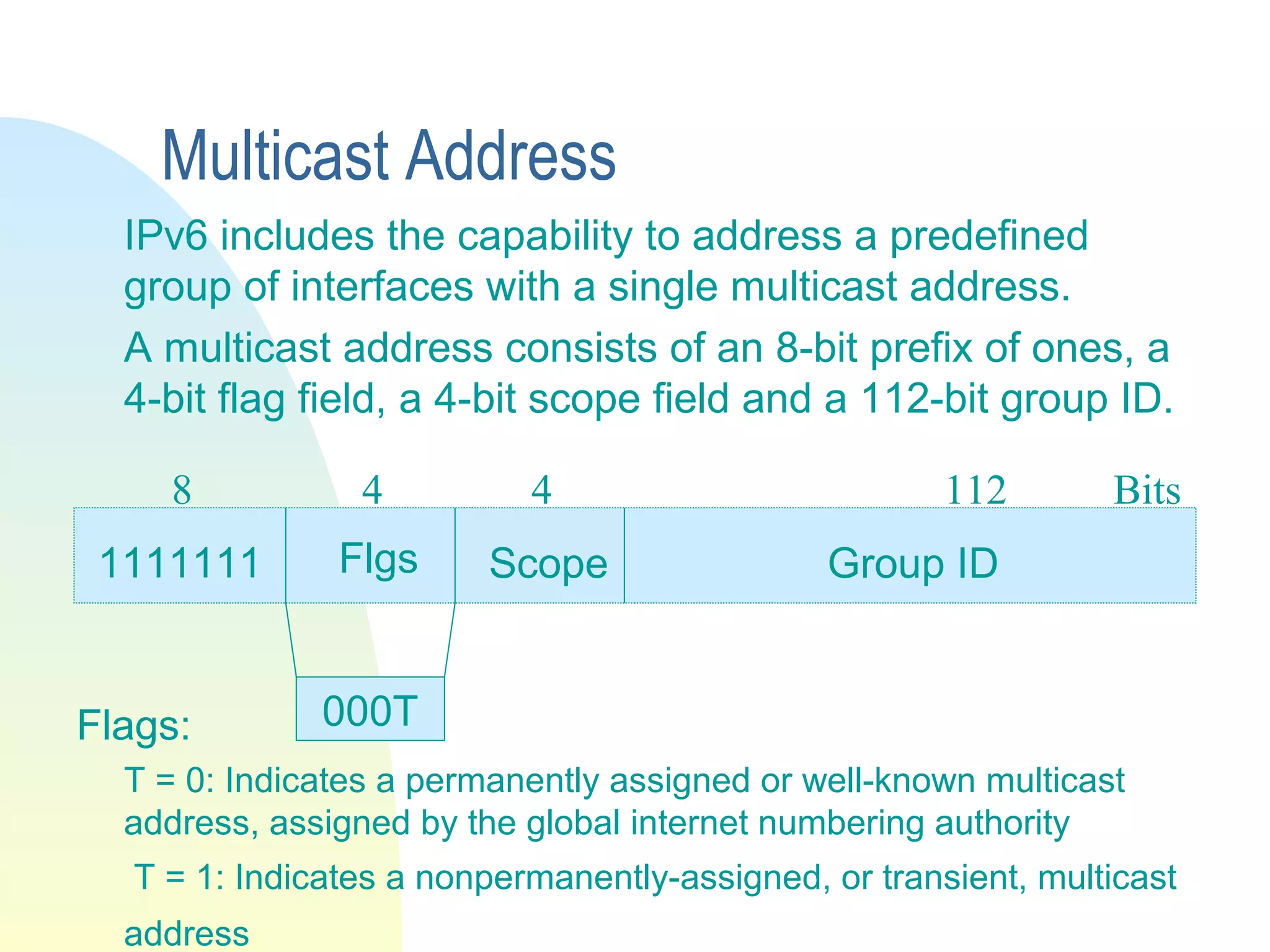
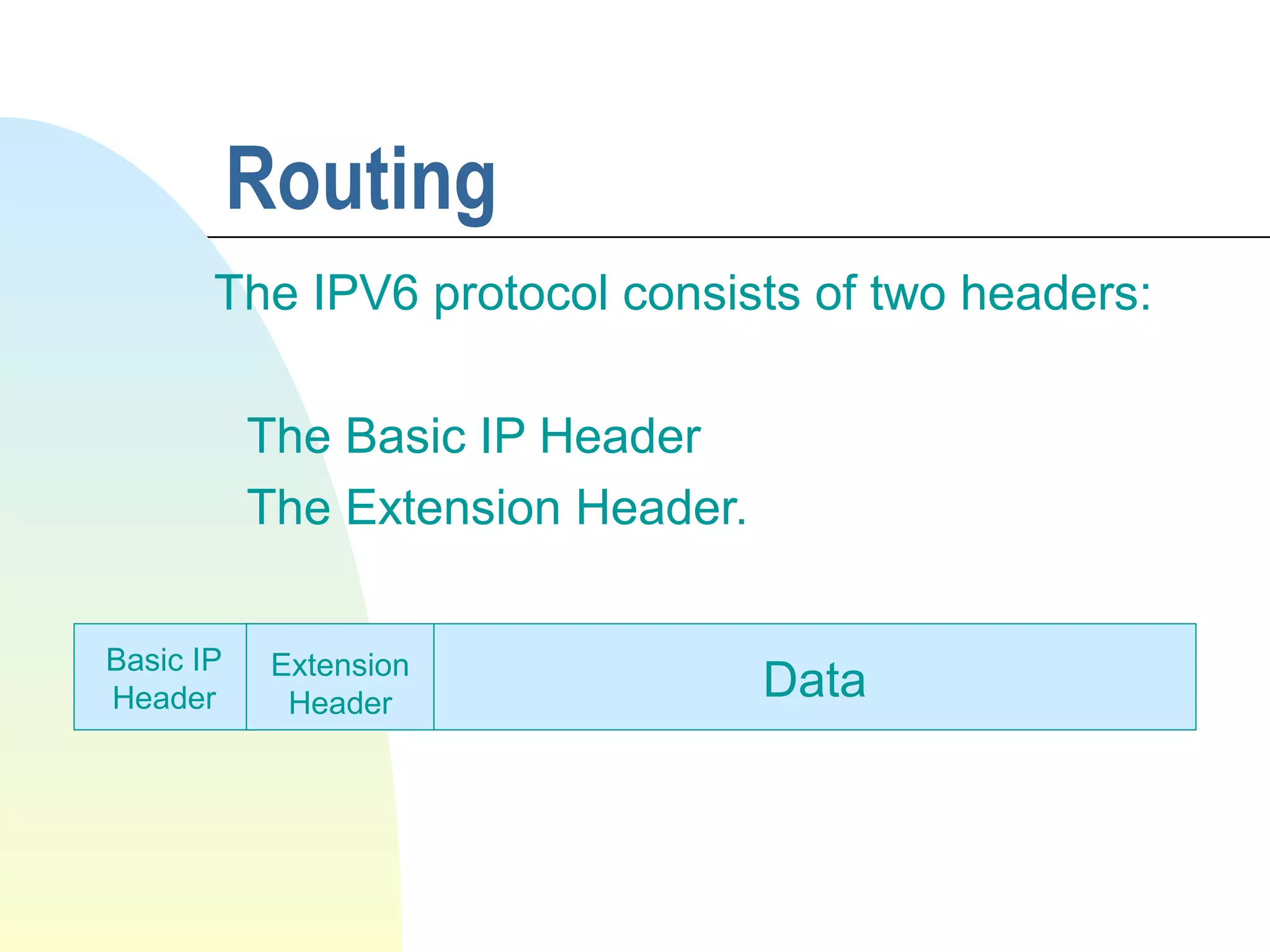
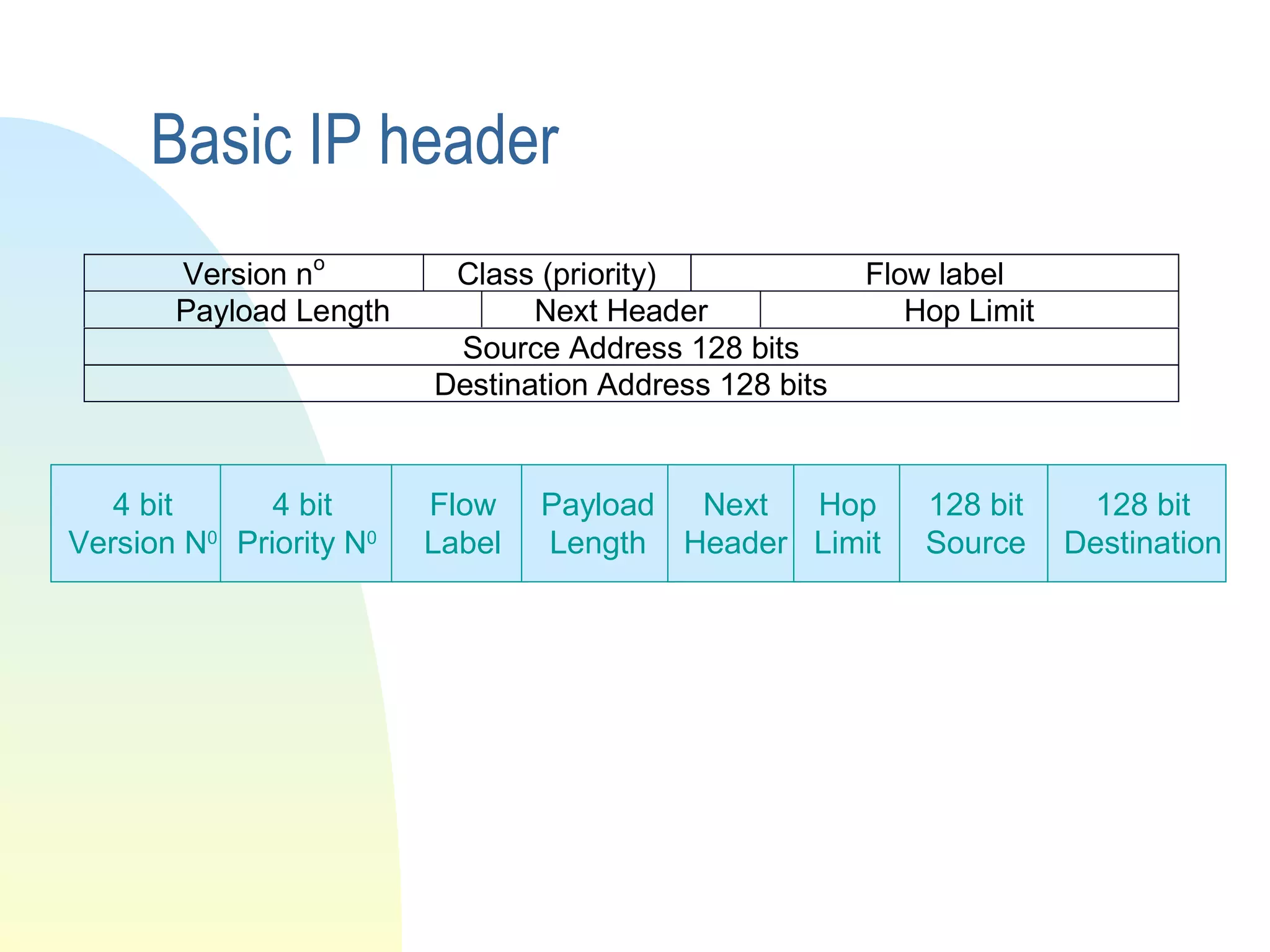
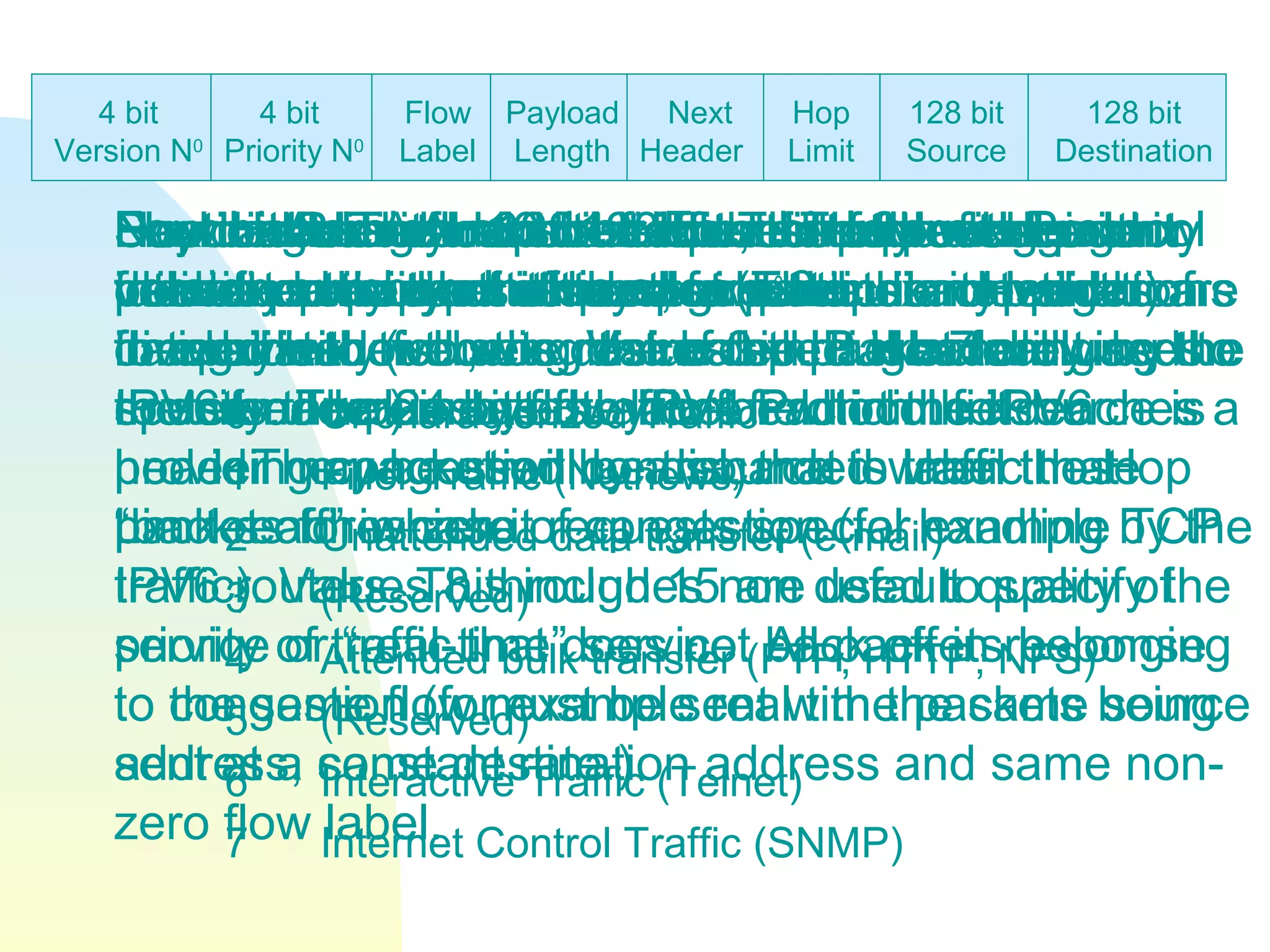
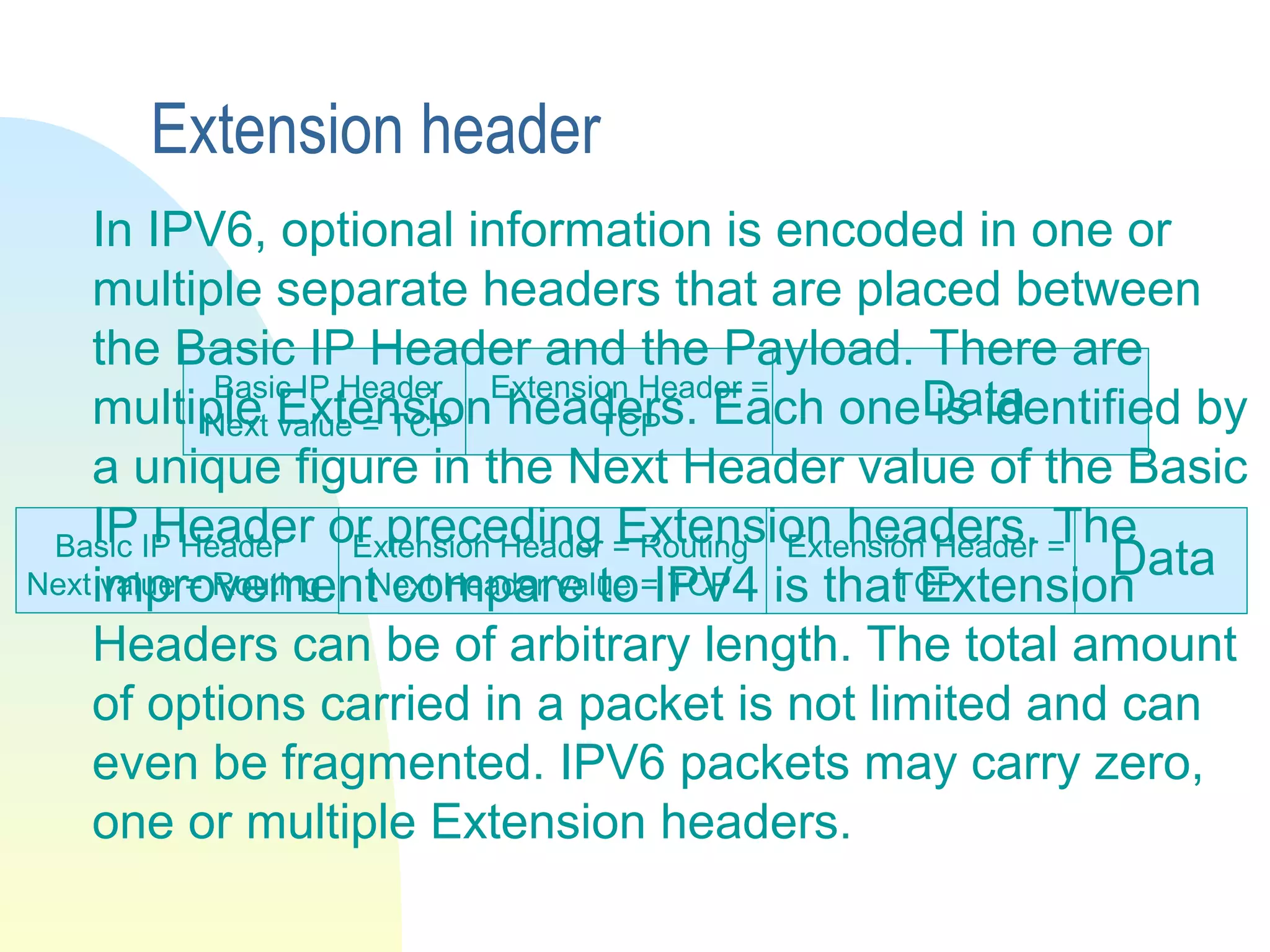
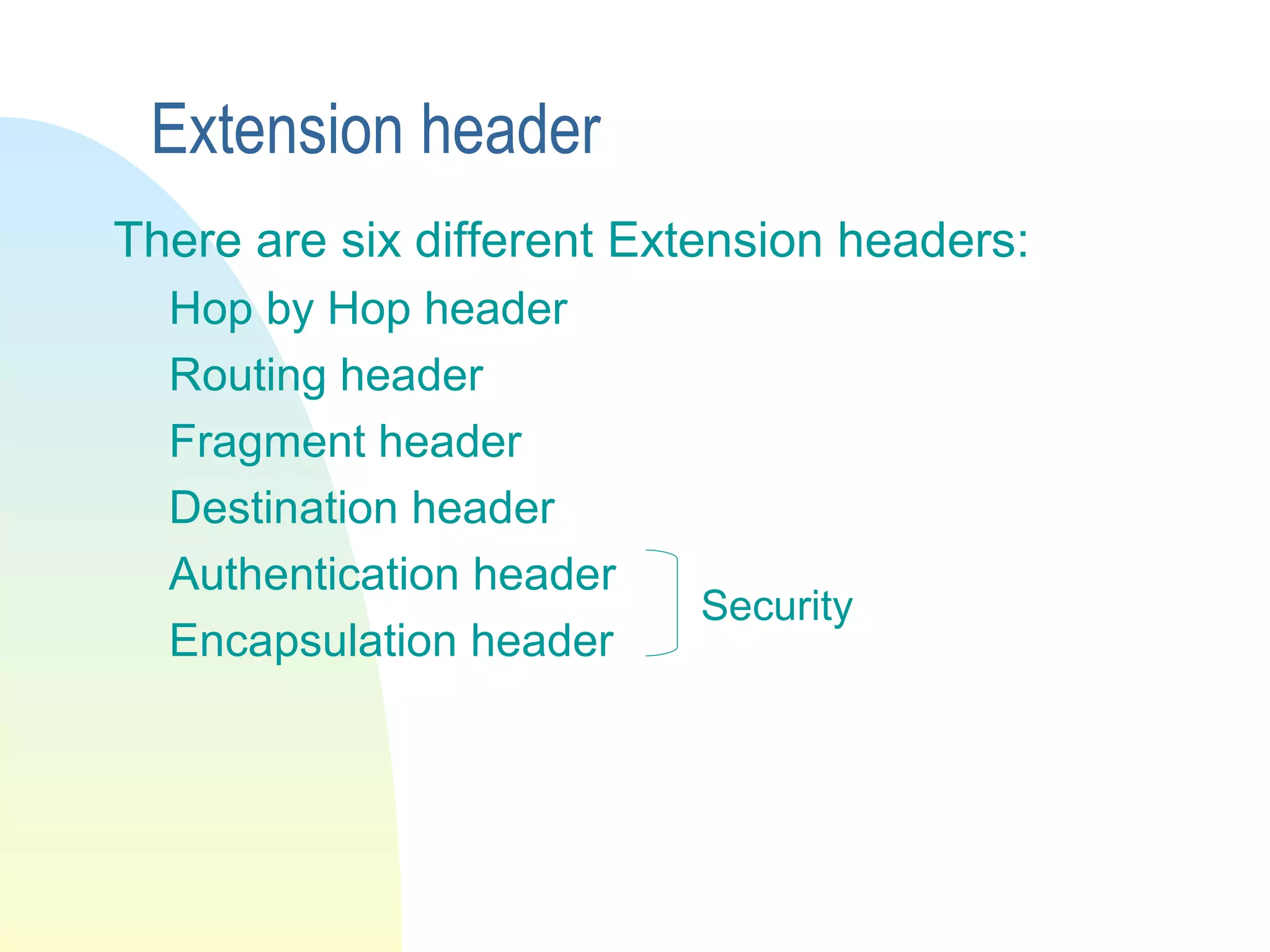
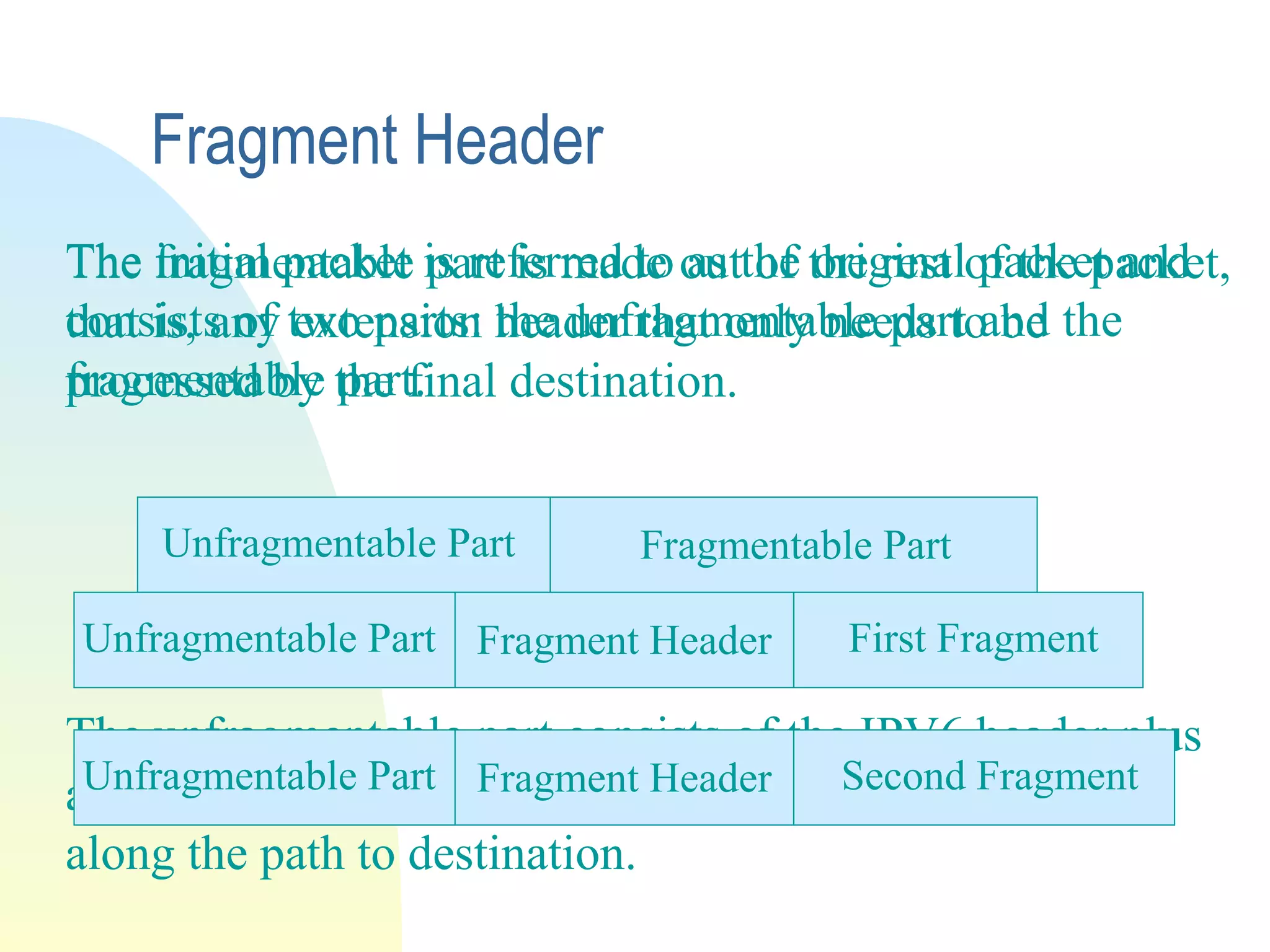
IPv6 was created to address limitations in IPv4 such as addressing space and header format. IPv6 features a 128-bit address providing vastly more unique addresses than IPv4. It simplifies the header format. Extension headers allow for optional information to be included in packets in a flexible way. IPv6 also supports anycast and multicast addressing and provides improvements in security, authentication, and mobility.