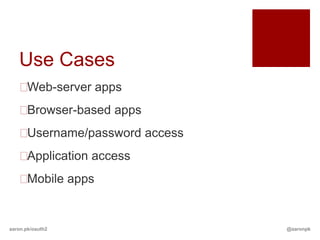
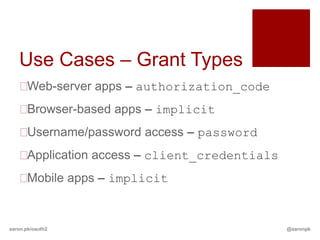
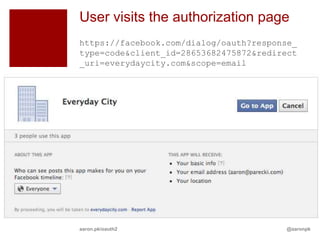
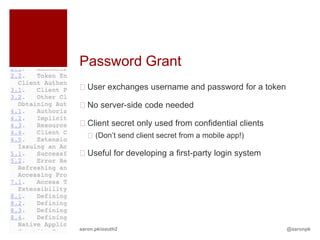
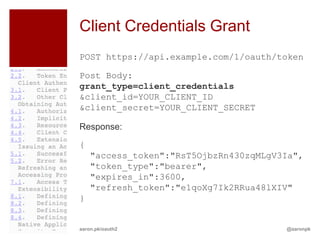
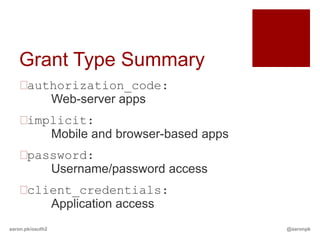
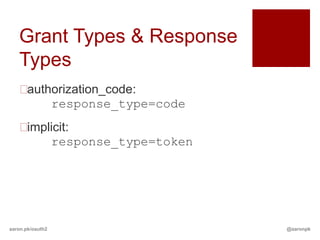
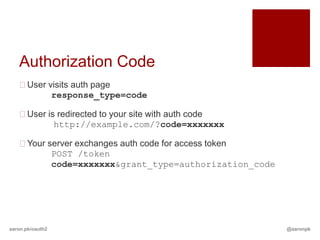
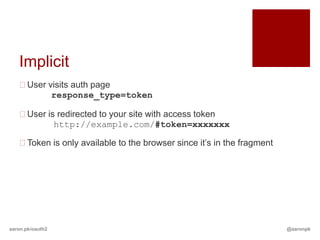
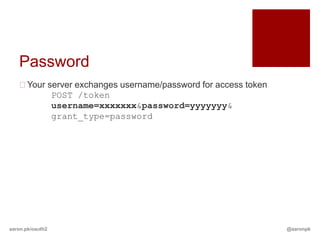
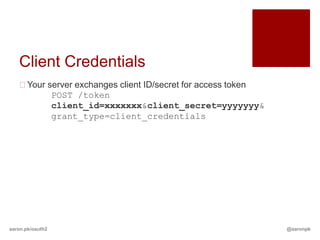
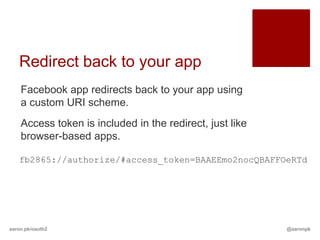
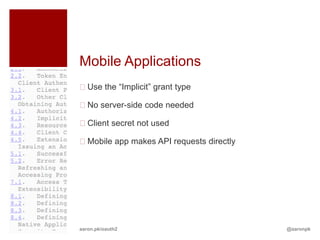
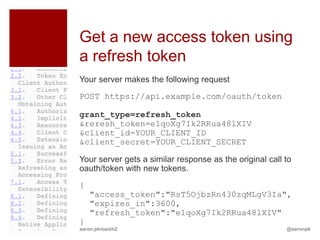
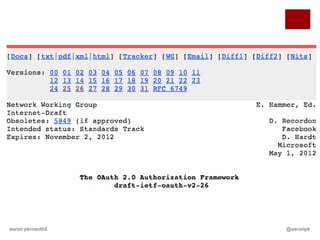
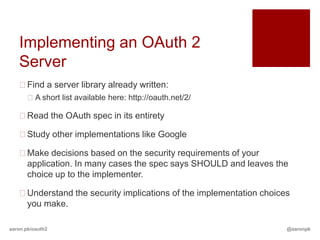
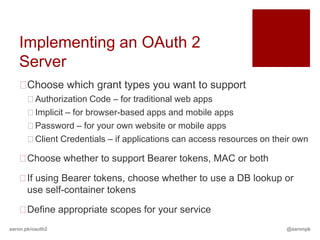
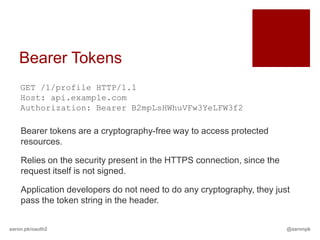
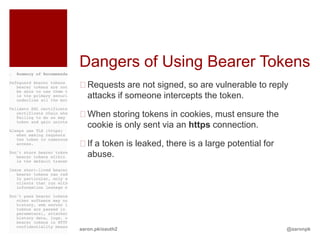
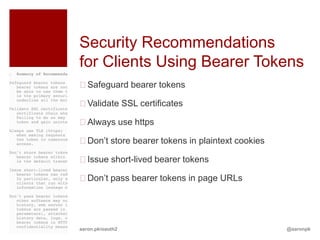
The document discusses OAuth 2.0 and implementing an OAuth 2.0 authorization server. It covers the different grant types (authorization code, implicit, password, client credentials), how each works, and which are best for different client types like web apps, browser-based apps, and mobile apps. It also discusses topics like scopes, limiting access to resources, accessing protected resources with an access token, and refreshing expired access tokens. The document provides guidance on implementing an OAuth 2.0 server including choosing library, grant types, token types, and defining scopes.
























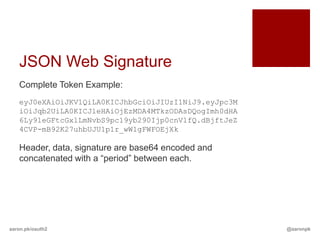
![DB Token Lookups vs
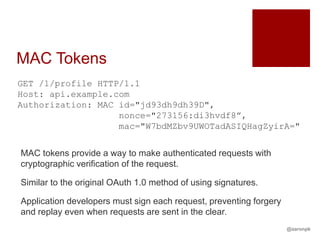
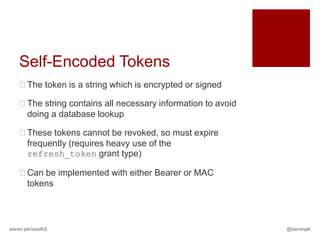
Self-Encoded Tokens
Token table probably looks like
Token
User ID
Expiration Date
Scopes
Instead, encode that into a JSON payload which *is*
the token:
{“user_id”:1000,”exp”:1355429676,”scopes”:[“email
”,”payment”]}
See JSON Web Signature for example of signing this
token
aaron.pk/oauth2 @aaronpk](https://image.slidesharecdn.com/thestateofoauth2-130110185015-phpapp01/85/The-State-of-OAuth2-78-320.jpg)
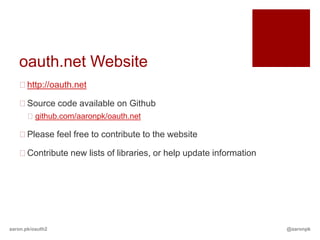
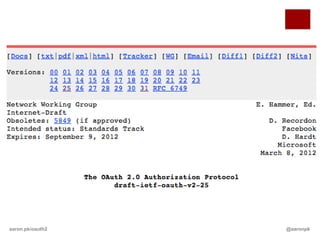
![JSON Web Signature
http://tools.ietf.org/html/draft-ietf-jose-json-web-signature-07
Data Base64 Encoded
{
"typ":"JWT", eyJ0eXAiOiJKV1QiLA0KICJhbGciOiJIUzI1NiJ9
"alg":"HS256”
}
{
"usr":"username", eyJpc3MiOiJqb2UiLA0KICJleHAiOjEzMDA4MT
"exp":1300819380, kzODAsDQogImh0dHA6Ly9leGFtcGxlLmNvbS9p
"scope":["profile"] c19yb290Ijp0cnVlfQ
}
Signature dBjftJeZ4CVP-mB92K27uhbUJU1p1r_wW1gFWFOE
aaron.pk/oauth2 @aaronpk](https://image.slidesharecdn.com/thestateofoauth2-130110185015-phpapp01/85/The-State-of-OAuth2-79-320.jpg)