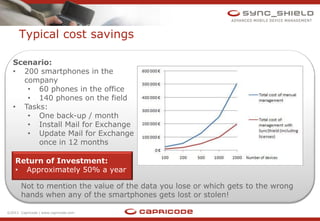
SyncShield is an unrivaled cross-platform mobile device management solution that allows IT personnel to manage an entire fleet of devices from a central location without user involvement. It provides efficient management of device security, applications, and settings while supporting over 90% of smartphones. SyncShield allows companies to save approximately 50% of costs associated with mobile device management annually.