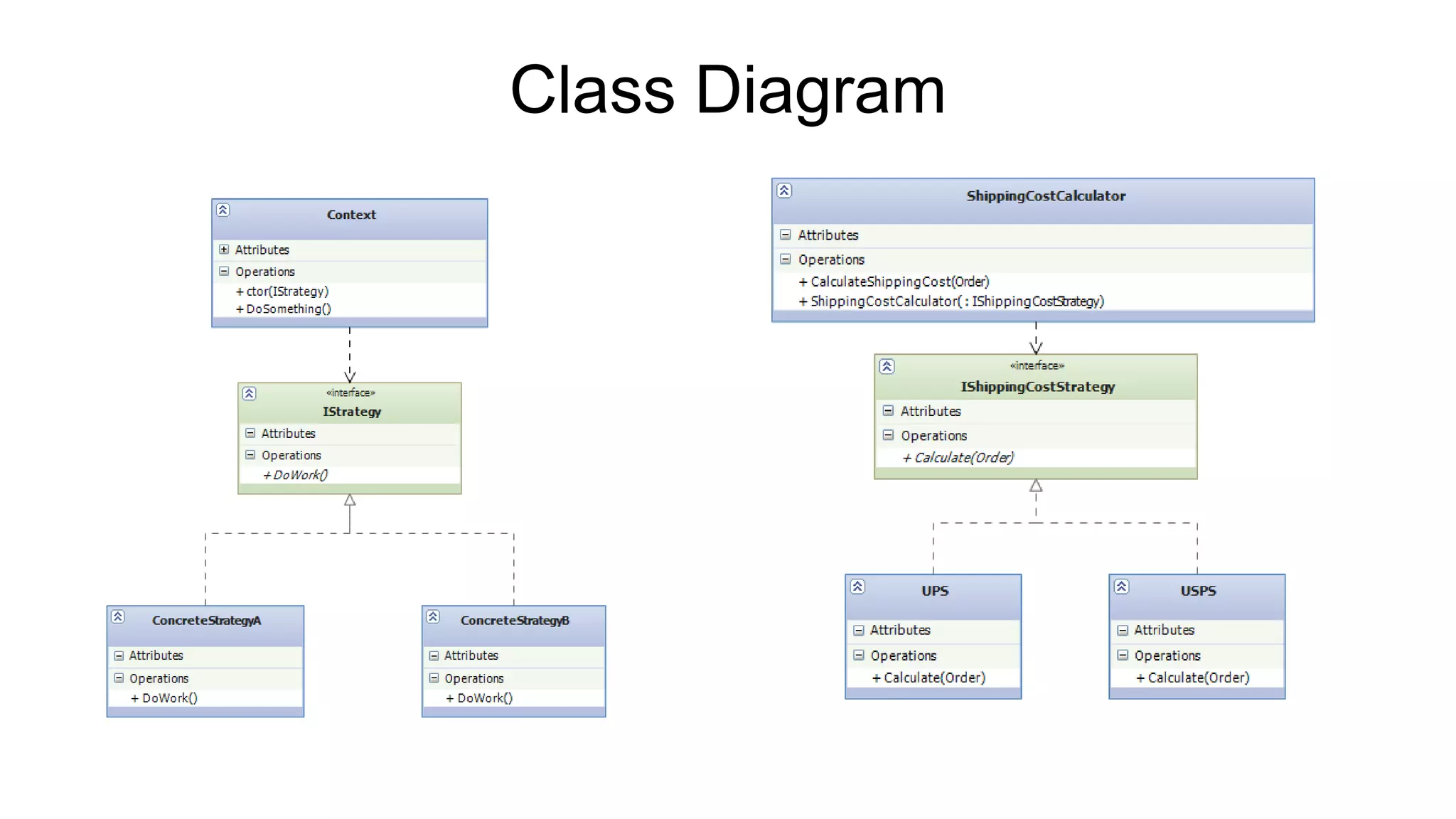
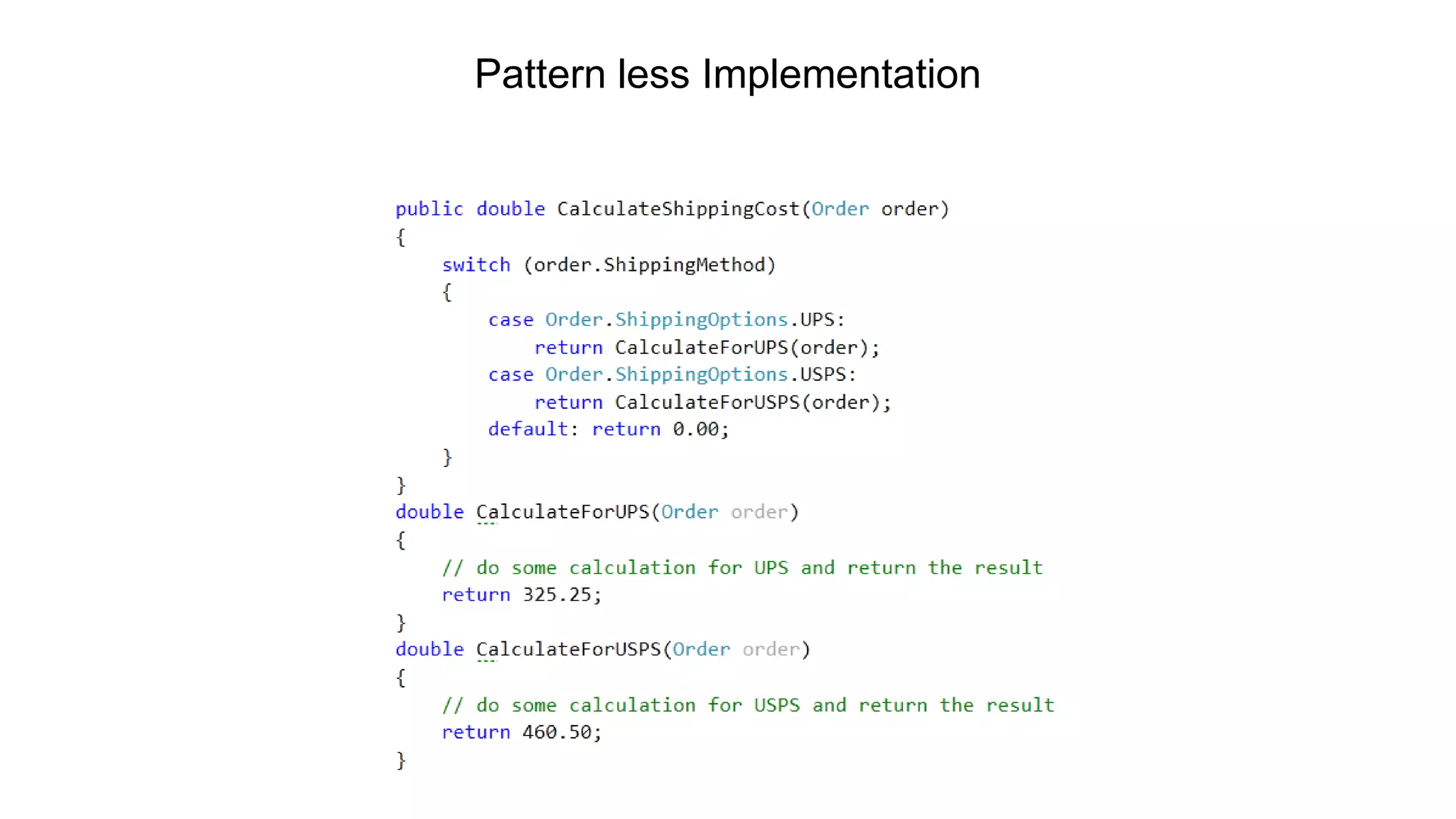
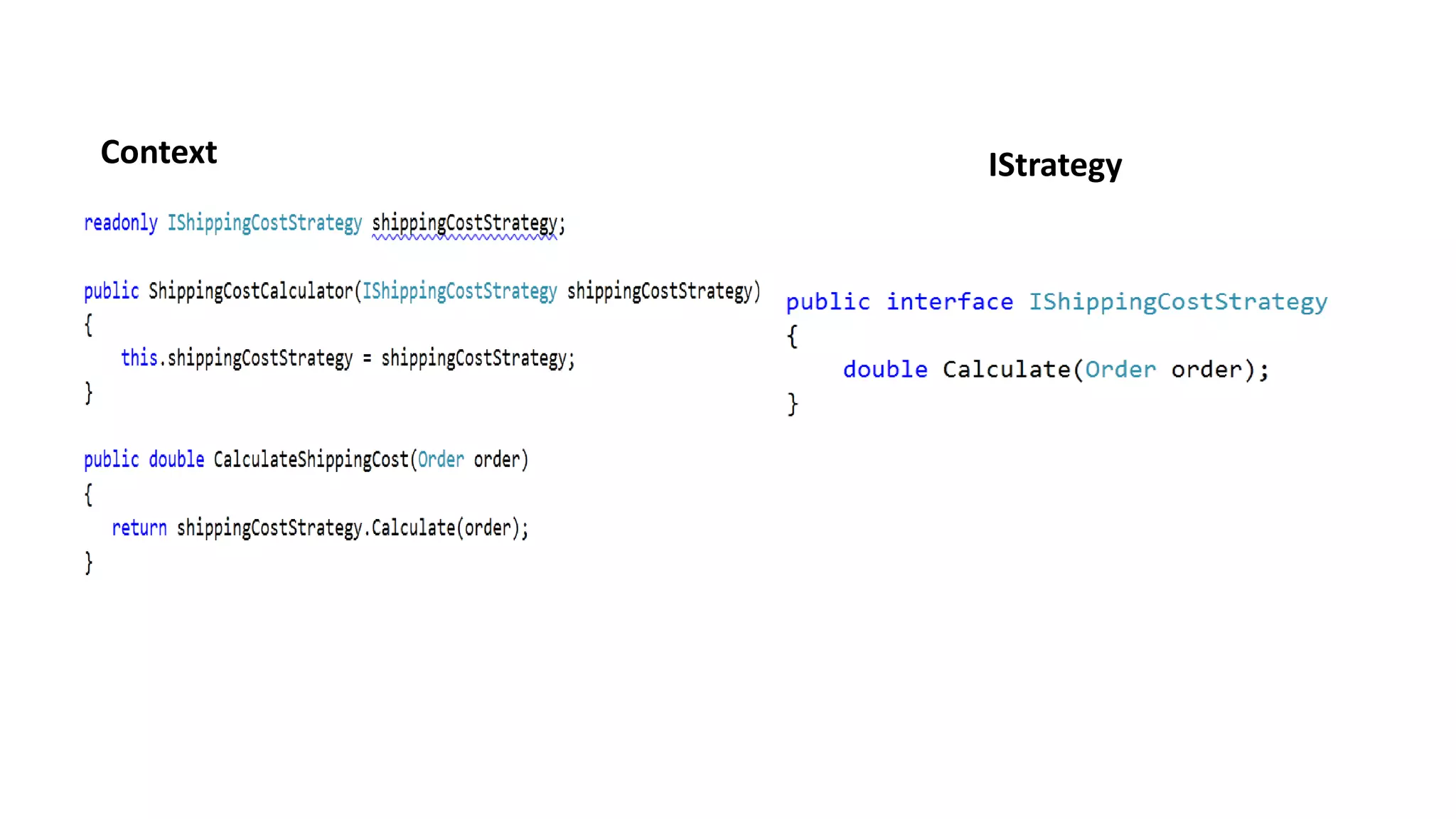
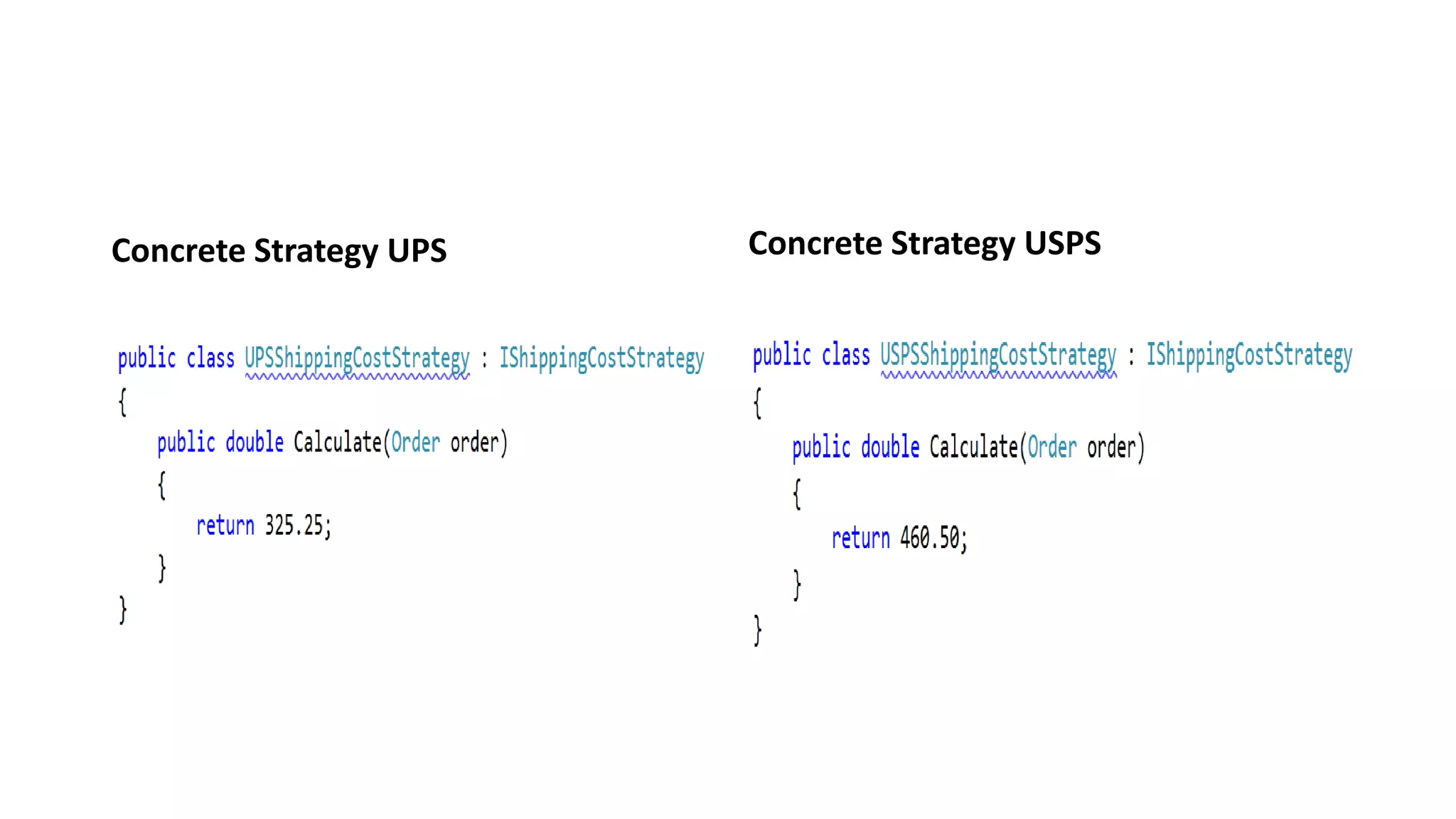
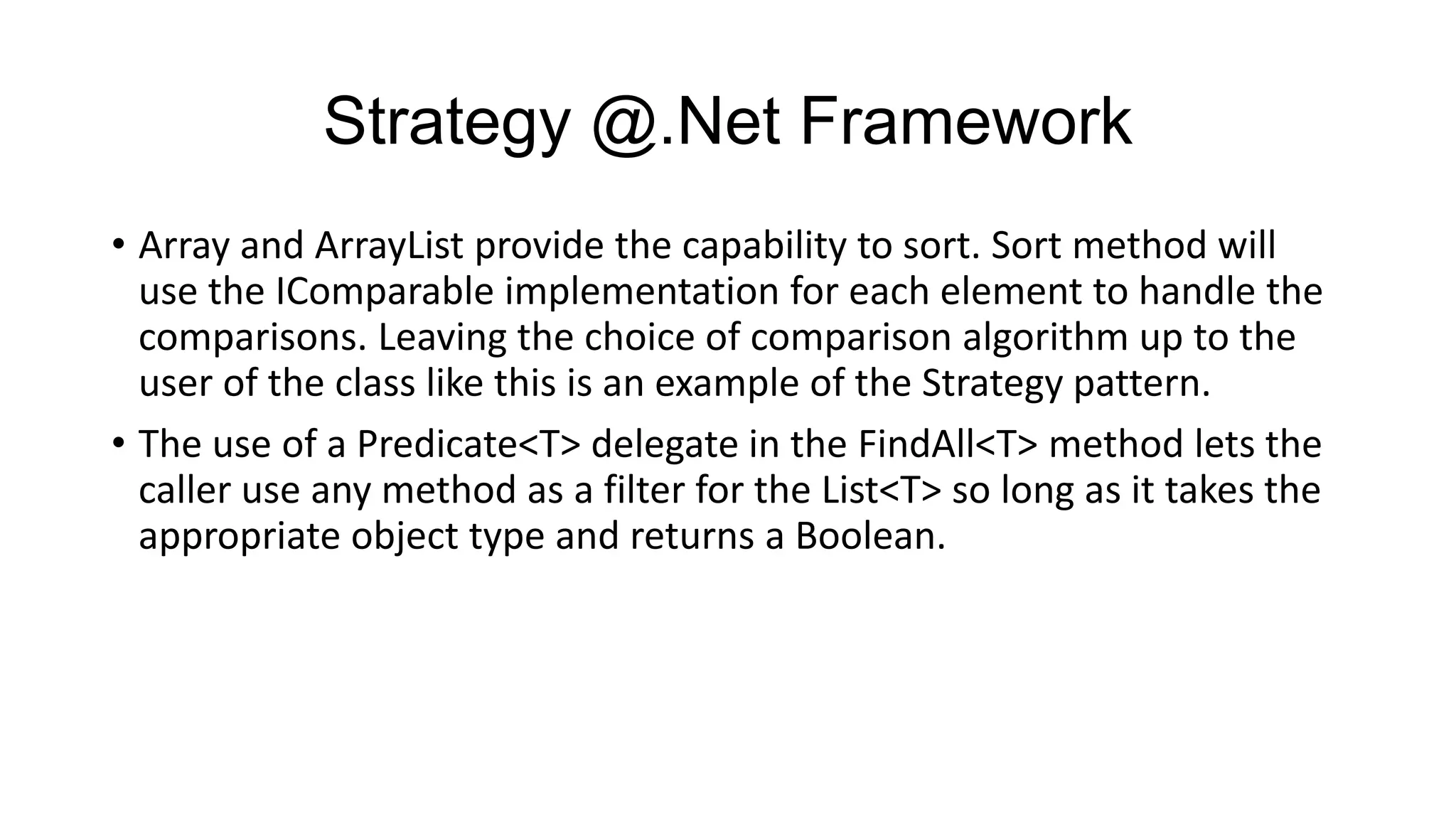
The document discusses the strategy pattern, which allows selecting algorithms or behaviors at runtime. It defines a family of algorithms, encapsulates each one, and makes them interchangeable. The strategy pattern is useful when wanting to choose algorithms dynamically, like for sorting or file compression. It keeps classes focused on a single purpose by extracting conditional logic into strategy objects. The document provides examples of how the strategy pattern can be implemented and used, such as for a robot identifying different objects or relationships.