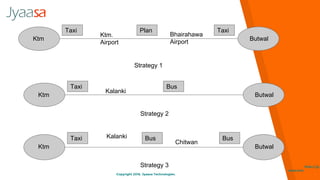
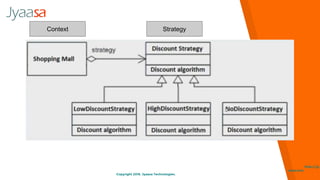
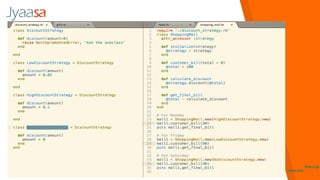
The document explains the strategy pattern, a design pattern in software that allows for the selection of an algorithm's behavior at runtime. It encapsulates a family of algorithms, making them interchangeable and suggesting their use in scenarios like calculating discounts in a shopping mall. Additionally, it emphasizes the open-closed principle, advocating for separable logic to enhance reusability and maintainability.