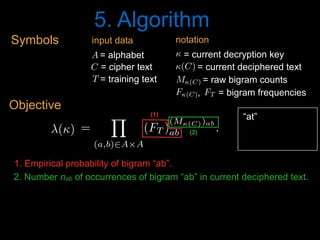
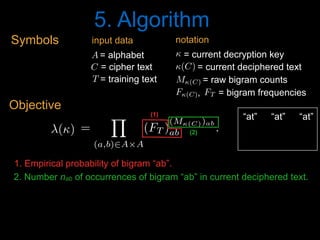
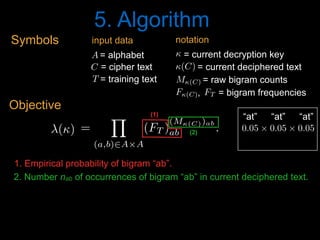
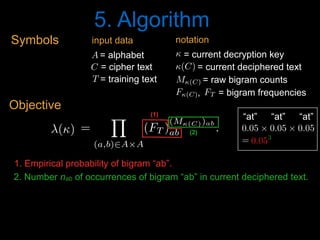
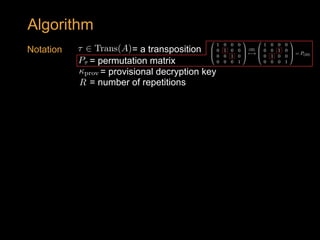
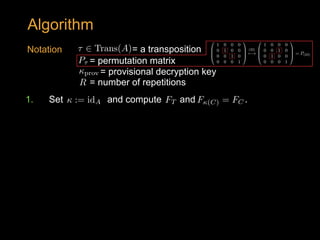
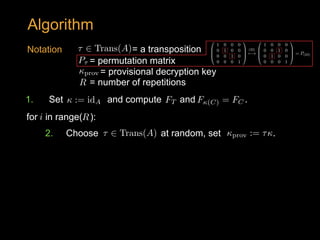
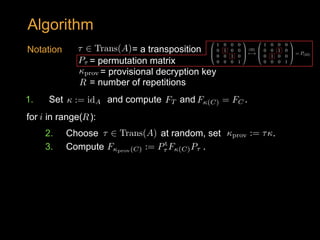
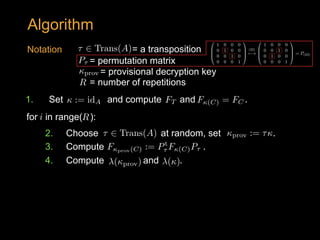
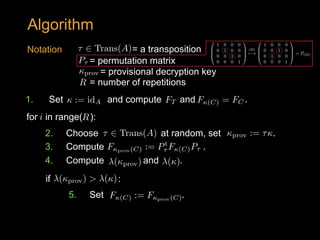
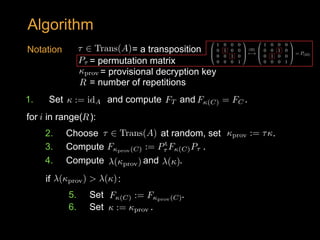
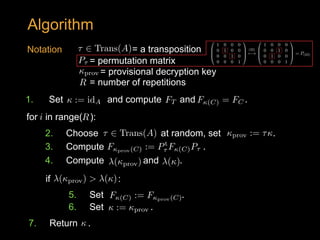
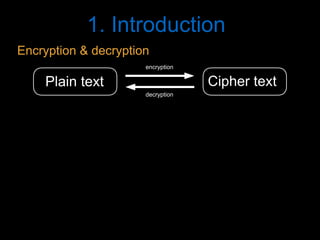
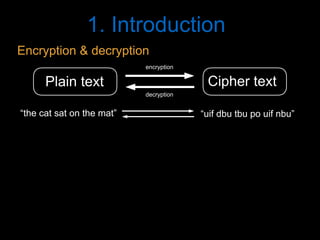
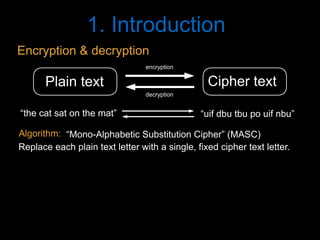
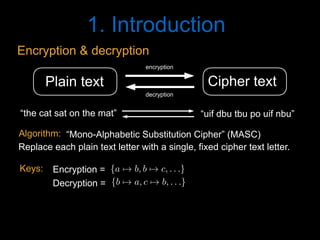
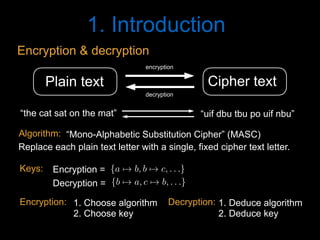
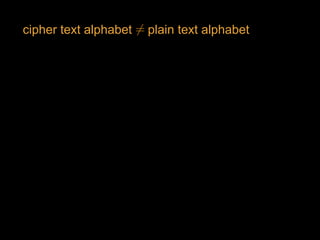
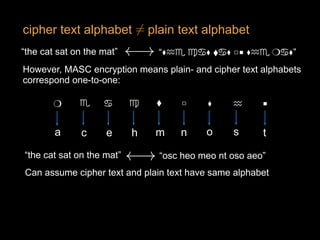
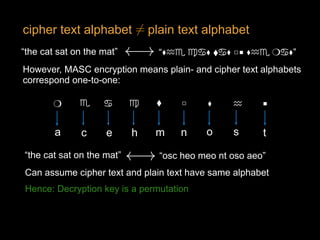
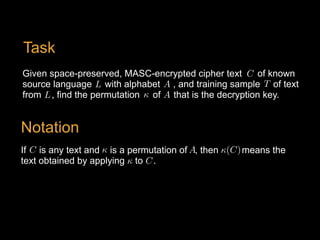
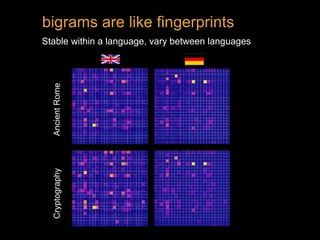
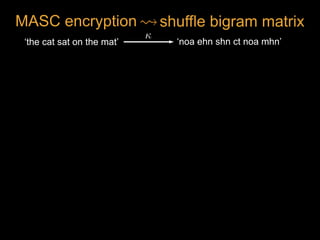
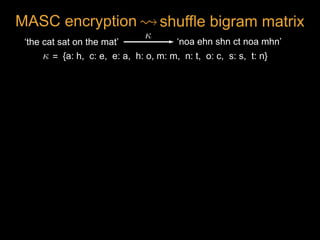
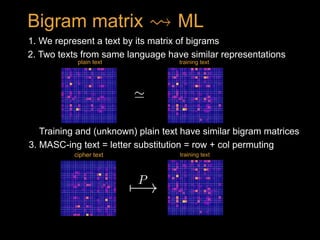
The document discusses solving simple substitution ciphers algorithmically, highlighting the challenge of decrypting historical texts like the Voynich manuscript. It introduces mono-alphabetic substitution ciphers and outlines methods for encryption and decryption involving fixed letter replacements. The content serves primarily as an educational overview rather than original research.


![(1234) = (34)(24)(14)
(1234)
[1, 2, 3, 4] [2, 3, 4, 1]
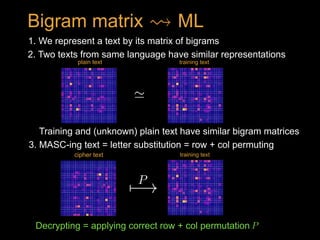
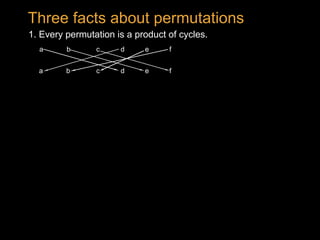
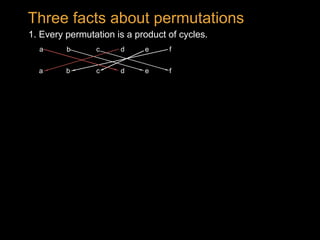
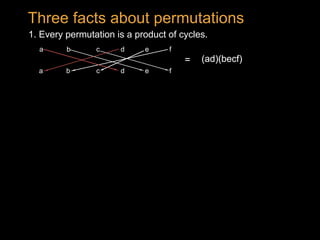
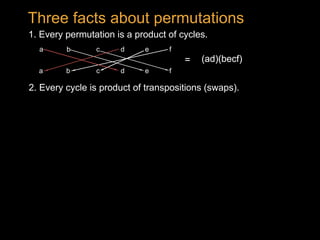
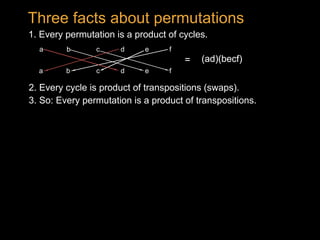
1. Every permutation is a product of cycles.
2. Every cycle is product of transpositions (swaps).
Three facts about permutations
Example:
3. So: Every permutation is a product of transpositions.
(ad)(becf)=
a b dc
a b dc
e f
fe](https://image.slidesharecdn.com/pydata2018masctalk-180723181103/85/Solving-very-simple-substitution-ciphers-algorithmically-Stephen-Enright-Ward-91-320.jpg)
![(1234) = (34)(24)(14)
(1234)
[1, 2, 3, 4] [2, 3, 4, 1]
[4, 2, 3, 1]
(14)
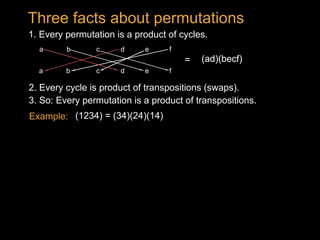
1. Every permutation is a product of cycles.
2. Every cycle is product of transpositions (swaps).
Three facts about permutations
Example:
3. So: Every permutation is a product of transpositions.
(ad)(becf)=
a b dc
a b dc
e f
fe](https://image.slidesharecdn.com/pydata2018masctalk-180723181103/85/Solving-very-simple-substitution-ciphers-algorithmically-Stephen-Enright-Ward-92-320.jpg)
![(1234) = (34)(24)(14)
(1234)
[1, 2, 3, 4] [2, 3, 4, 1]
[4, 2, 3, 1]
(14)
[2, 4, 3, 1]
(24)
1. Every permutation is a product of cycles.
2. Every cycle is product of transpositions (swaps).
Three facts about permutations
Example:
3. So: Every permutation is a product of transpositions.
(ad)(becf)=
a b dc
a b dc
e f
fe](https://image.slidesharecdn.com/pydata2018masctalk-180723181103/85/Solving-very-simple-substitution-ciphers-algorithmically-Stephen-Enright-Ward-93-320.jpg)
![(1234) = (34)(24)(14)
(1234)
[1, 2, 3, 4] [2, 3, 4, 1]
[4, 2, 3, 1]
(14)
[2, 4, 3, 1]
(24)
(34)
1. Every permutation is a product of cycles.
2. Every cycle is product of transpositions (swaps).
Three facts about permutations
Example:
3. So: Every permutation is a product of transpositions.
(ad)(becf)=
a b dc
a b dc
e f
fe](https://image.slidesharecdn.com/pydata2018masctalk-180723181103/85/Solving-very-simple-substitution-ciphers-algorithmically-Stephen-Enright-Ward-94-320.jpg)
![(1234) = (34)(24)(14)
(1234)
[1, 2, 3, 4] [2, 3, 4, 1]
[4, 2, 3, 1]
(14)
[2, 4, 3, 1]
(24)
(34)
1. Every permutation is a product of cycles.
2. Every cycle is product of transpositions (swaps).
Three facts about permutations
Example:
3. So: Every permutation is a product of transpositions.
(ad)(becf)=
a b dc
a b dc
e f
fe
In general: (a b … z) = (y z)(x z) … (b z)(a z)](https://image.slidesharecdn.com/pydata2018masctalk-180723181103/85/Solving-very-simple-substitution-ciphers-algorithmically-Stephen-Enright-Ward-95-320.jpg)