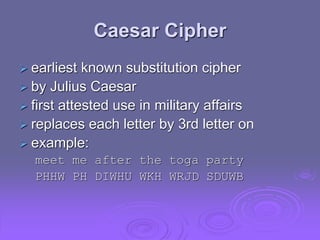
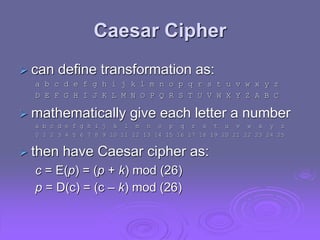
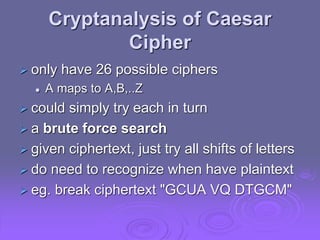
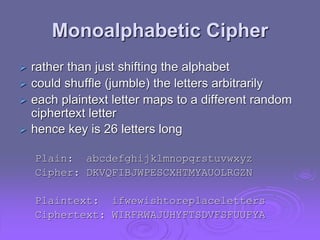
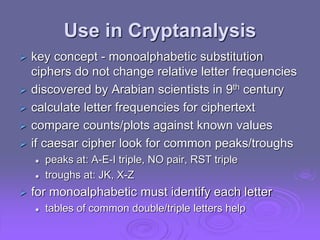
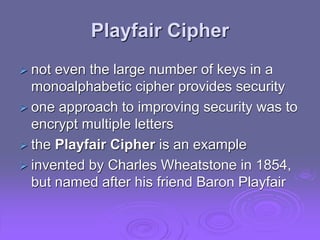
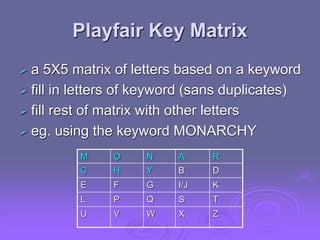
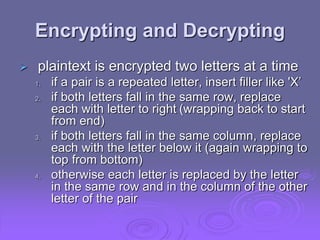
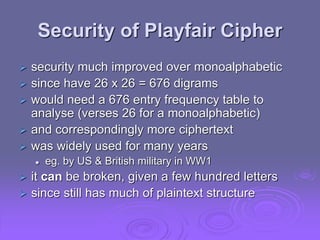
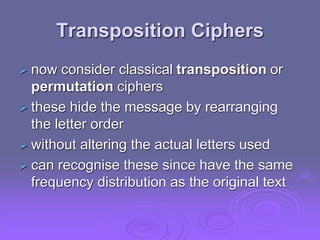
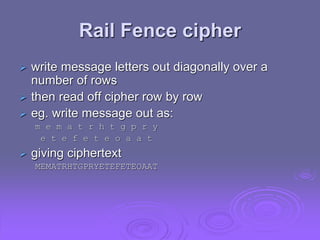
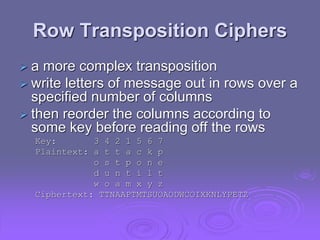
The document discusses various classical encryption techniques including monoalphabetic substitution ciphers like the Caesar cipher and polyalphabetic ciphers. It also covers the Playfair cipher, which encrypts pairs of letters, and transposition ciphers that rearrange letter order. More complex ciphers discussed are product ciphers using both substitution and transposition, and rotor machines like the Enigma that implemented complex varying substitution. Steganography is also mentioned as an alternative approach of hiding information.