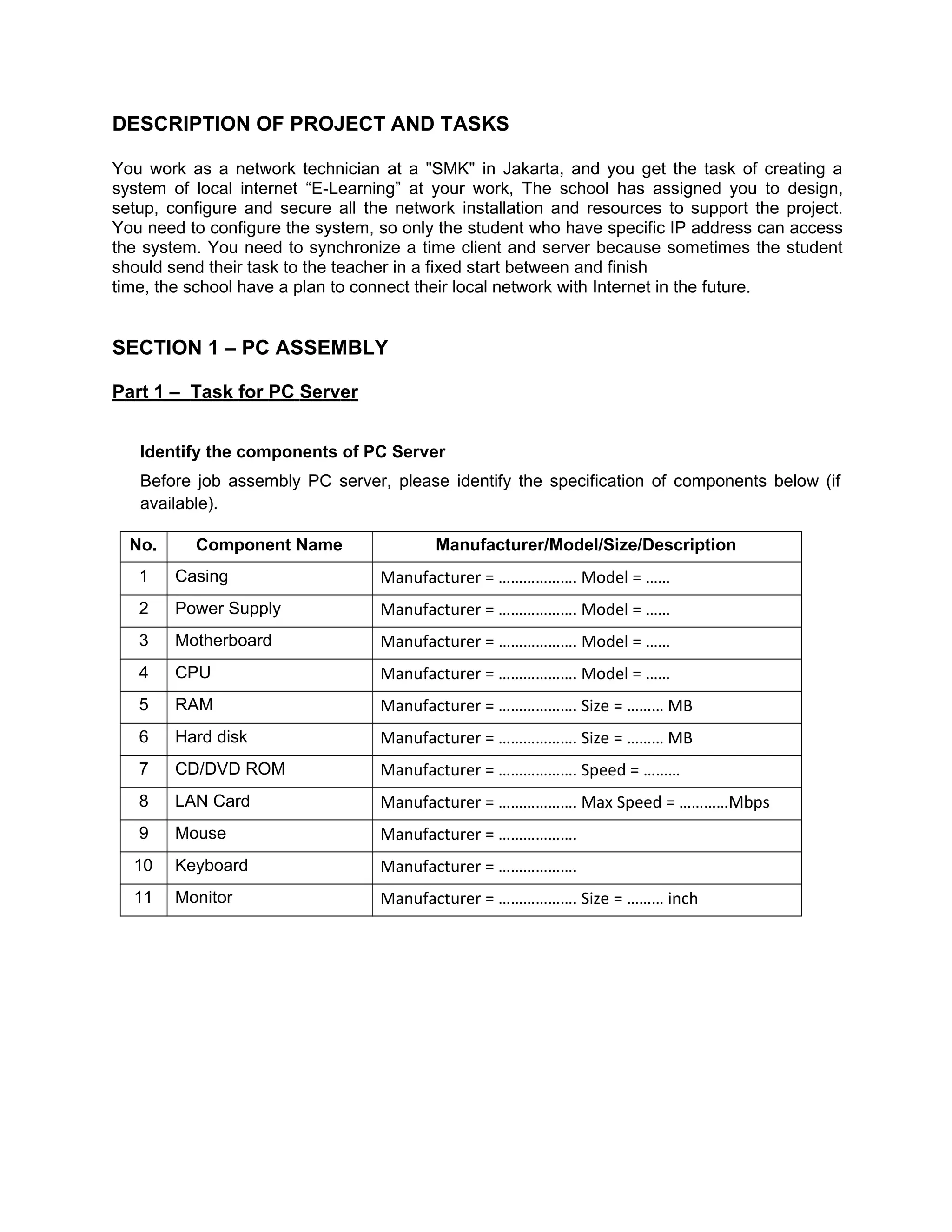
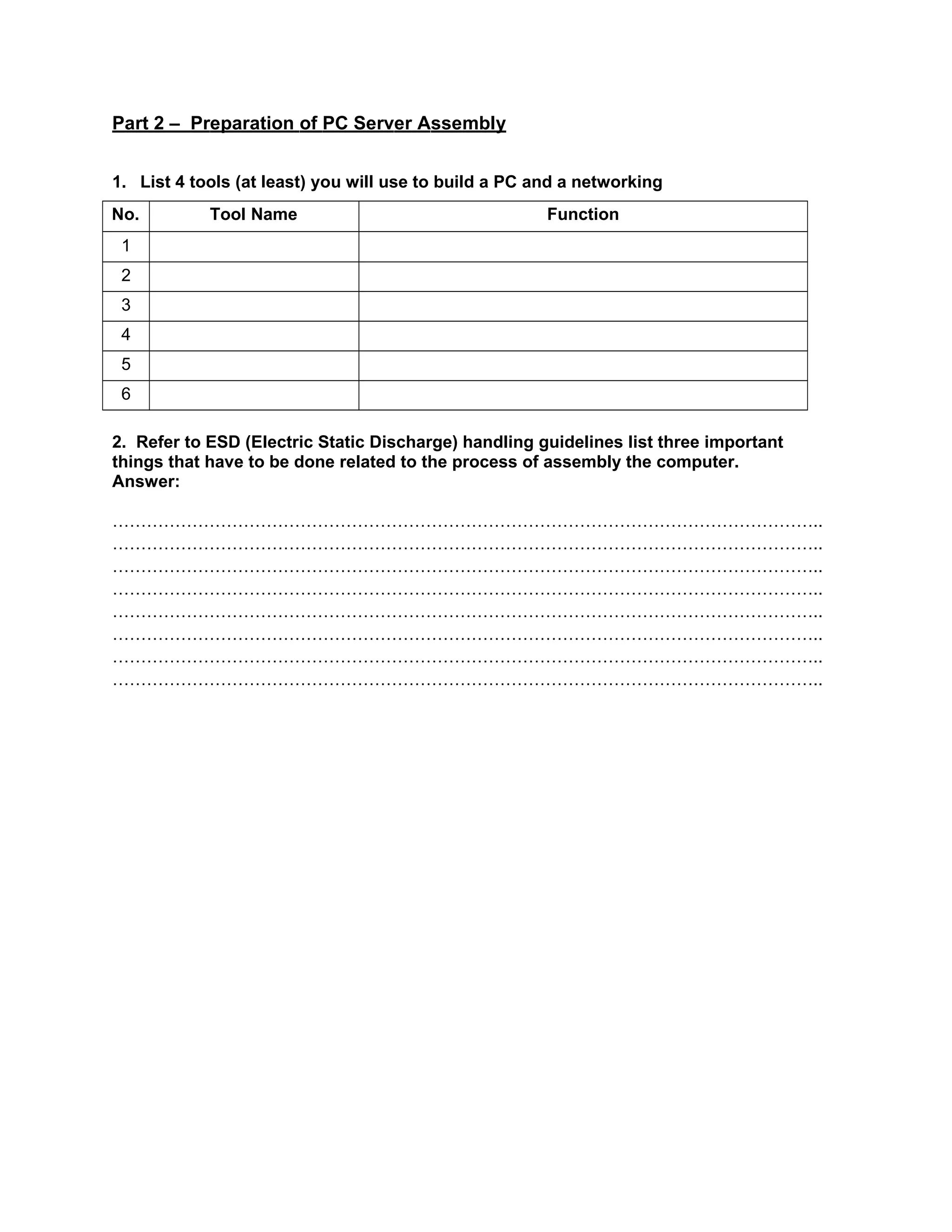
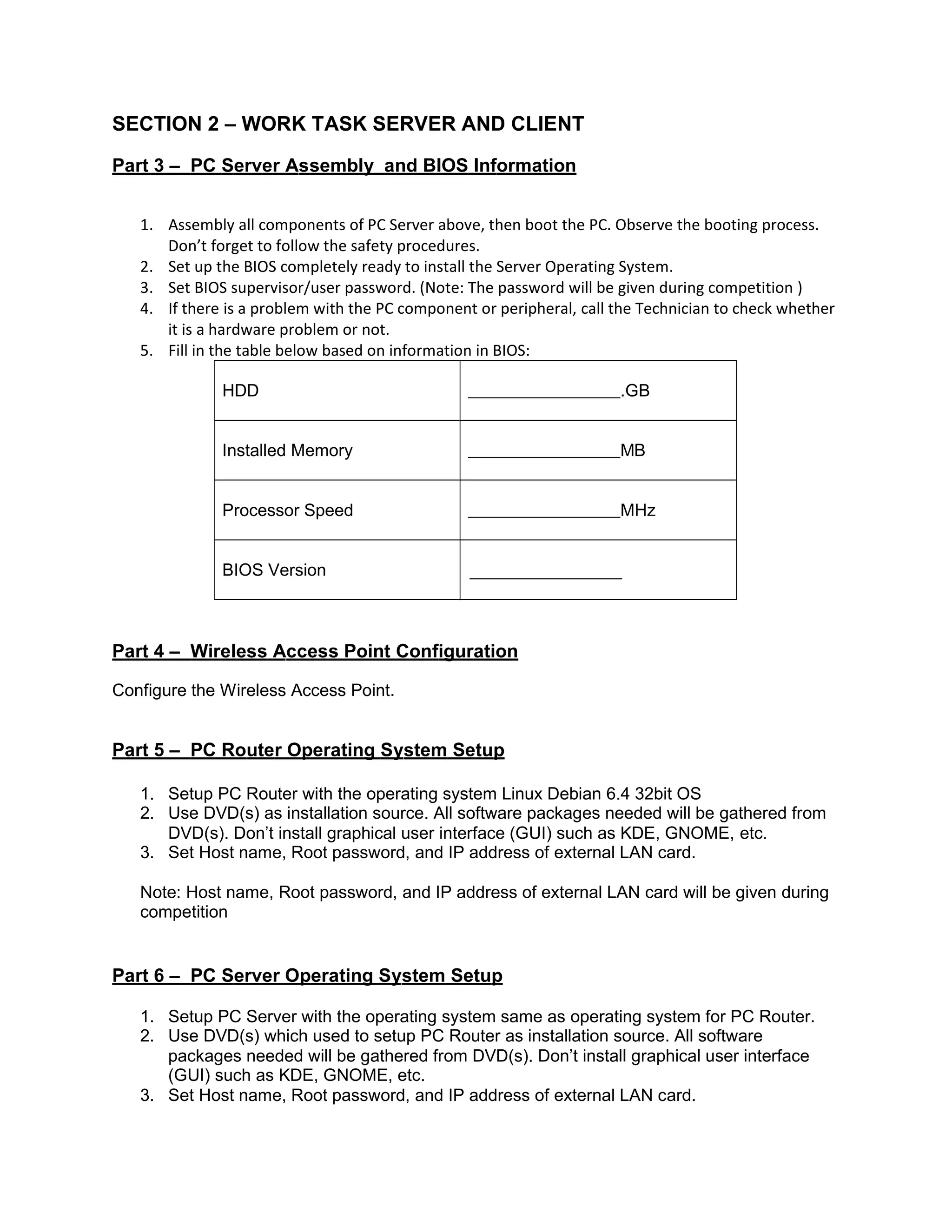
The document describes tasks for setting up a local internet e-learning network for a vocational school in Jakarta. The tasks include assembling PC servers and clients, installing operating systems, configuring networking components like routers, DHCP, DNS, firewalls, mail servers, and troubleshooting connectivity issues. The network is to support an e-learning project allowing only specific student IP addresses to access course content within fixed time windows.