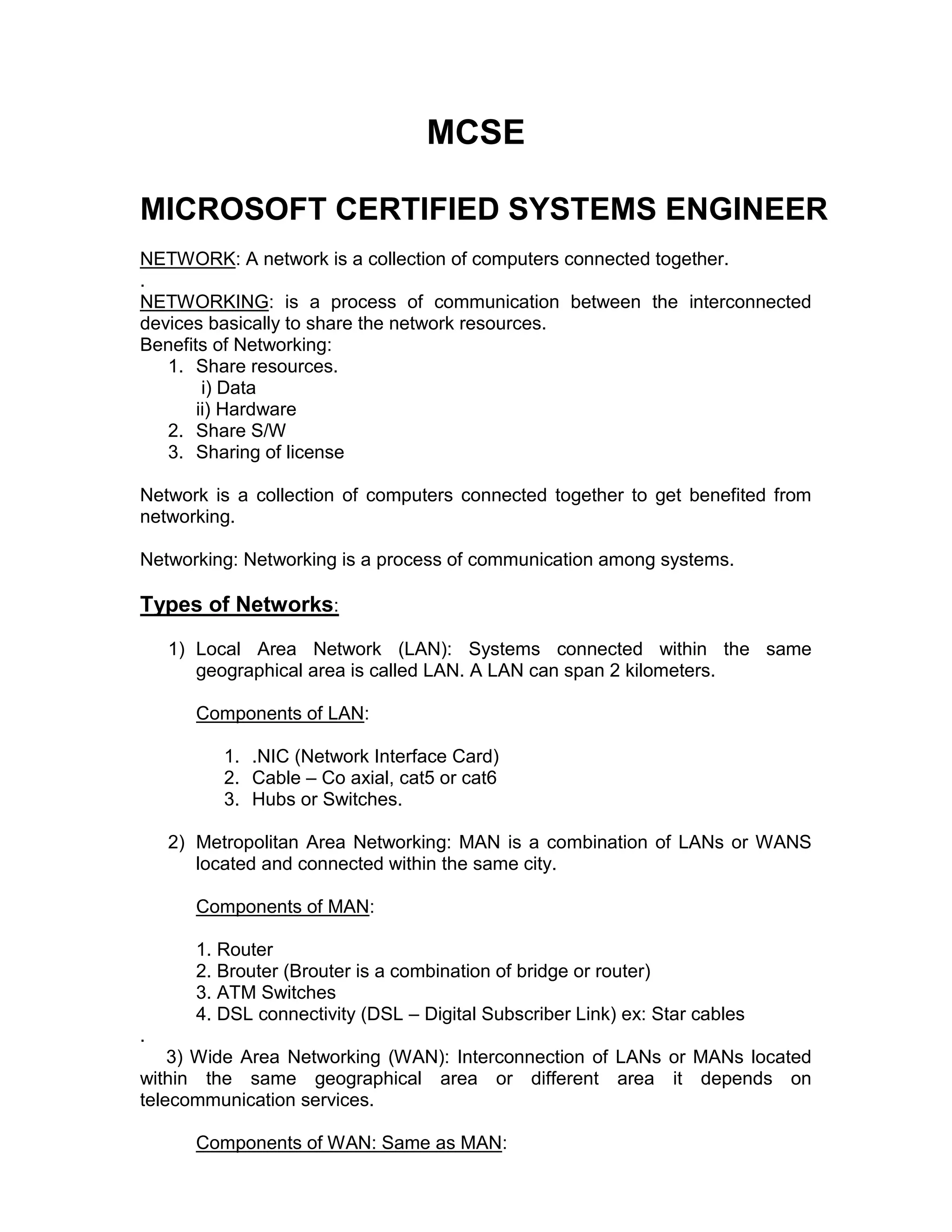
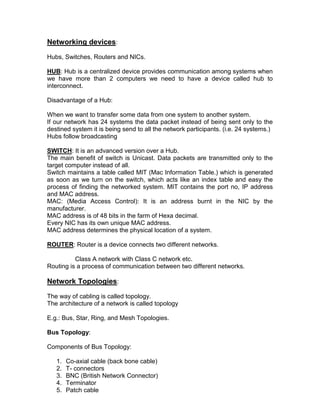
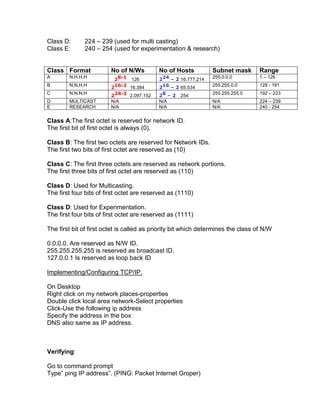
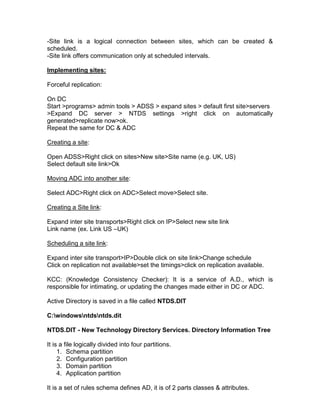
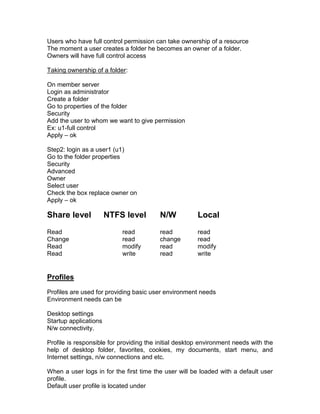
This document provides information about networking and Microsoft Certified Systems Engineer (MCSE) certification. It defines what a network is and discusses the benefits of networking such as sharing resources, software, and licenses. It also describes different types of networks including local area networks (LANs), metropolitan area networks (MANs), and wide area networks (WANs). Additionally, it discusses networking devices like hubs, switches, routers, and network interface cards. The document also covers topics such as network topologies, IP addressing, implementing TCP/IP, and Active Directory.