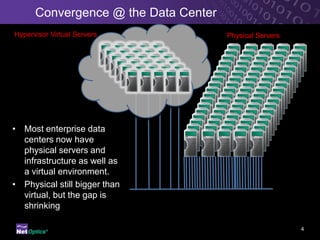
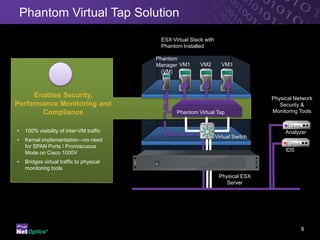
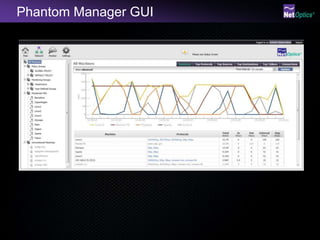
The document presents an overview of virtual tap technology, aimed at improving monitoring and security within virtualized environments. It discusses the challenges associated with visibility and compliance in hypervisor-based systems and proposes a phantom virtual tap solution that enhances traffic monitoring without degrading network performance. Key advantages include increased ROI on existing tools and low resource impact, ultimately facilitating better performance and compliance in data centers.