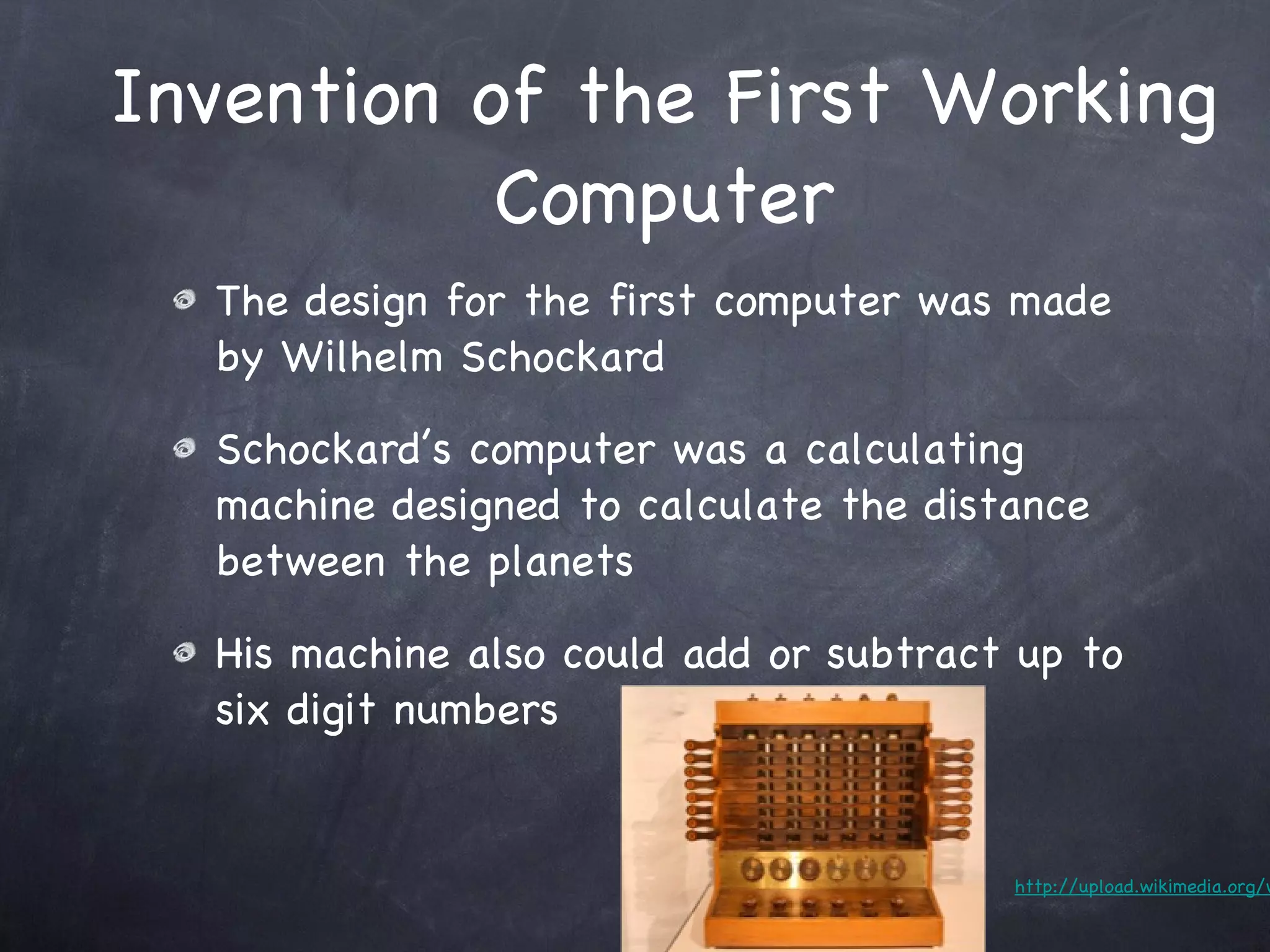
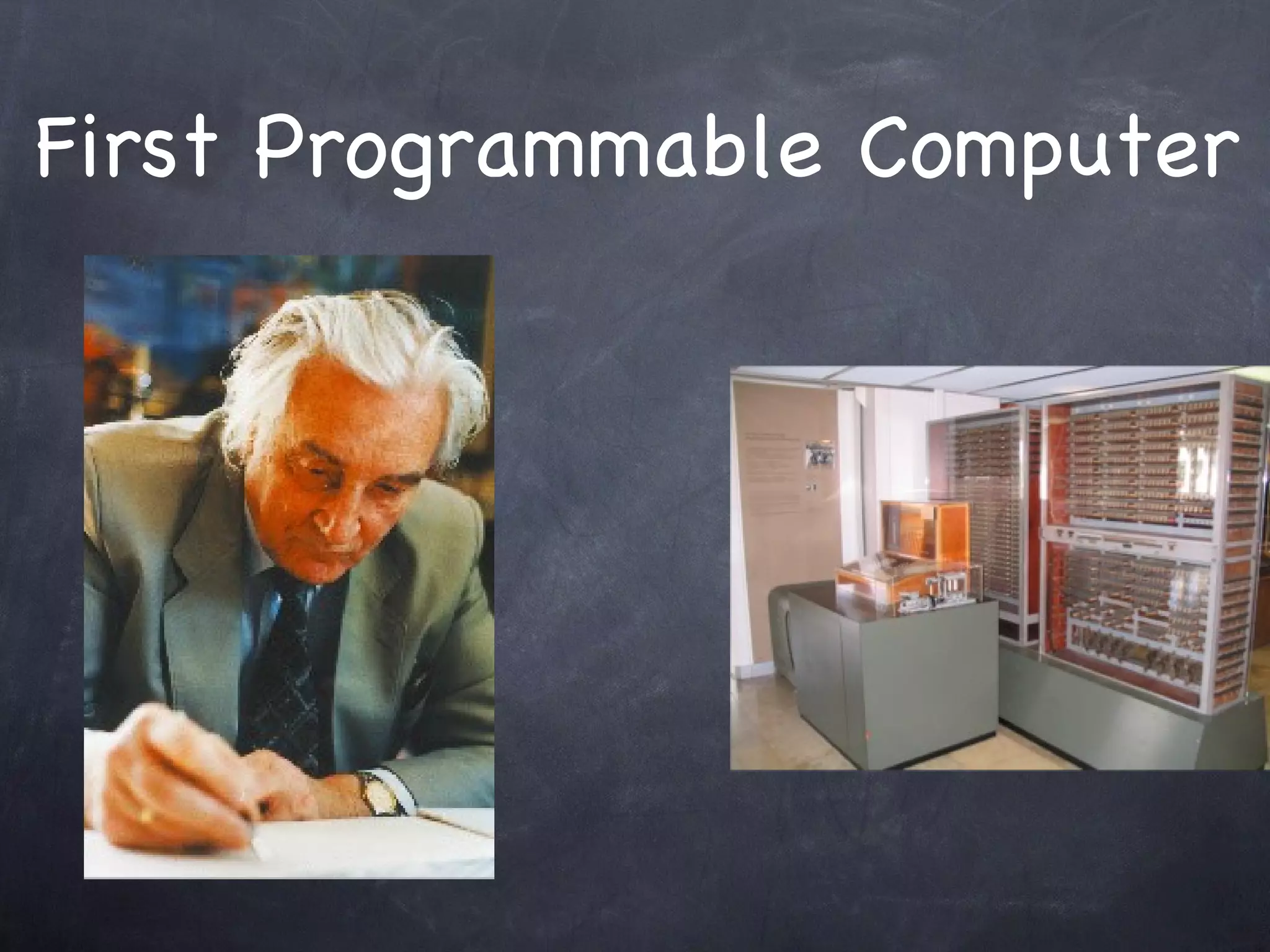
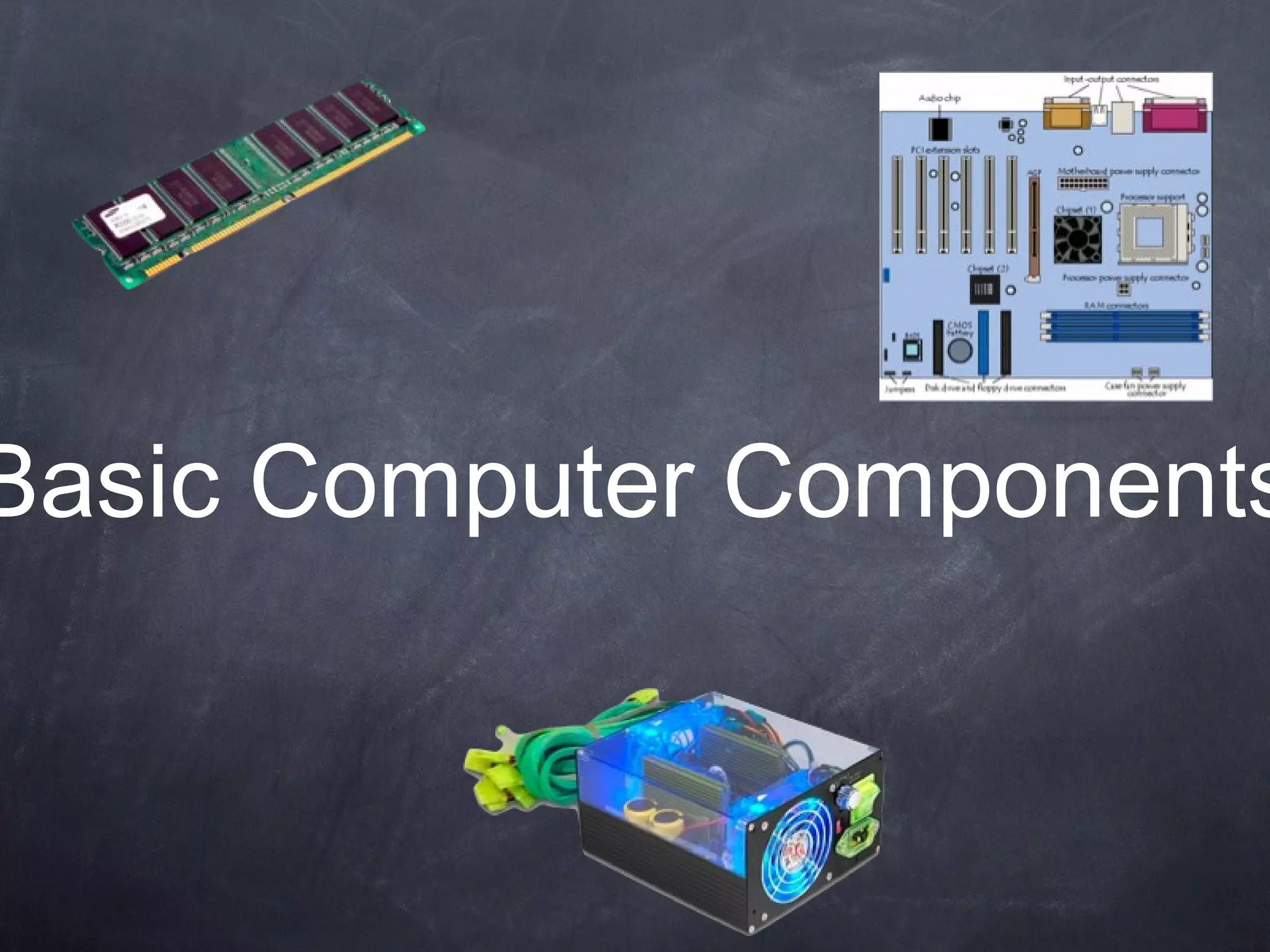
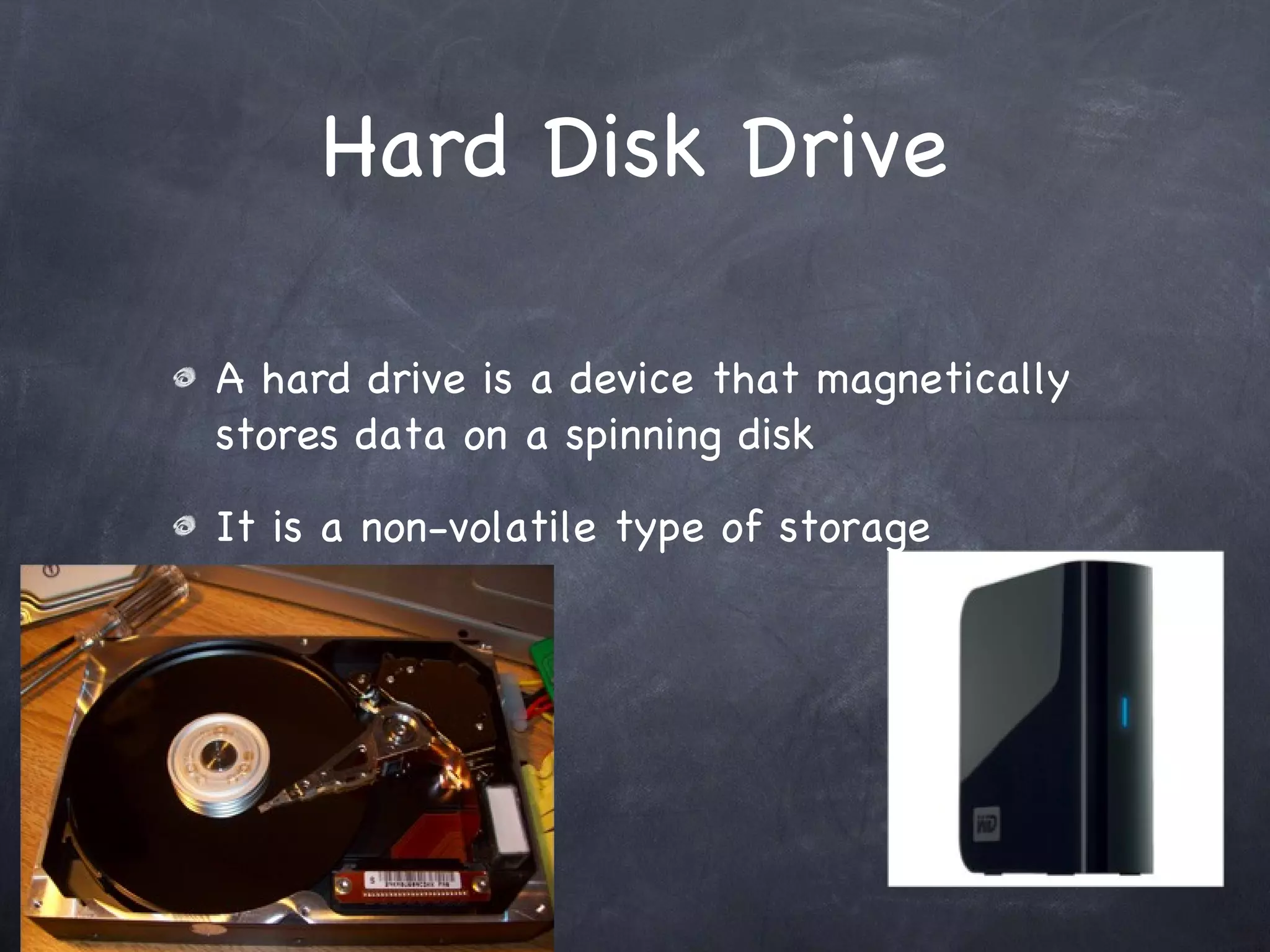
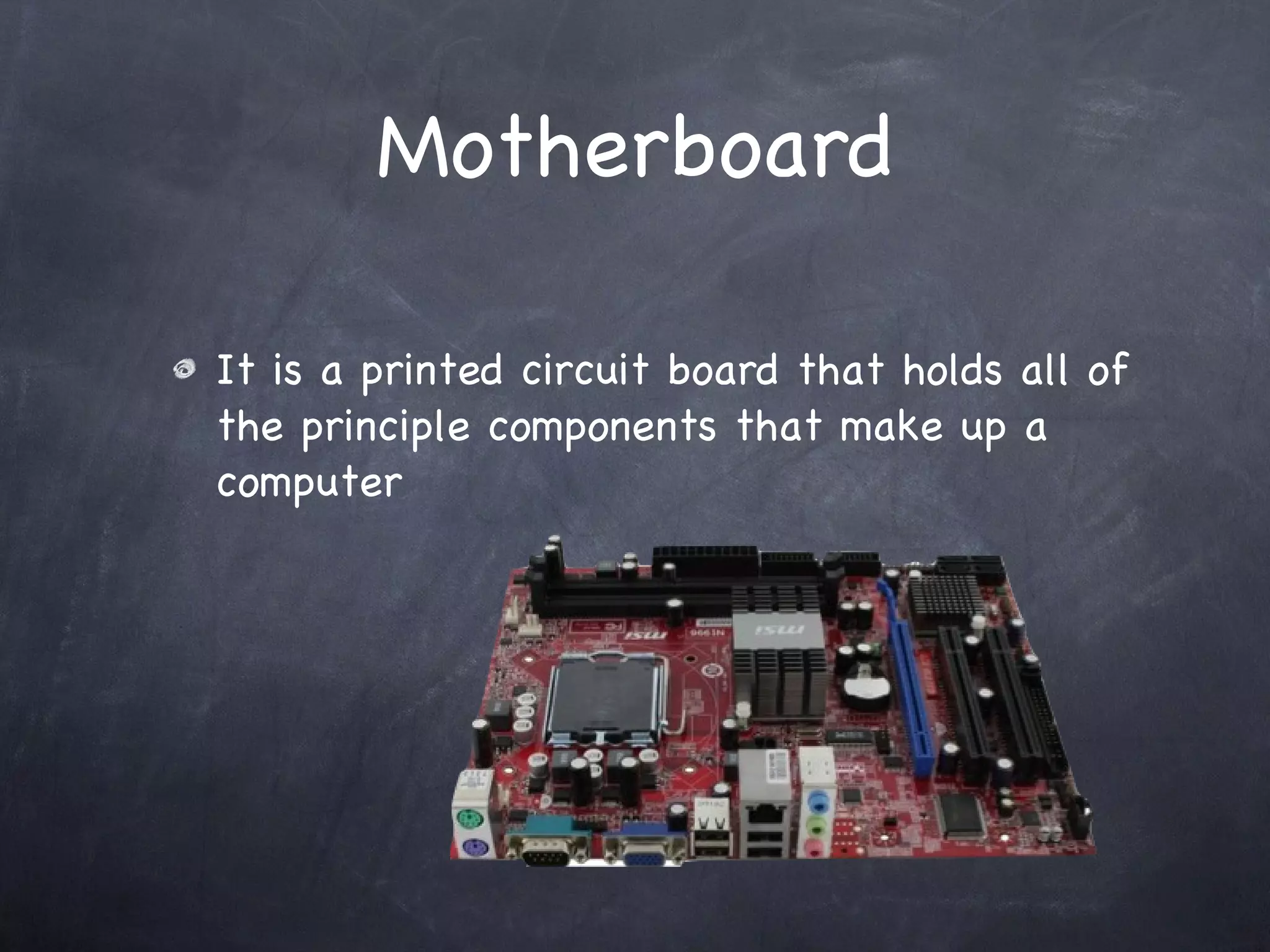
The document discusses the evolution of computers from their early invention to modern times. It describes how early computers were large, expensive machines only affordable to institutions and the wealthy, while modern computers are small, affordable devices ubiquitous in everyday life and business. The core components of computers like the CPU, RAM, hard drives and other parts are also explained.