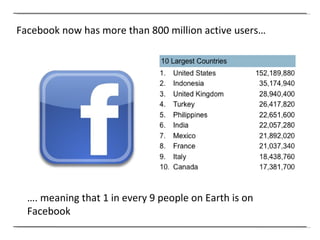
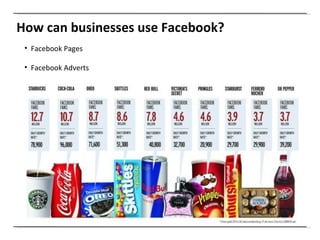
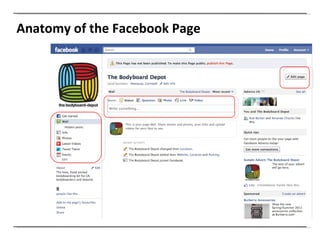
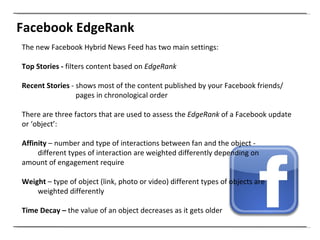
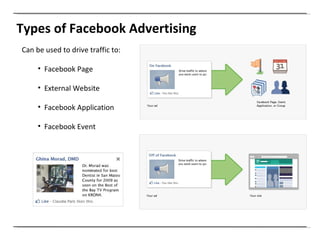
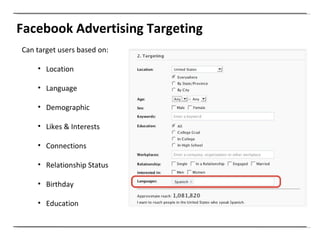
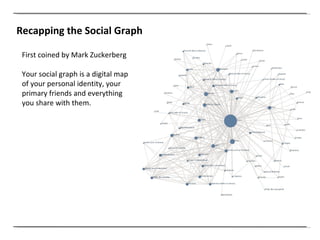
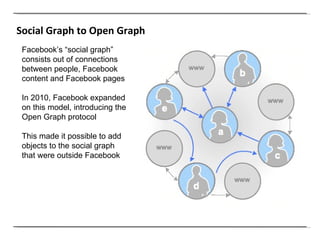
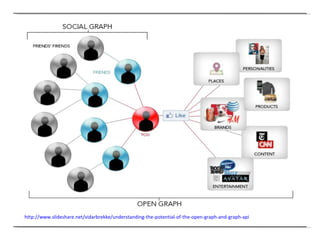
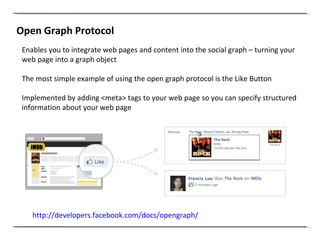
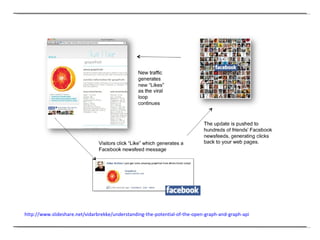
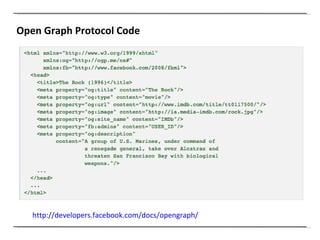
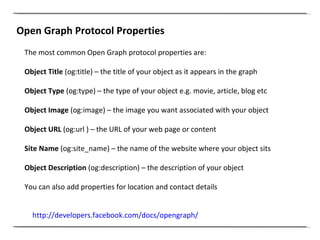
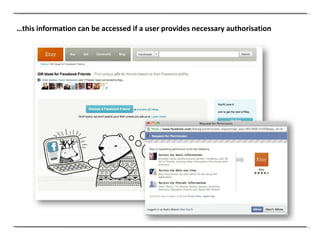
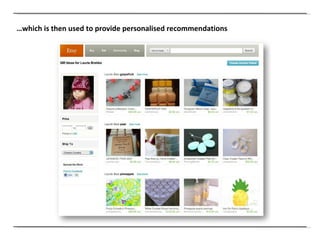
Facebook now has over 800 million active users, making it the third largest "country" in the world. Businesses can use Facebook Pages to share content like status updates, photos, and videos to interact with fans. Facebook Advertising allows targeting users based on location, interests, and other factors to promote the business Page or drive traffic to other websites and apps. The Open Graph protocol enables websites to integrate their content into the Facebook social graph, turning web pages into objects that can be shared.
















![Clemi Hardie [email_address] @clemihardie](https://image.slidesharecdn.com/session4-111025125014-phpapp02/85/Introducing-Facebook-51-320.jpg)