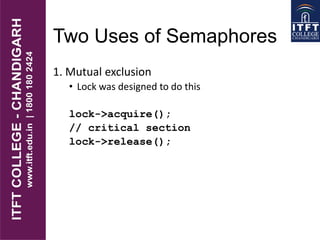
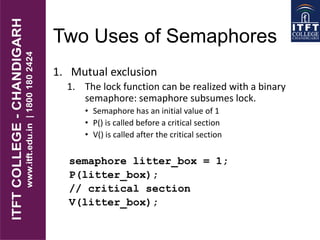
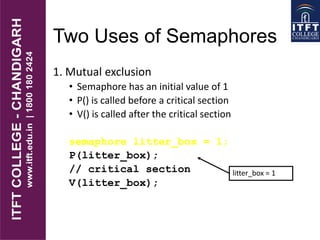
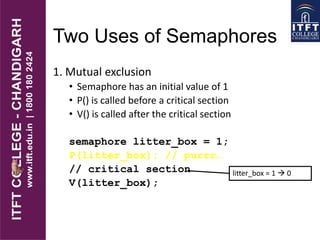
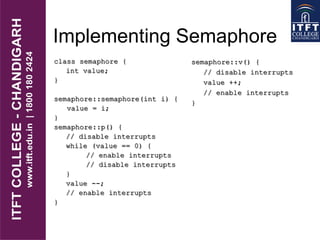
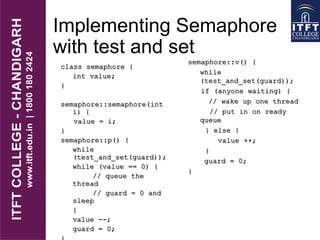
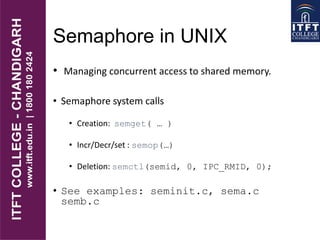
This document discusses semaphores and their use for synchronization between threads or processes. It defines semaphores as consisting of a positive integer value and atomic P() and V() operations that decrement and increment the value. Semaphores can be used for mutual exclusion by initializing a binary semaphore to 1 and having threads call P() before and V() after critical sections. Semaphores can also be used to synchronize producers and consumers in a bounded buffer problem, ensuring the consumer waits if the buffer is empty and the producer waits if the buffer is full. The document outlines implementations of semaphores using spinlocks or queues and the system calls used to manage semaphores in UNIX.