Embed presentation
Download as PDF, PPTX
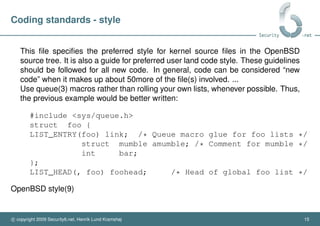
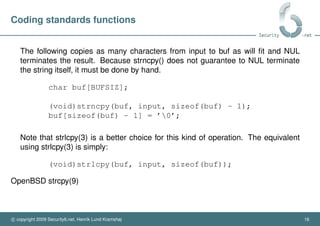
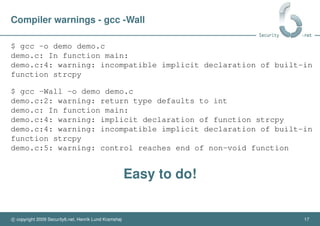
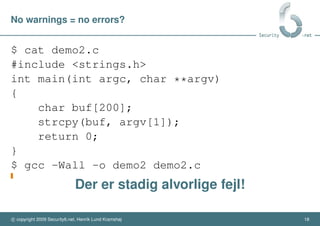
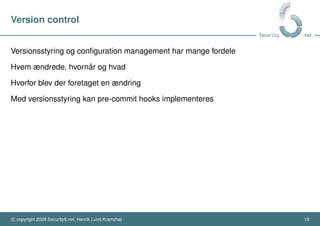
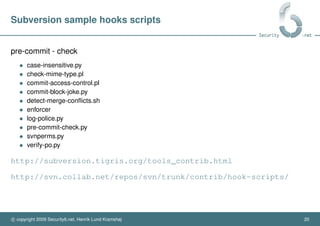
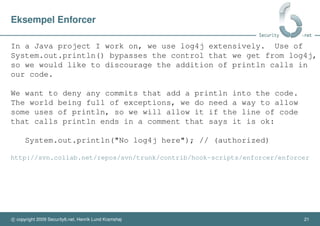
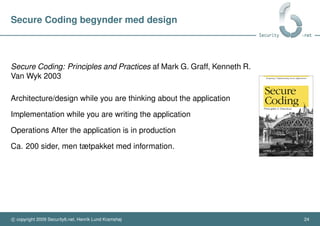
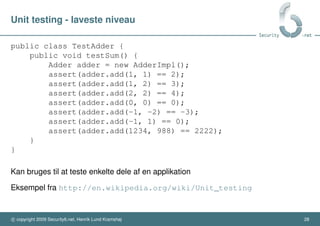
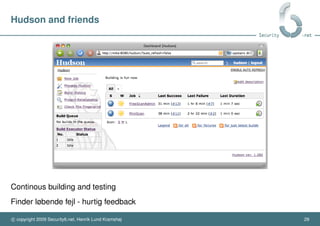
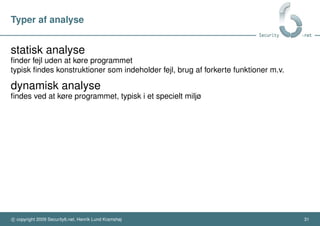
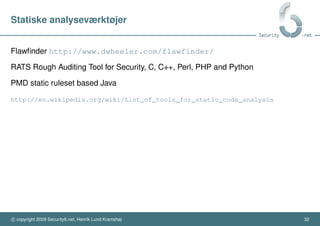
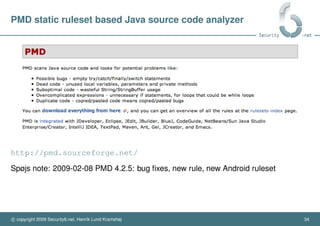
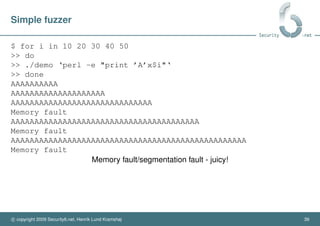
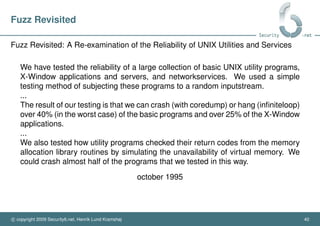


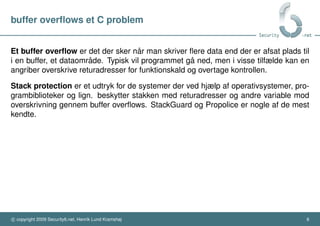
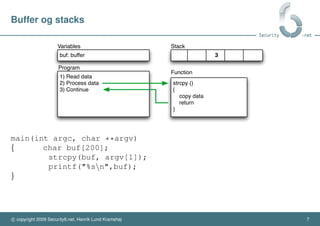
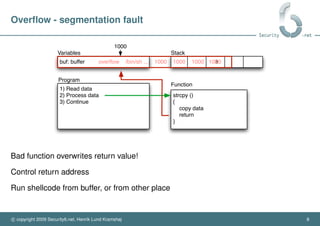
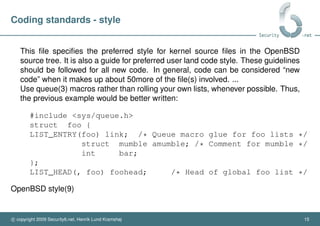
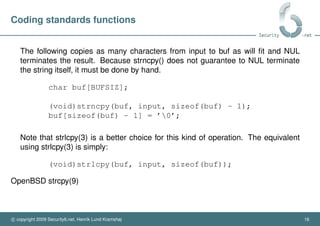
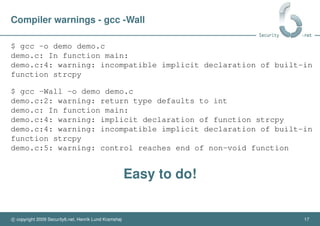
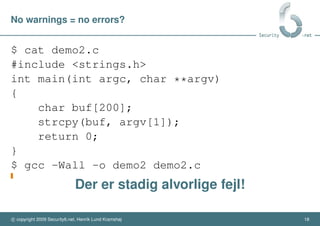
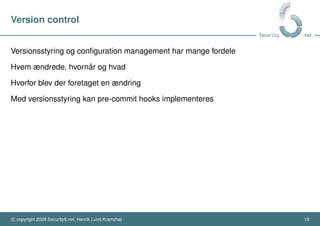
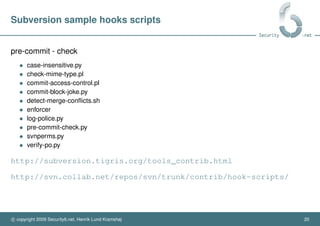
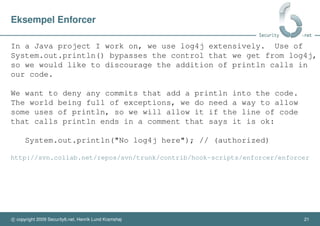
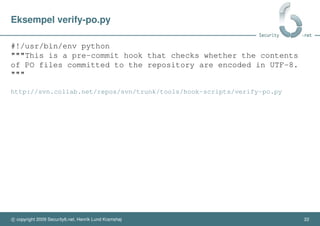
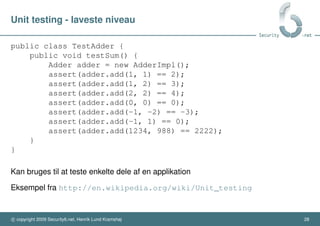
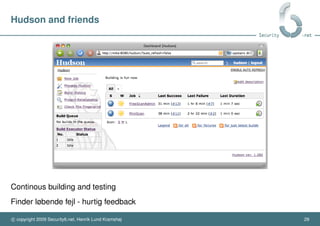
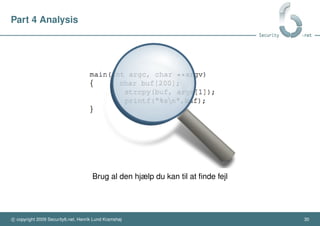
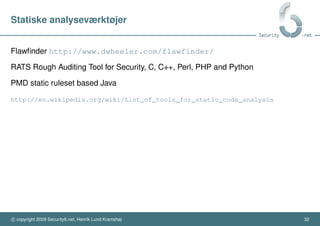
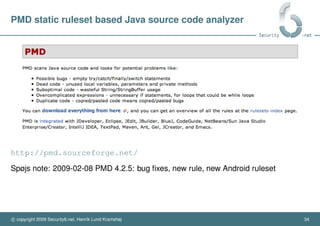
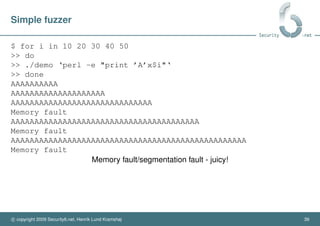
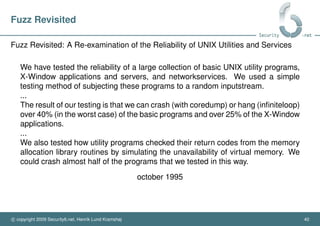
This document provides an overview of security tools that can be used in software development. It discusses coding standards, compiler warnings, version control, design for security, testing, and analysis tools. Coding standards and following compiler warnings can help catch simple errors. Version control allows reviewing changes and implementing hooks to catch issues early. Designing for security from the start is important. Testing on multiple levels from units to full systems helps improve quality. Static and dynamic analysis tools can find bugs without or during execution. Overall, applying security best practices throughout the development cycle leads to higher quality software.