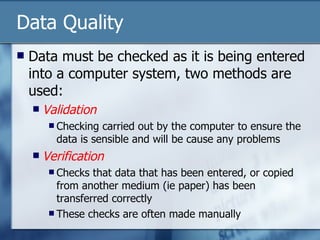
There are many threats to business data such as physical damage, viruses, user error, and hardware failure that can result in financial and reputational harm if measures are not taken to secure data. Data can be stolen by employees or hackers seeking sensitive information. Businesses should use strong passwords, encryption, lock computers when unattended, and back up data regularly to protect against data loss or theft. It is also important to validate and verify data quality as it is entered into systems.