The document discusses various topics related to asset management and data security in an IT environment. It covers:
- The importance of having policies for classifying, retaining, and destroying assets like data, hardware, software and documentation.
- Defining roles for data owners, custodians, system owners and administrators.
- Methods for securely storing, transmitting and destroying sensitive data.
- Vulnerabilities that can affect web-based systems and ways to assess security risks through scanning and testing.



























![Malicious Code Examples
Copyright © 2019 Logical Operations, Inc. All rights reserved.
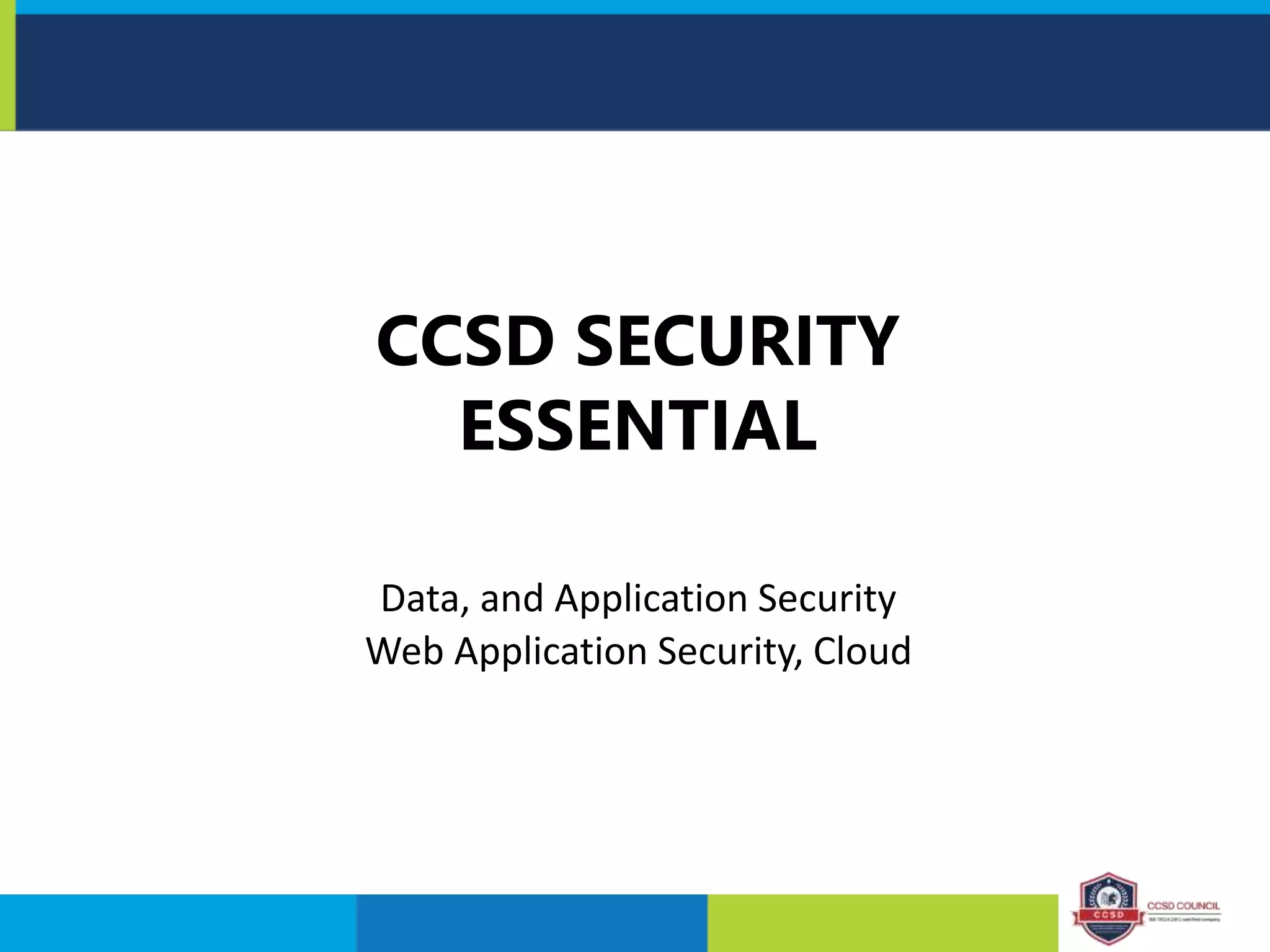
Name Example Comment
SQL Injection blah' or 1=1-- • Based on an OR statement
• Todefeat, you must sanitize input or use
stored procedures with parameterized SQL
queries
Directory traversal https://www.victim.com/..%c0%af../w
innt/system32/cmd.exe?/c+tftp.exe+-
i+get+exploit.exe
• Uses special Unicode characters or other
mechanisms to bypass controls and allow
browsing of the file system
• Todefeat, use file system permissions
Metacharacters ' " [ ] ; & ^ . | ? * + { } ( ) • Some special characters have programmatic
meaning
• Todefeat, sanitize client input and use
escape characters to neutralize
programmatic capabilities
Script <script>Some malicious command
here</script>
• Malicious code often takes the form of a
script
• Patch systems and sanitize input to disallow
unauthorized scripts](https://image.slidesharecdn.com/securityessentialtopic3-210920014438/75/Secuntialesse-29-2048.jpg)









