Embed presentation
Download as PDF, PPTX

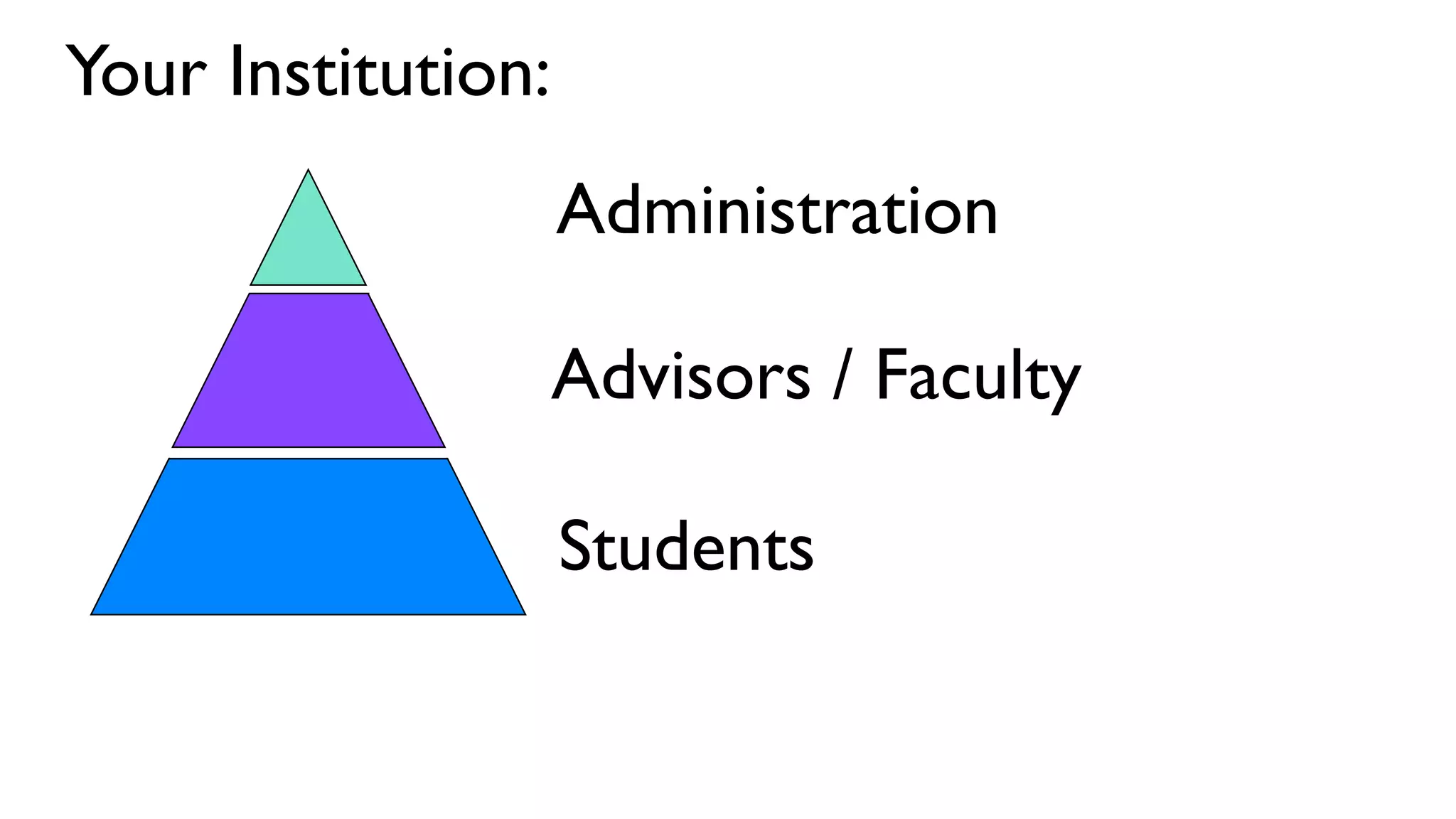
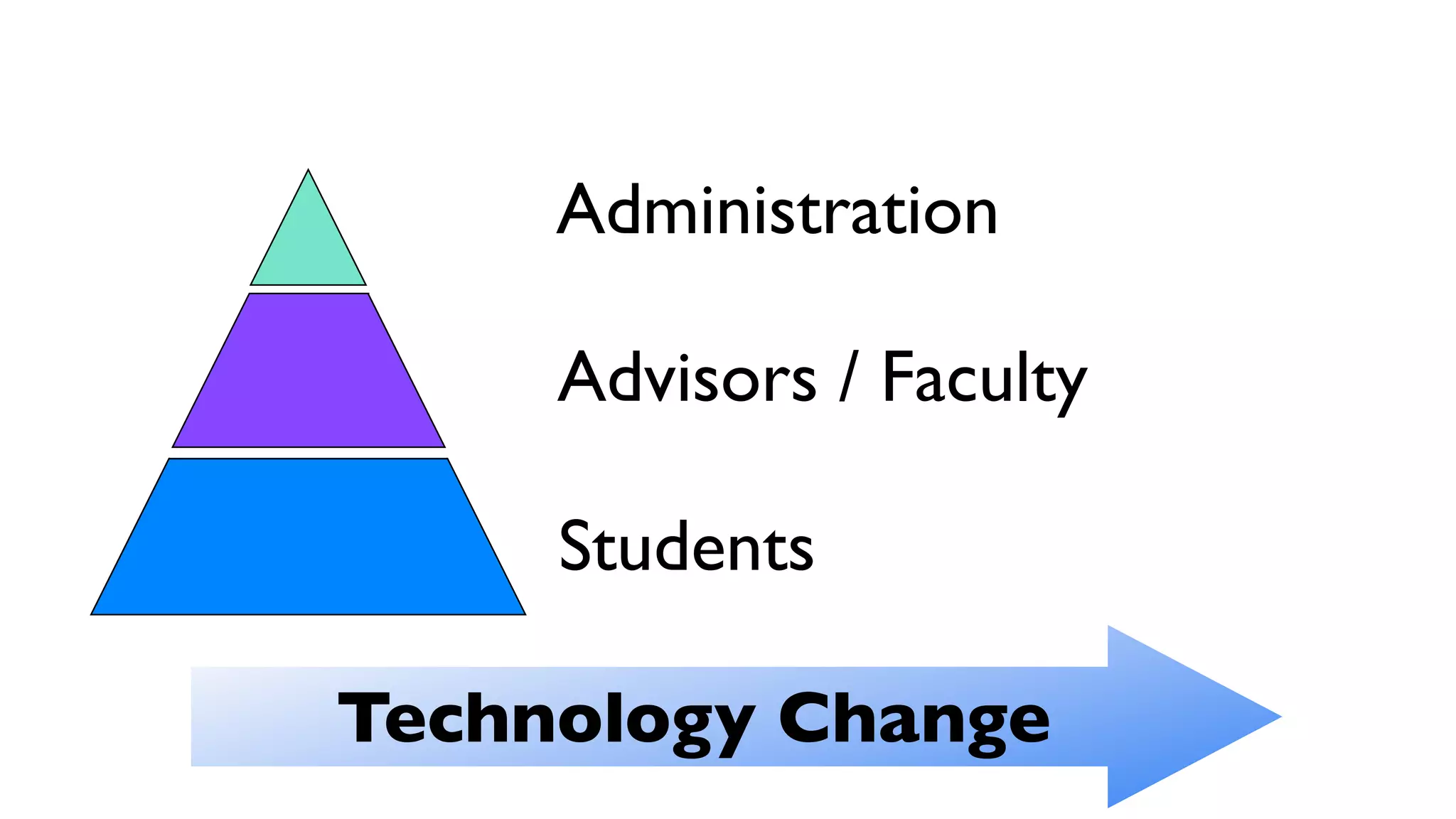
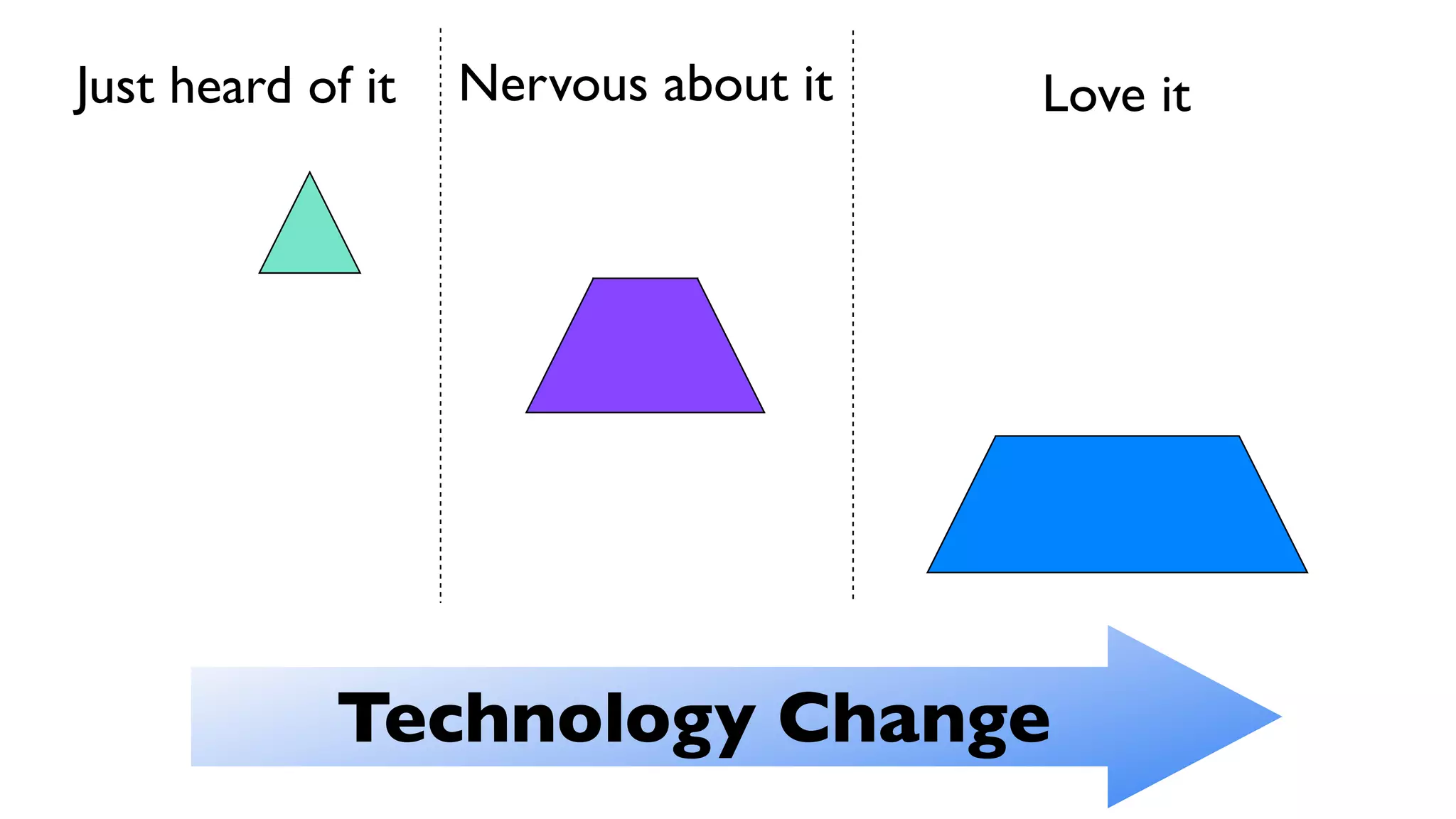
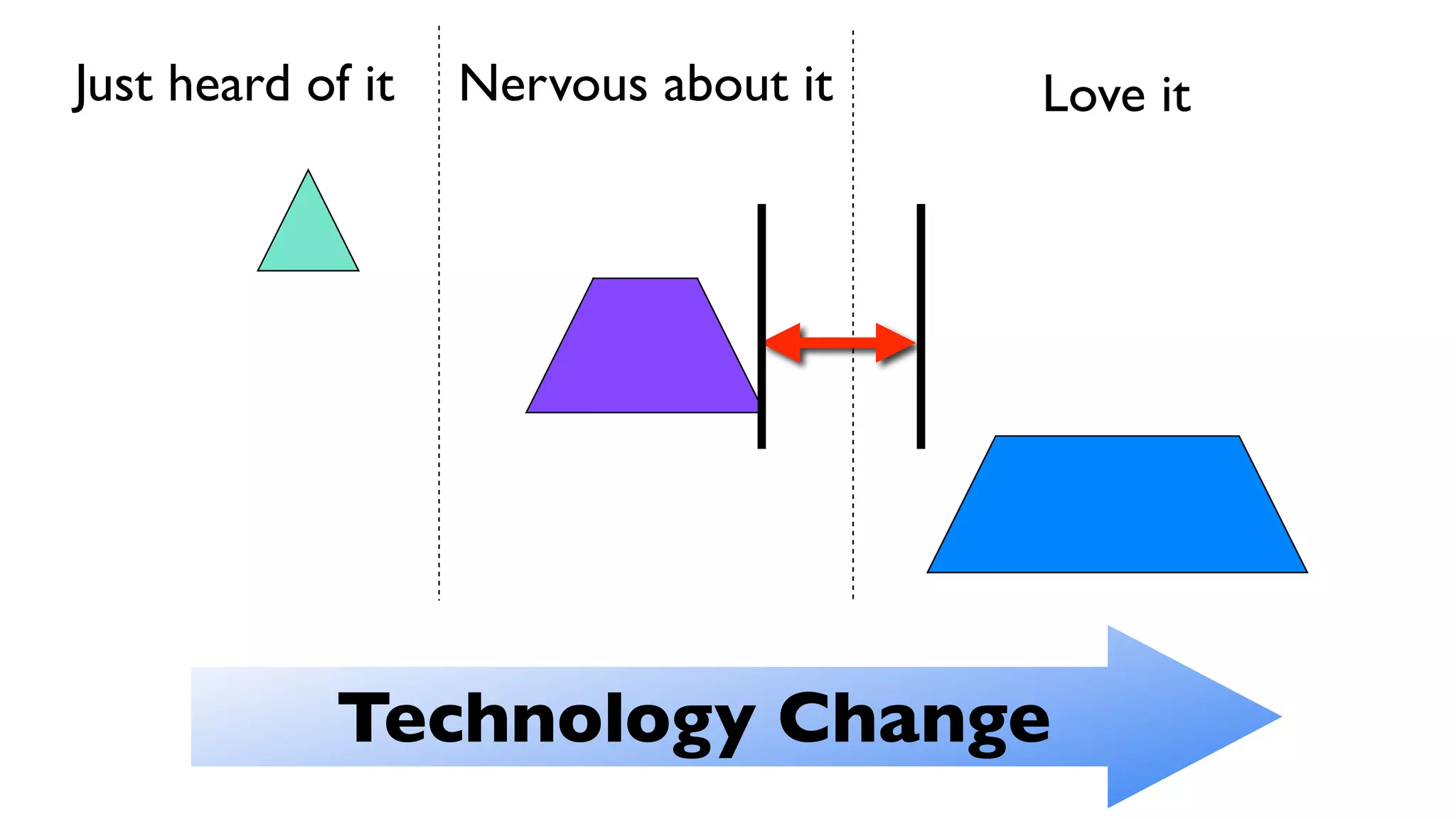
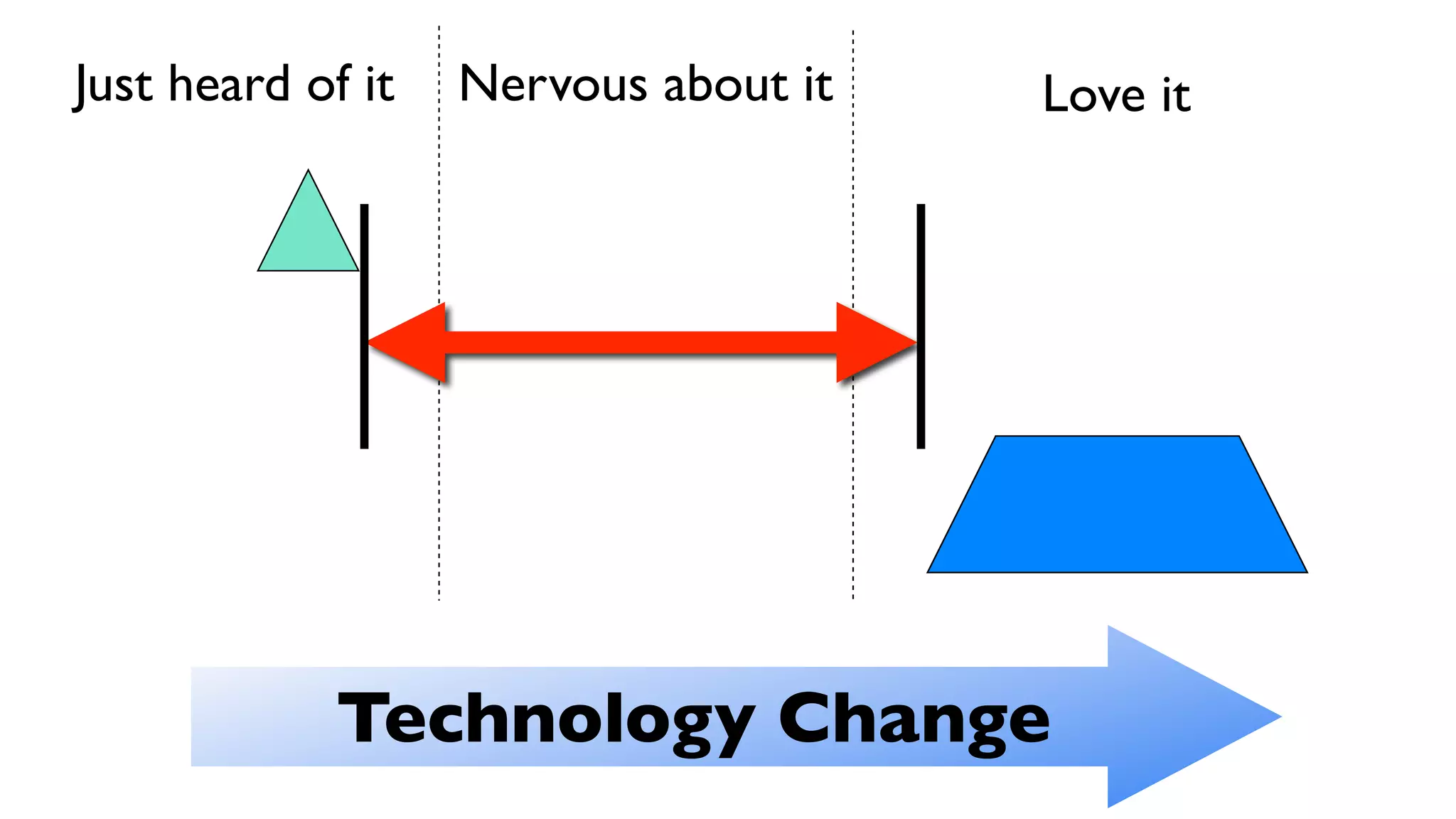
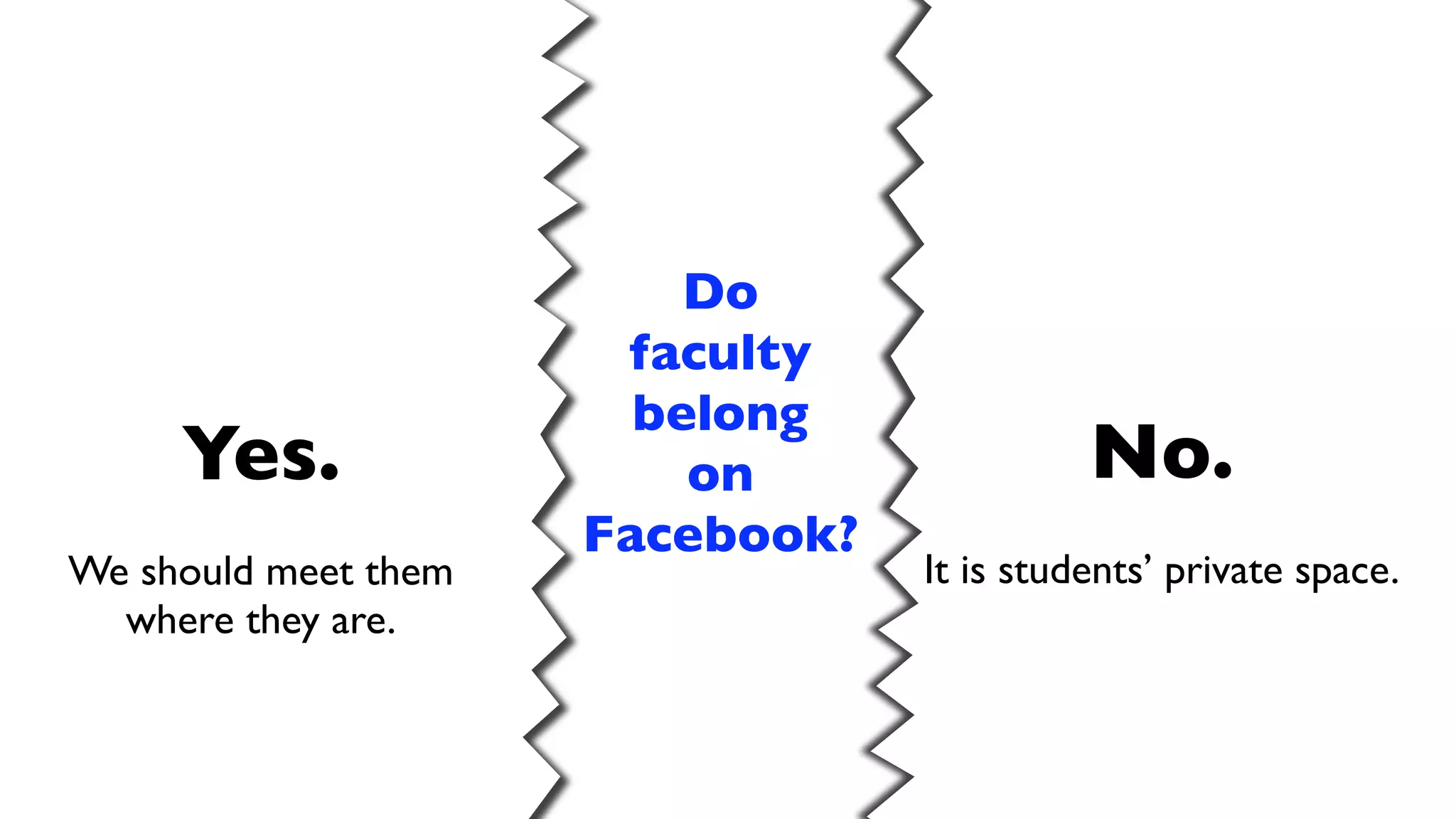





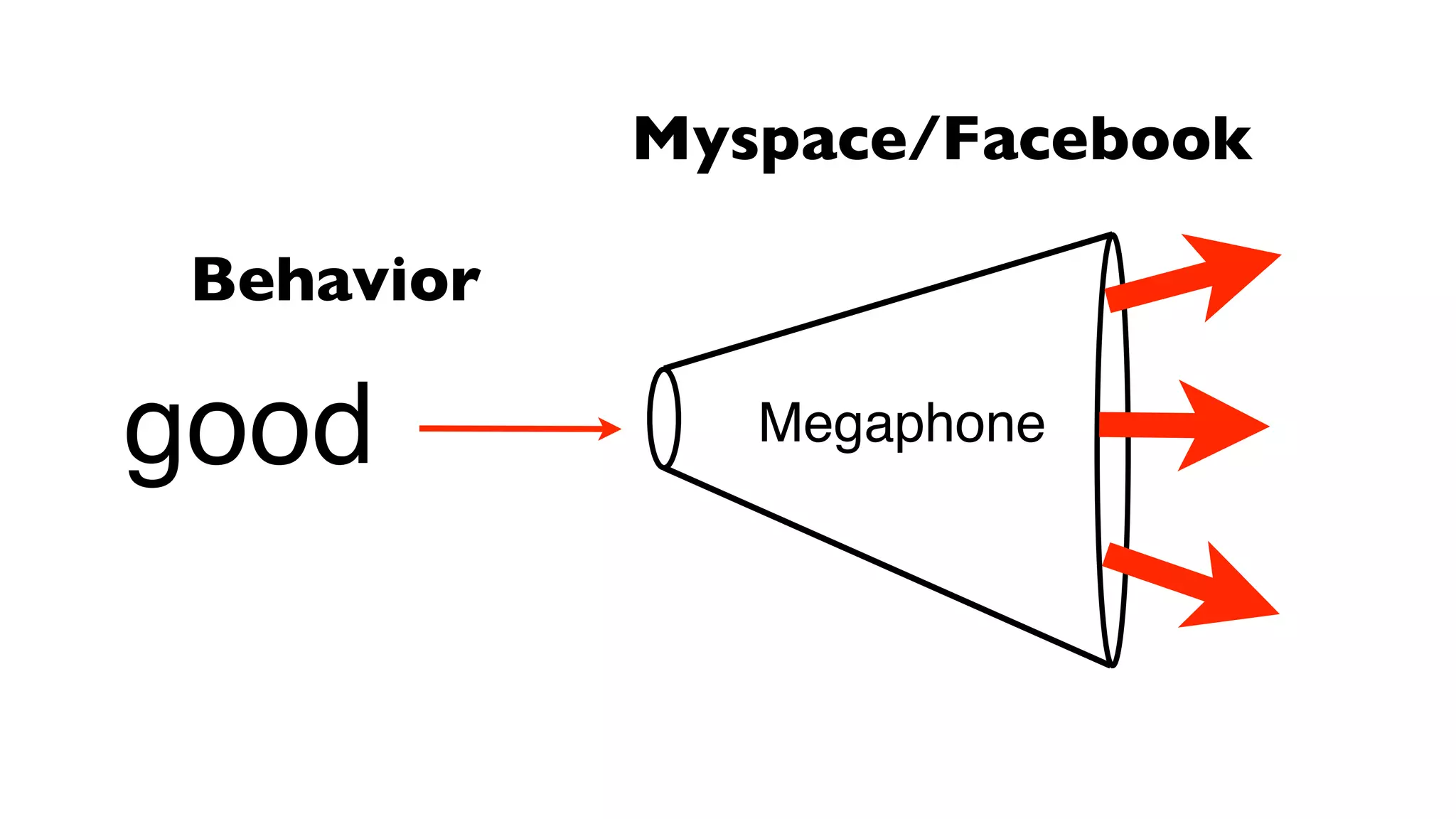








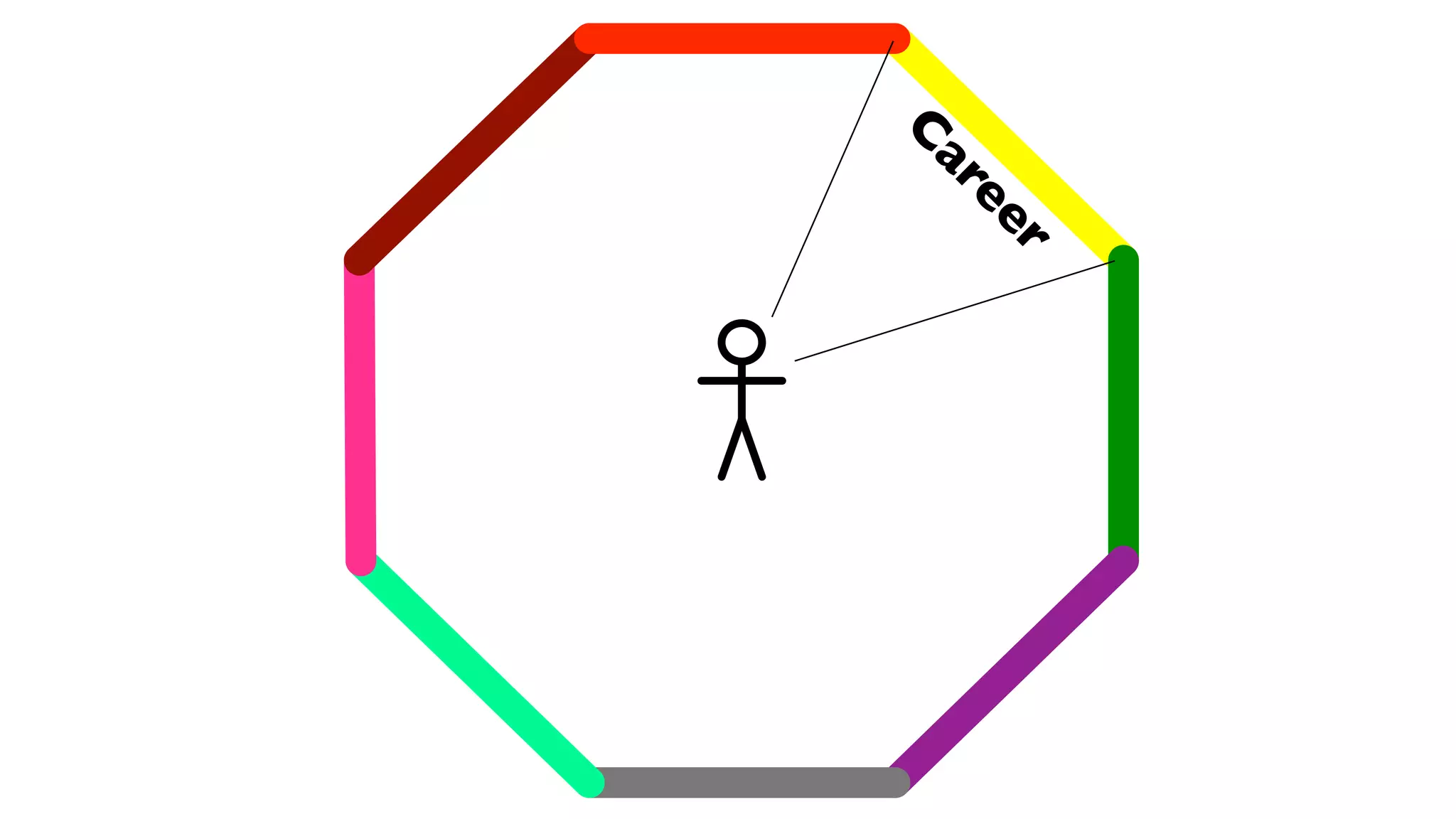










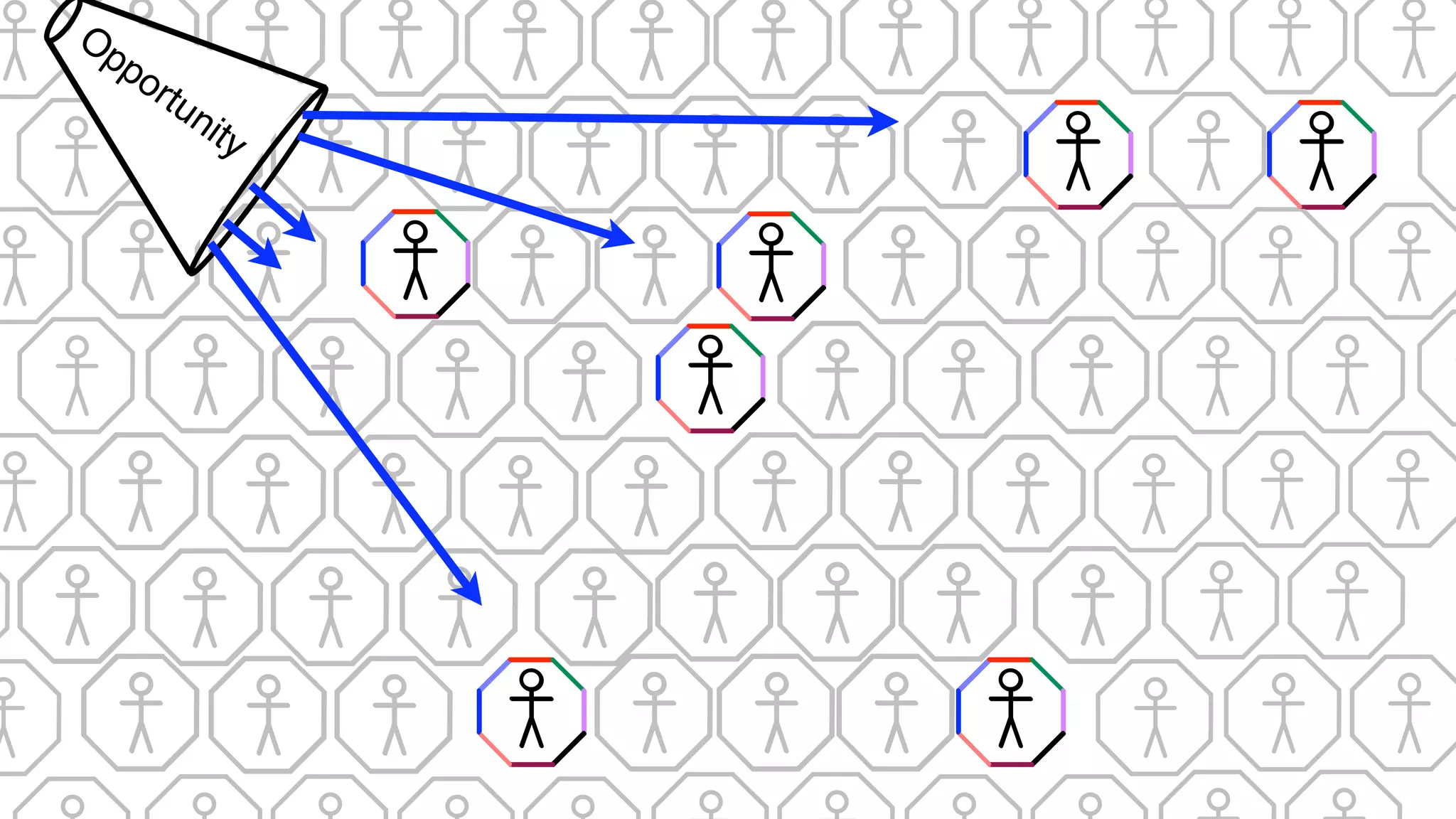
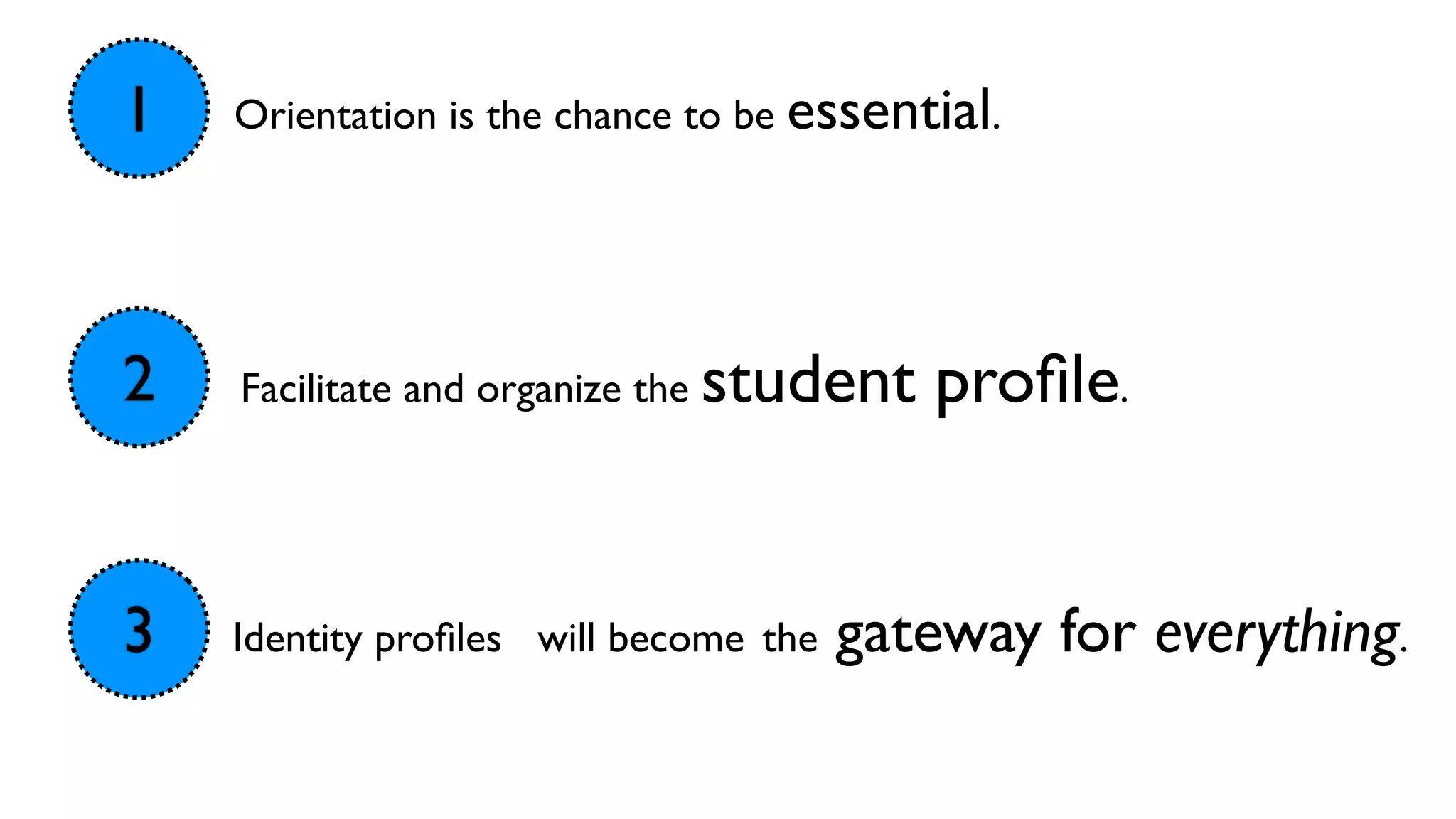
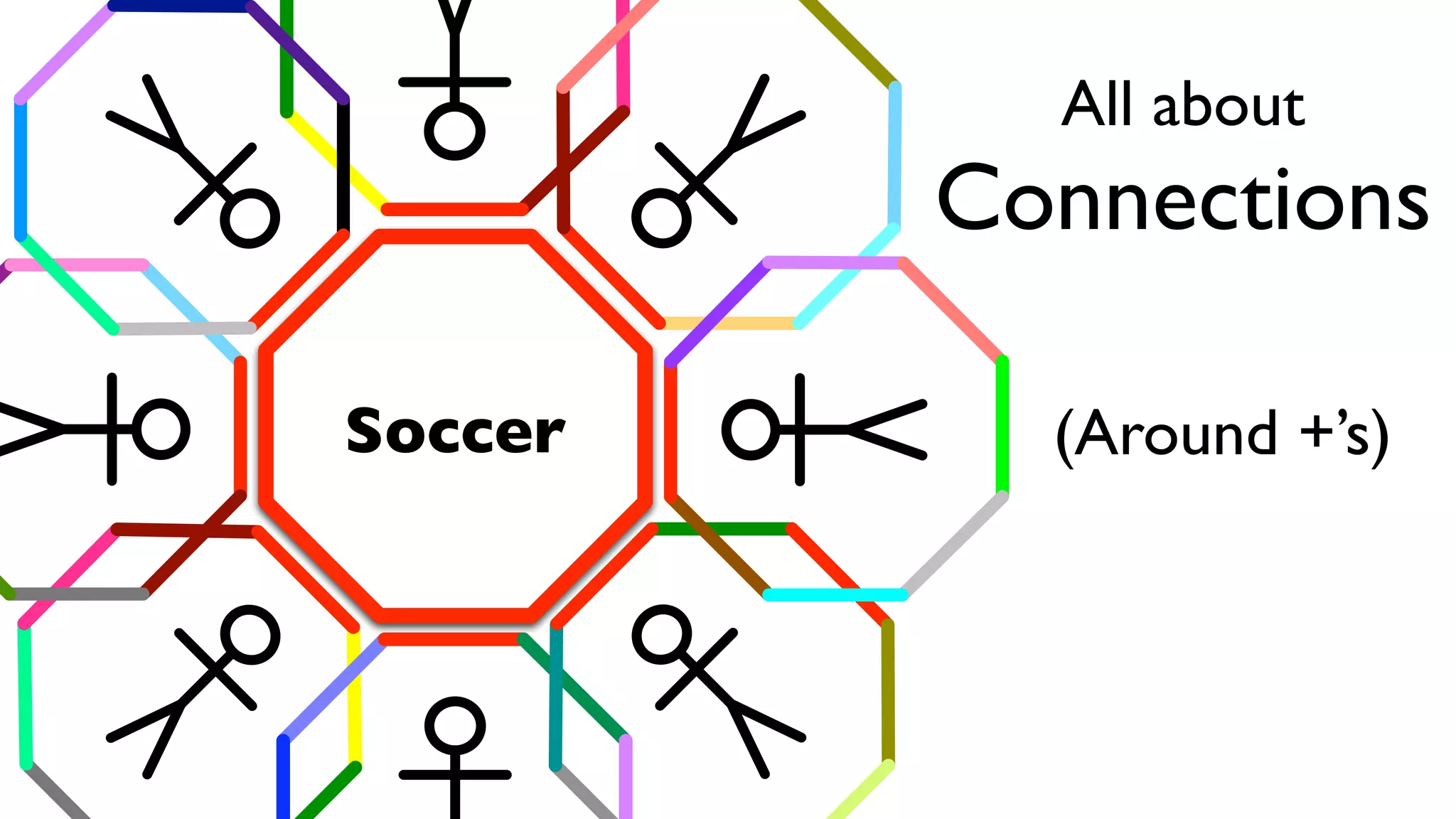






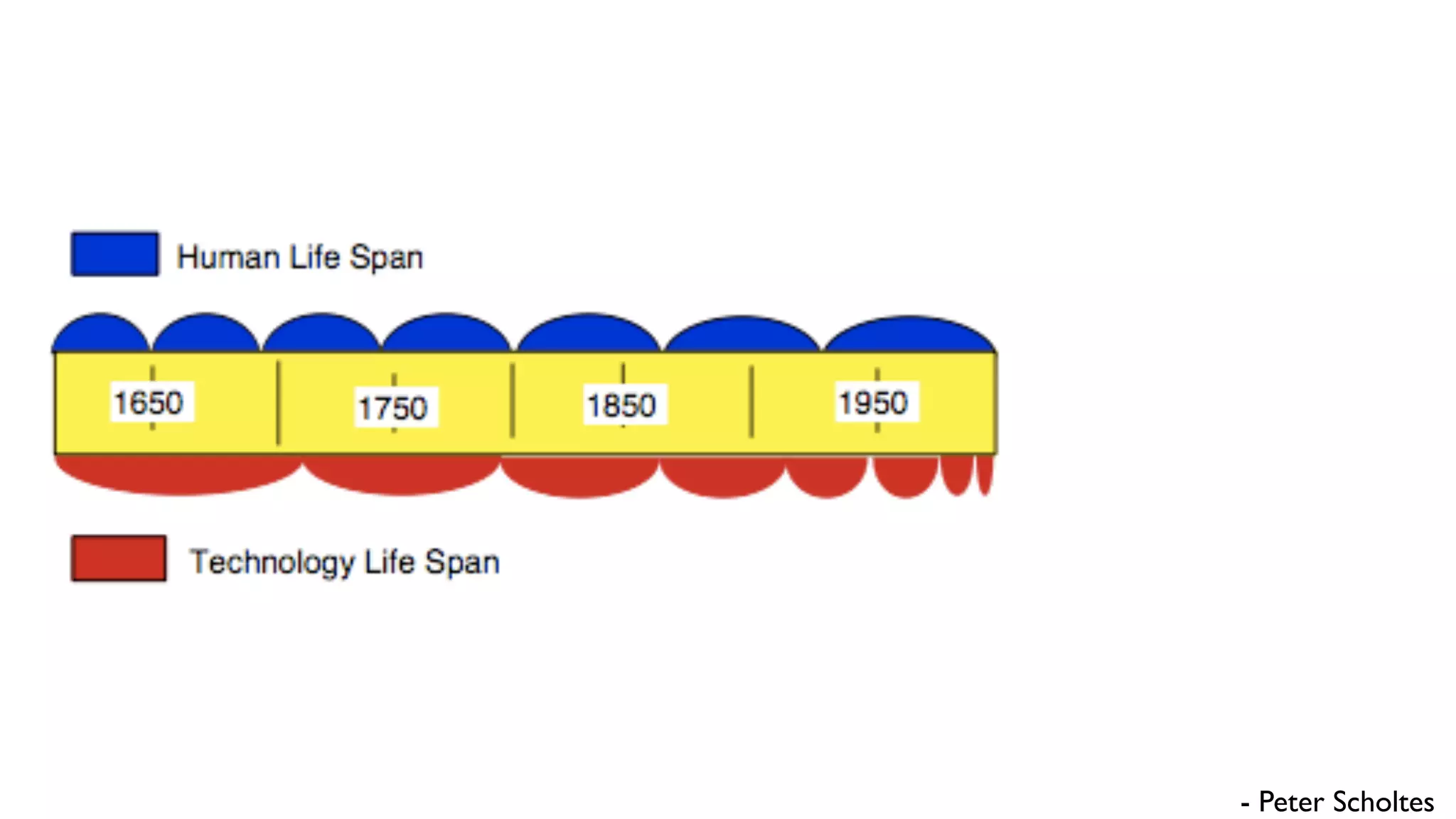









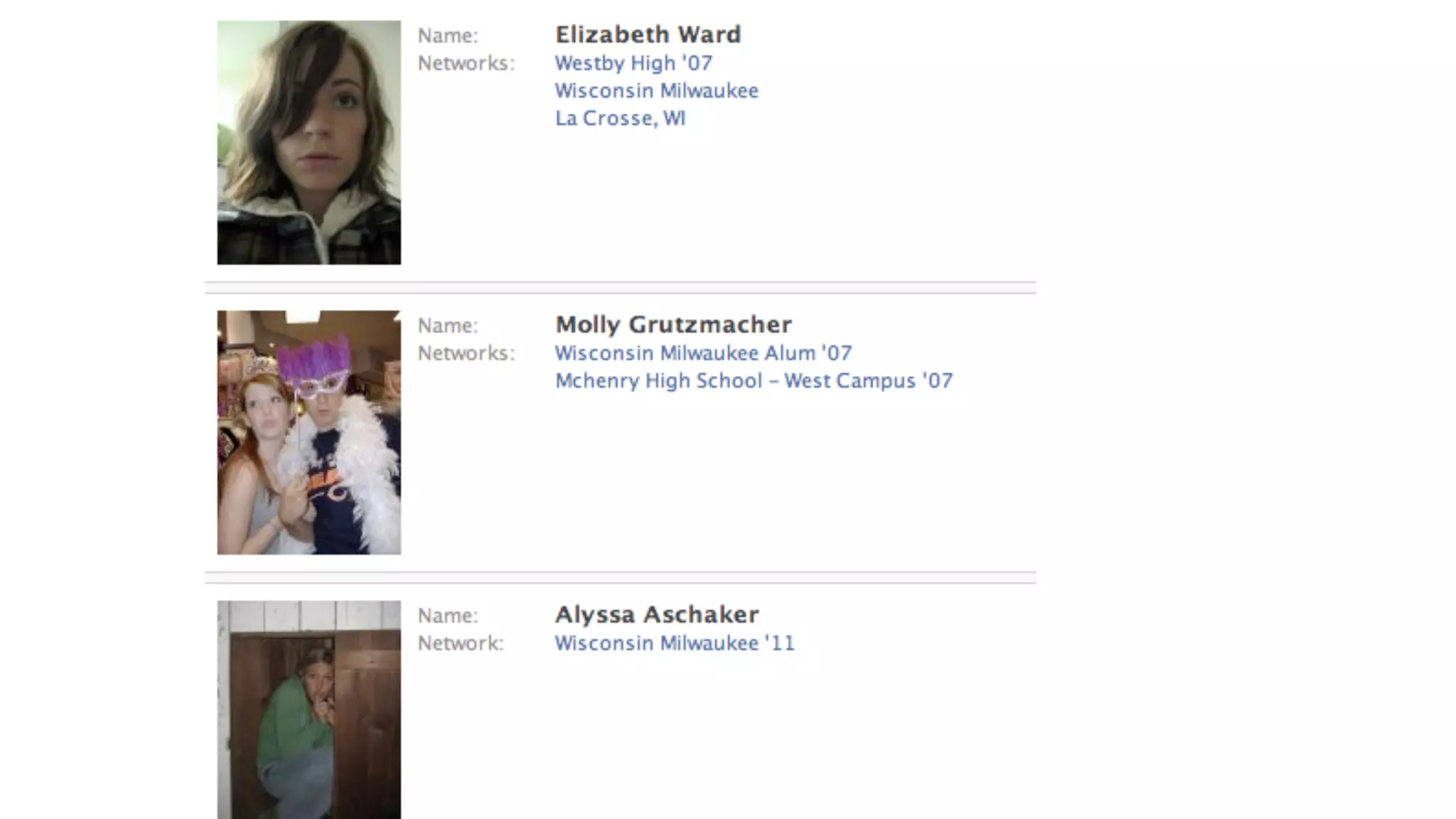




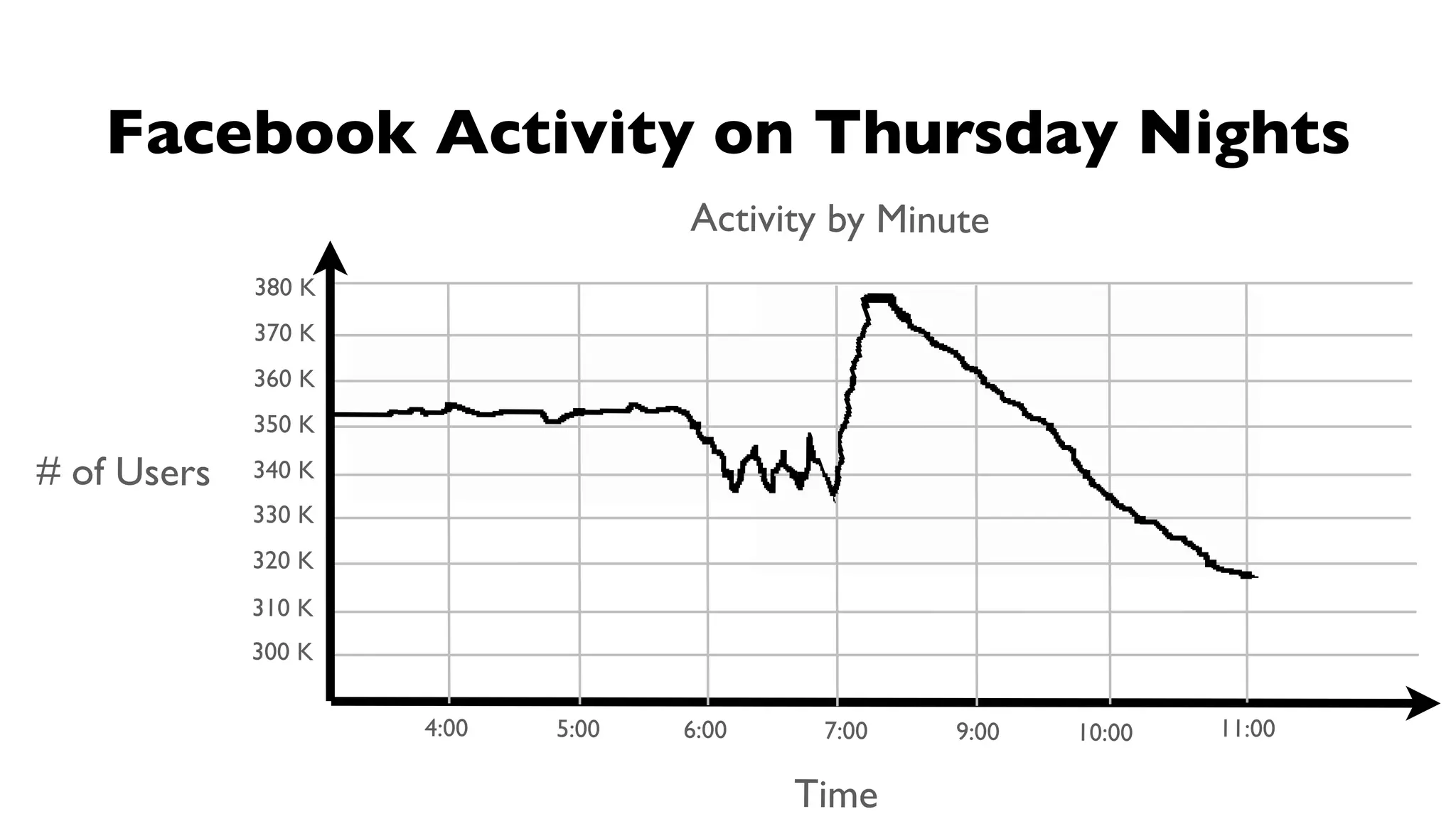


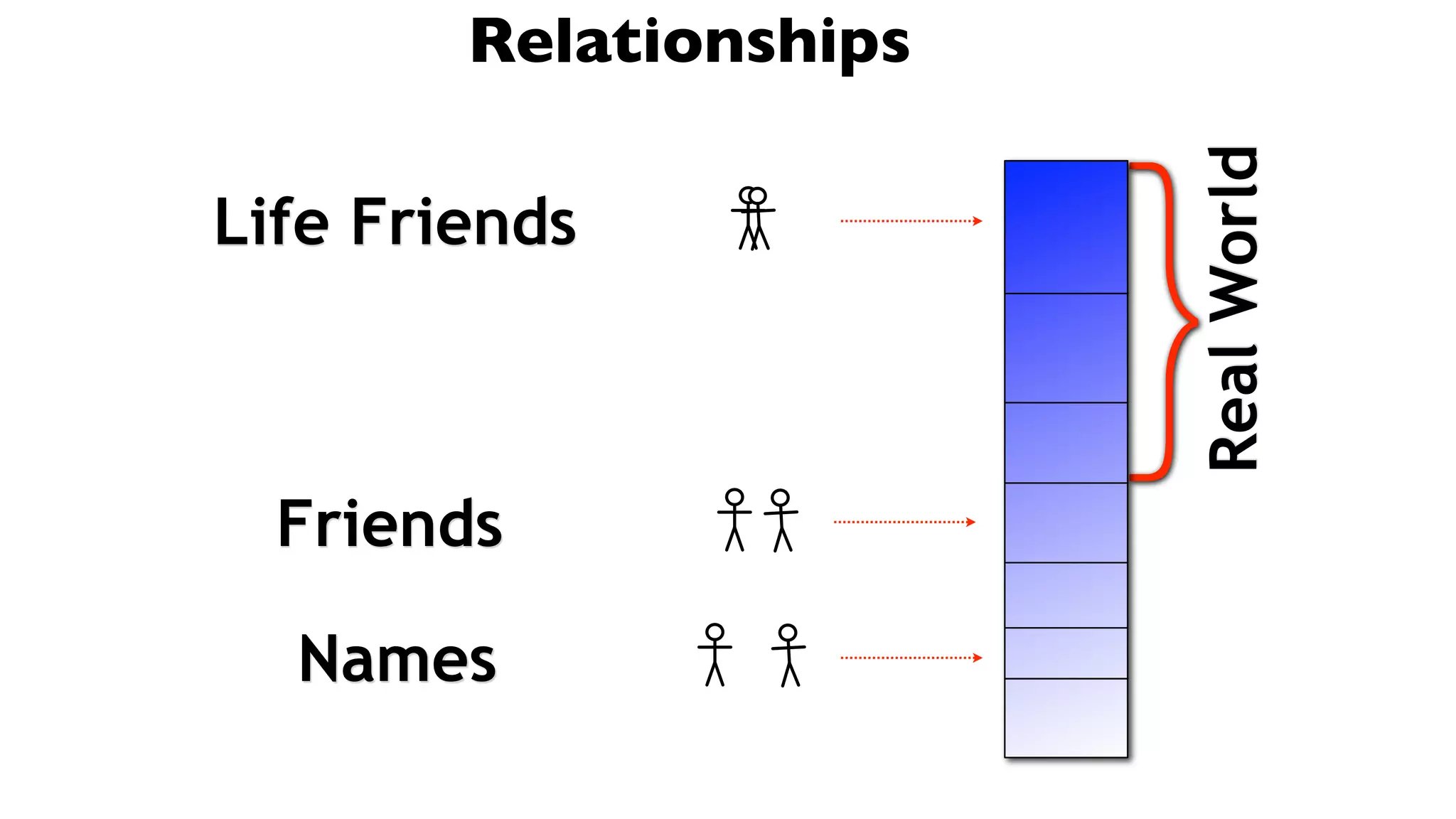
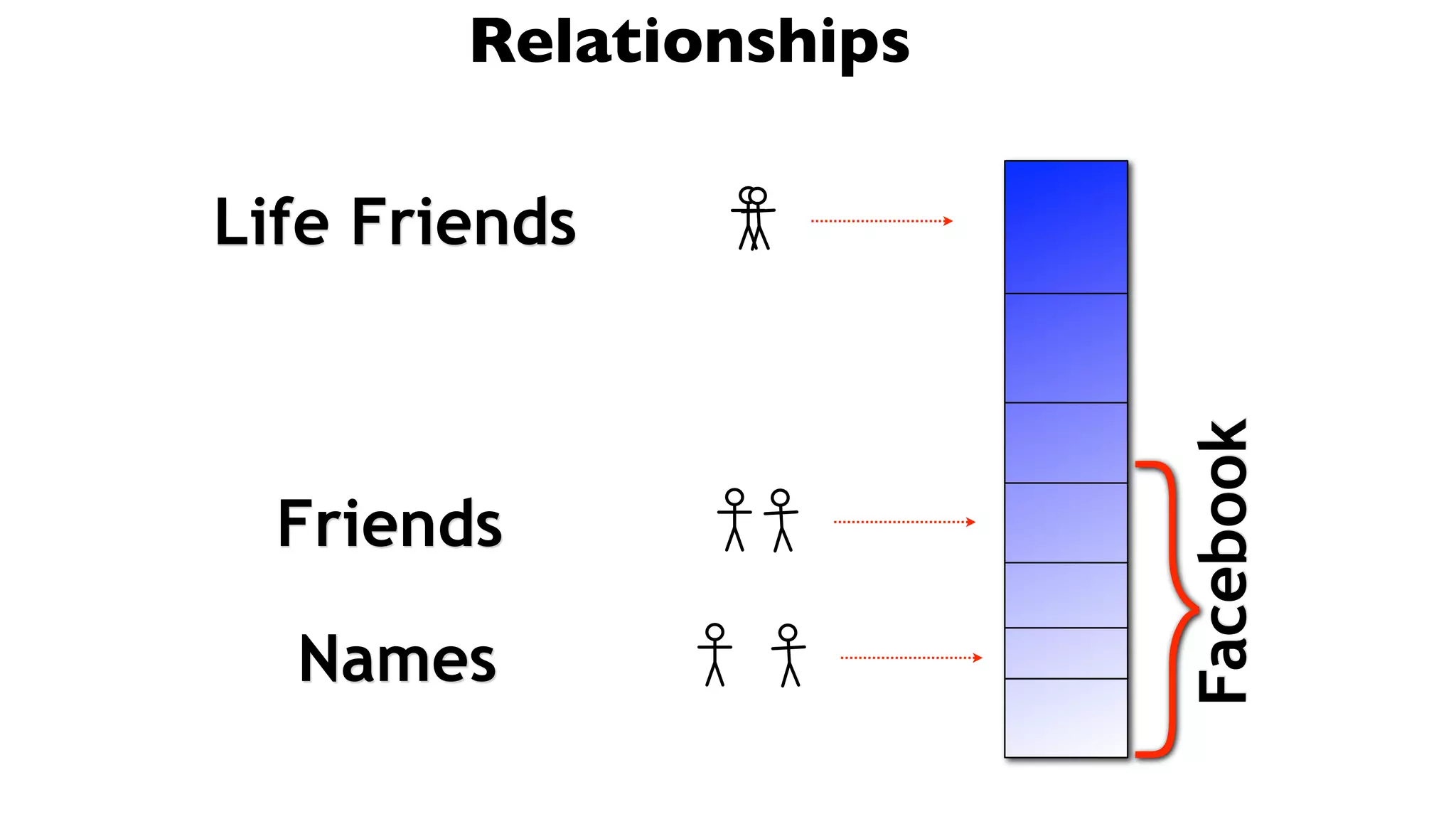






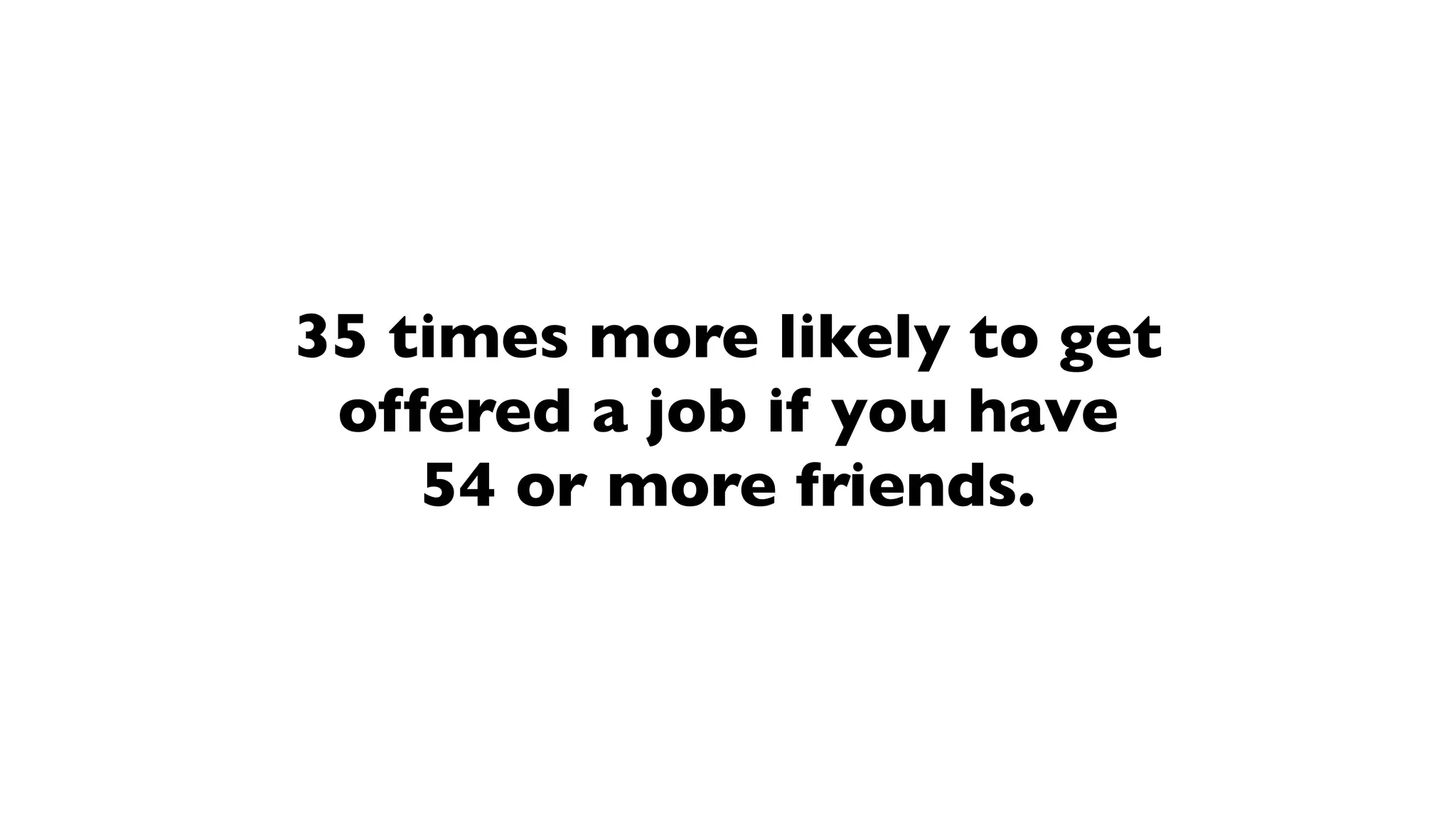




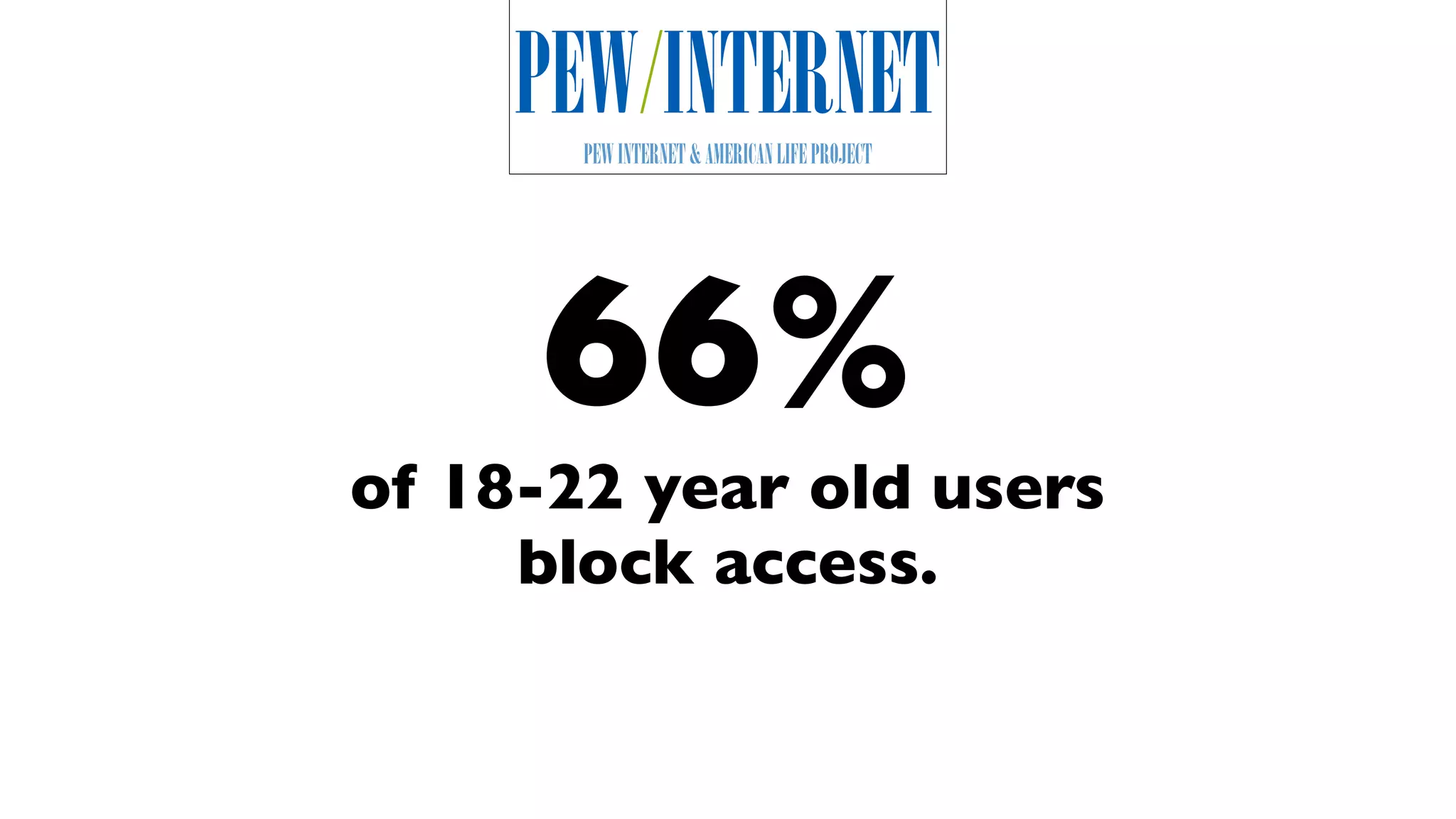


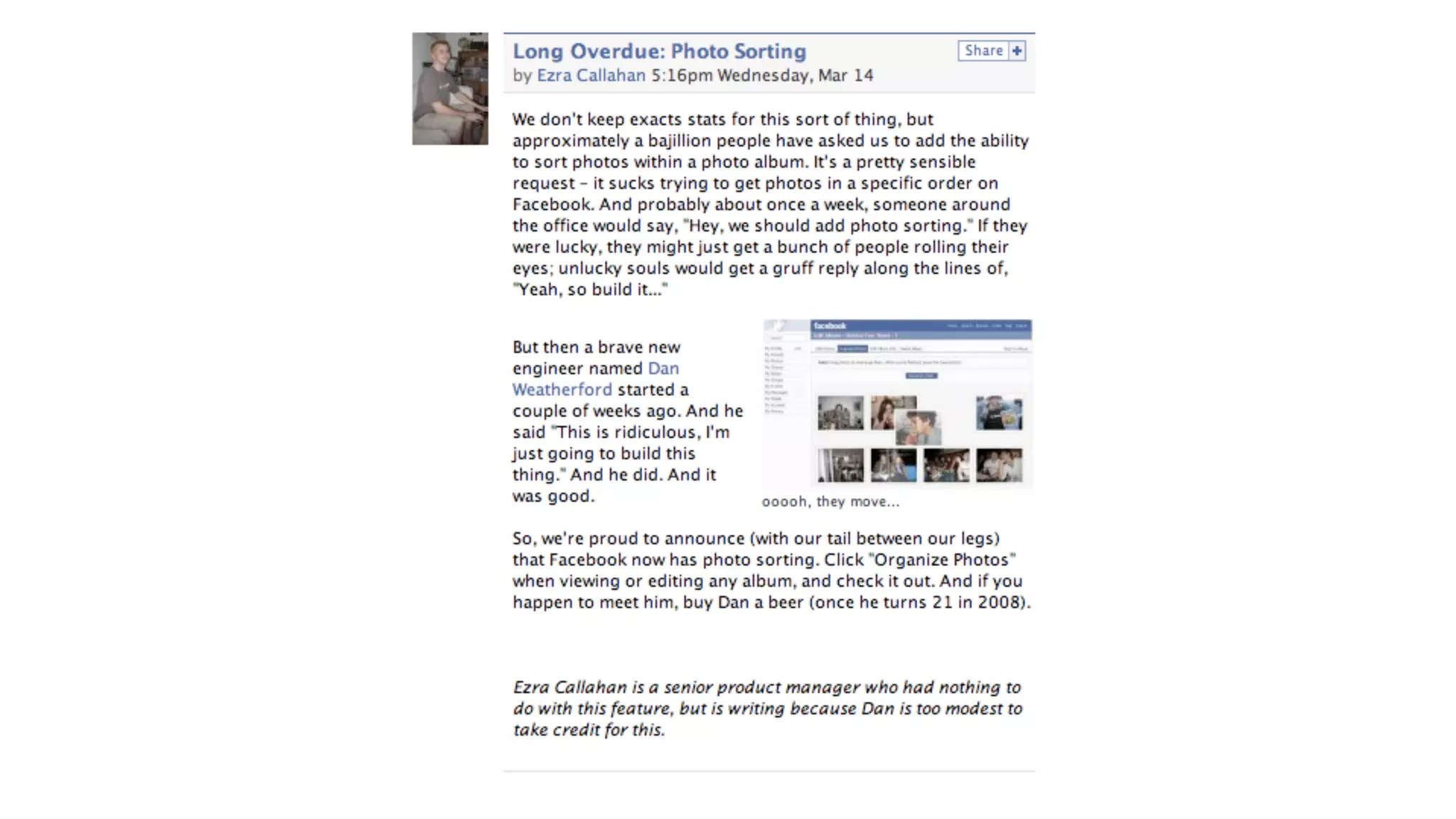




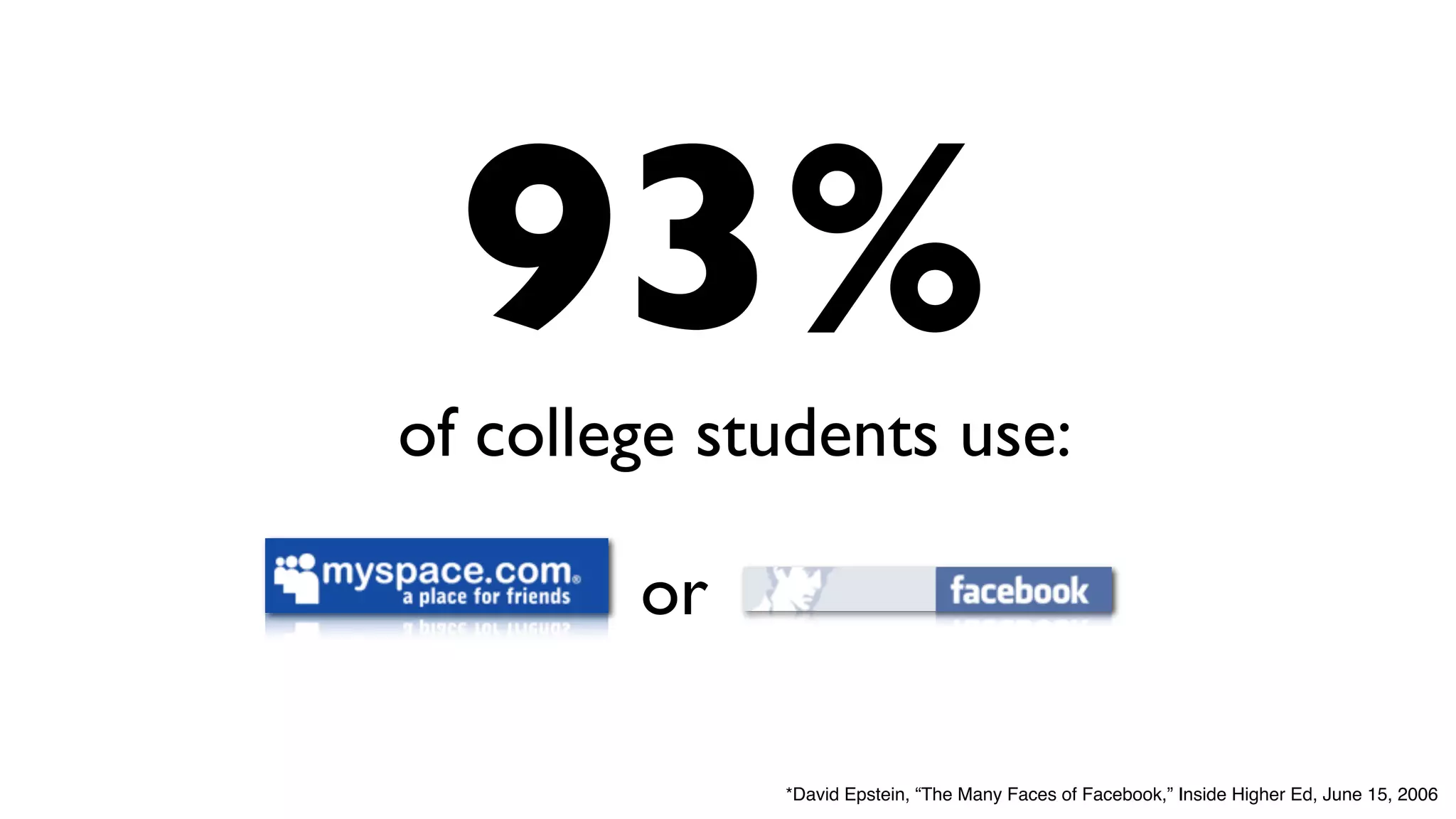

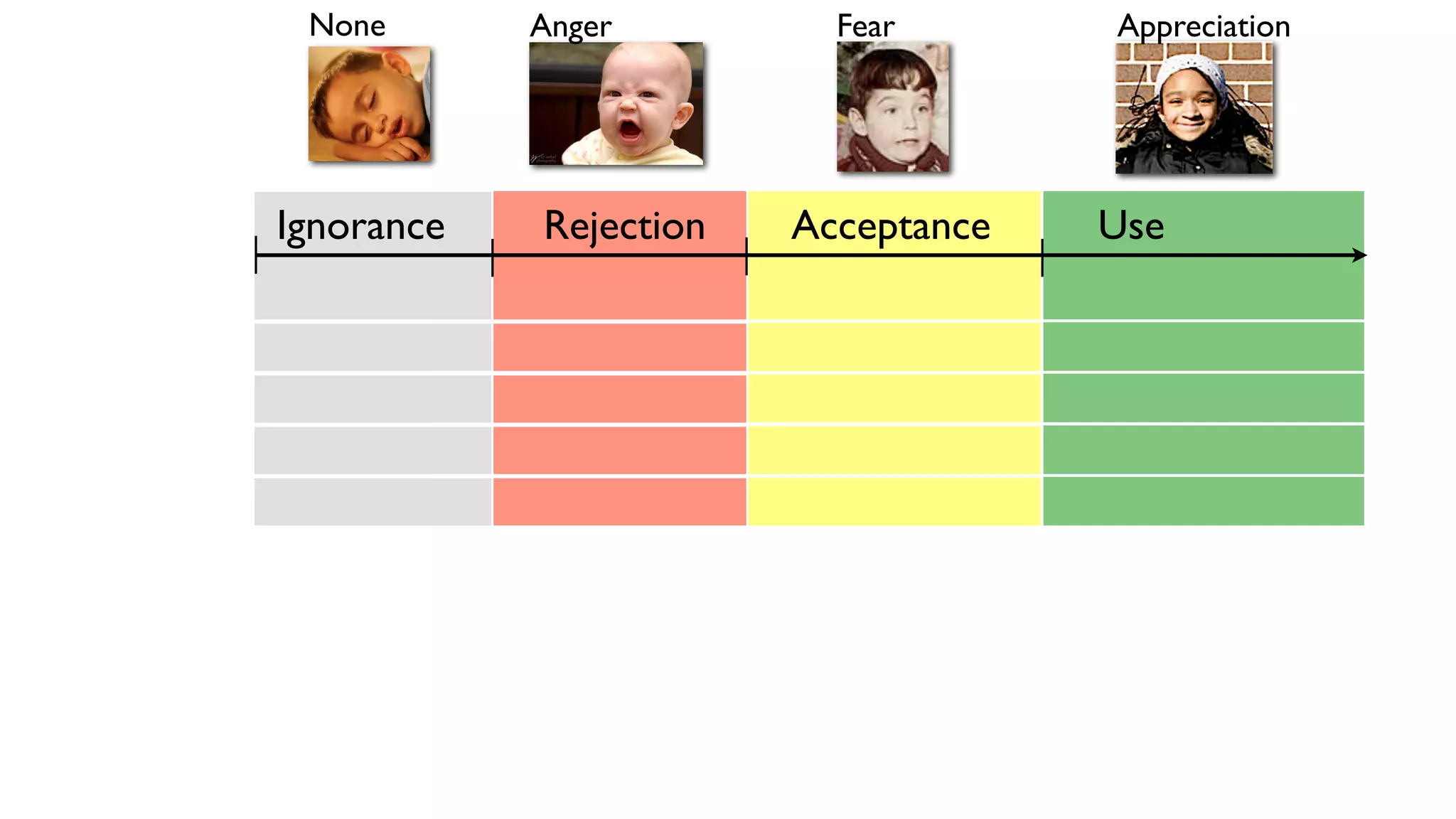
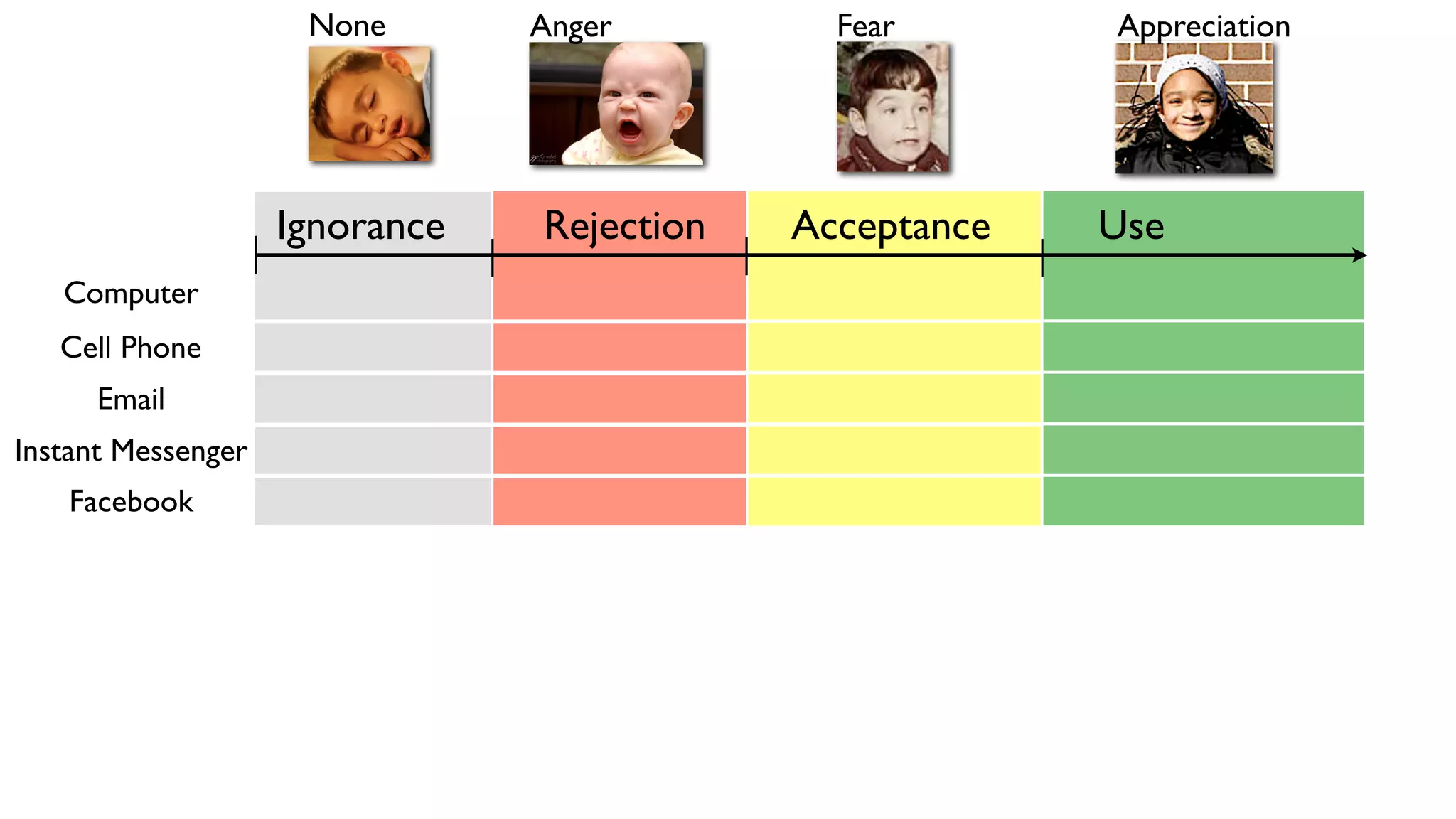

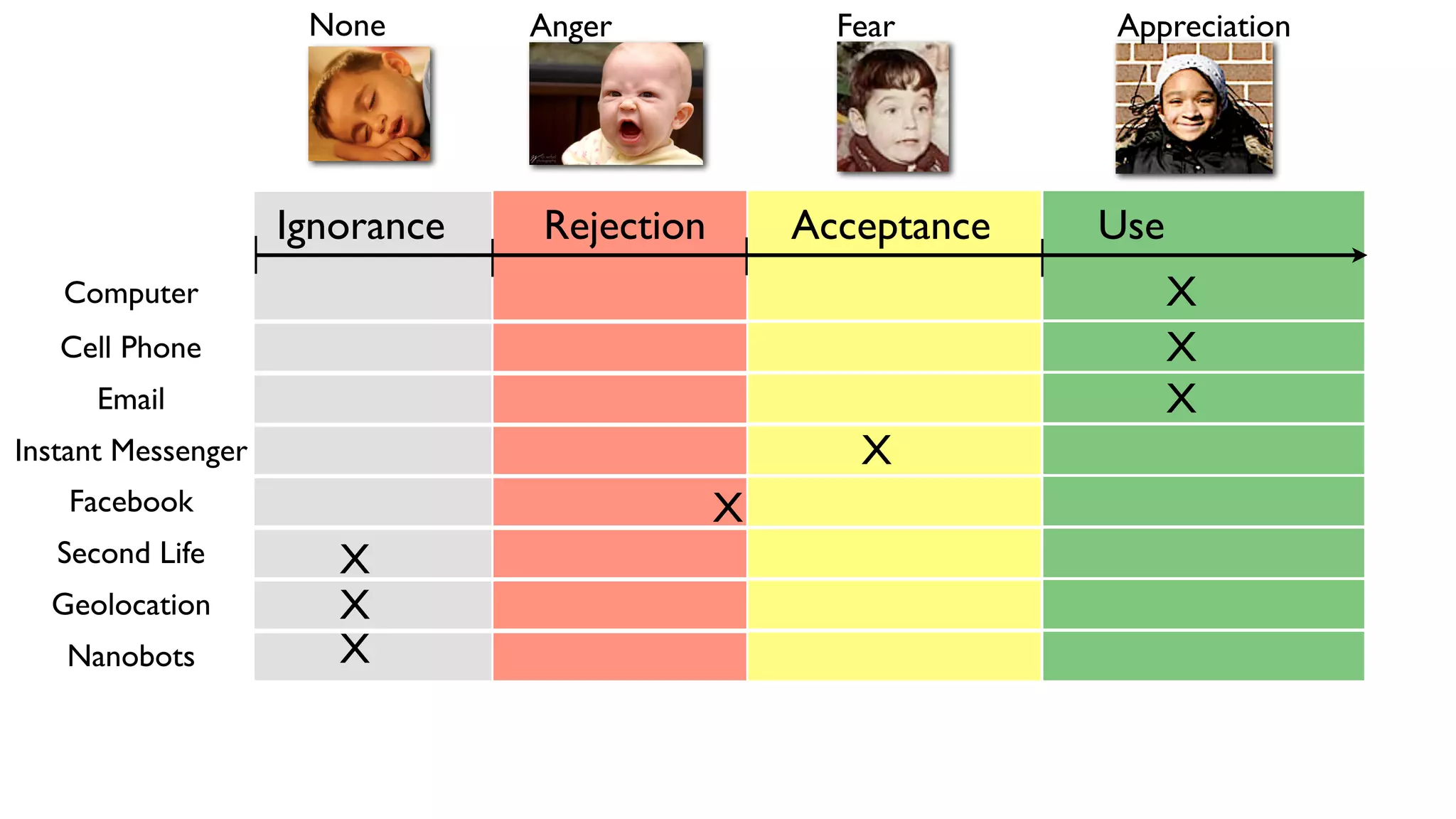
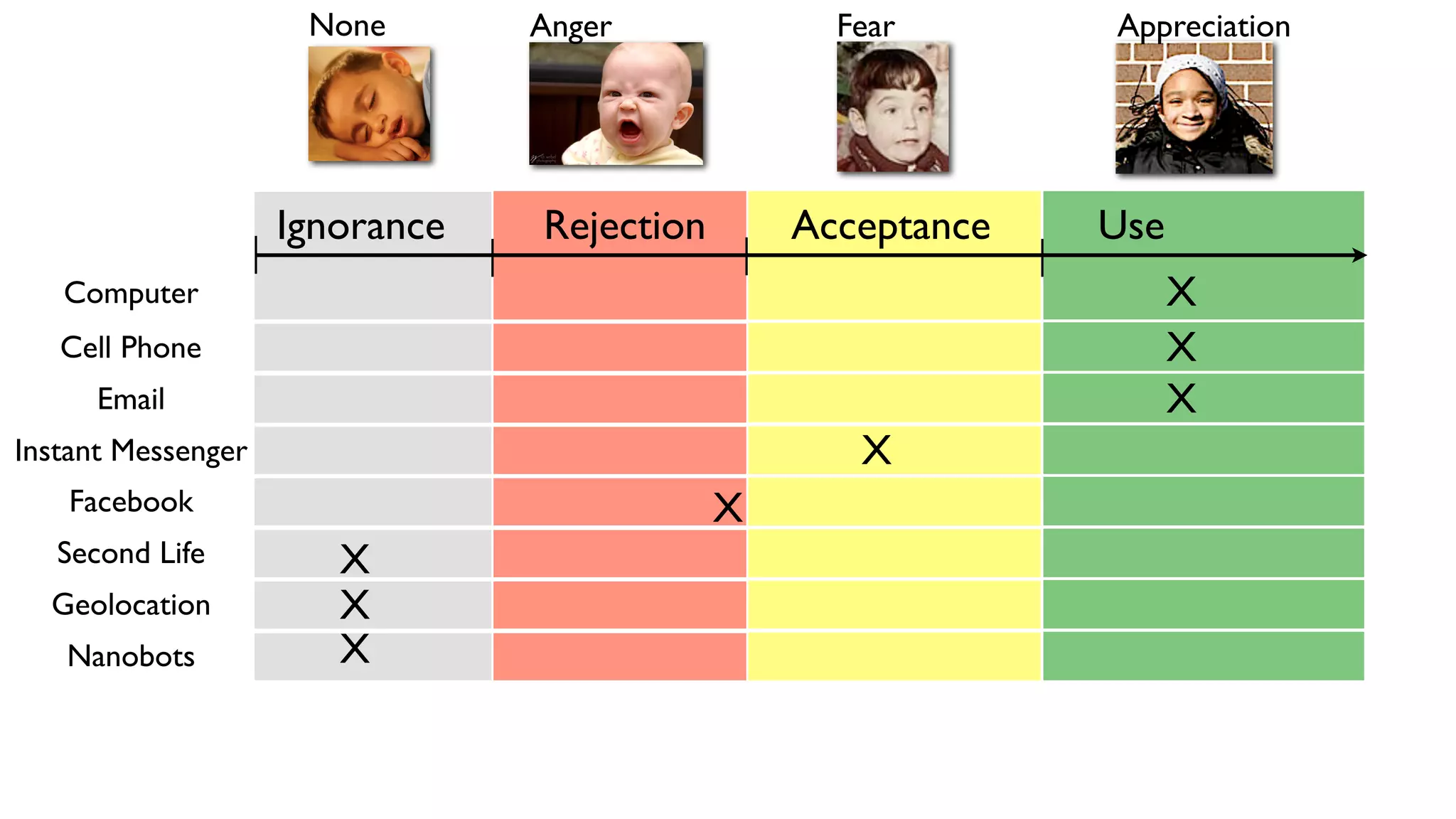
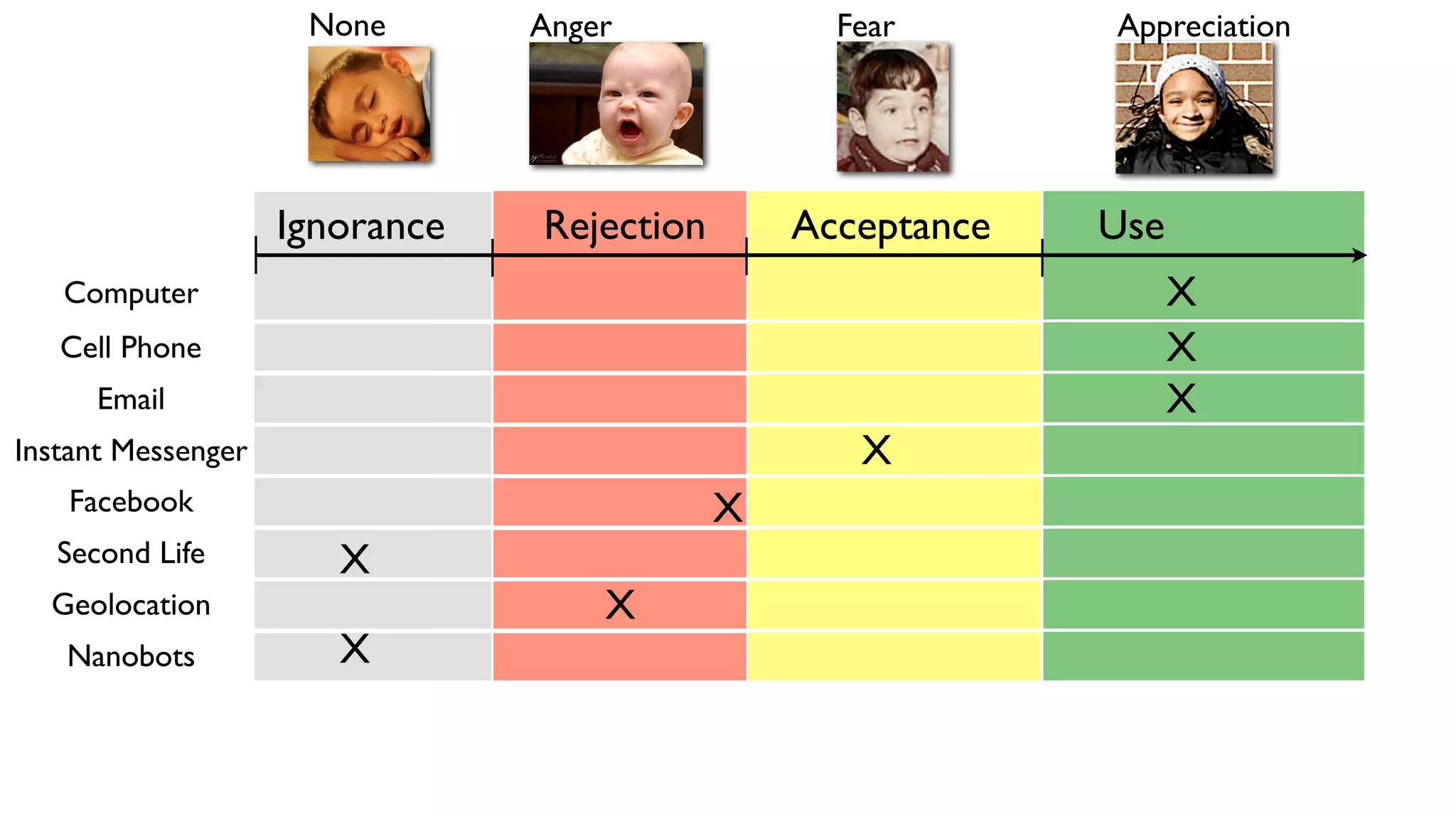








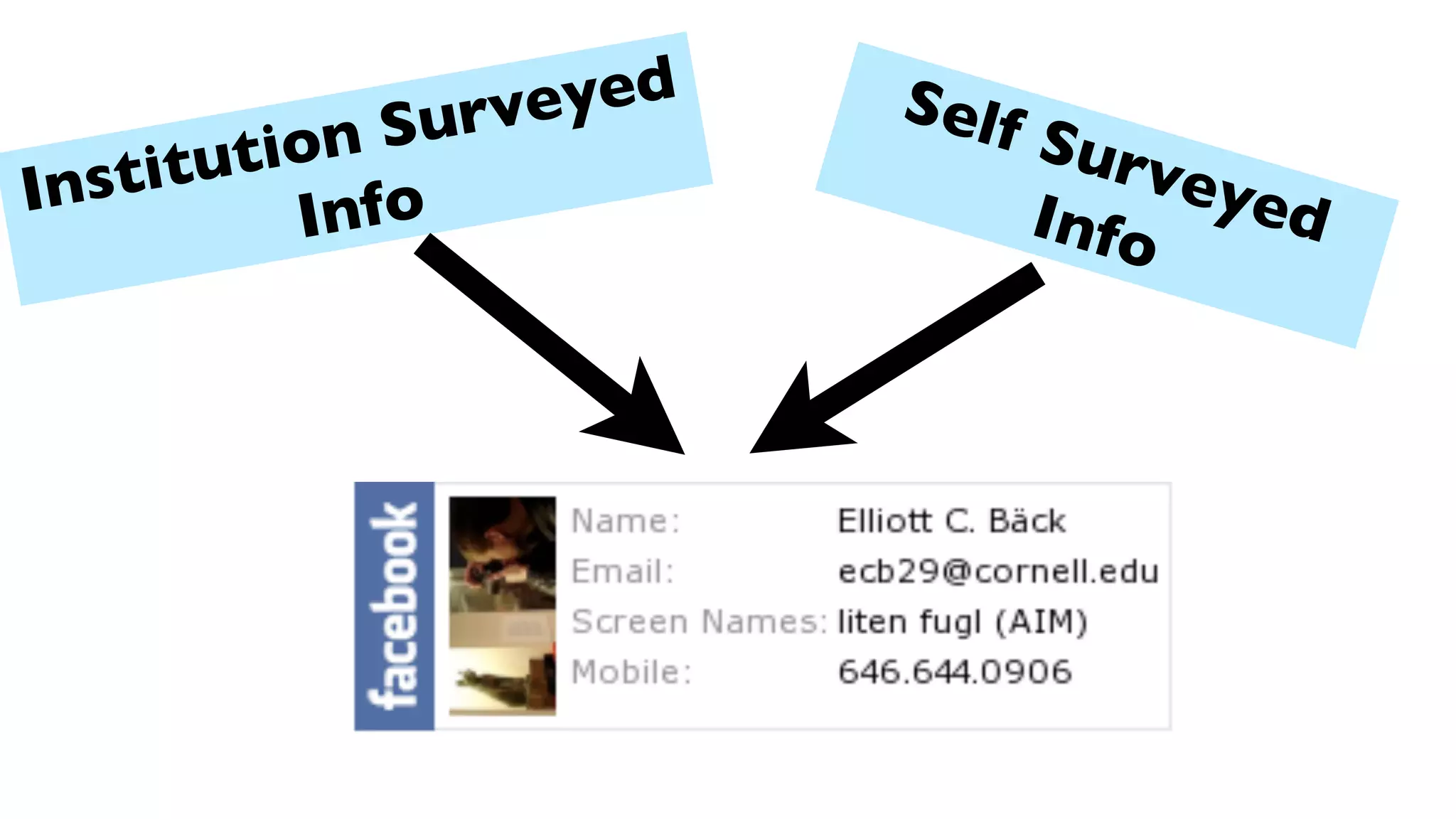
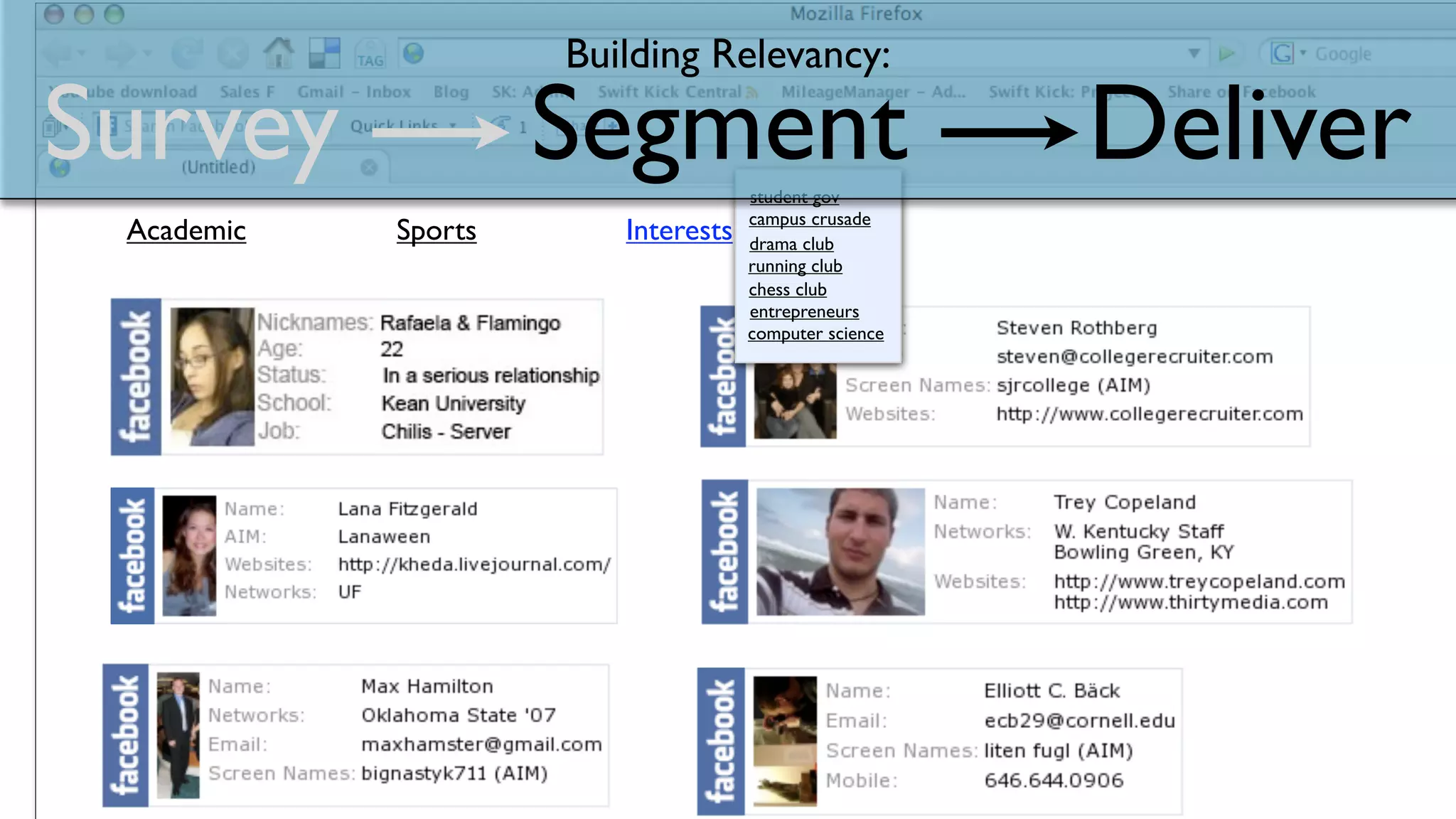







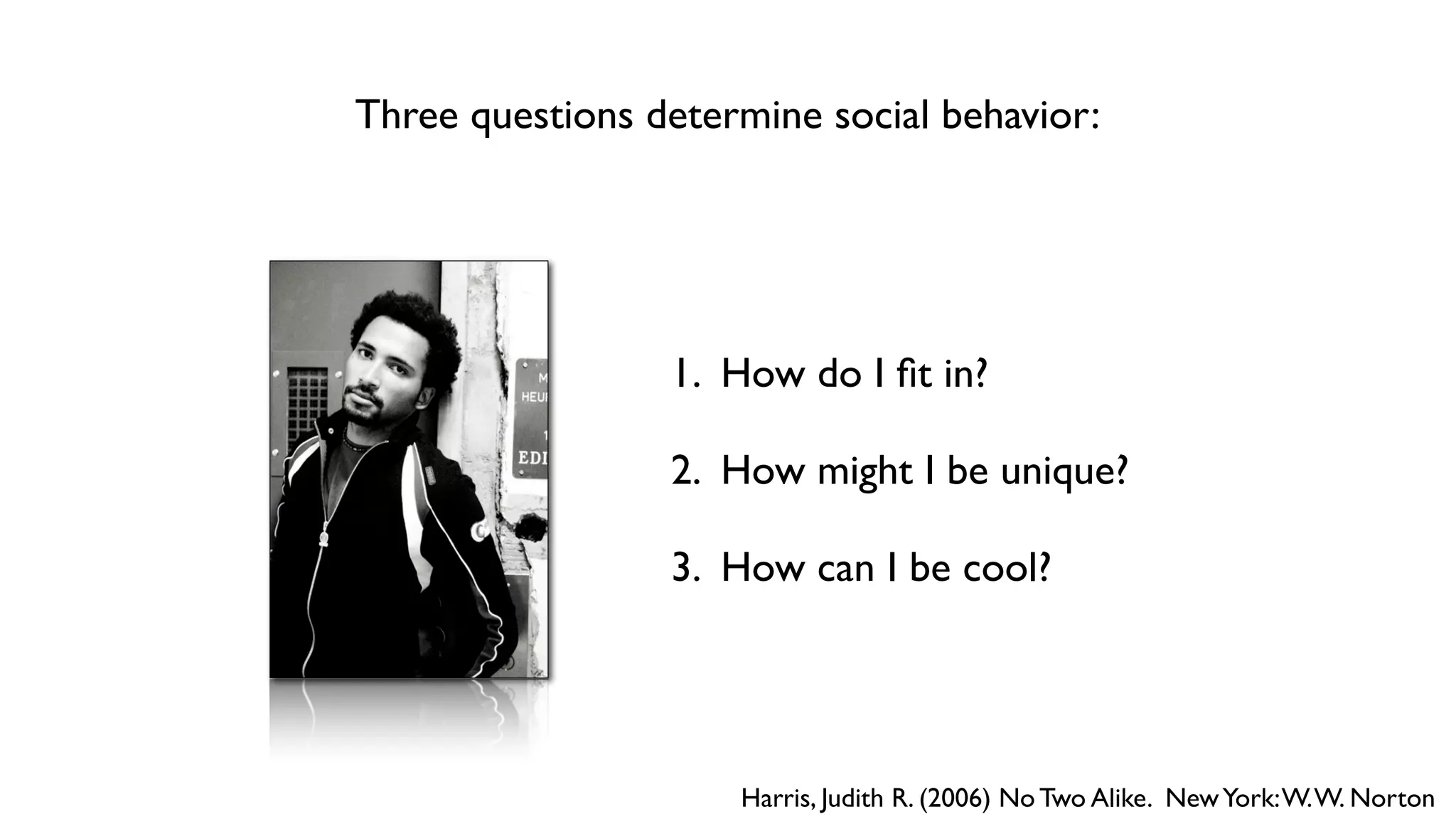




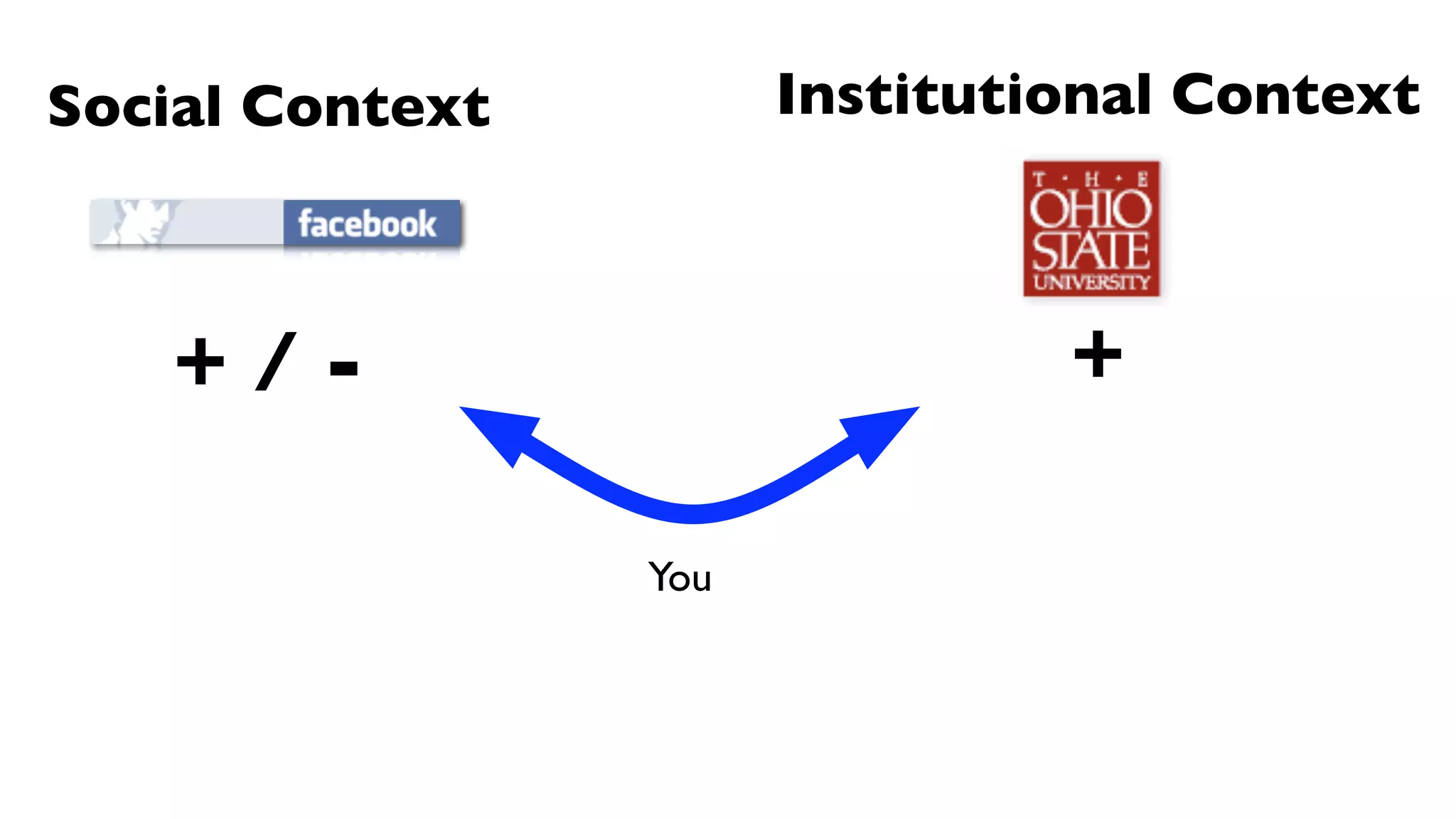

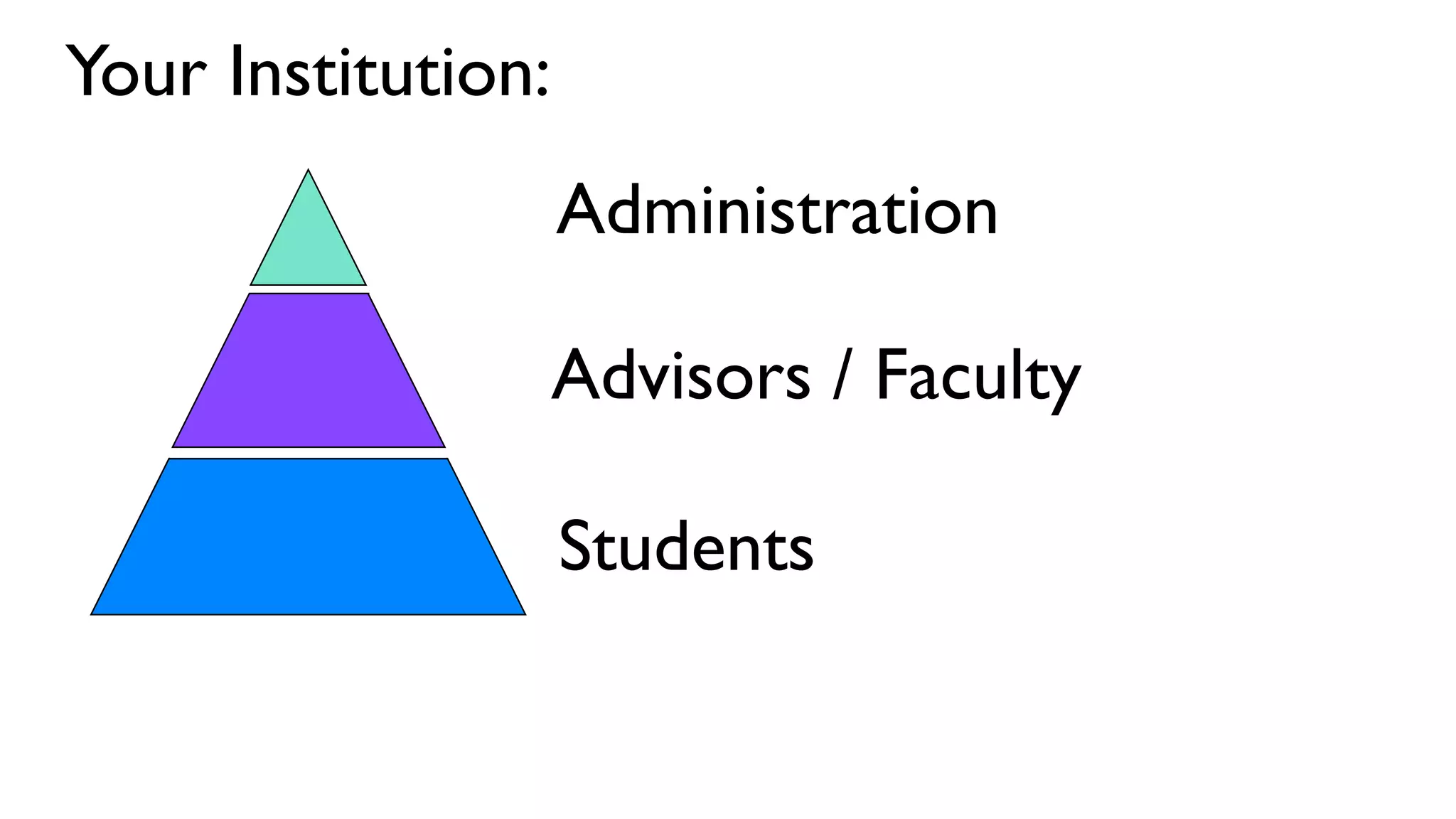
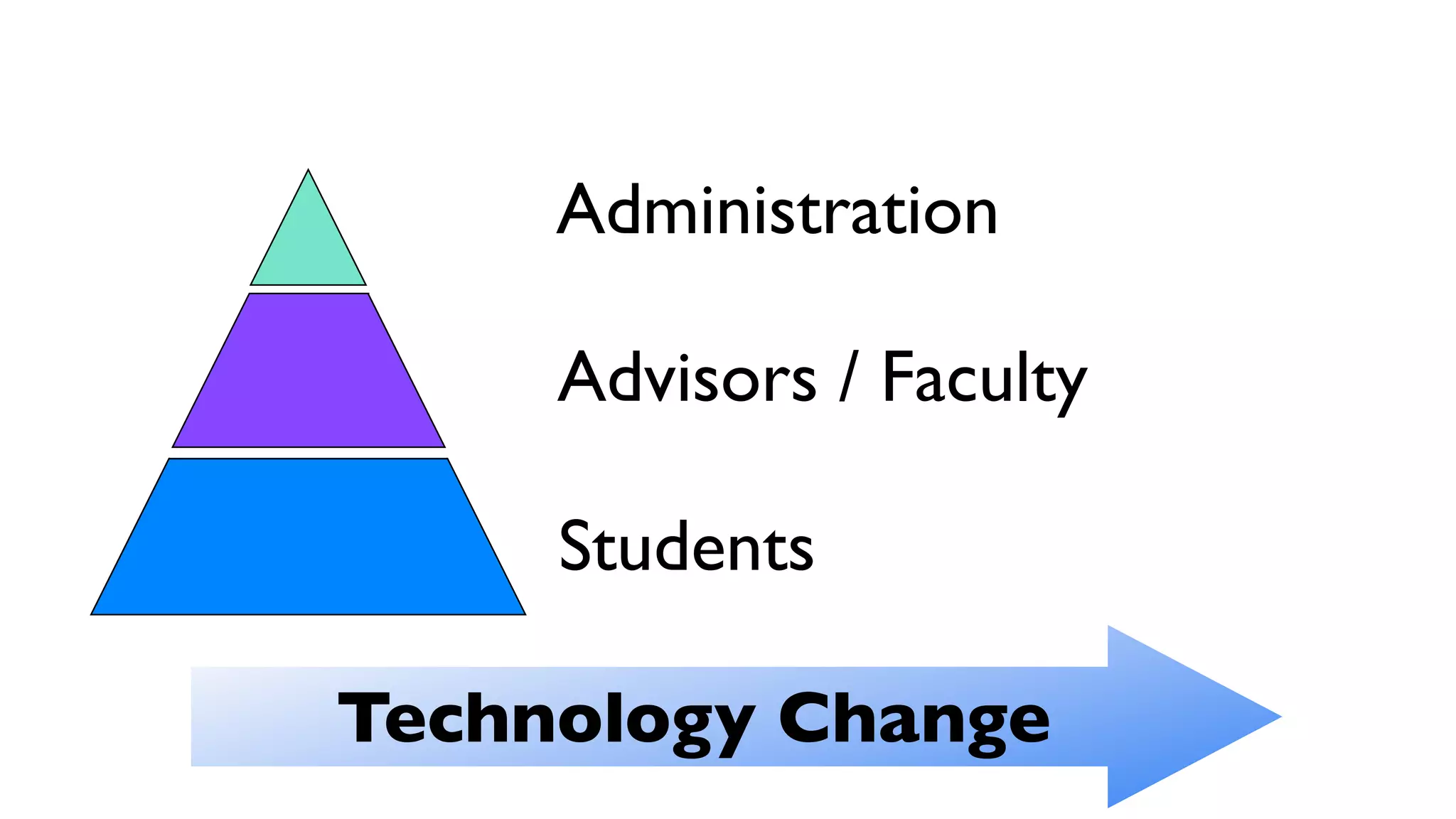
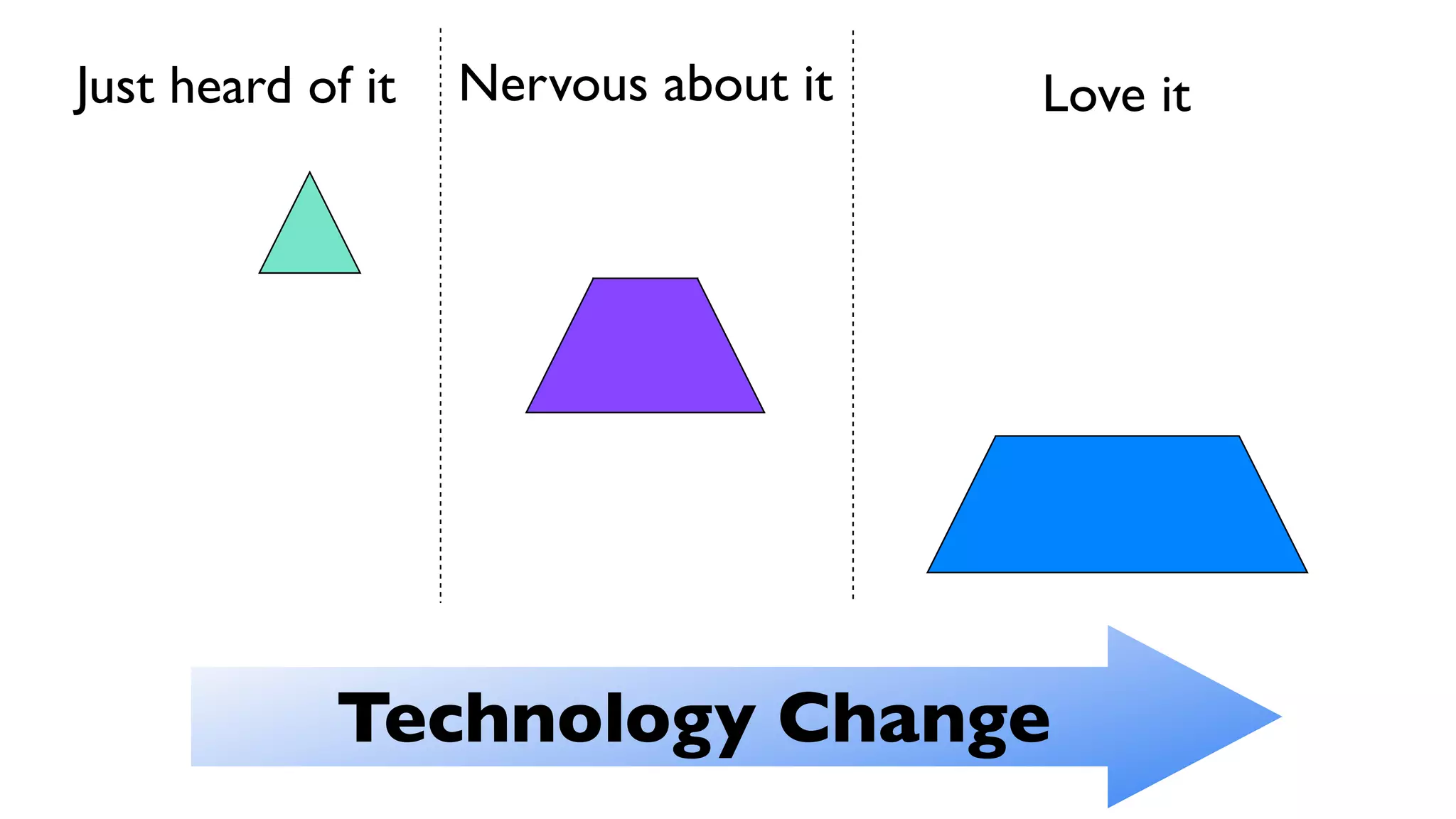
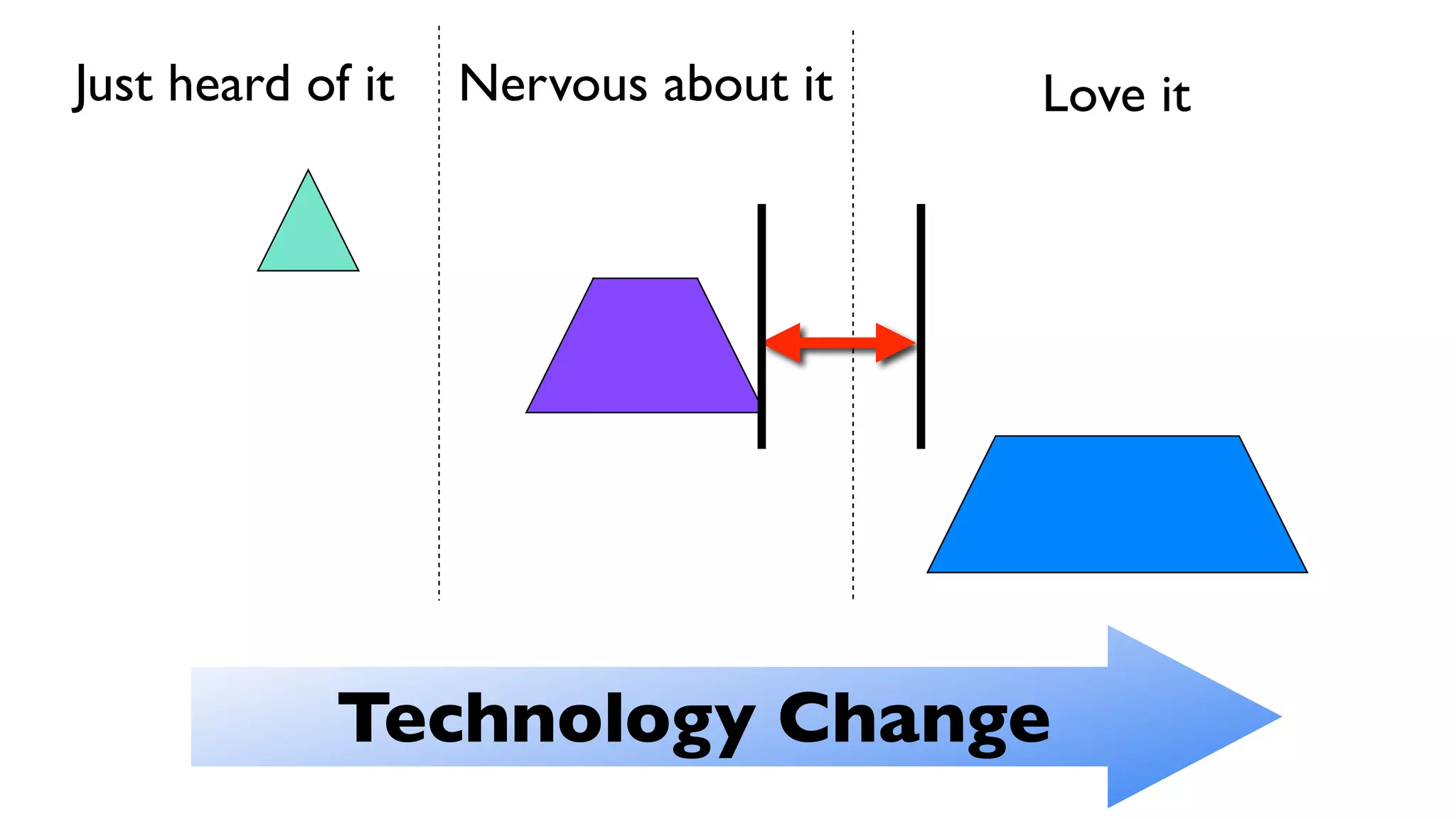
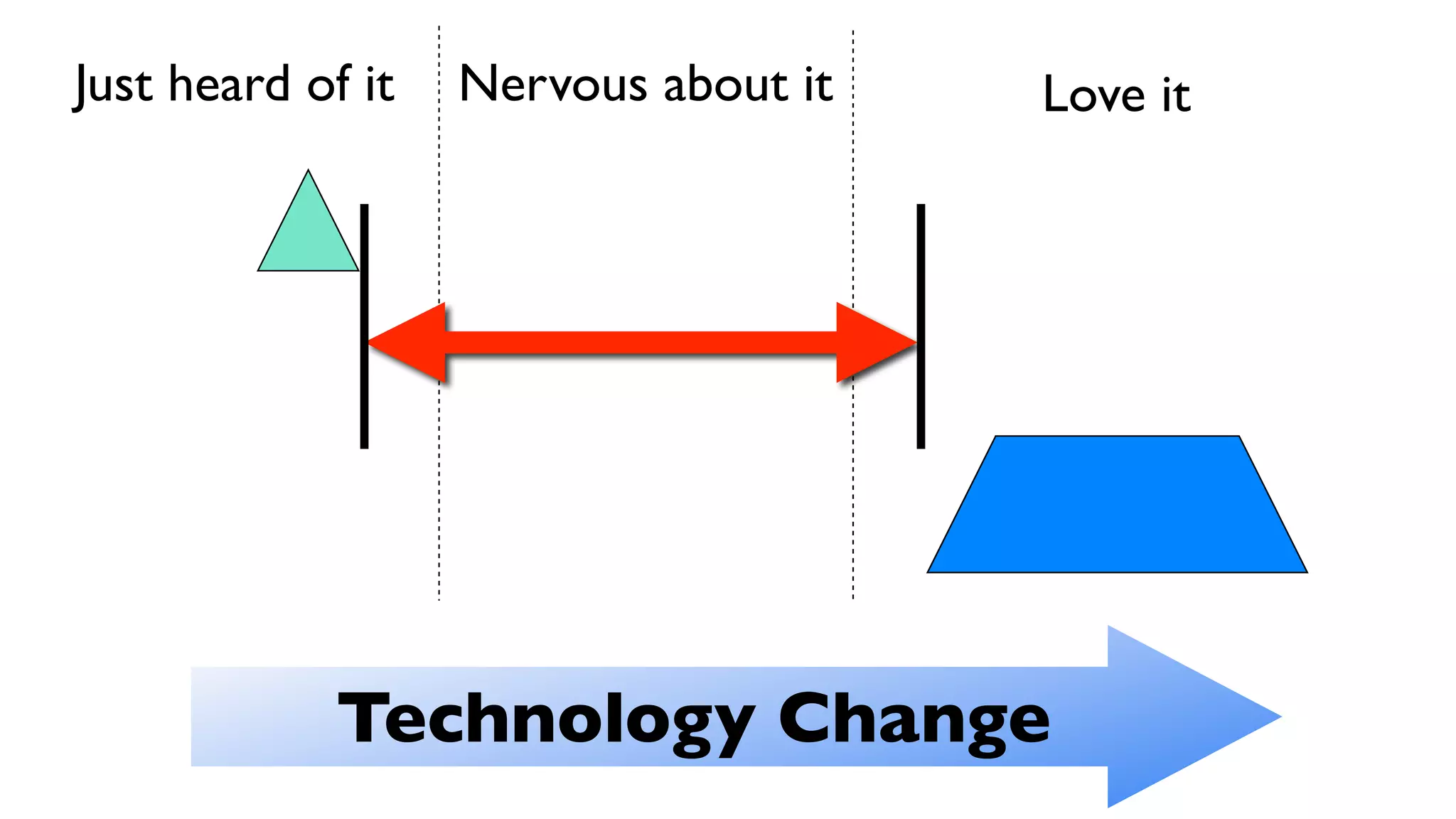
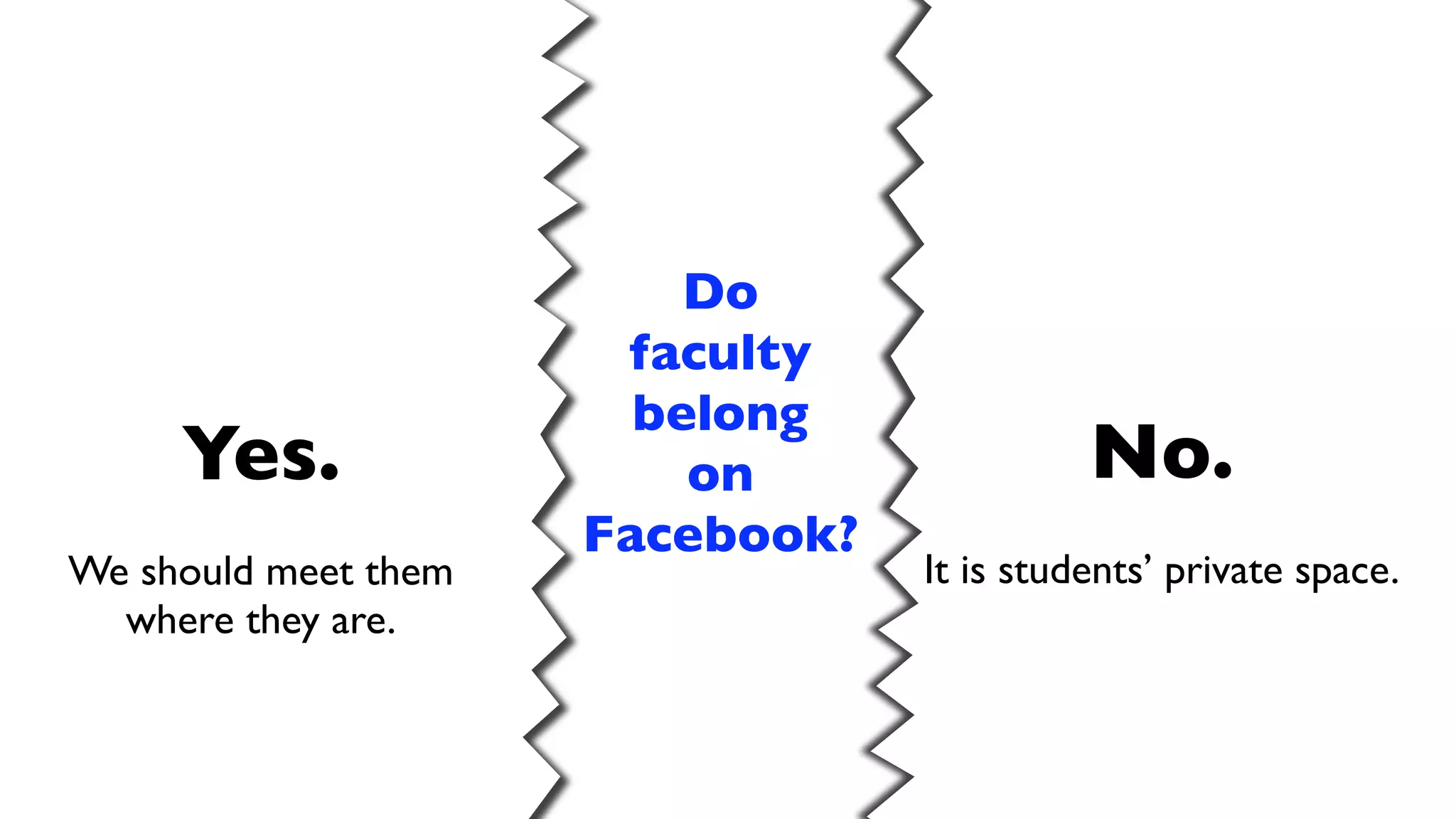
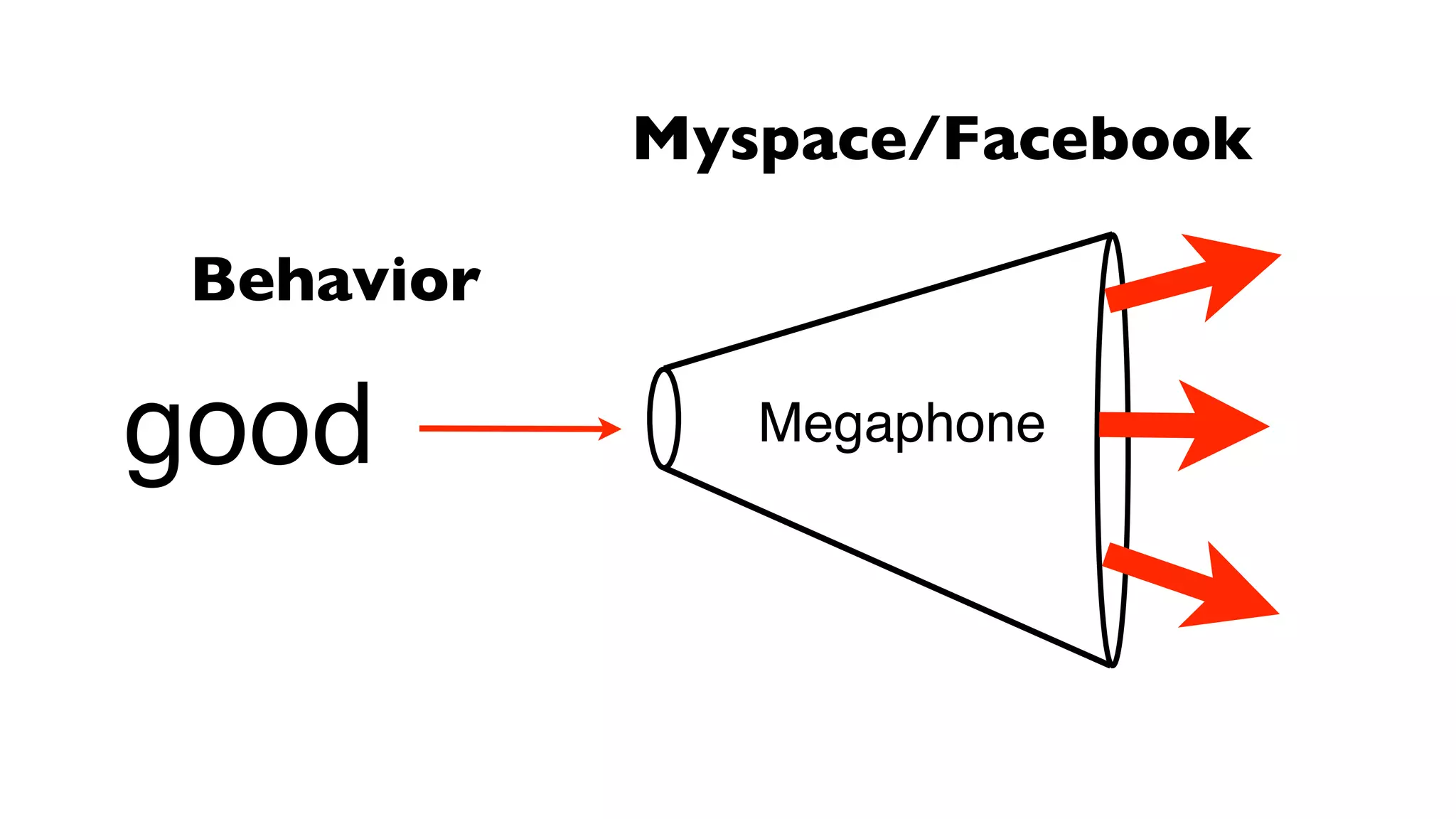
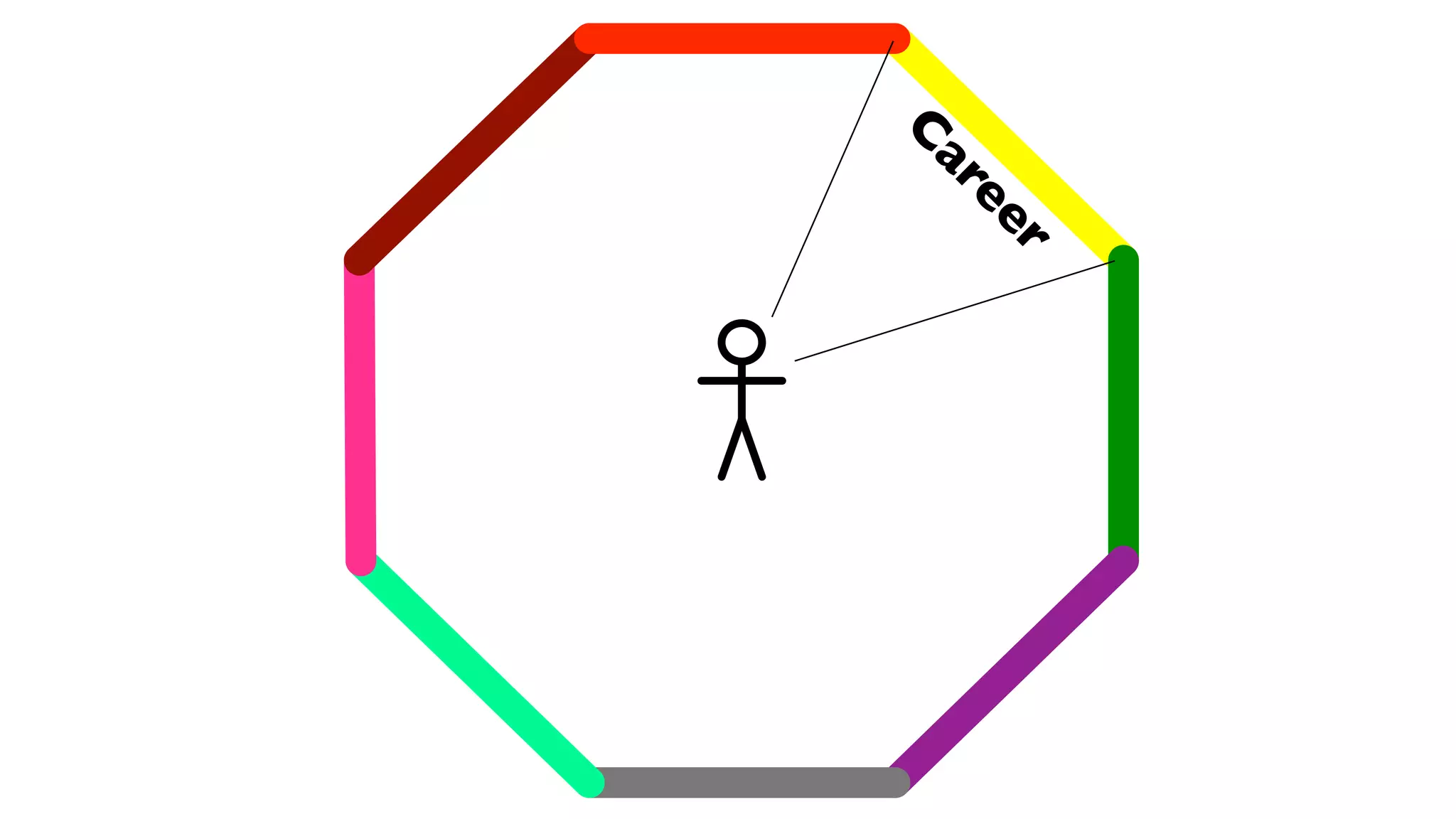
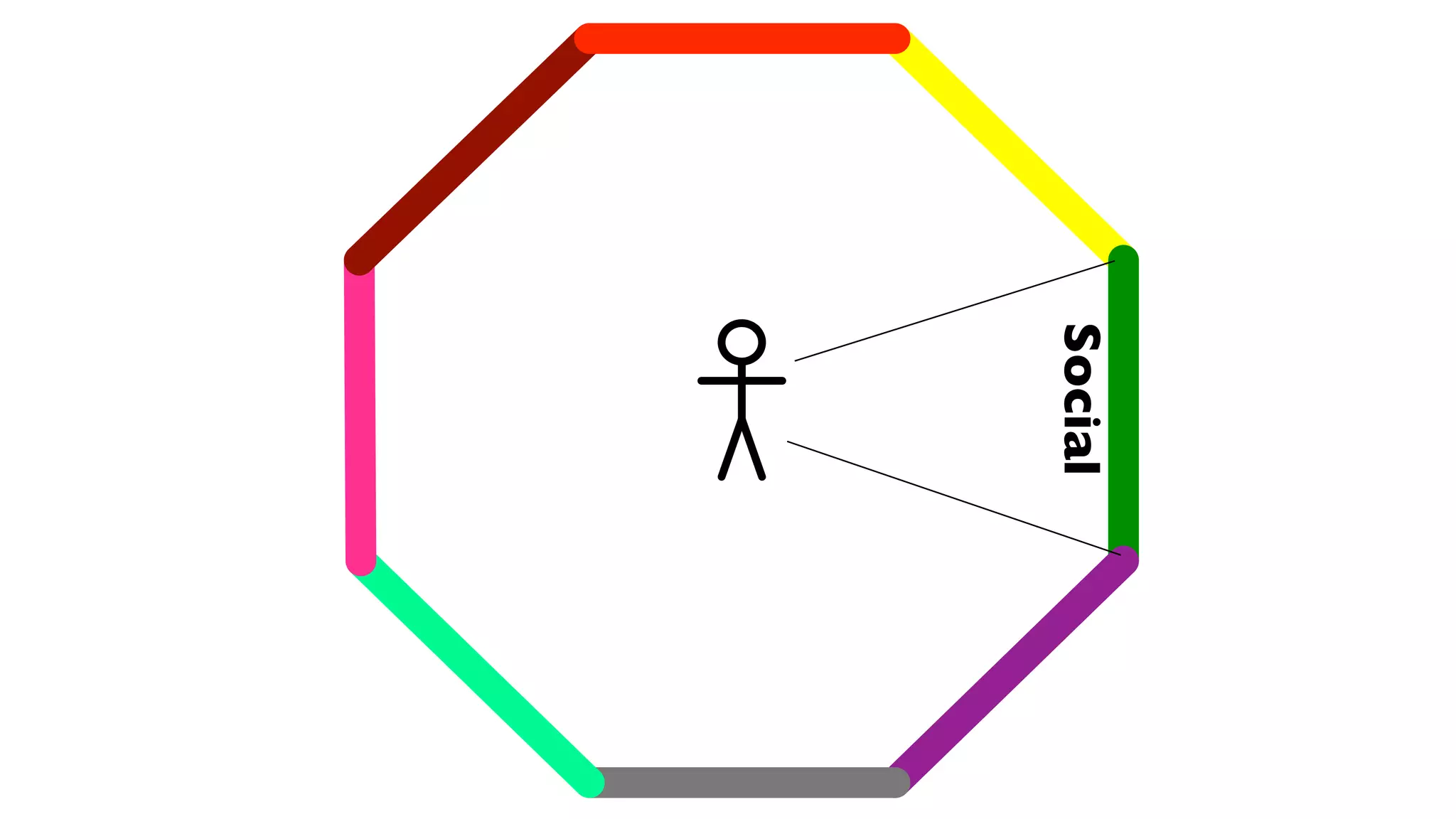
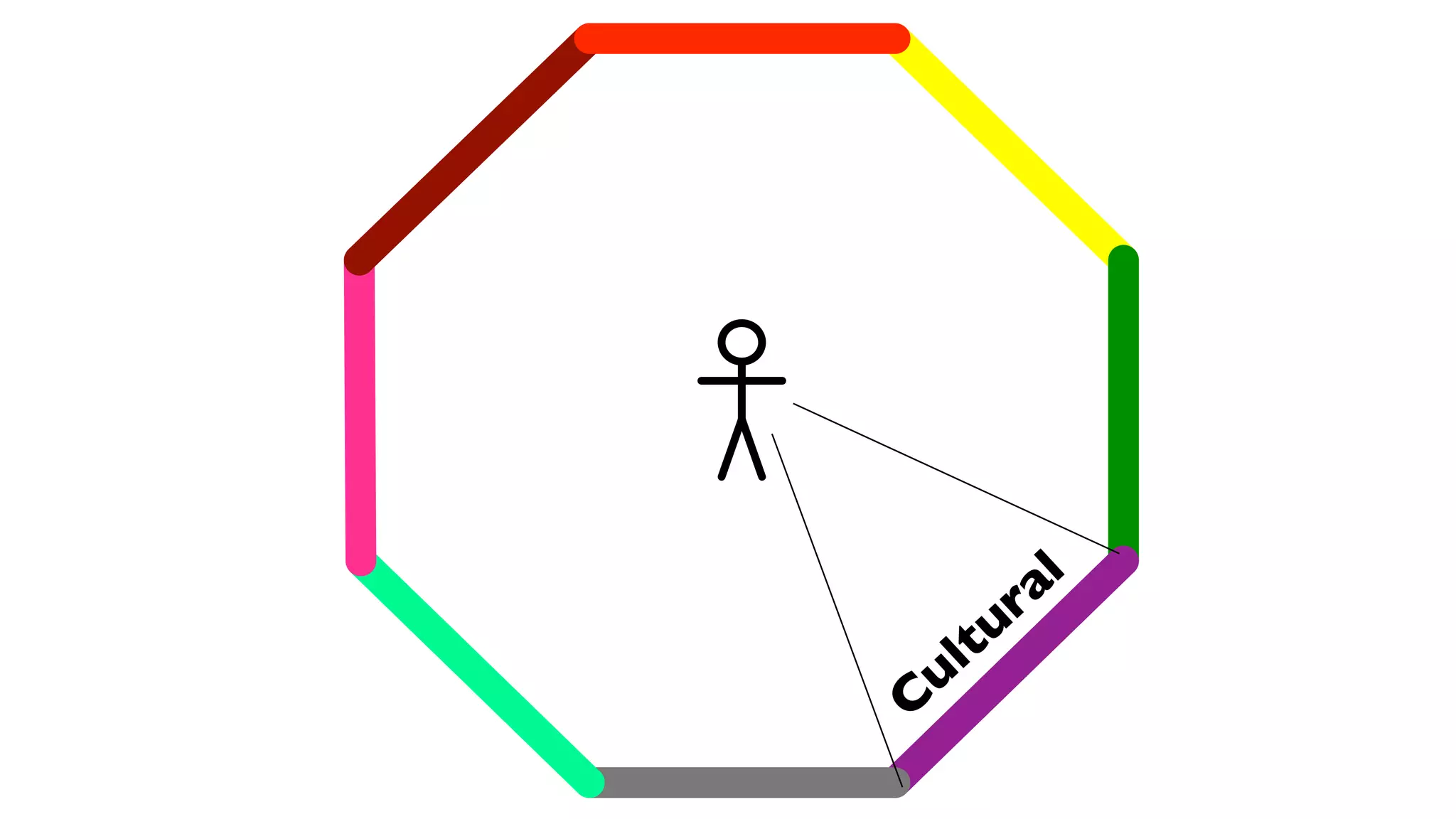
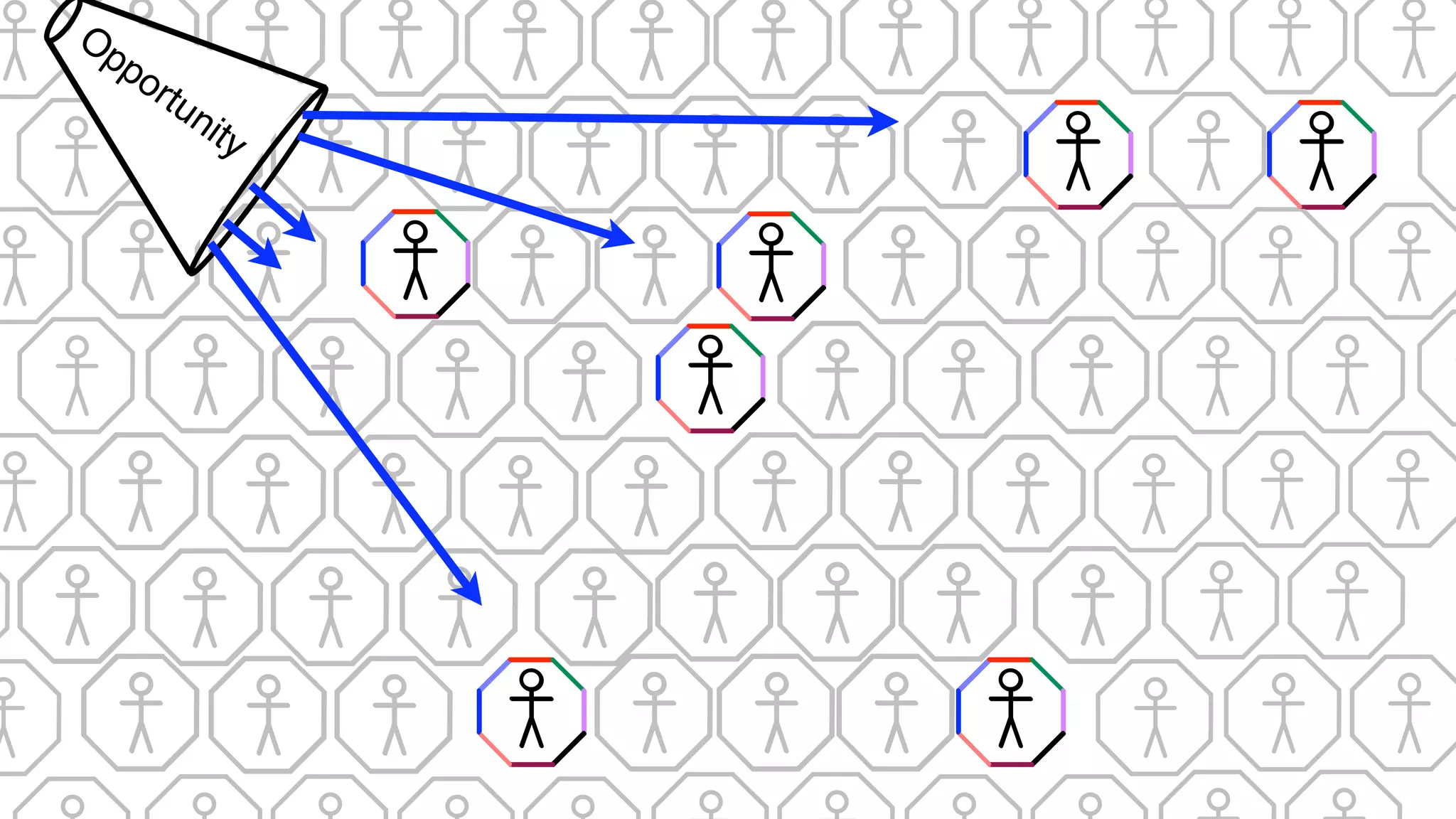
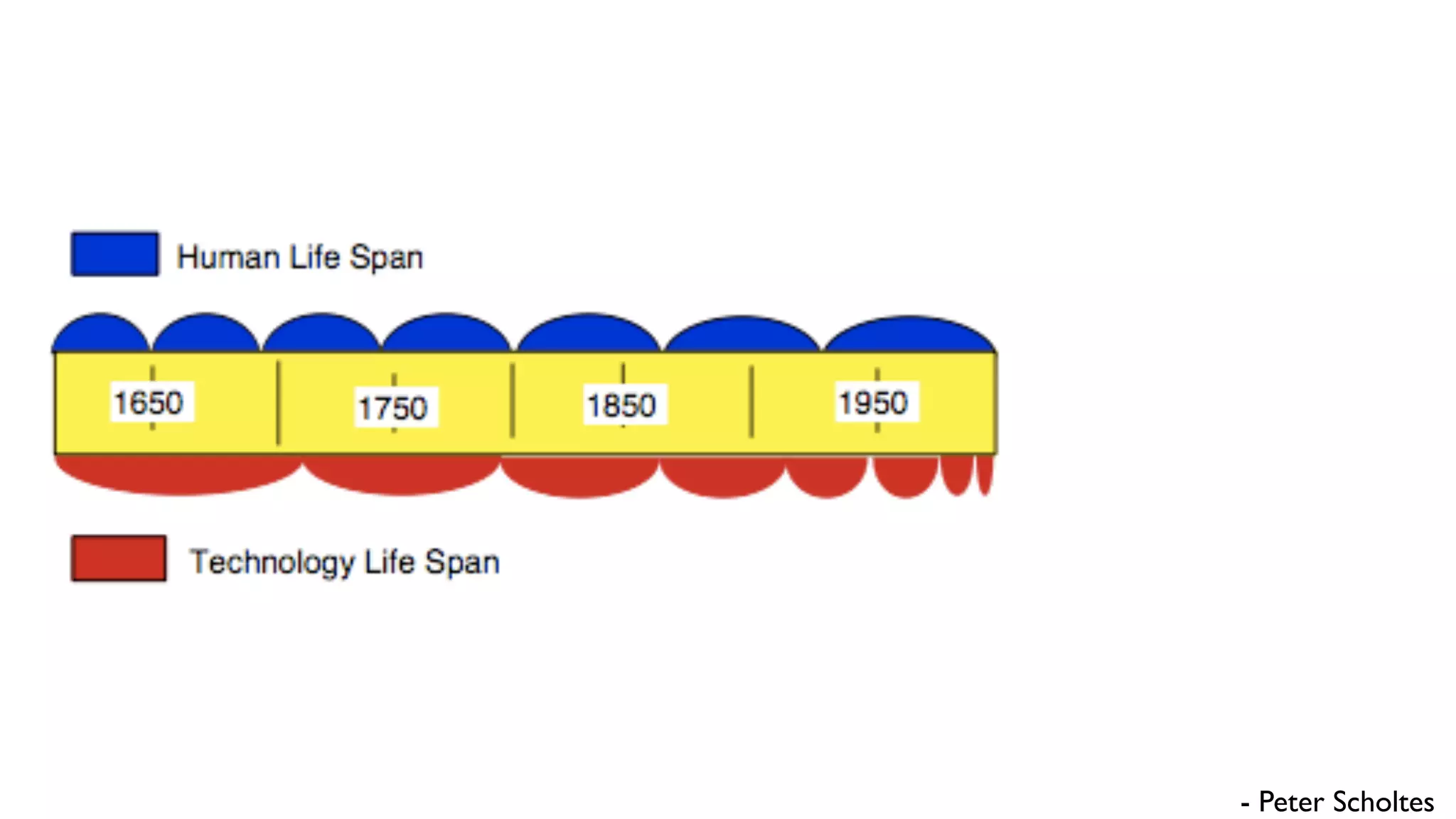
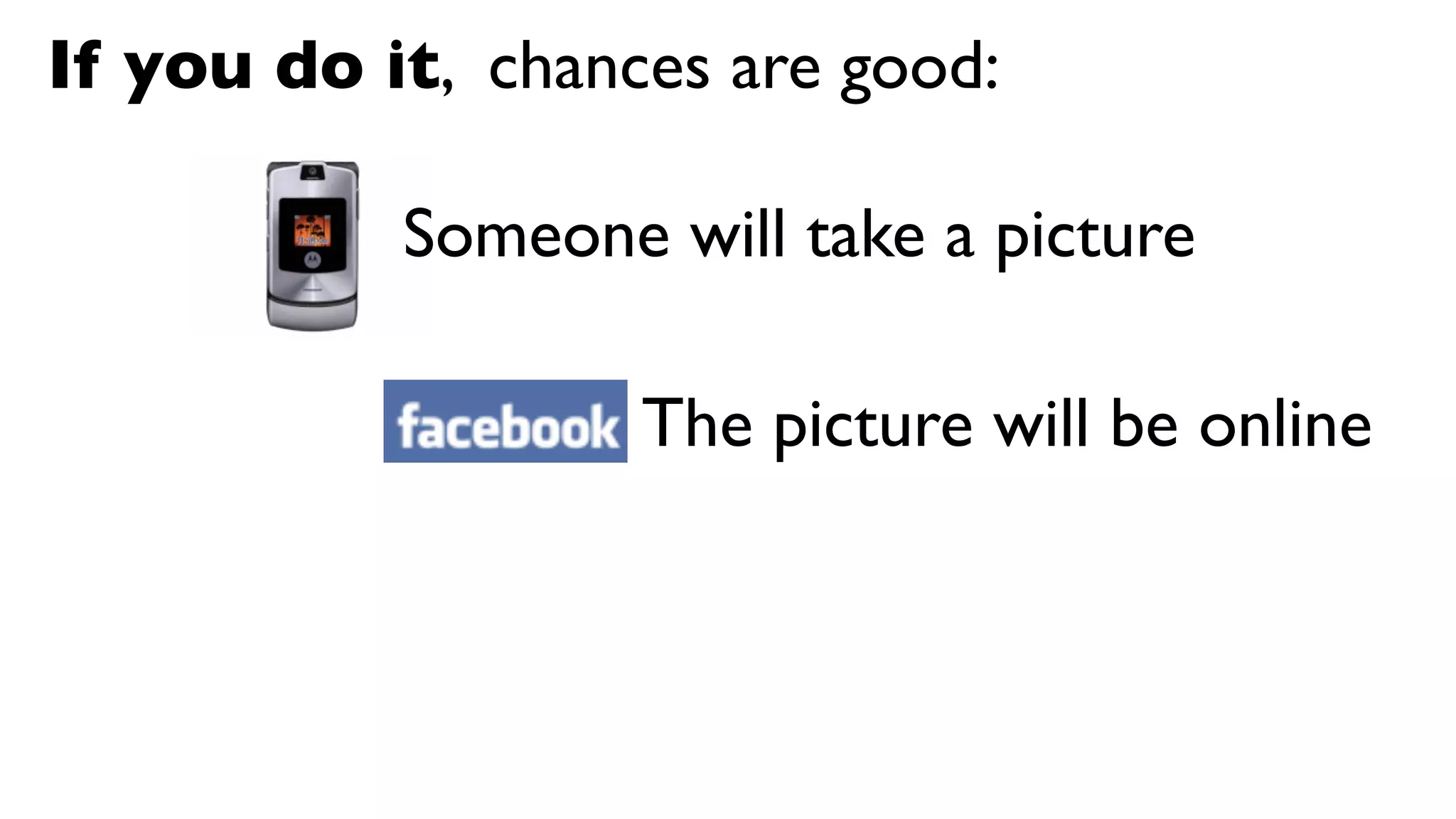
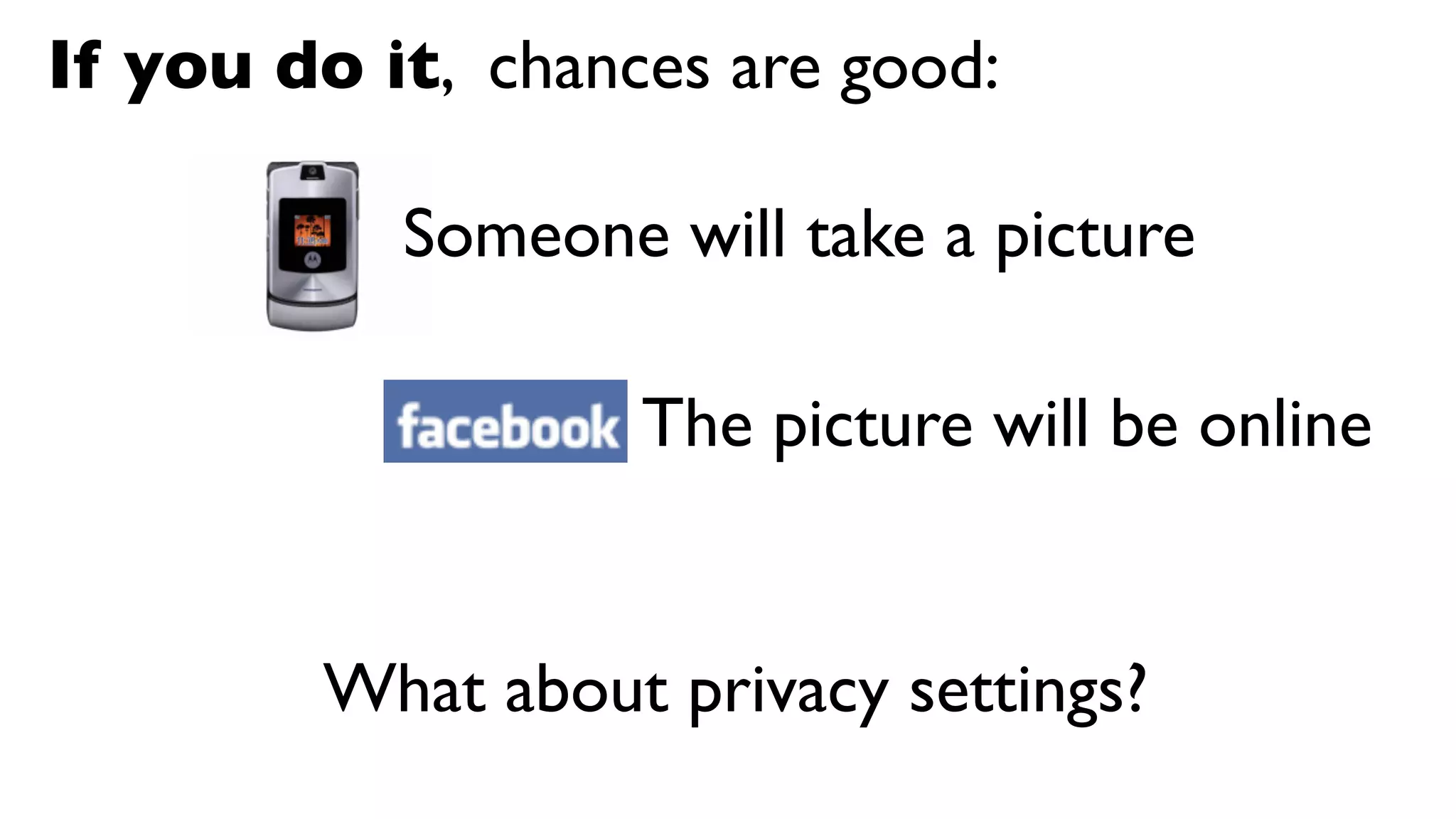
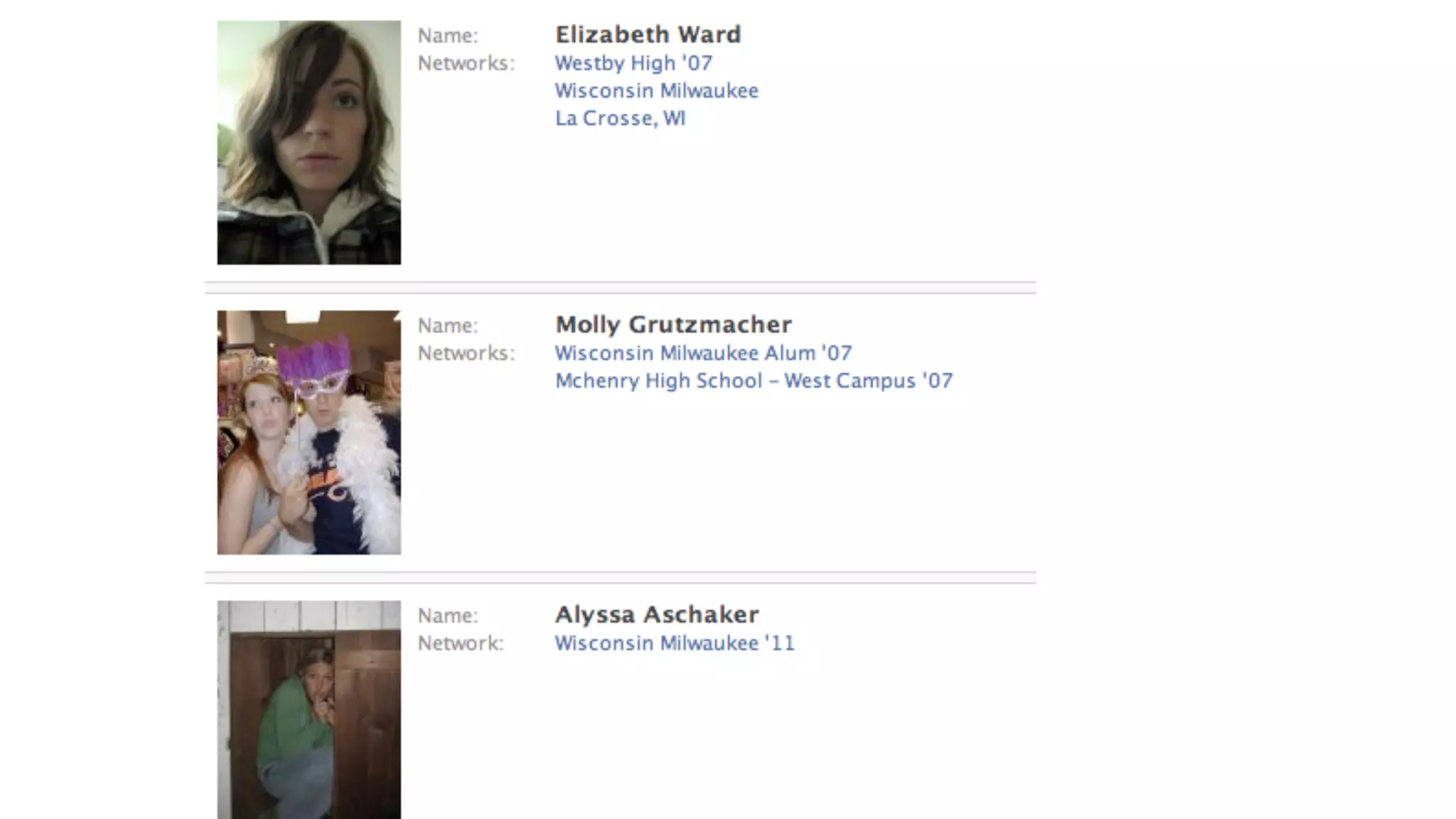
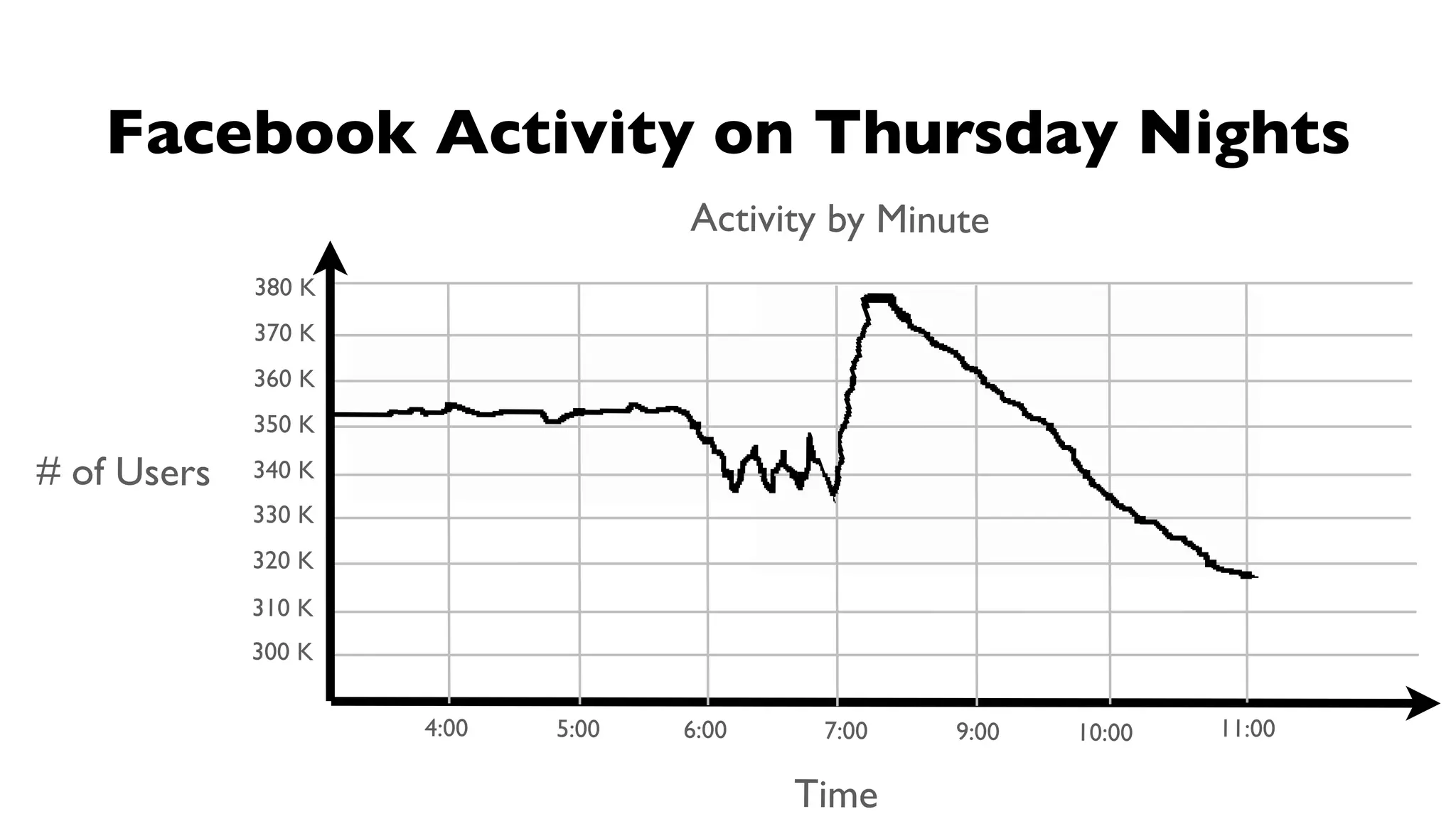
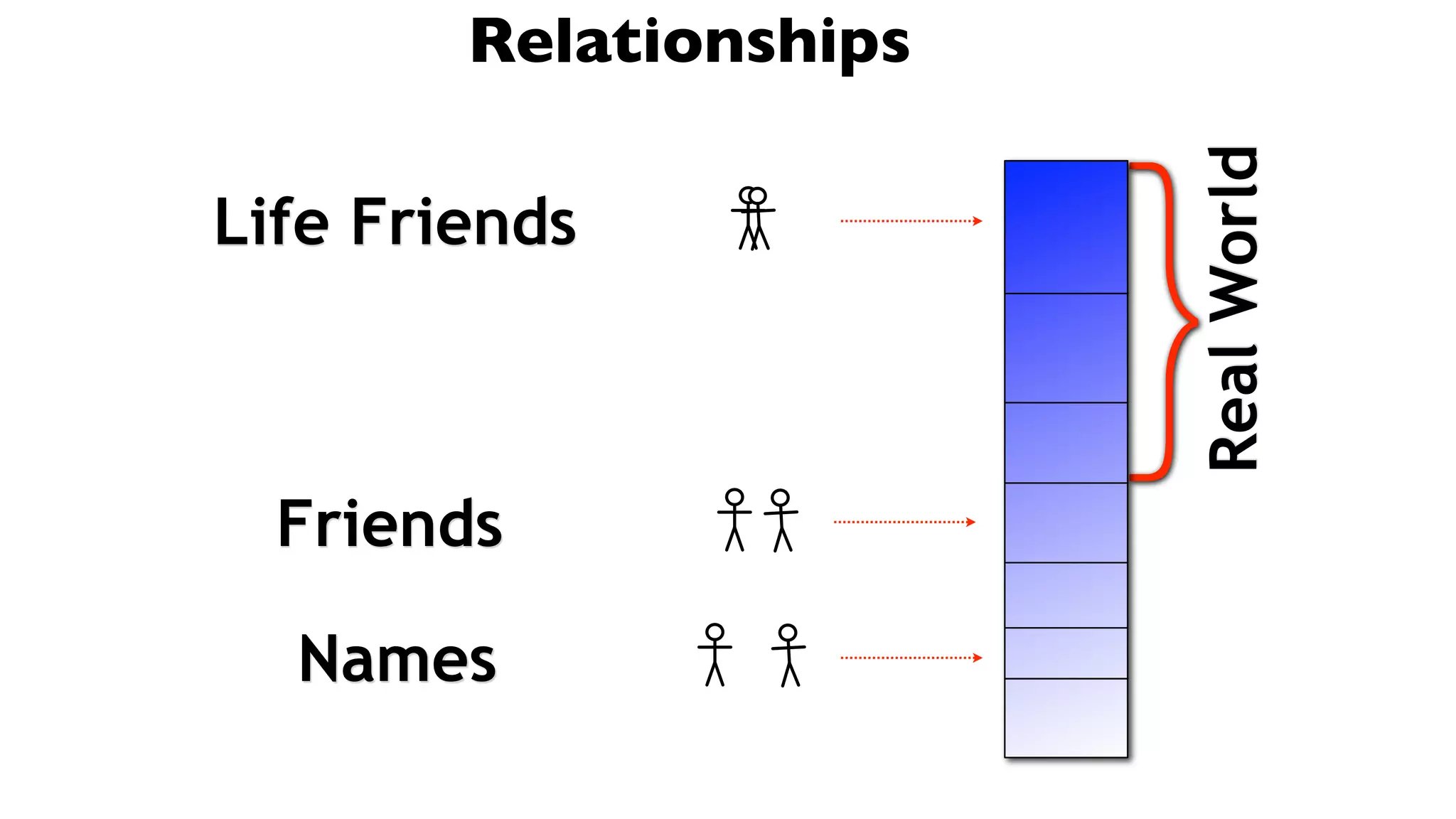
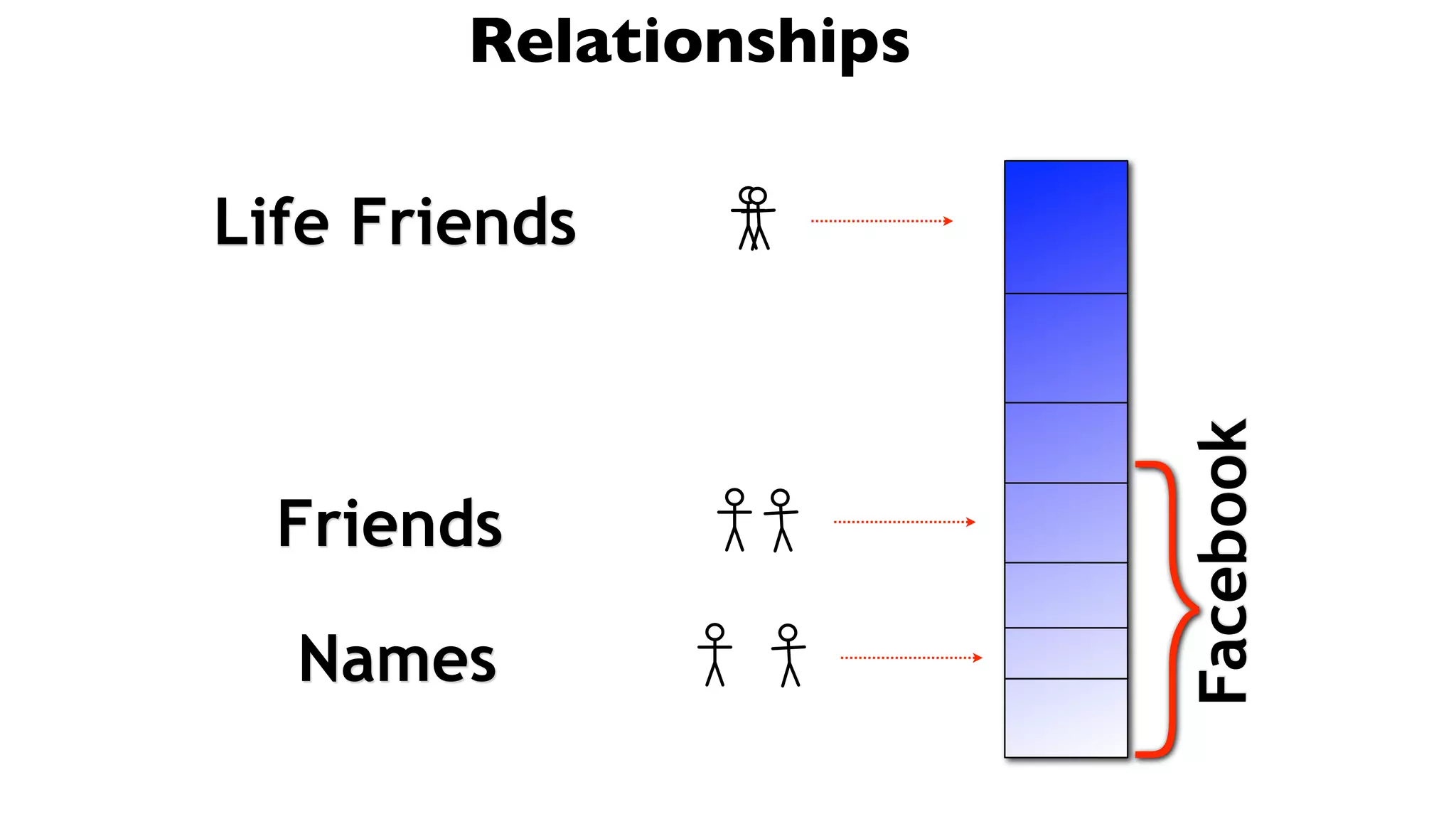
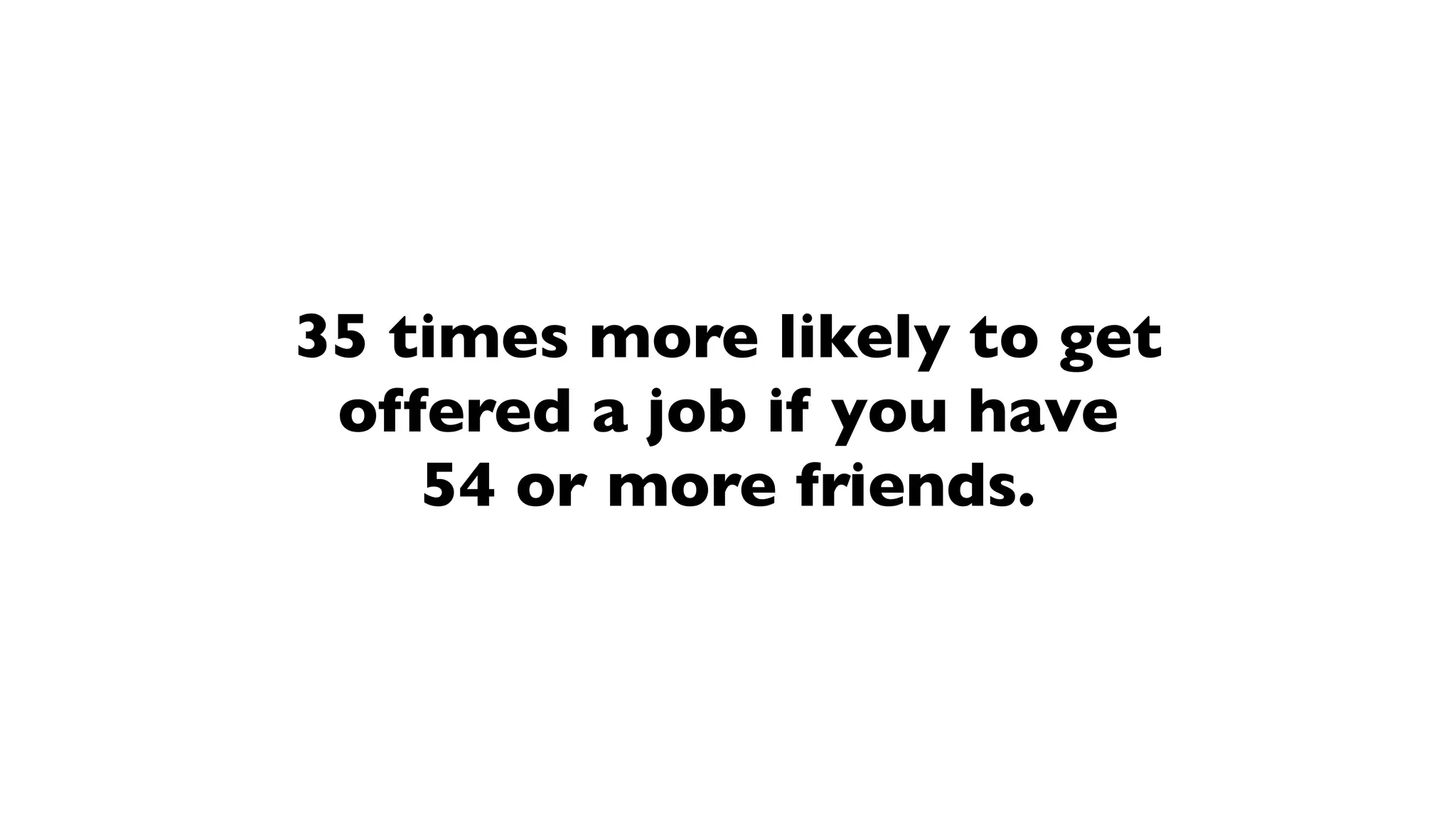
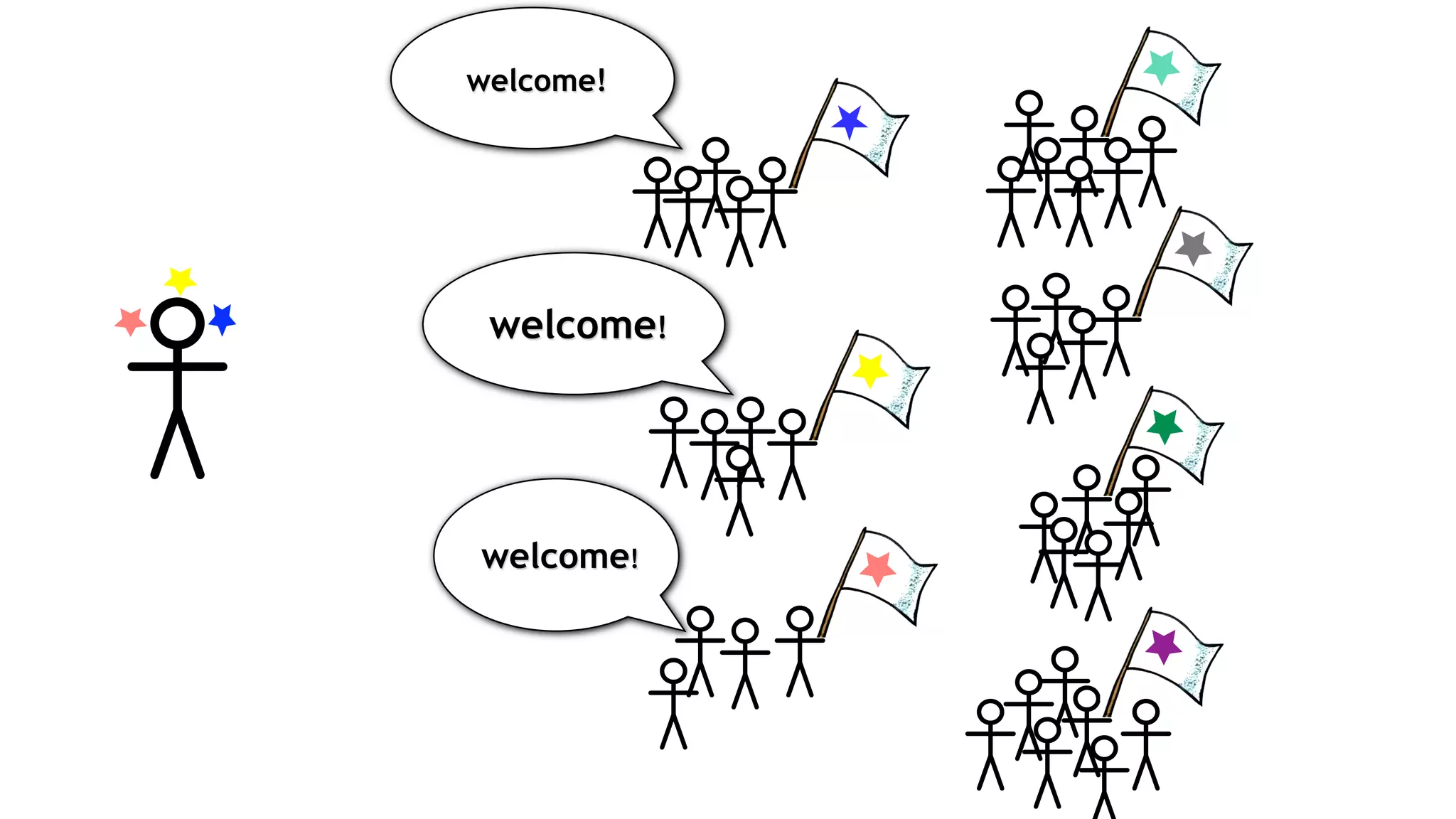
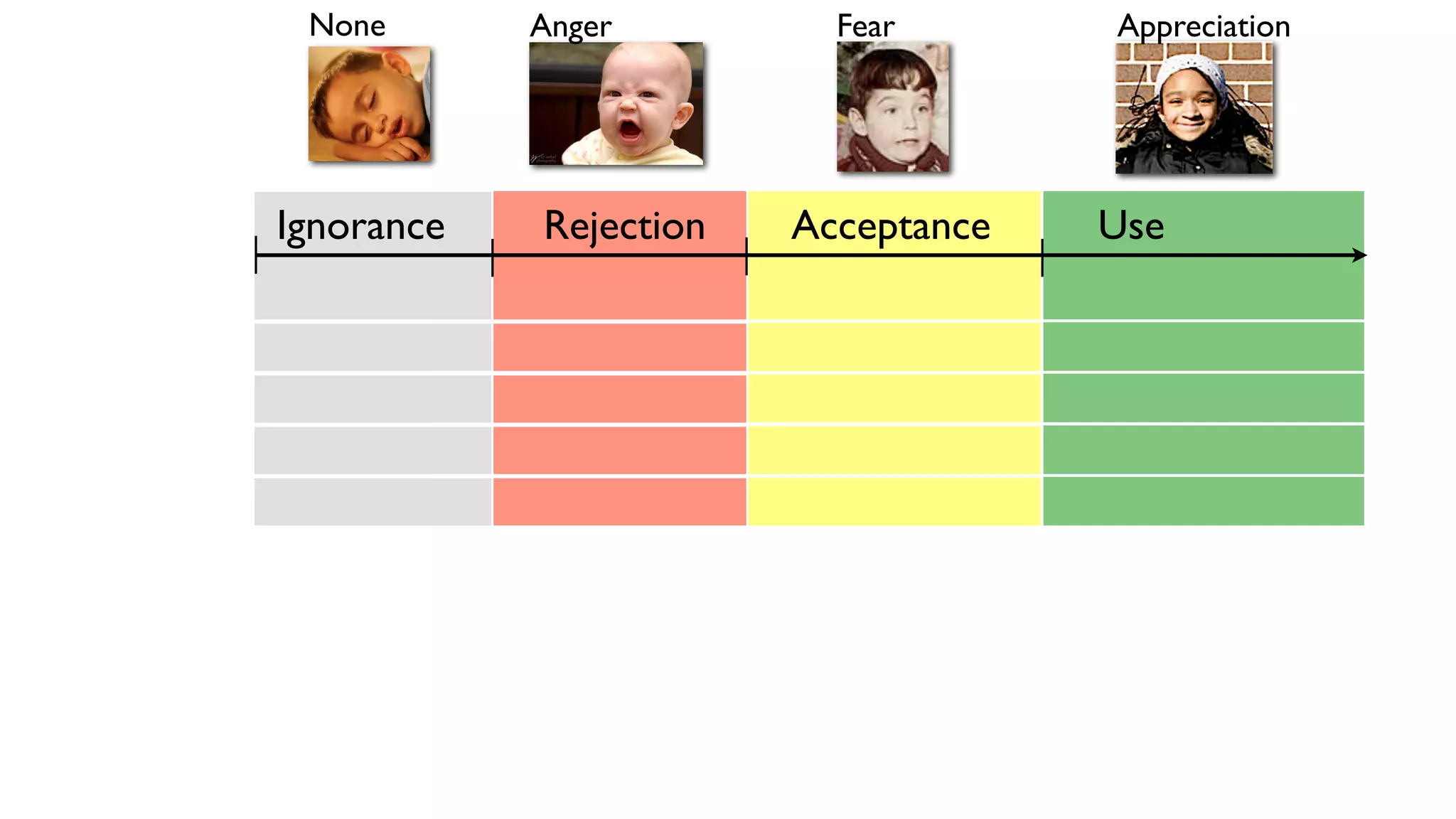
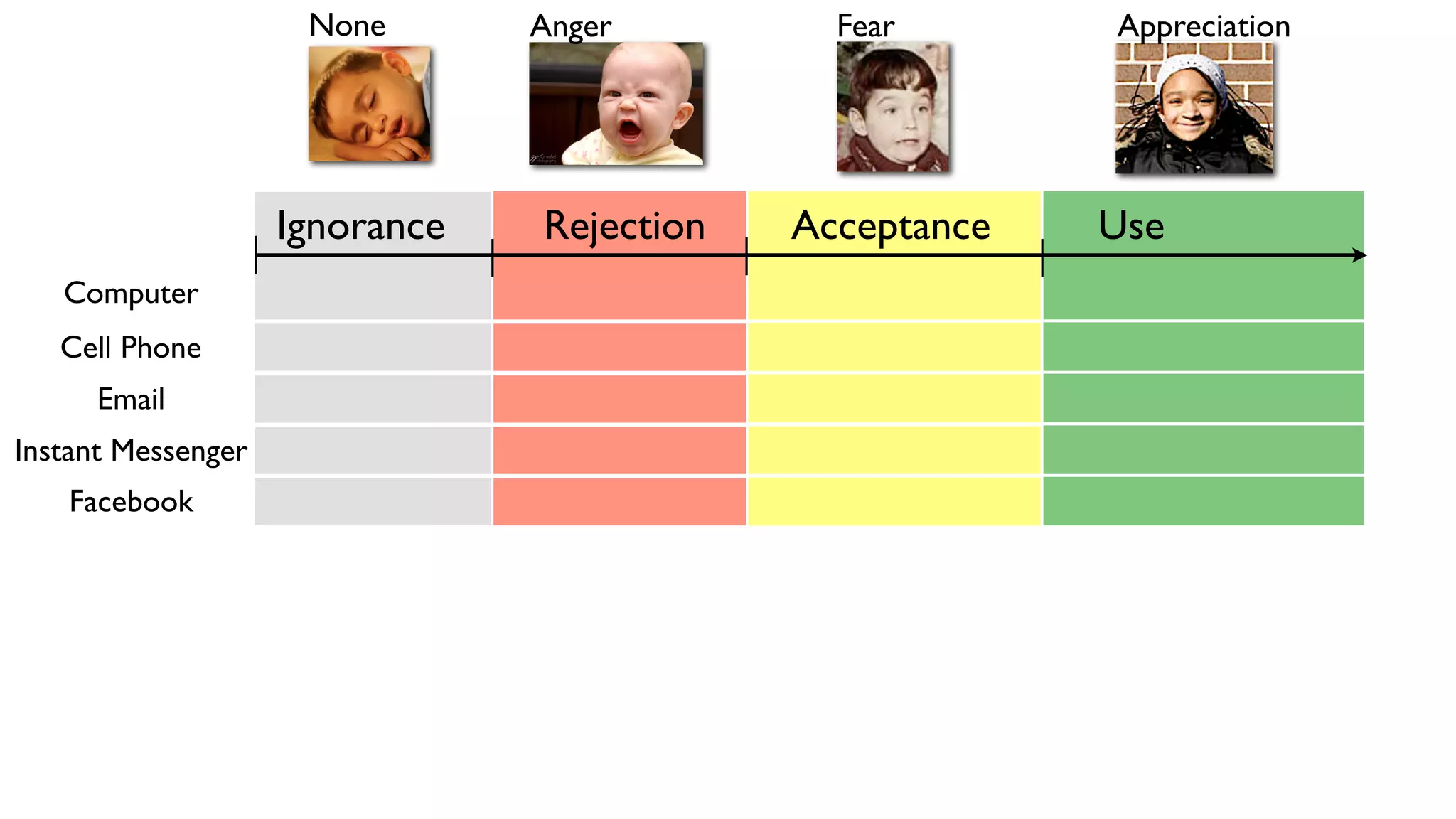
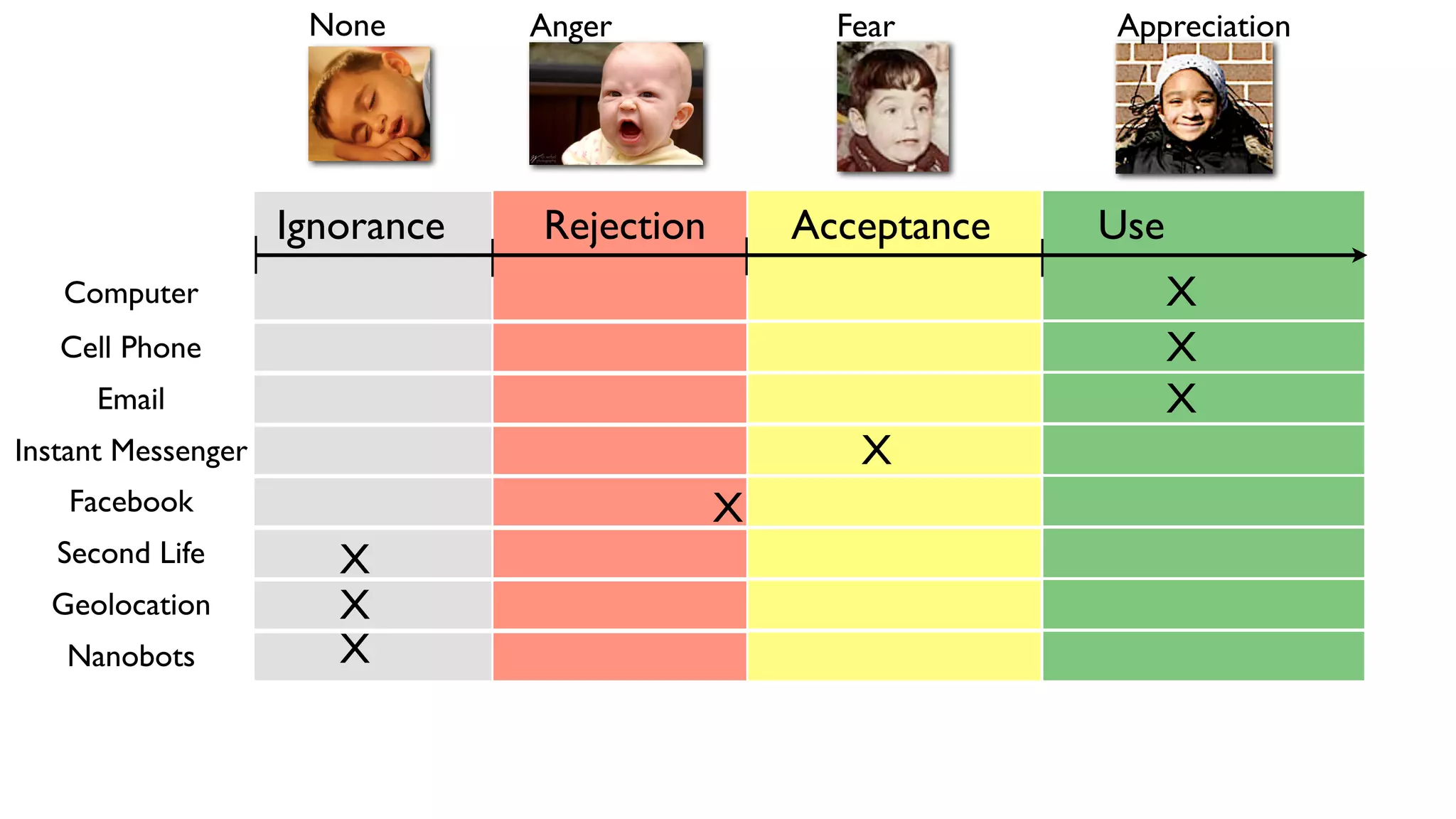
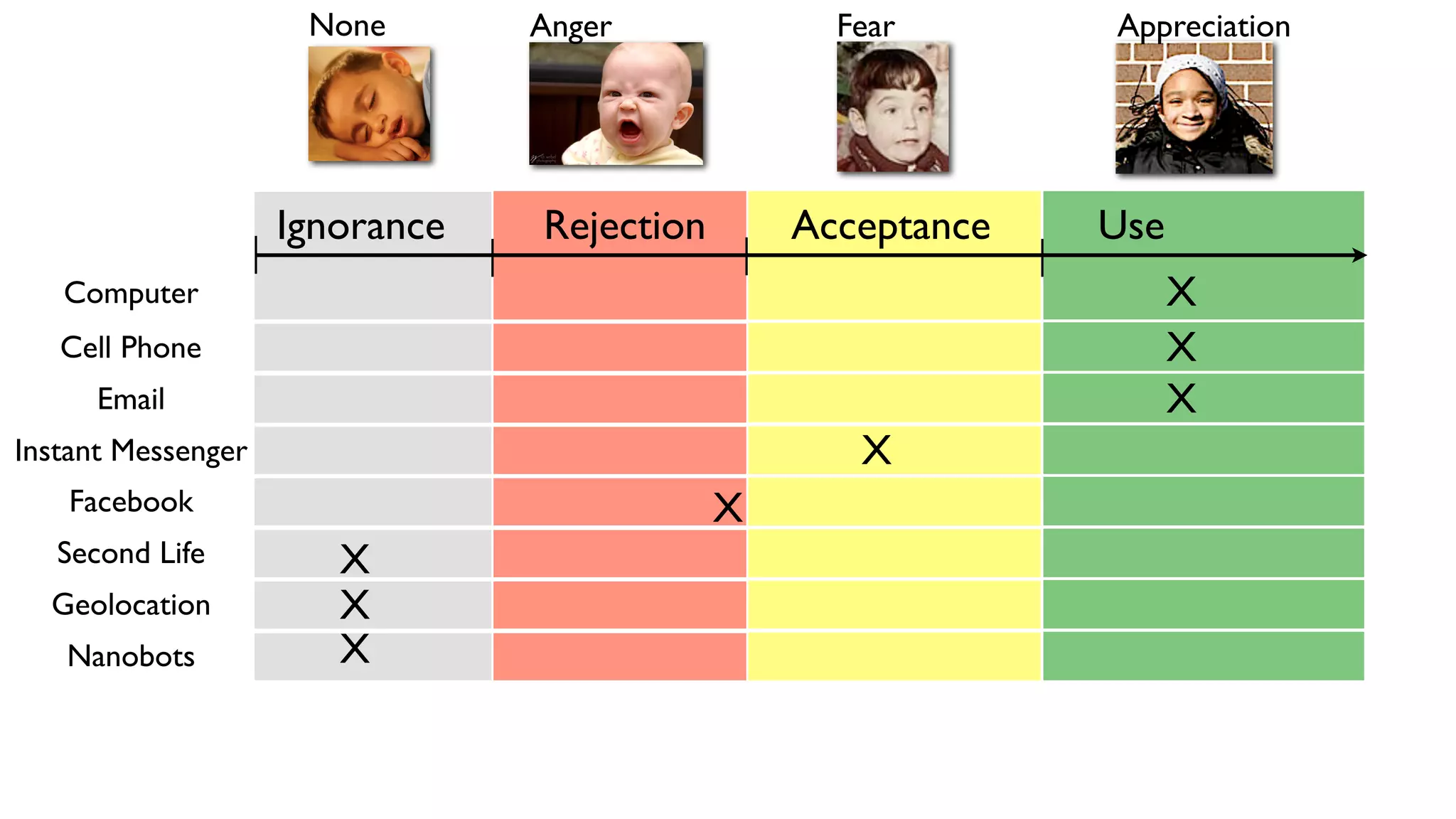
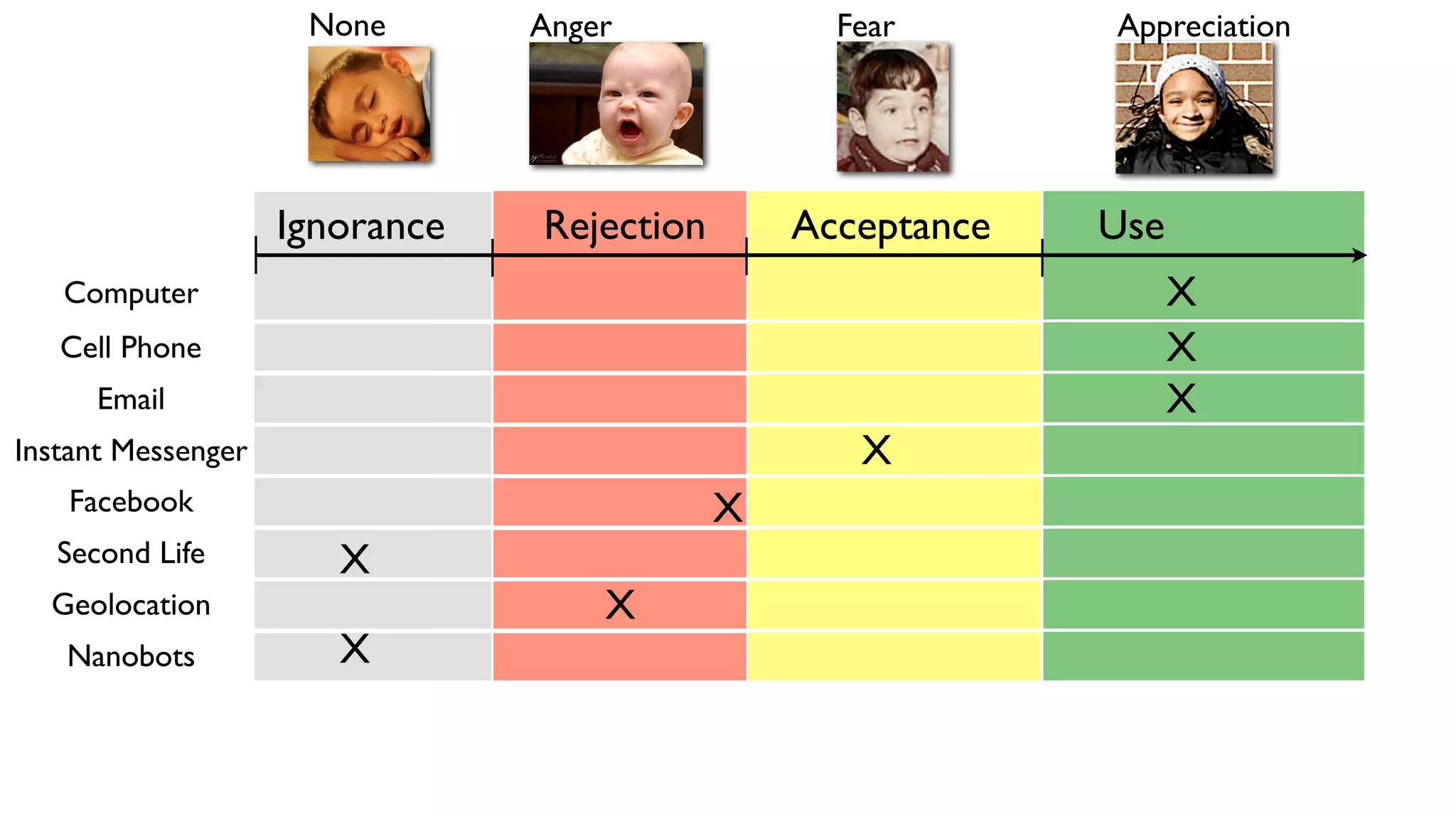
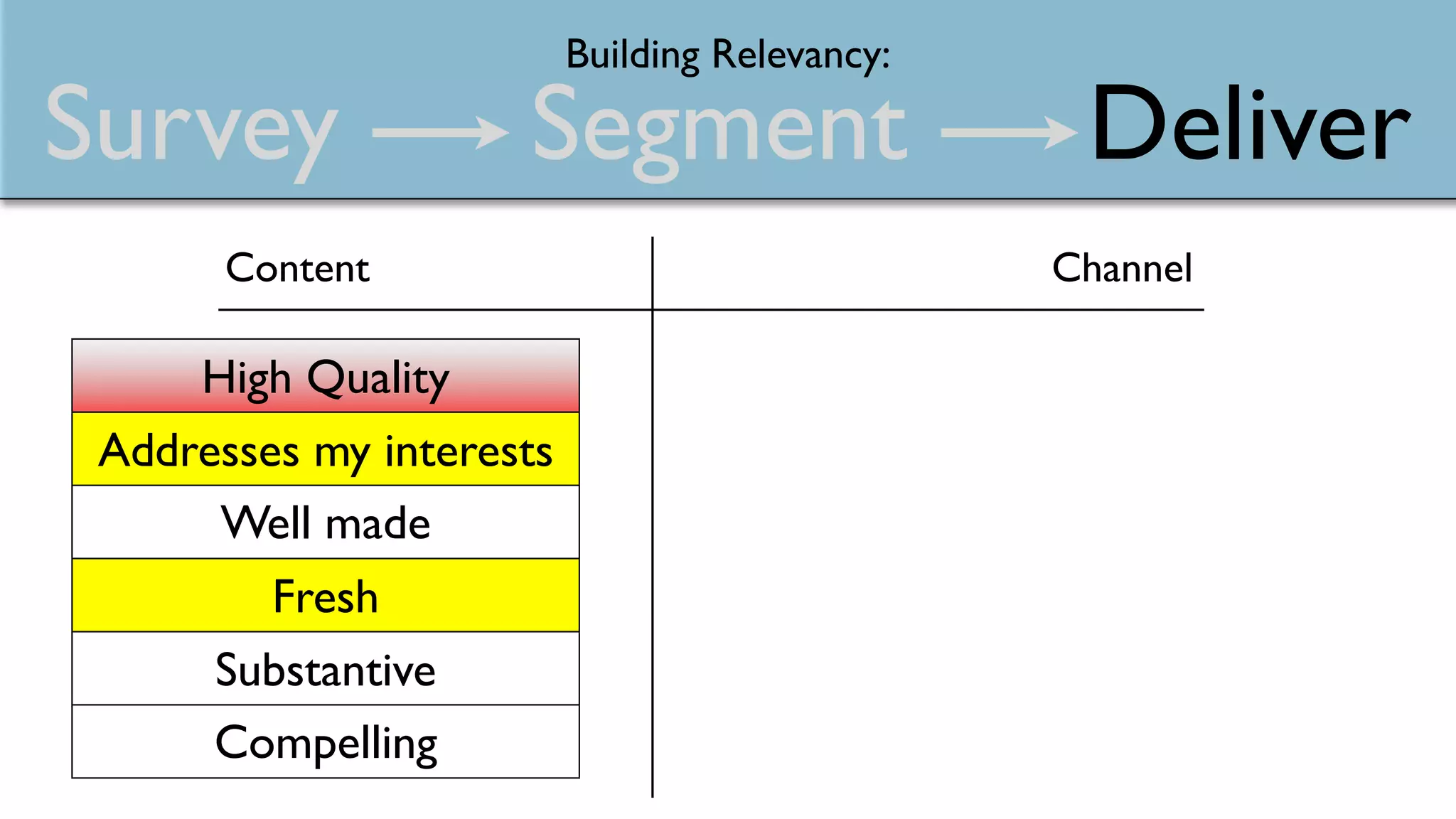
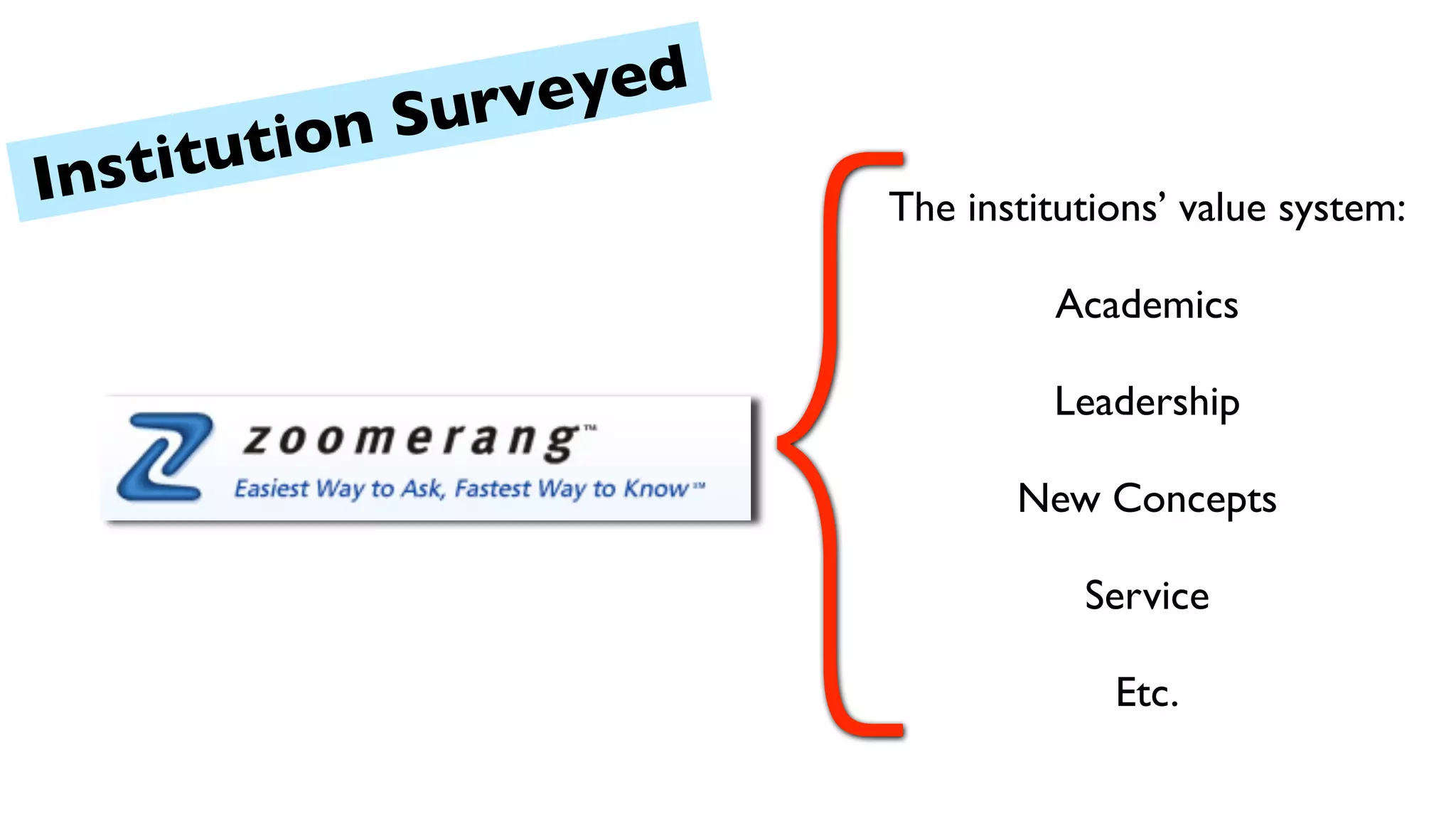
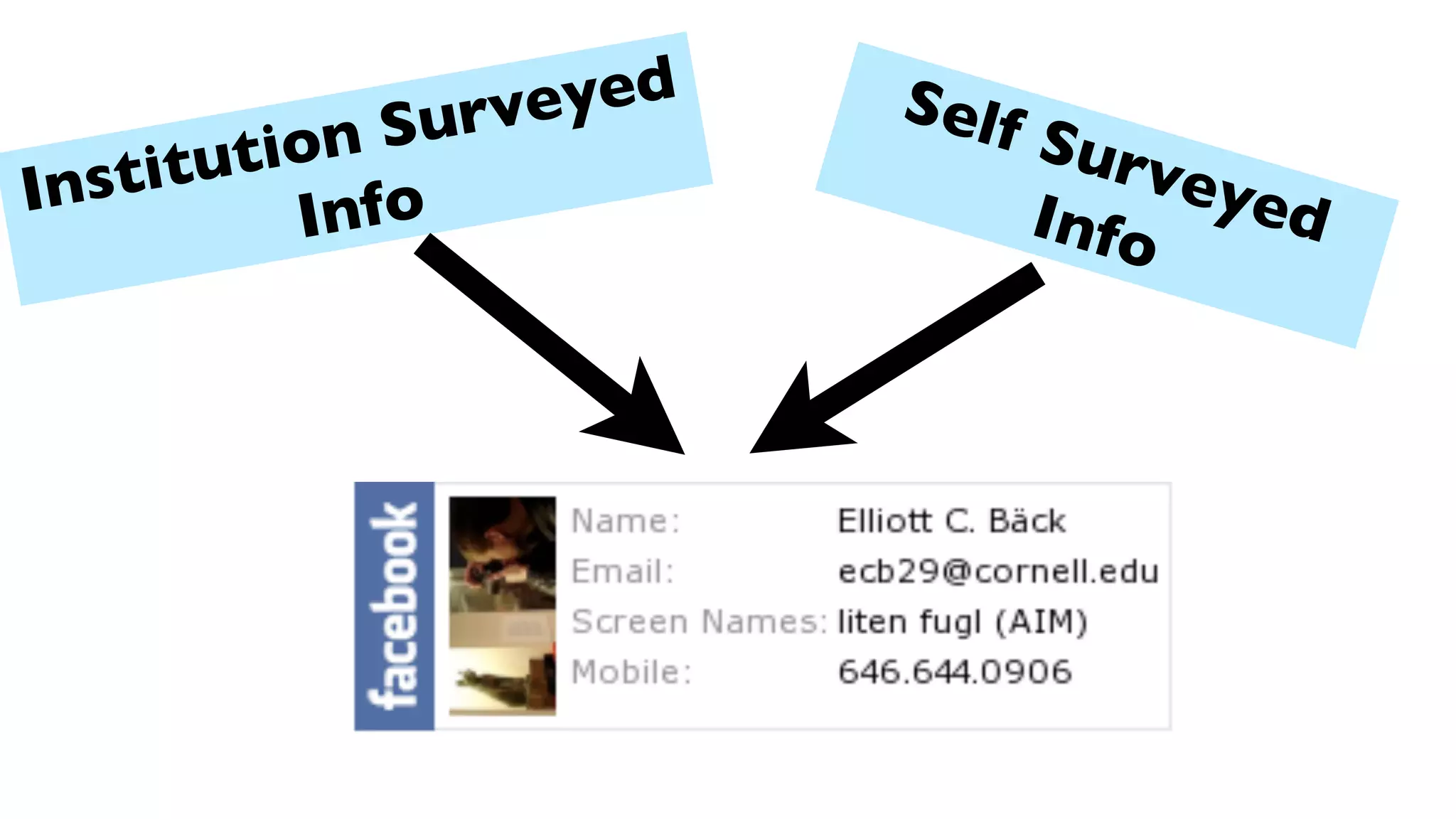
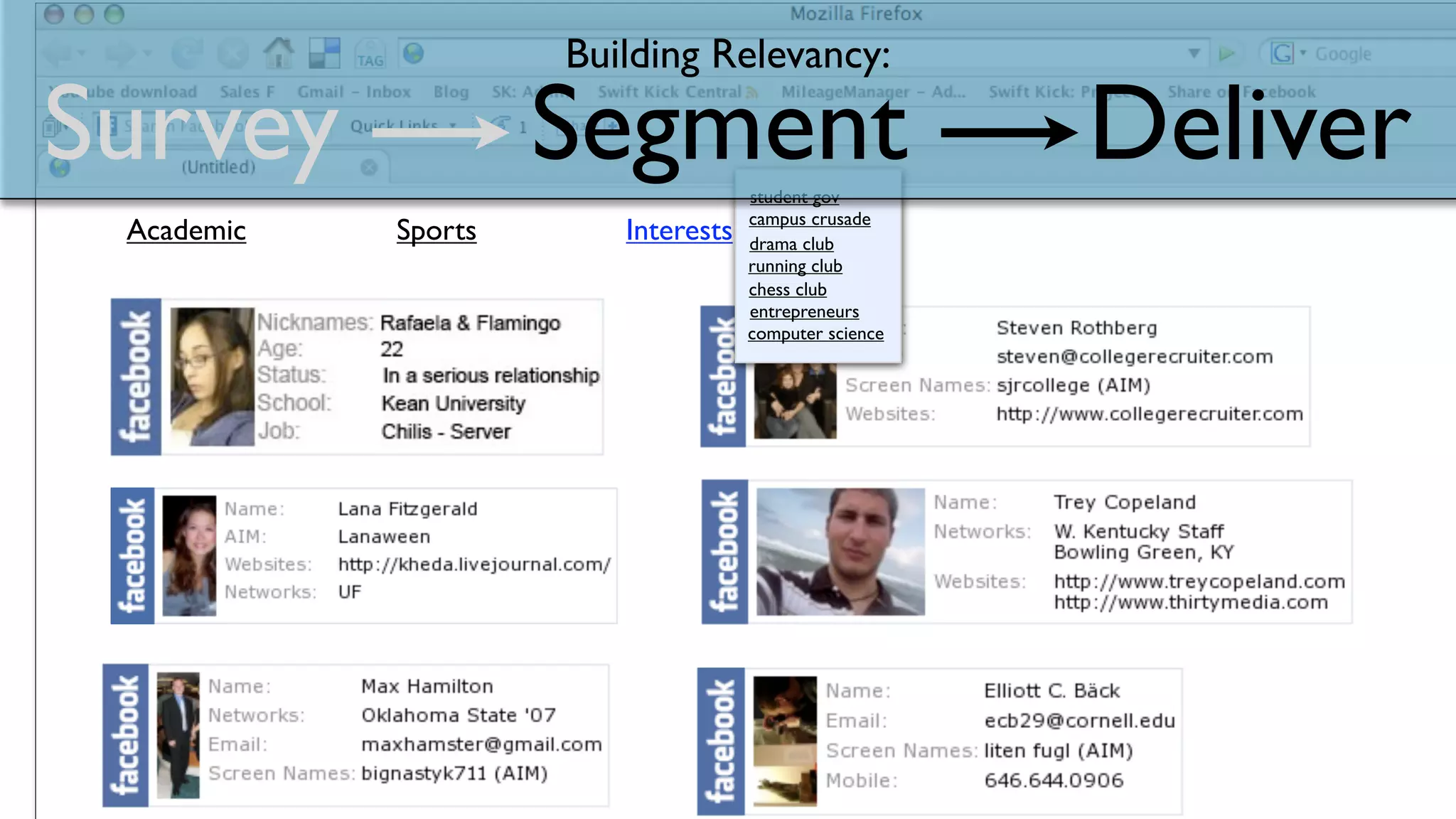
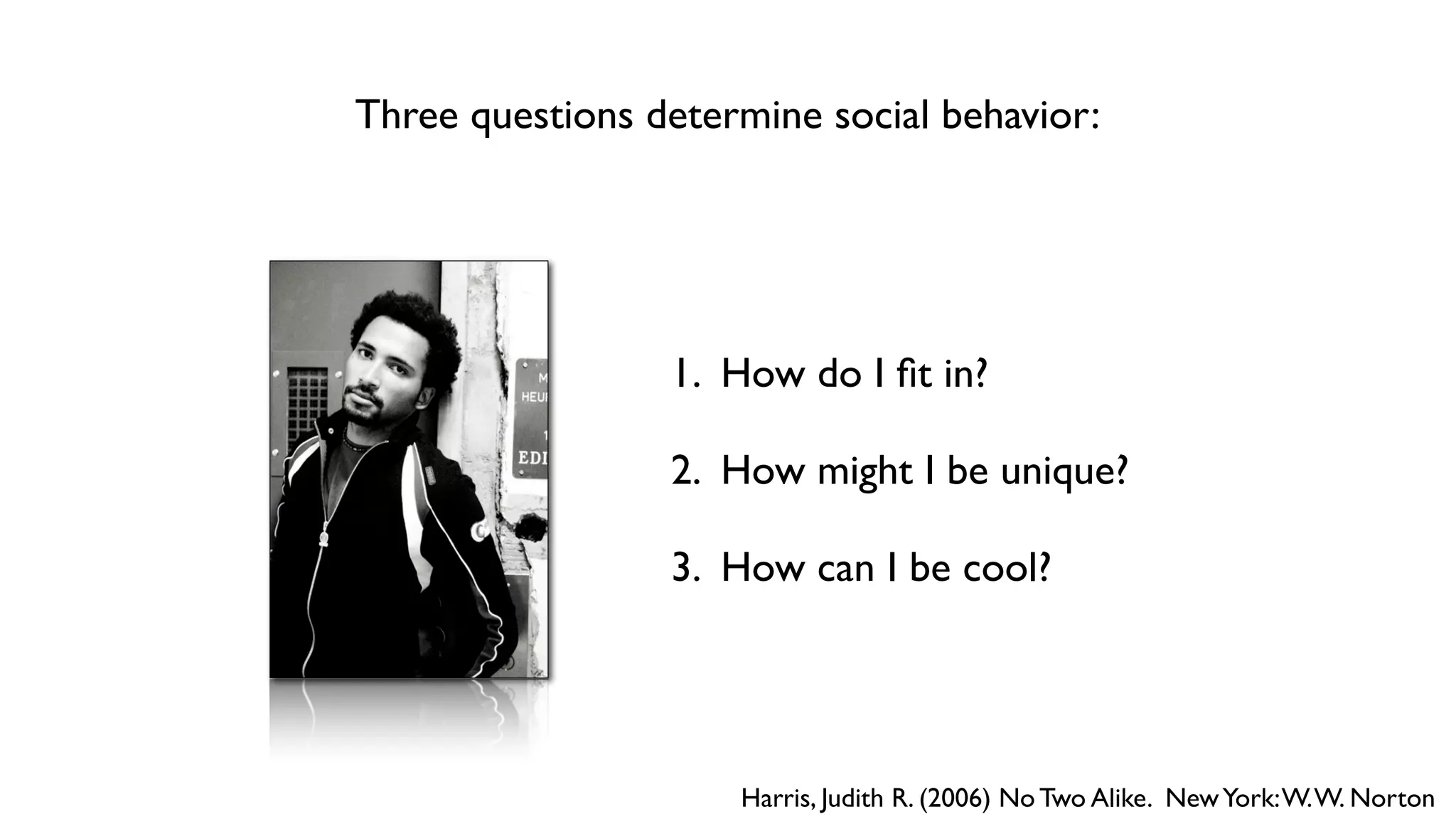
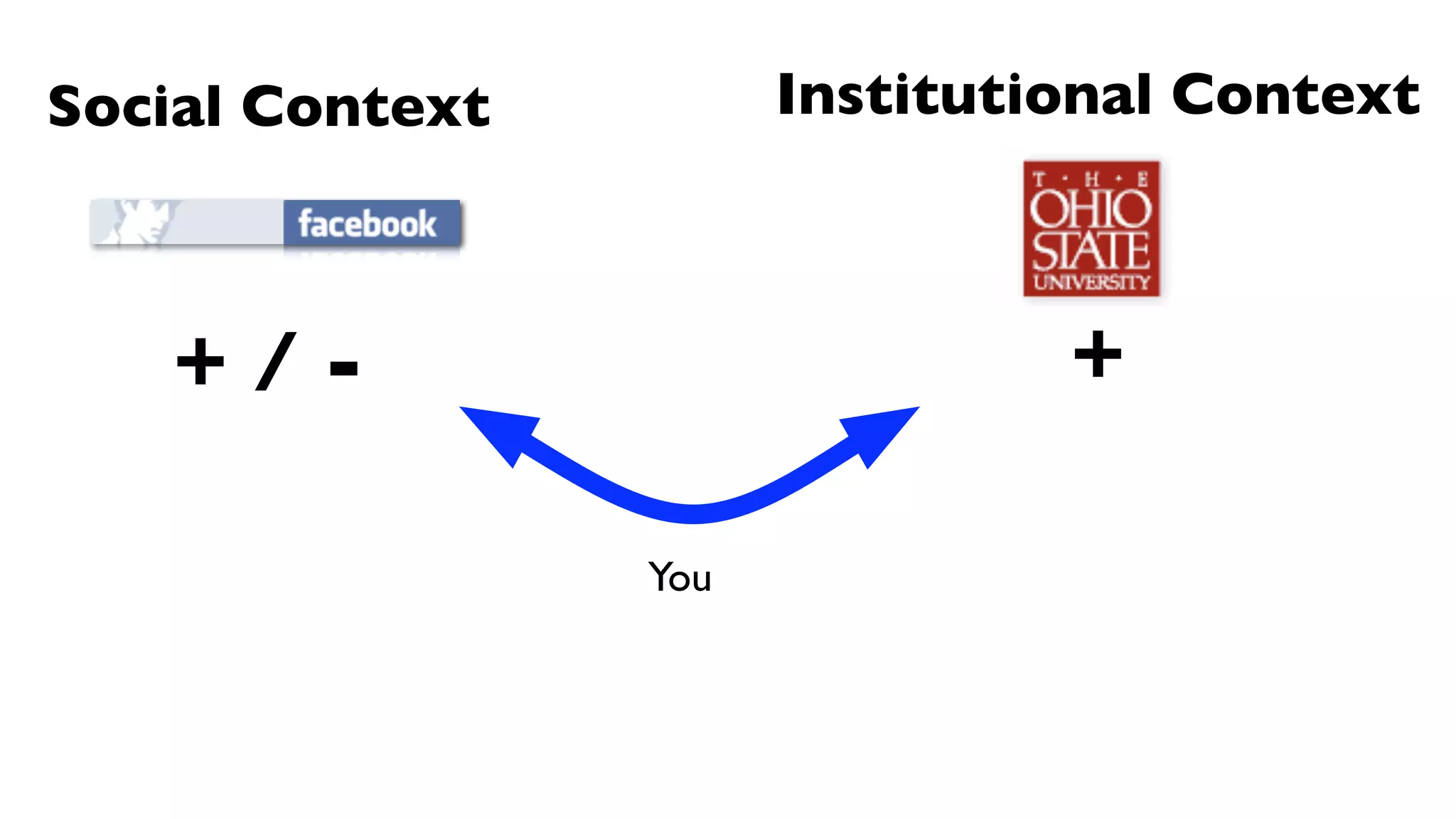
The document discusses the role of technology, particularly social media platforms like Facebook and MySpace, in the context of higher education, focusing on the importance of student identity development and connections. It notes that college students are increasingly using these platforms for communication and social engagement, highlighting both opportunities and challenges regarding privacy and social behavior. Additionally, it emphasizes that student orientation plays a critical role in facilitating these connections and developing student profiles.