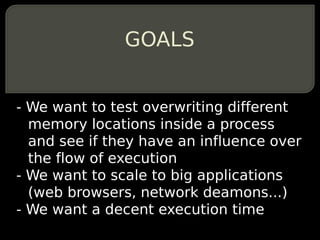
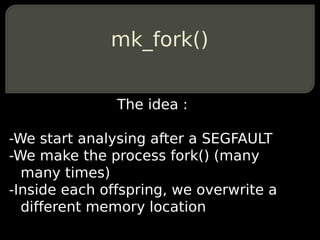
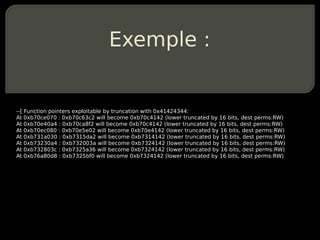
The document introduces PMCMA, a debugger tool that analyzes memory corruption bugs by forcing processes to fork, overwriting memory locations in the offspring processes, and monitoring execution to map exploitable scenarios. PMCMA aims to provide a roadmap for exploitation by identifying vulnerabilities and possible exploitation techniques like truncating function pointers or exploiting 4-byte aligned memory writes. The tool is available online and has received over 10,000 downloads in its first two months.
![Invalid memory reads (1/2)
Eg :
CVE-2011-0761 (Perl)
cmp BYTE PTR [ebx+0x8],0x9](https://image.slidesharecdn.com/ruxcon-111127233040-phpapp02/85/Ruxcon-2011-Post-Memory-Corruption-Memory-Analysis-21-320.jpg)
![Invalid memory reads (2/2)
Eg :
CVE-2011-0764 (t1lib)
fld QWORD PTR [eax+0x8]](https://image.slidesharecdn.com/ruxcon-111127233040-phpapp02/85/Ruxcon-2011-Post-Memory-Corruption-Memory-Analysis-22-320.jpg)
![Invalid memory writes
Eg :
CVE-2011-1824 (Opera)
mov DWORD PTR [ebx+edx*1],eax](https://image.slidesharecdn.com/ruxcon-111127233040-phpapp02/85/Ruxcon-2011-Post-Memory-Corruption-Memory-Analysis-24-320.jpg)


![Means of modifying the
flow of execution without
function pointers
Call tables.
Calling [Offset+register]
=> This is also already performed
automatically using pmcma.](https://image.slidesharecdn.com/ruxcon-111127233040-phpapp02/85/Ruxcon-2011-Post-Memory-Corruption-Memory-Analysis-75-320.jpg)