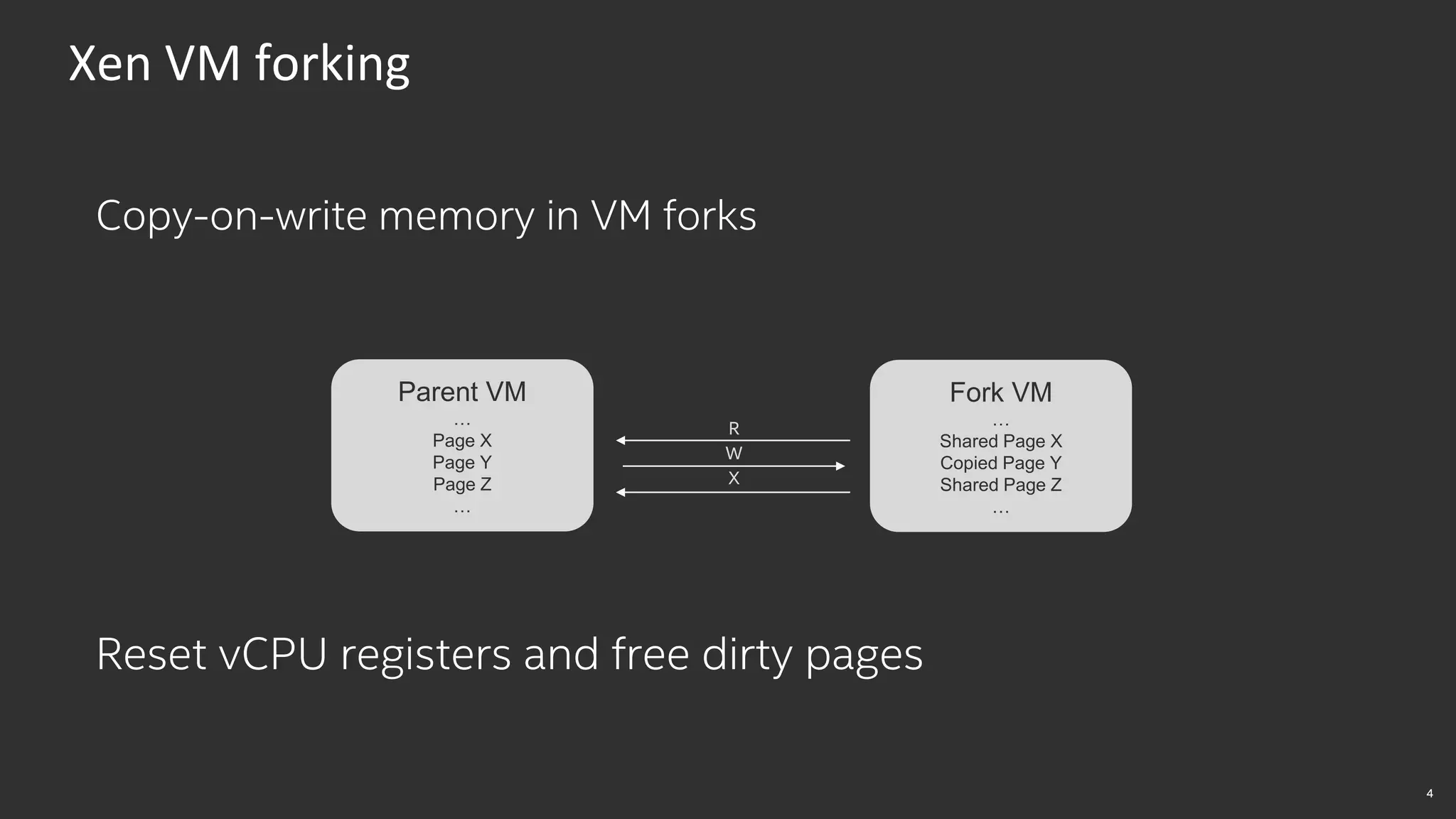
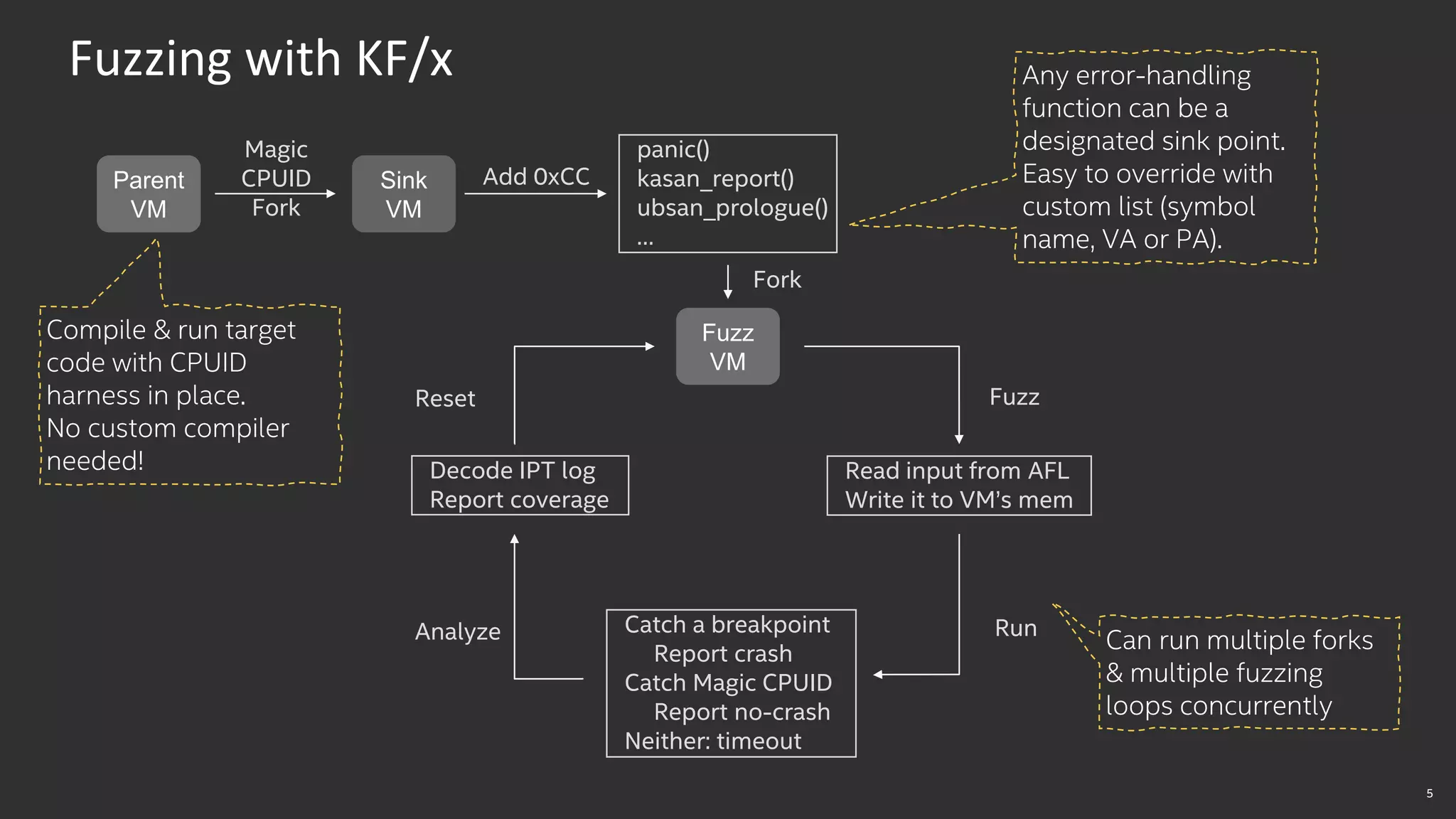
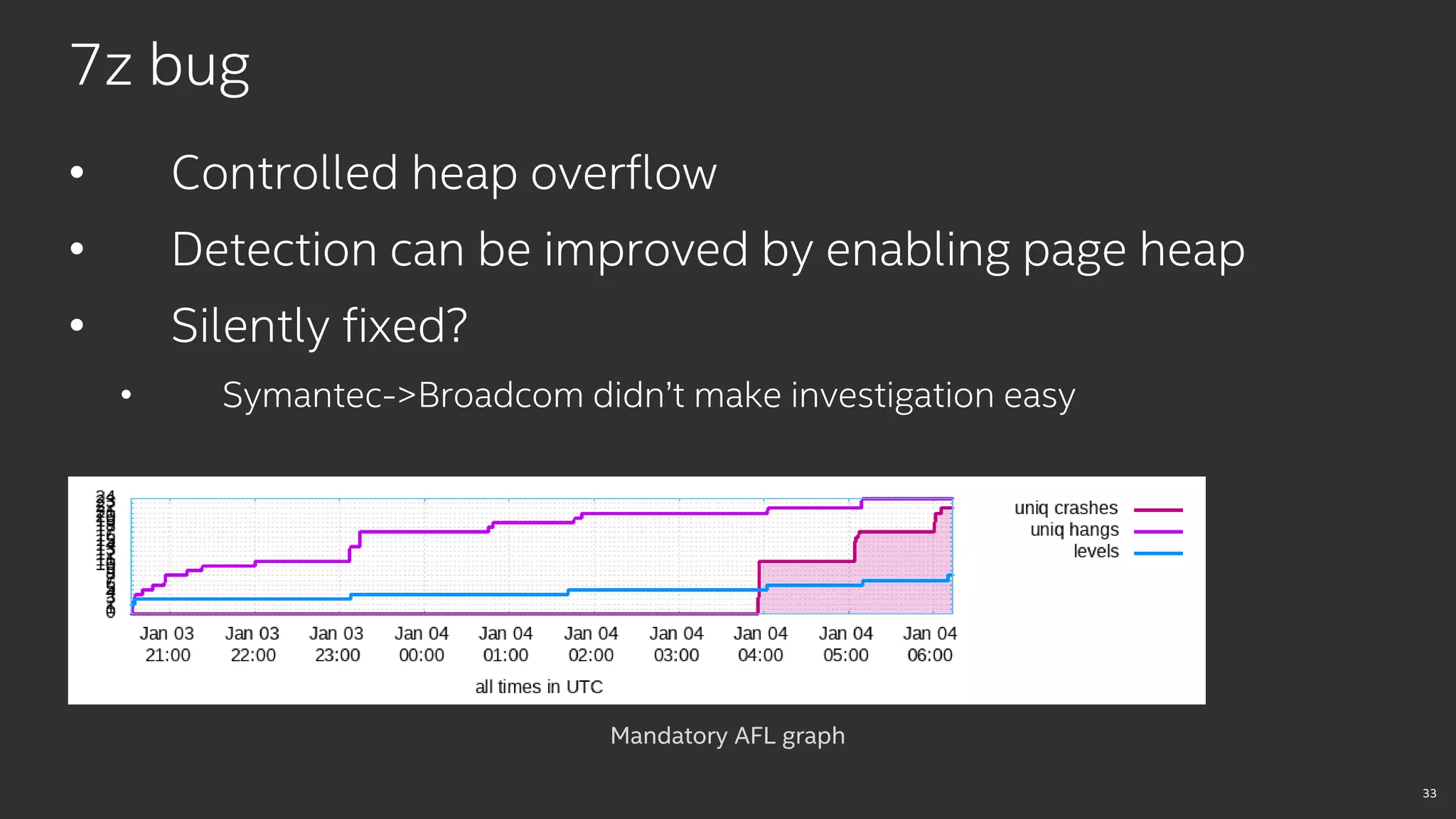
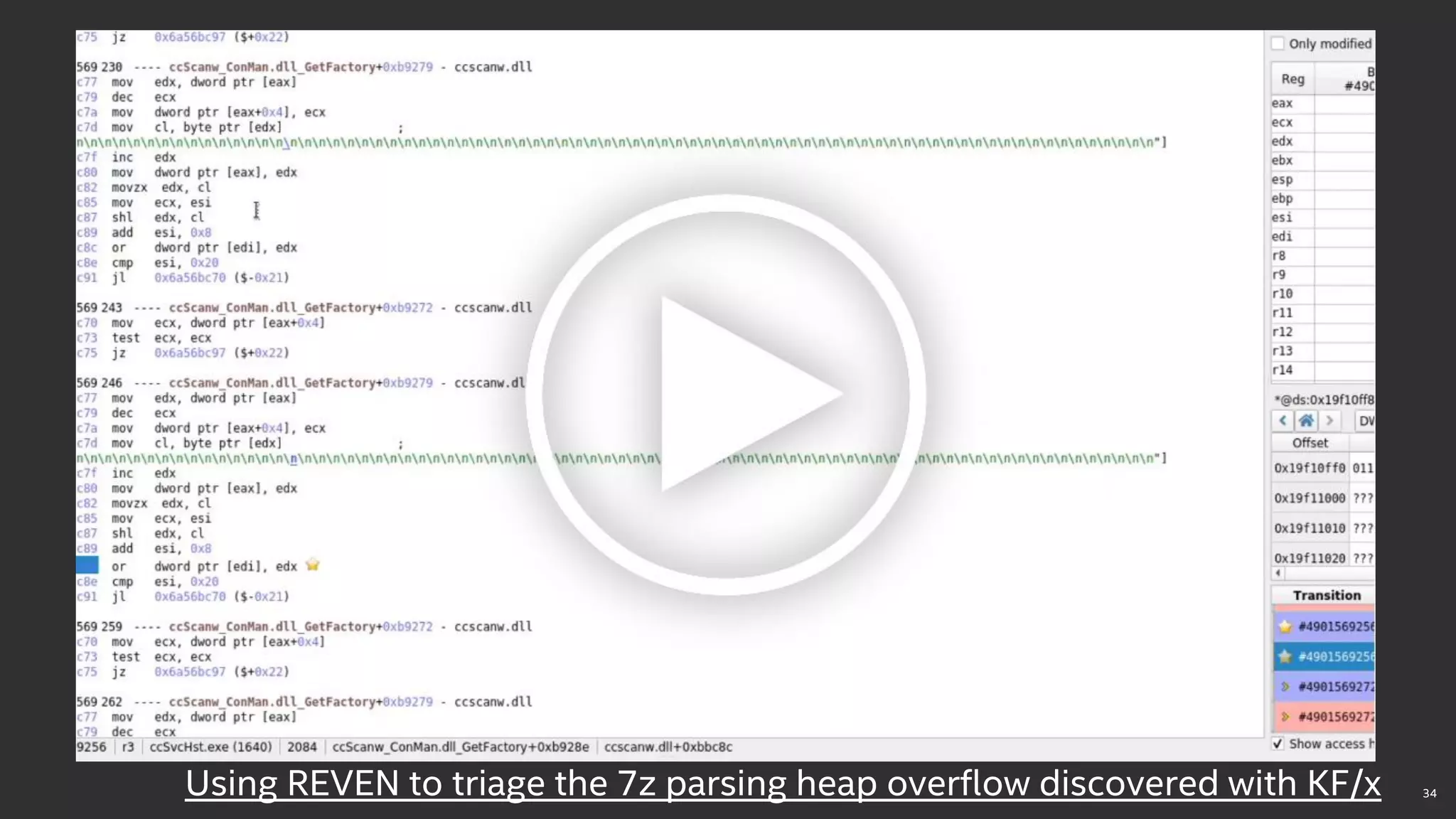
KF/x is an open-source fuzzing framework that leverages virtual machine introspection to fuzz code running inside virtual machines. It was used to discover vulnerabilities in the Virtio driver in Linux and a heap overflow in the 7z parser of Symantec Endpoint Protection. KF/x allows taking full memory snapshots of a VM, forking it to generate new test cases, and monitoring for crashes or desired program states. This approach found issues that may have otherwise remained undetected due to the lack of proper fuzzing tools for systems running complex, isolated software like antivirus programs.