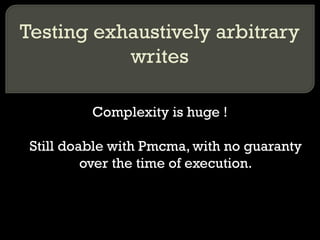
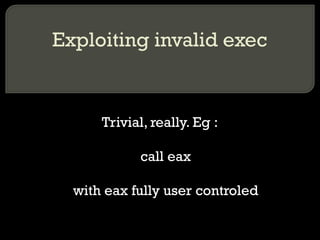
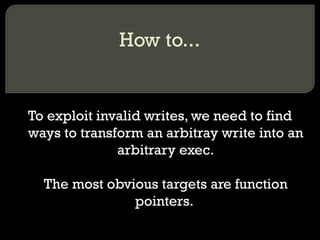
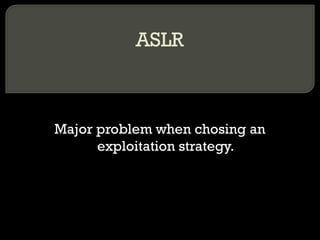
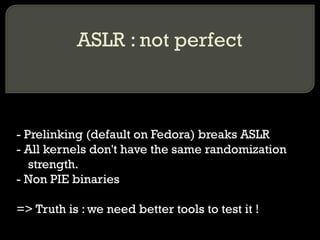
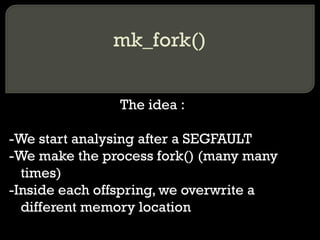
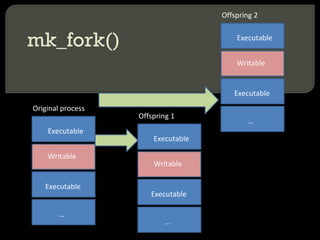
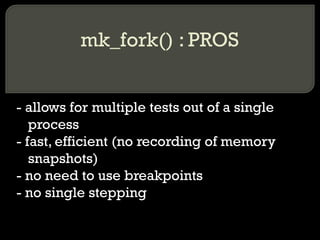
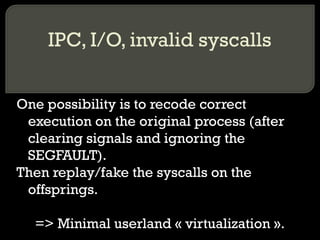
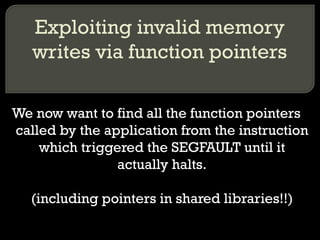
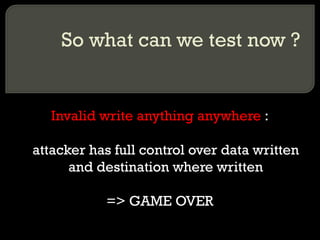
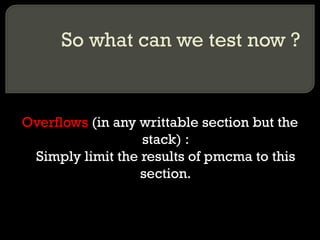
The document summarizes the Post Memory Corruption Memory Analysis (PMCMA) tool. PMCMA allows finding and testing exploitation scenarios resulting from invalid memory accesses. It provides a roadmap to exploitation without generating exploit code. The tool analyzes programs after crashes to overwrite memory locations in forked processes and test impact on execution flow.
![Invalid memory reads (1/2) Eg : CVE-2011-0761 (Perl) cmp BYTE PTR [ ebx+0x8 ] ,0x9](https://image.slidesharecdn.com/28c3-120107122834-phpapp02/85/CCC-28c3-Post-Memory-Corruption-Memory-Analysis-23-320.jpg)
![Invalid memory reads (2/2) Eg : CVE-2011-0764 (t1lib) fld QWORD PTR [eax+0x8]](https://image.slidesharecdn.com/28c3-120107122834-phpapp02/85/CCC-28c3-Post-Memory-Corruption-Memory-Analysis-24-320.jpg)
![Invalid memory writes Eg : CVE-2011-1824 (Opera) mov DWORD PTR [ ebx+edx*1 ] ,eax](https://image.slidesharecdn.com/28c3-120107122834-phpapp02/85/CCC-28c3-Post-Memory-Corruption-Memory-Analysis-26-320.jpg)




![Means of modifying the flow of execution without function pointers Call tables. Calling [Offset+register] => This is also already performed automatically using pmcma.](https://image.slidesharecdn.com/28c3-120107122834-phpapp02/85/CCC-28c3-Post-Memory-Corruption-Memory-Analysis-77-320.jpg)