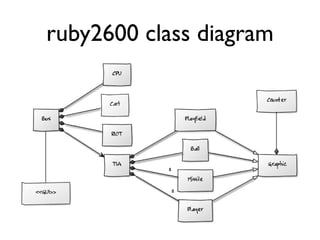
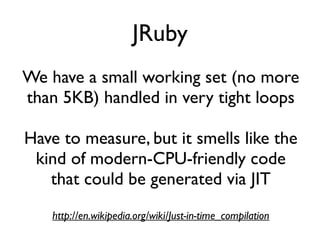
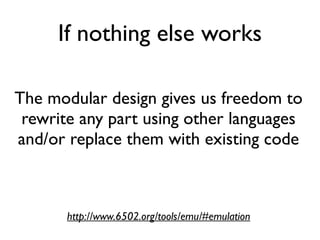
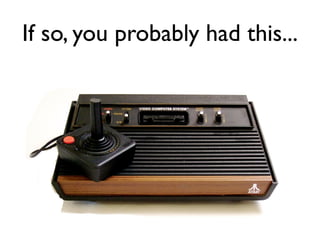
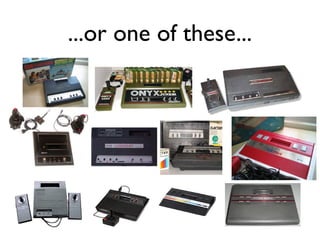
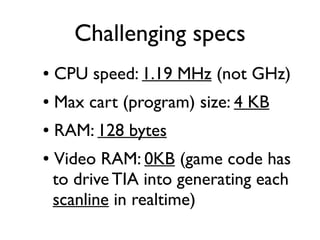
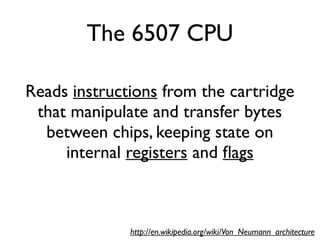
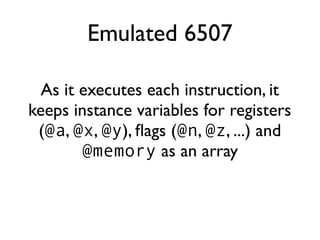
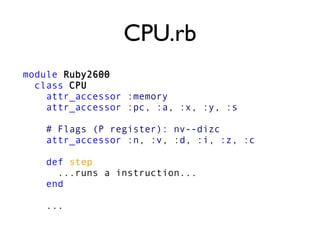
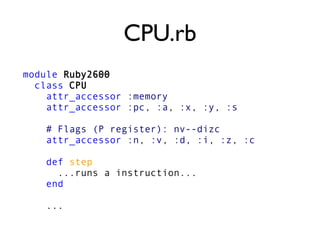
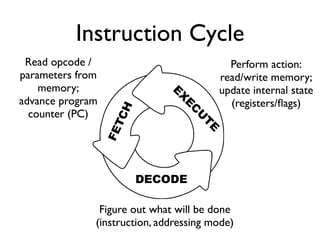
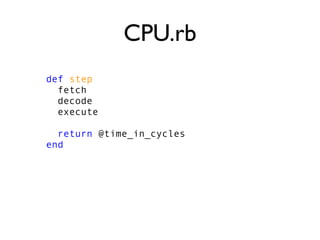
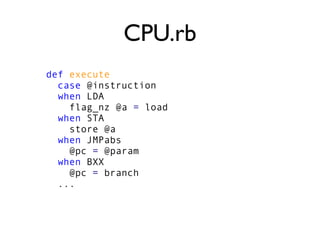
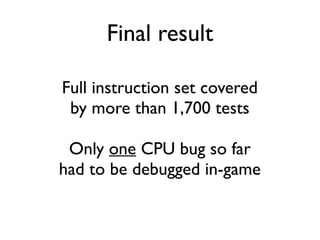
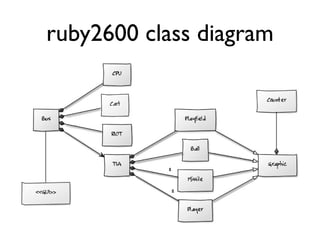
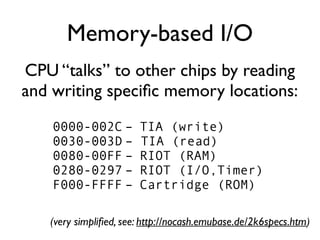
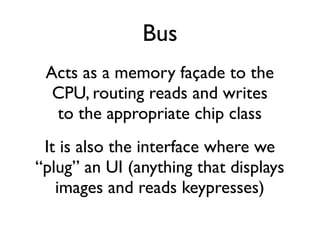
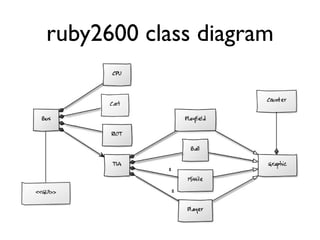
An emulator of the Atari 2600 game console was created entirely in Ruby using a test-driven approach. The emulator, called ruby2600, simulates the 6507 CPU, TIA graphics chip, and RIOT I/O chip in software through classes that represent each chip's functionality. Over 1,700 tests cover the CPU instruction set. The modular design allows each component to be developed and tested independently, and potential optimizations like JRuby were discussed to improve performance.






![CPU_spec.rb
context 'INX' do
before do
cpu.memory[0] = 0xE8 # INX
cpu.pc = 0x0000
cpu.x = 0x07
end
it 'should advance PC by one' do
cpu.step
cpu.pc.should == 0x0001
end
it 'should set X value' do
cpu.step
cpu.x.should == 0x08
end
...](https://image.slidesharecdn.com/ruby2600new-130828142032-phpapp01/85/ruby2600-an-Atari-2600-emulator-written-in-Ruby-31-320.jpg)
![“Literate Testing”
context 'INX' do
before do
cpu.memory[0] = 0xE8 # INX
cpu.x = 0x07
end
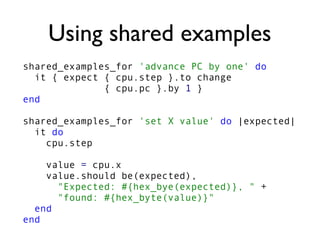
it_should 'advance PC by one'
it_should 'take two cycles'
it_should 'set X value', 0x08
it_should 'reset Z flag'
it_should 'reset N flag'
...
http://en.wikipedia.org/wiki/Literate_programming](https://image.slidesharecdn.com/ruby2600new-130828142032-phpapp01/85/ruby2600-an-Atari-2600-emulator-written-in-Ruby-34-320.jpg)
![No byte/word
data types :-(CPU.rb
def fetch
@opcode = memory[@pc]
@param_lo = memory[word(@pc + 1)]
@param_hi = memory[word(@pc + 2)]
@param = @param_hi * 0x100 + @param_lo
@pc = word(@pc +
OPCODE_SIZES[@opcode])
end
Lookup table](https://image.slidesharecdn.com/ruby2600new-130828142032-phpapp01/85/ruby2600-an-Atari-2600-emulator-written-in-Ruby-39-320.jpg)
![more
lookup!
CPU.rb
def decode
if (@opcode & 0b11111) == BXX
@instruction = BXX
elsif (@opcode & 0b11111) == SCX
@instruction = SCX
else
@instruction_group = @opcode & 0b11
mode_in_group = (@opcode & 0b11100) >> 2
@addressing_mode = ADDRESSING[
@instruction_group][mode_in_group]
@instruction = @opcode & 0b11100011
end
@time_in_cycles = time_in_cycles
end](https://image.slidesharecdn.com/ruby2600new-130828142032-phpapp01/85/ruby2600-an-Atari-2600-emulator-written-in-Ruby-40-320.jpg)

...return value for position...
end
def []=(position, value)
...react to writing value to position...
end](https://image.slidesharecdn.com/ruby2600new-130828142032-phpapp01/85/ruby2600-an-Atari-2600-emulator-written-in-Ruby-49-320.jpg)

@bytes[address]
end
def []=(address, value)
# Don't write to Read-Only Memory, duh!
end
end](https://image.slidesharecdn.com/ruby2600new-130828142032-phpapp01/85/ruby2600-an-Atari-2600-emulator-written-in-Ruby-51-320.jpg)
![TIA.rb
def draw_scanline
scanline = []
0.upto(SCANLINE_WIDTH) do |pixel|
scanline << topmost_pixel
tick_other_chips pixel
end
return scanline
end
def topmost_pixel ...
def tick_other_chips
@cpu.tick if pixel % 3 == 2
@riot.tick if pixel % 3 == 0
end
TIA runs 3x faster
than CPU and RIOT](https://image.slidesharecdn.com/ruby2600new-130828142032-phpapp01/85/ruby2600-an-Atari-2600-emulator-written-in-Ruby-53-320.jpg)