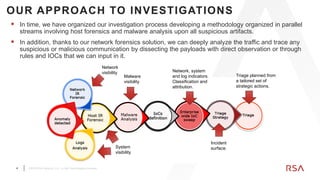
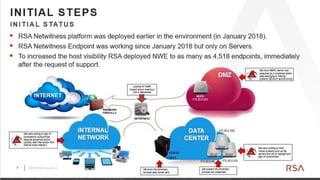
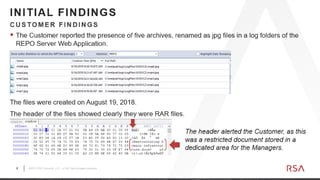
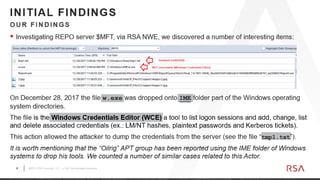
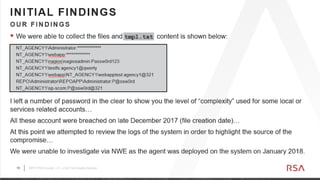
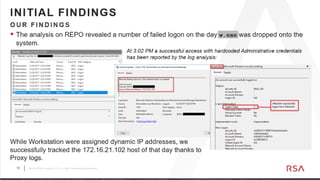
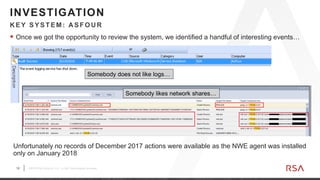
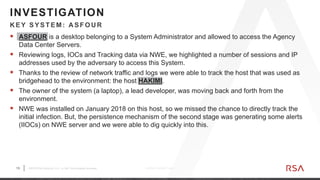
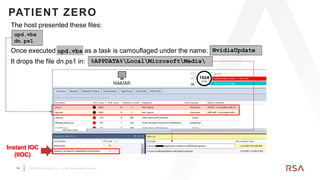
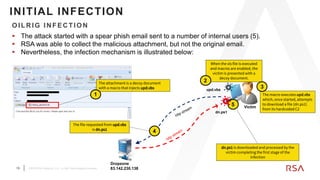
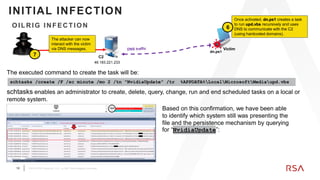
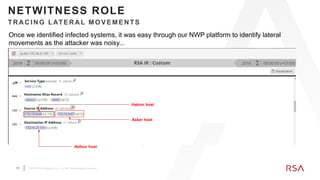
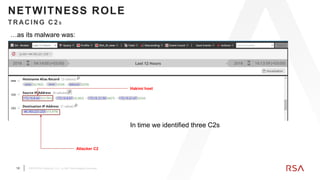
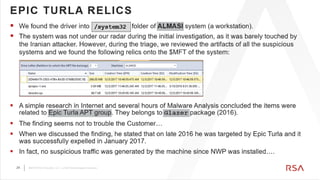
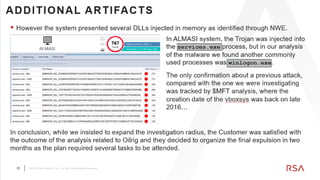
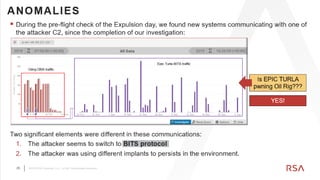
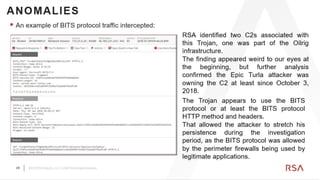
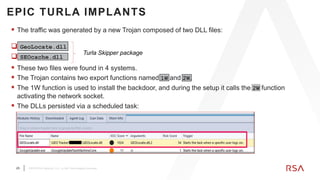
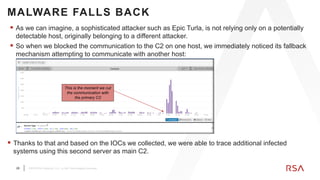
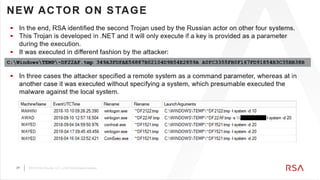
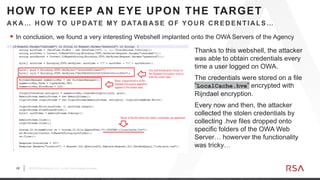
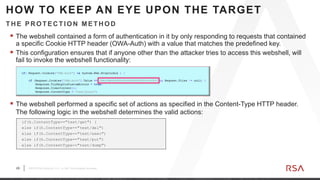
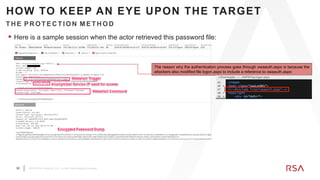
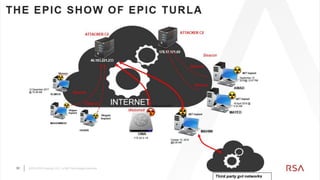
Stefano Maccaglia is a Senior Principal Consultant at RSA who investigates cyber incidents. The document describes an investigation conducted at a government agency that discovered stolen data on an internal system. RSA found the system, called ASFOUR, had been compromised since August 2018. By analyzing logs and network traffic with RSA tools, they traced the activity to an adversary accessing ASFOUR and another system called HAKIMI. They also found evidence of two threat groups - Oilrig and Epic Turla. RSA helped the agency remediate by rebuilding compromised systems, resetting passwords, and removing unused accounts.