The document discusses the complexities of email addresses as defined by RFC standards, highlighting common misunderstandings and mistakes made by developers, testers, and support staff. It details the formatting rules for local and domain parts of email addresses, the implications of 8-bit and international characters, as well as the significance of context in address validation. Additionally, it emphasizes the need for awareness and best practices when handling email addresses to ensure compliance with standards and avoid potential security risks.




![RFC2822 Local Parts
● Unrestricted characters
0..9 a..z A..Z ! # $ % & ' * + - / = ? ^ _ ` | { } ~ .
● Quotable charactersq u( oted by “ )
< [ ( : @ ; ) ] > , non-ws-ctrl
● Illegal characters
All 8-bit.
● Whitespace
ws-ctrl illegal, only used for folding in headers
space character is valid if quoted
[ RFC2821: 4.1.2; RFC2822: 3.2, 3.4 ]](https://image.slidesharecdn.com/rfc2822formeremortals-140830104359-phpapp01/75/RfC2822-for-Mere-Mortals-6-2048.jpg)
![Does Case Matter?
● Case is ignored in domain
ntaba.biz == ntaba.biz
● Strictly-speaking case matters in local-parts
schalk@ntaba.biz != ScHaLk@ntaba.biz
– Most MTAs ignore case
– RFC2821 discourages use of case as a
distinguishing factor
[ RFC2821: 2.4 ]](https://image.slidesharecdn.com/rfc2822formeremortals-140830104359-phpapp01/75/RfC2822-for-Mere-Mortals-8-2048.jpg)
![Does Size Matter?
● RFC2821 places limitations on length of local-part and
domain-part
– 64 characters for local-part
– 255 characters for domain-part
● This is normally not a problem for messages
transmitted across the internet, but can be problematic
for in-house applications or encoded email addresses
such as X.400.
● Many MTAs will now ignore this length restriction as
long as the overall SMTP protocol line length restriction
is not exceeded.
[ RFC2821: 4.5.3.1 ]](https://image.slidesharecdn.com/rfc2822formeremortals-140830104359-phpapp01/75/RfC2822-for-Mere-Mortals-9-2048.jpg)
![Address Literals
● Workarounds for when host names cannot
be resolved.
– @[protocol:host-address]
– IPv4: @[192.1.1.1]
– IPv6: @[IPv6:fe80::a00:20ff:fec2:2ef4]
● Protocol must be registered with ICANN.
[ RFC2821: 4.1.3 ]](https://image.slidesharecdn.com/rfc2822formeremortals-140830104359-phpapp01/75/RfC2822-for-Mere-Mortals-11-2048.jpg)

![Valid or not?
schalk_cronje@[192.168.1.1]
● Yes, the domain part is an address-literal
● Acceptance of address-literals should be
configurable
– They can be security risks
– RFC2821 prefers usage of MX-based deliveries.](https://image.slidesharecdn.com/rfc2822formeremortals-140830104359-phpapp01/75/RfC2822-for-Mere-Mortals-14-2048.jpg)
![Valid or not?
schalk_cronje@192.168.1.1
● No, it is not an address-literal nor a valid
domain name.
● Some systems will attempt to deliver this by
passing the 192.168.1.1 to the domain
resolving subsystem, which in return will
simply return the IP address.
– This violates RFC1123
– This is a potential security risk.
[ RFC1123: 2.1 ]](https://image.slidesharecdn.com/rfc2822formeremortals-140830104359-phpapp01/75/RfC2822-for-Mere-Mortals-15-2048.jpg)
![Valid or not?
schalk_cronje@1967.com
● Not valid according to RFC1035
● Limitation lifted in RFC1123.
[ RFC1123: 2.1 ]](https://image.slidesharecdn.com/rfc2822formeremortals-140830104359-phpapp01/75/RfC2822-for-Mere-Mortals-16-2048.jpg)
![Valid or not?
schalk_cronje@#192168
● Valid in RFC821 for compatibility with
non-TCP/IP networks.
● Outlawed by RFC2821.
● Not supported by any modern MTA.
[ RFC821: 4.1.2; RFC2821: F.4 ]](https://image.slidesharecdn.com/rfc2822formeremortals-140830104359-phpapp01/75/RfC2822-for-Mere-Mortals-17-2048.jpg)
![Valid or not?
schalk_cronje@.ntaba.biz
● No, domain-part may not start with a dot.
[ RFC2822: 3.2.4 ]](https://image.slidesharecdn.com/rfc2822formeremortals-140830104359-phpapp01/75/RfC2822-for-Mere-Mortals-18-2048.jpg)
![Valid or not?
schalk_cronje@ntaba.biz.
● No, strictly RFC2822 states that domain-part
may not end with a dot.
● RFC1034 use the dot-ending to indicate
absolute domains (FQDN) in resource
records.
● Most systems will accept, resolve and deliver
this
[ RFC2822: 3.2.4; RFC1034: 3.1]](https://image.slidesharecdn.com/rfc2822formeremortals-140830104359-phpapp01/75/RfC2822-for-Mere-Mortals-19-2048.jpg)
![Valid or not?
schalk_cronje@ntaba..biz.
● No, consecutive dots are not allowed in
domain parts.
[ RFC2822: 3.2.4; RFC1034: 3.1]](https://image.slidesharecdn.com/rfc2822formeremortals-140830104359-phpapp01/75/RfC2822-for-Mere-Mortals-20-2048.jpg)
![Valid or not?
● No.
.schalk_cronje@ntaba.biz
schalk..cronje@ntaba.biz
– Local-parts may not start with a dot.
– Consecutive dots are not allowed in local parts.
● Pragmatically, many known MTAs don’t care
[ RFC2822: 3.2.4]](https://image.slidesharecdn.com/rfc2822formeremortals-140830104359-phpapp01/75/RfC2822-for-Mere-Mortals-21-2048.jpg)
![Valid or not?
schalk_cronje@lon_eng.ntaba.biz
● No, _ is not valid in domain names
● Some DNS servers will support this.
● Some sites do use th_e for internal systems.
● It remains illegal for internet operations
[ RFC2821: 4.1.3 ]](https://image.slidesharecdn.com/rfc2822formeremortals-140830104359-phpapp01/75/RfC2822-for-Mere-Mortals-22-2048.jpg)
![Valid or not?
schalk_cronje@lon_eng@ntaba.biz
● No, @ cannot be used unquoted in local
parts
“schalk_cronje@lon_eng”@ntaba.biz
schalk_cronje@lon_eng@ntaba.biz
[ RFC2822: 3.2.5, 3.4 ]](https://image.slidesharecdn.com/rfc2822formeremortals-140830104359-phpapp01/75/RfC2822-for-Mere-Mortals-23-2048.jpg)
![Local-part Quoting
● Quoting should only be used where
absolutely necessary
● Where a quoted-form have an unquoted
form...
– The two forms are equivalent
– The unquoted form should be used for
transmission
● Quoting is performed by enclosing local-part
in quotes or preceding a character by
backslash.
[ RFC2821: 4.1.2 ]](https://image.slidesharecdn.com/rfc2822formeremortals-140830104359-phpapp01/75/RfC2822-for-Mere-Mortals-24-2048.jpg)


![Valid or not?
“schalk_O”cronje”@ntaba.biz
● This is debatable
● Neither RFC2821, nor RFC2822, is
completely clear whether the double quote is
valid if escaped
Note that the backslash, "", is a quote character, which is
used to indicate that the next character is to be used literally
[ RFC2821: 4.1.2 ]](https://image.slidesharecdn.com/rfc2822formeremortals-140830104359-phpapp01/75/RfC2822-for-Mere-Mortals-28-2048.jpg)

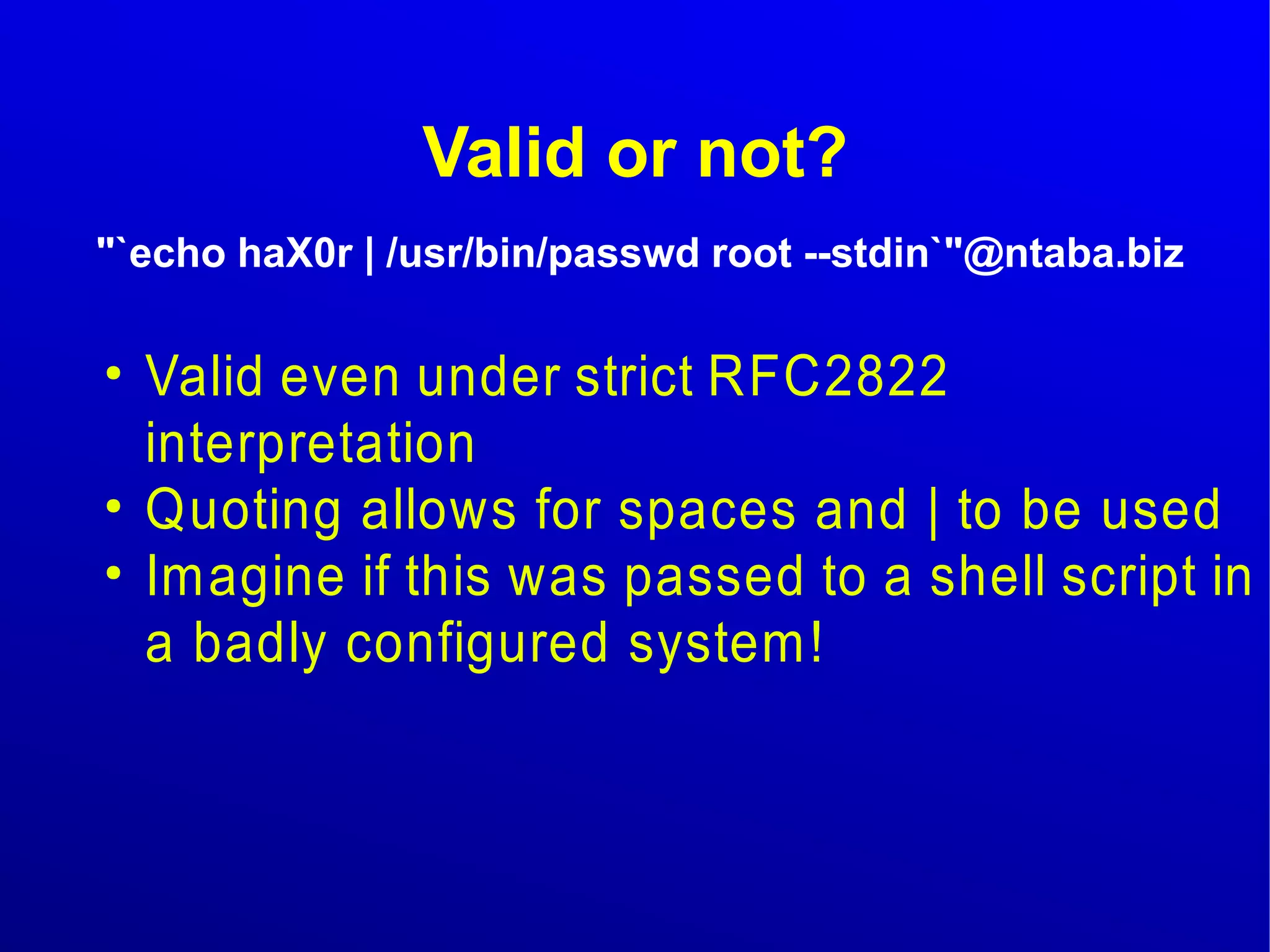
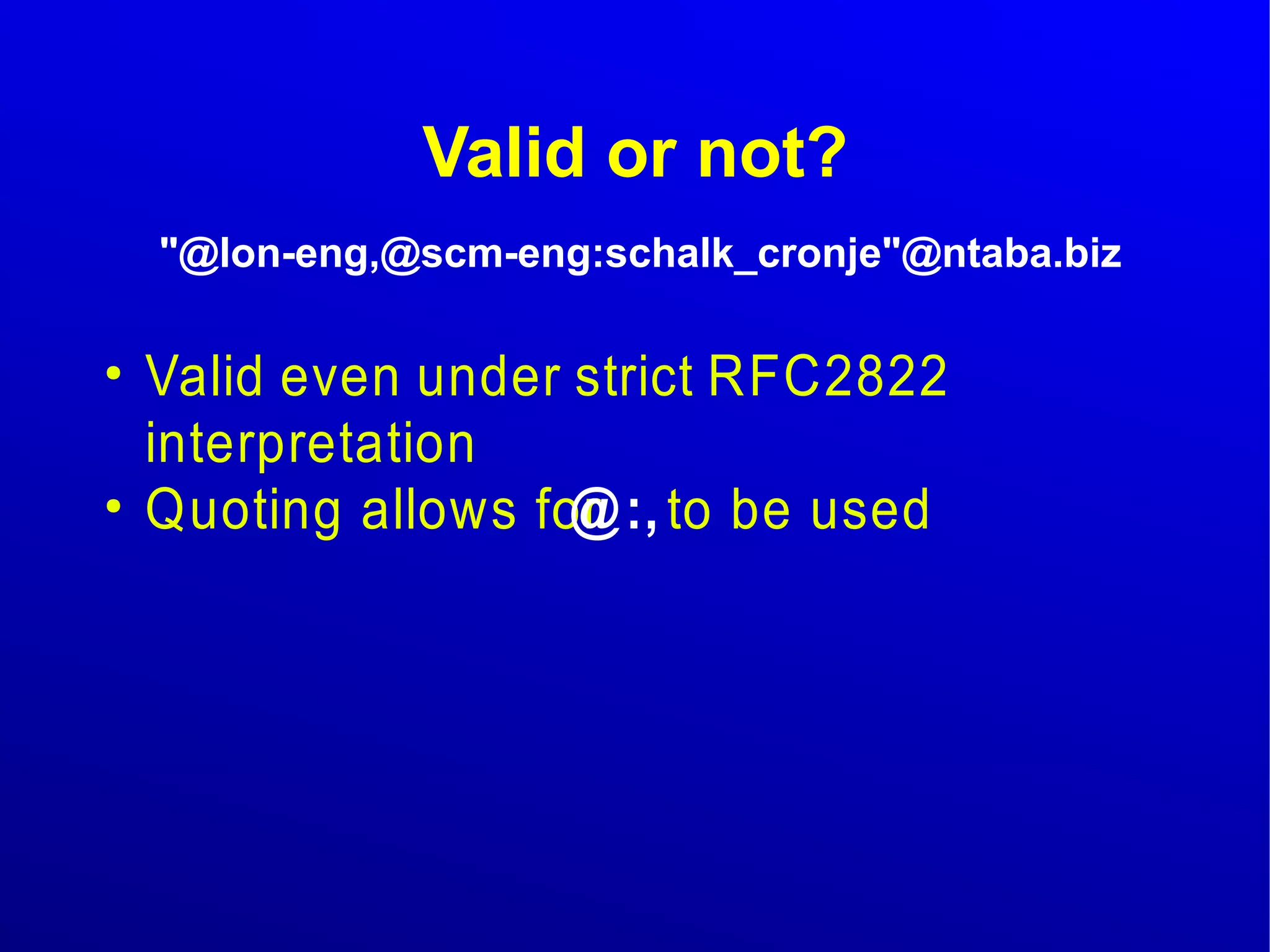
![Valid or not?
@lon-eng,@scm-eng:schalk_cronje@ntaba.biz
● Valid even under strict RFC2822
interpretation
● This is an example of a source-route.
● Usage is deprecated
● It is best to remove them, before relaying.
[ RFC2821: 3.7, C, F.2 ]](https://image.slidesharecdn.com/rfc2822formeremortals-140830104359-phpapp01/75/RfC2822-for-Mere-Mortals-34-2048.jpg)