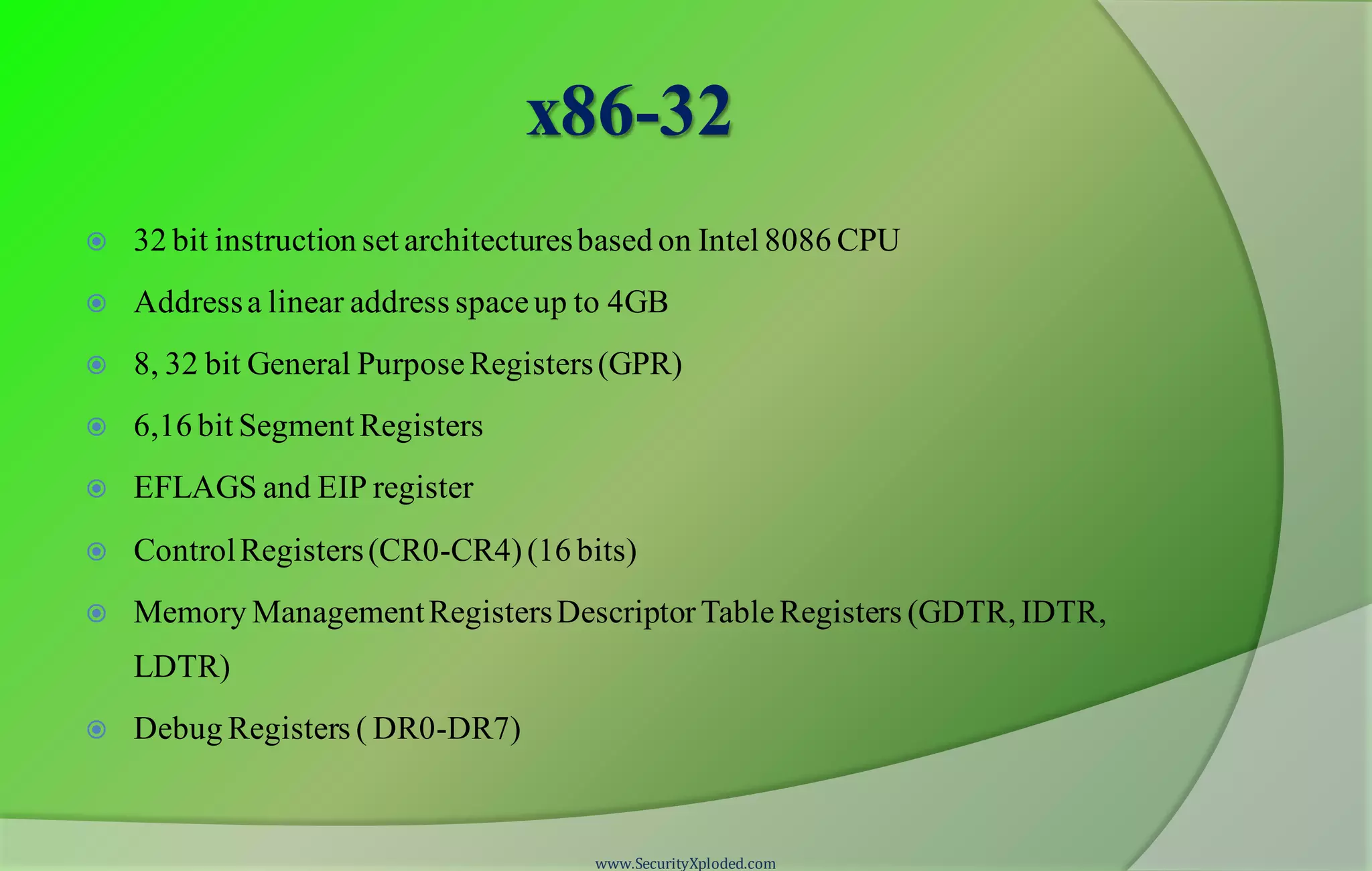
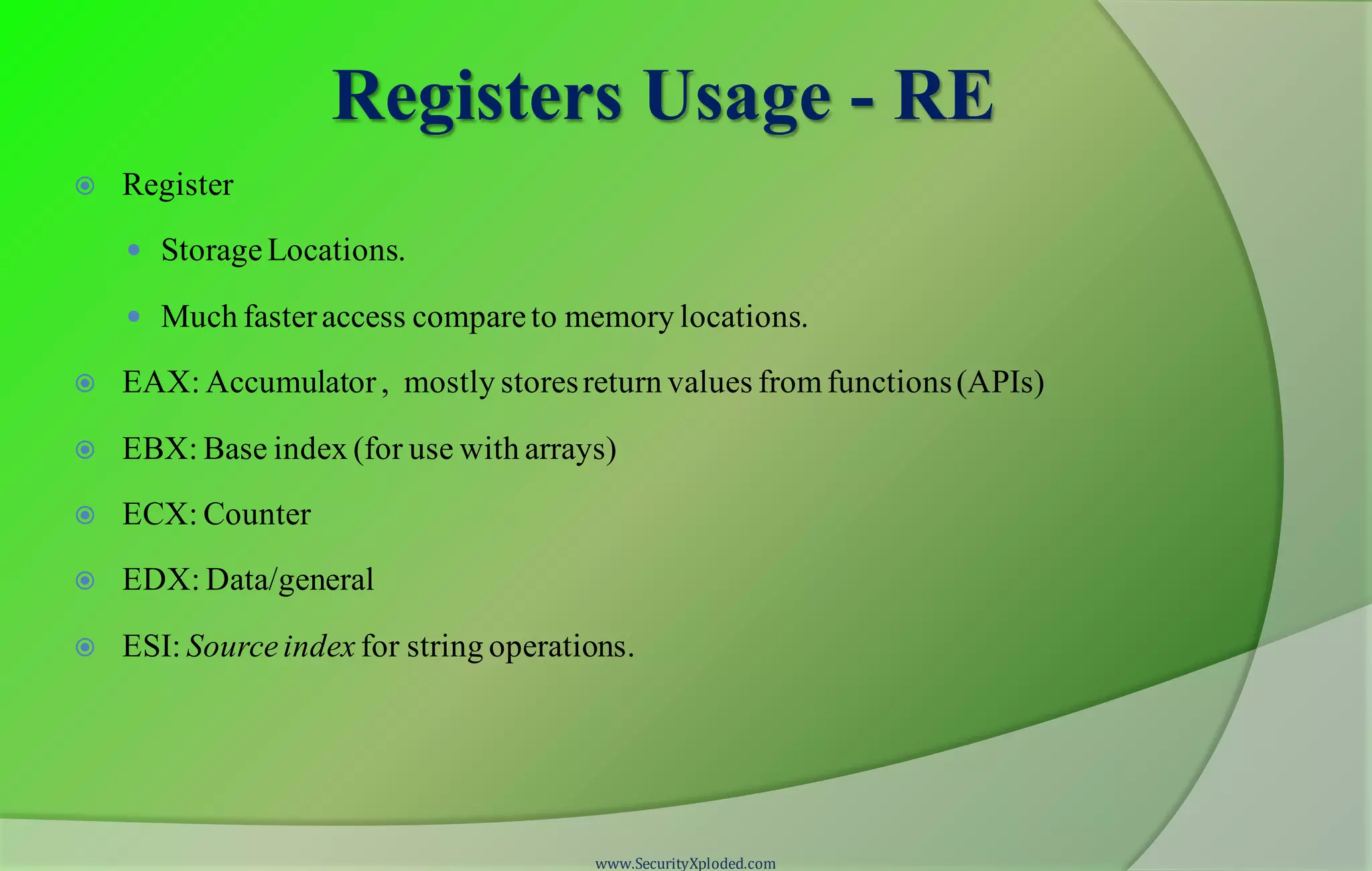
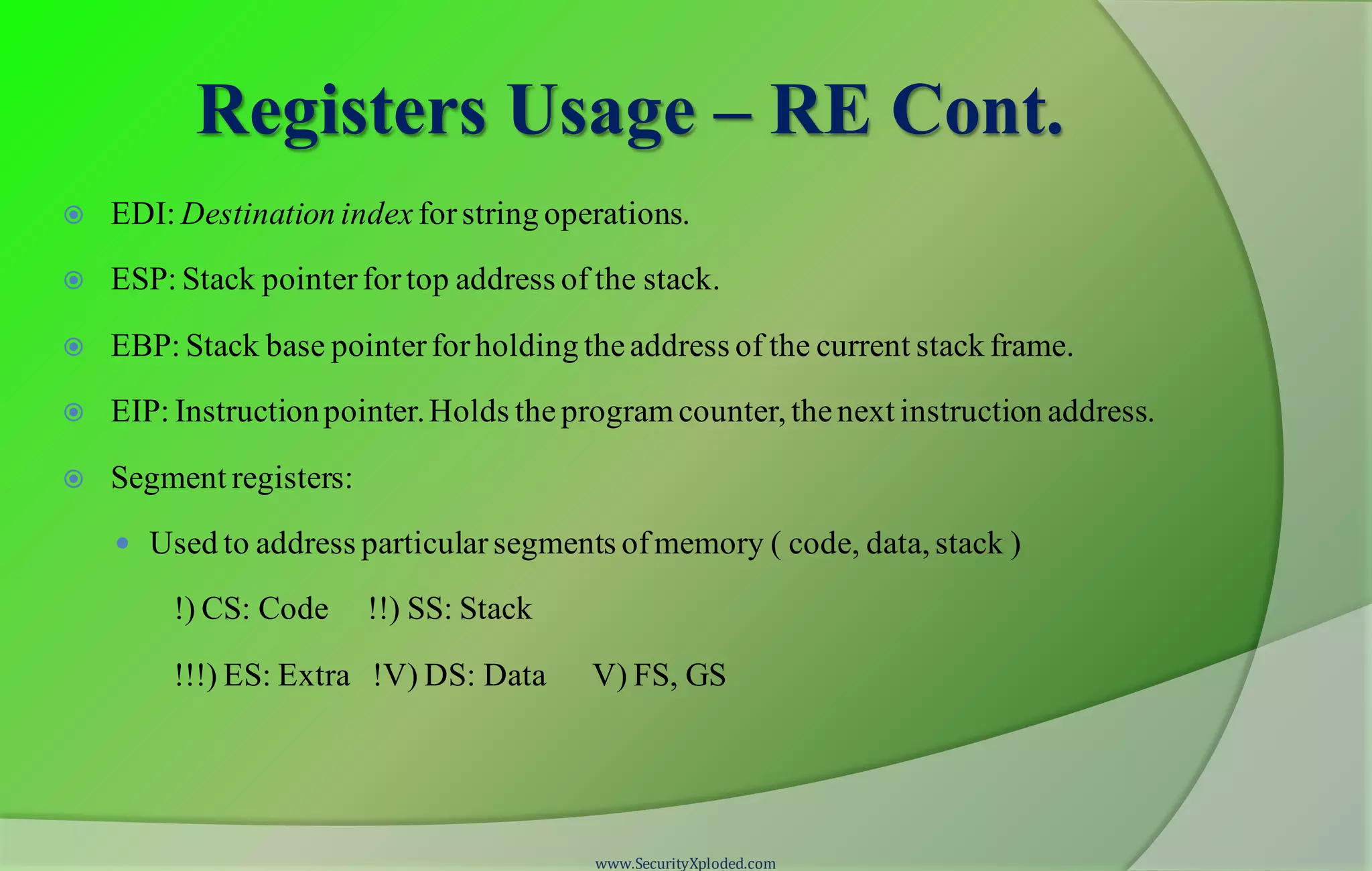
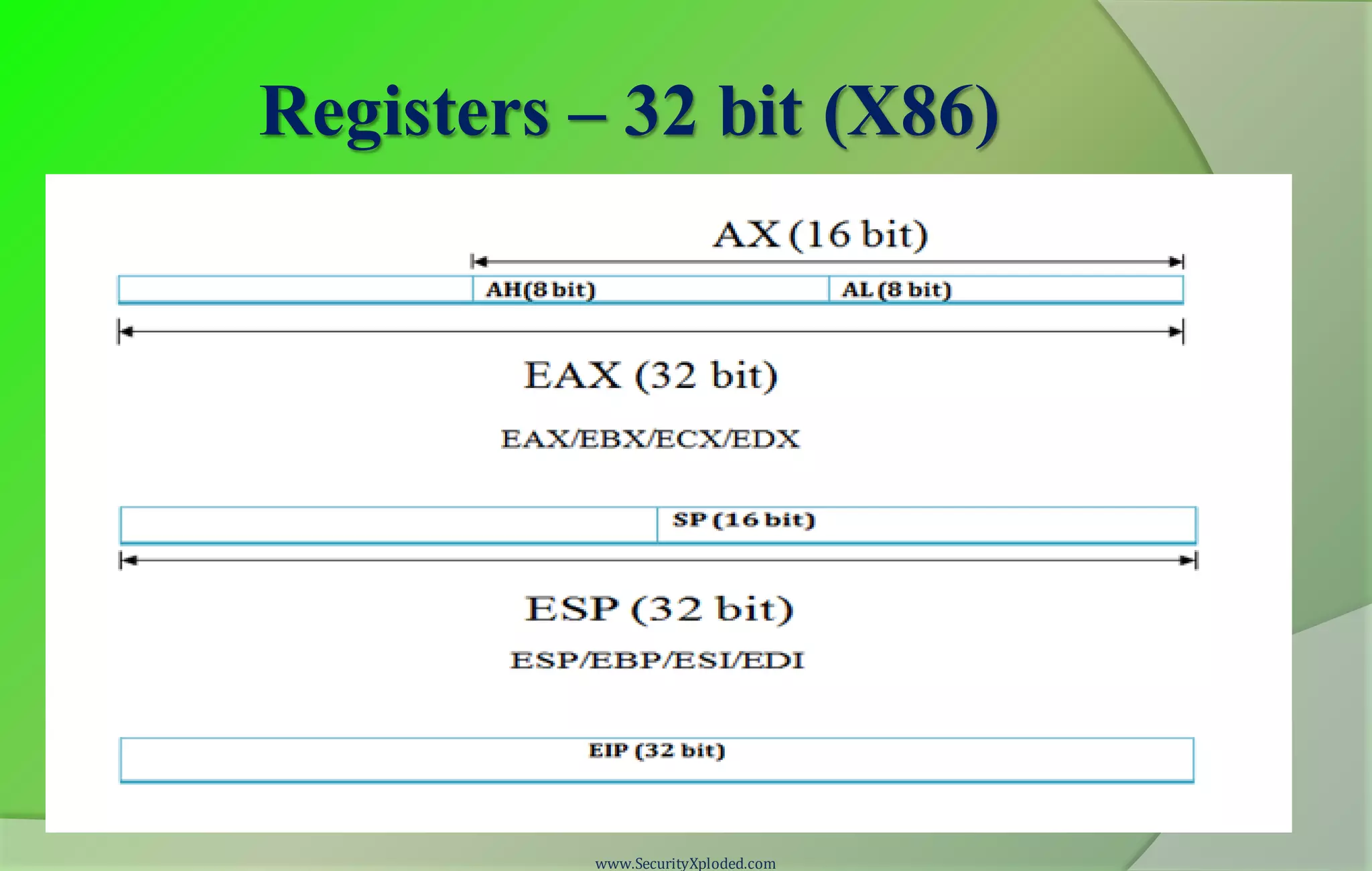
The document discusses an introduction to x86-32 assembly language and reversing techniques. It covers common x86 registers, instructions, stack operations, and calling conventions. The presentation is part of a reversing and malware analysis training program delivered by SecurityXploded members Amit Malik and Swapnil Pathak, who are security researchers at McAfee Labs. It provides contact information and outlines the topics that will be discussed, including x86 architecture, assembly language, demonstrations, and a Q&A section.


![Assembly Language
Low level programming language
Symbolicrepresentationof machinecodes, constants.
Assemblylanguageprogramconsist ofsequenceof process instructions and meta
statements
Assemblertranslates themto executableinstructionsthat are loaded into memory and
executed.
BasicStructure
[label]: opcode operand1,operand2
opcode – mnemonicthat symbolizeinstructions
Example.
MOV AL, 61h => 1011000001100001
www.SecurityXploded.com](https://image.slidesharecdn.com/reversingmalwareanalysistrainingpart4-assemblyprogrammingbasics-131009095600-phpapp02/75/Reversing-malware-analysis-training-part-4-assembly-programming-basics-14-2048.jpg)
![Instructions cont.
MOV dst, src
- Moves datafrom src (left operand)to destination(right operand)
- For examplemov EDI, ESI
Note:
- Both operands cannotbe memory locations.
- Both the operands must be of the same size
LEAdst, src
- Stands forLoad EffectiveAddress.
- Computestheeffectiveaddress of src operand and stores it in dst operand.
- For exampleLEA ECX,[EBX + 5]
Note:
- Generally bracketsdenotevalueat memory locations.
- In case of LEA it does simplearithmeticand stores it in dst
www.SecurityXploded.com](https://image.slidesharecdn.com/reversingmalwareanalysistrainingpart4-assemblyprogrammingbasics-131009095600-phpapp02/75/Reversing-malware-analysis-training-part-4-assembly-programming-basics-16-2048.jpg)
![Instructions cont.
REP
- Used with string operations
- Repeats a string instructionuntil ECX (counterregister)valueis equal to zero.
- For exampleREPMOVS byte ptr DS:[EDI], DS:[ESI]
LOOP
- Similarto loops in high level languages
- Used to executesequenceof instructionsmultipletimes.
- For example
MOV ECX, 10
Test : INC EBX
INC EAX
LOOP Test
www.SecurityXploded.com](https://image.slidesharecdn.com/reversingmalwareanalysistrainingpart4-assemblyprogrammingbasics-131009095600-phpapp02/75/Reversing-malware-analysis-training-part-4-assembly-programming-basics-18-2048.jpg)
![Instructions cont.
CALLaddress
- Performs two functions
- Push address of the next instructionon stack (return address)
- Jump to the address specifiedby the instruction
- For exampleCALL dword ptr [EAX+4]
RET
- Transfers thecontrol to the address previously pushedon the stack by CALL
instruction
- Mostlydenotestheend of the function
www.SecurityXploded.com](https://image.slidesharecdn.com/reversingmalwareanalysistrainingpart4-assemblyprogrammingbasics-131009095600-phpapp02/75/Reversing-malware-analysis-training-part-4-assembly-programming-basics-20-2048.jpg)