Embed presentation
Downloaded 70 times
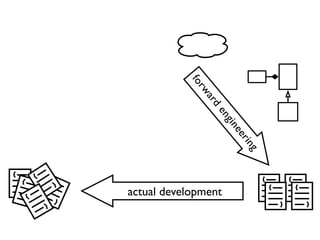
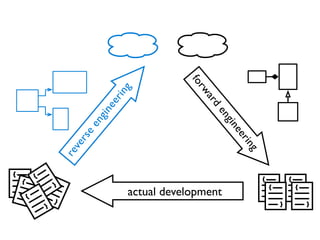
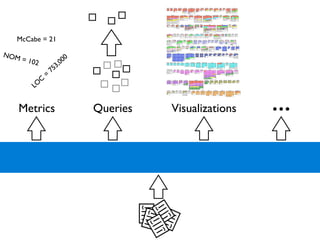
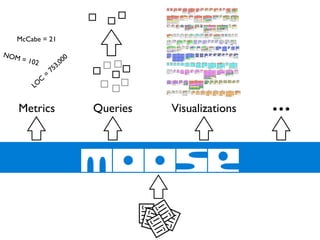
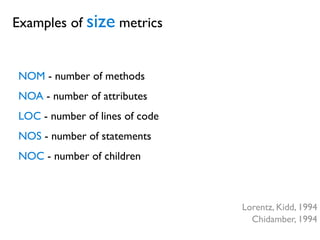
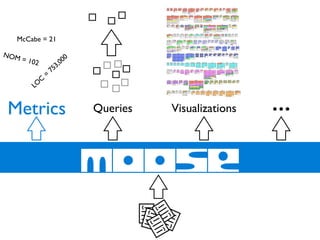
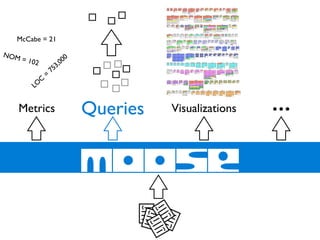
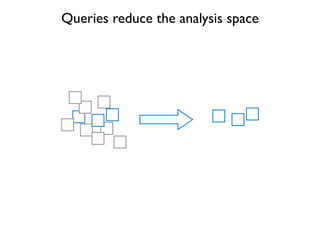
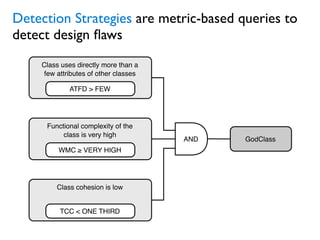
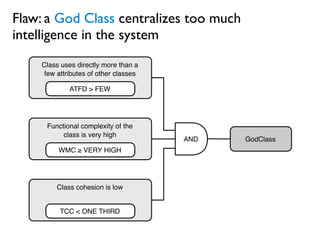
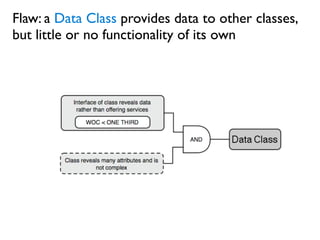
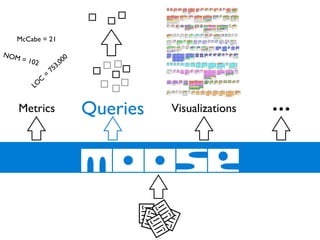
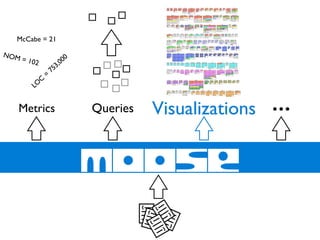
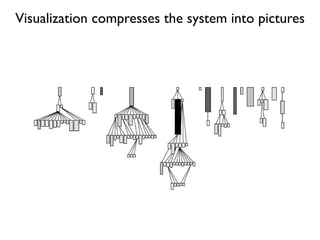
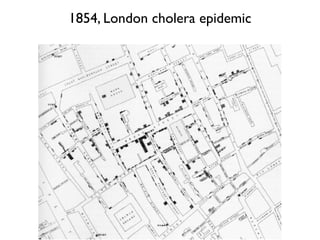
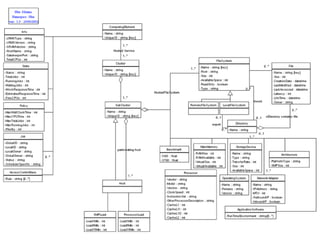
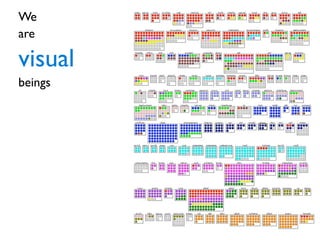

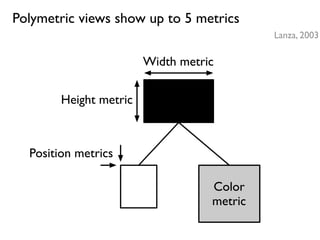
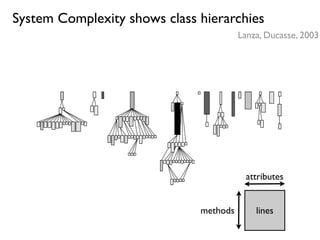
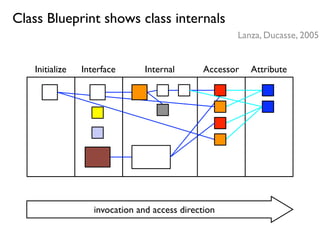
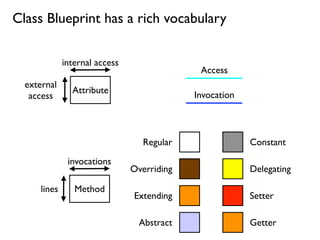
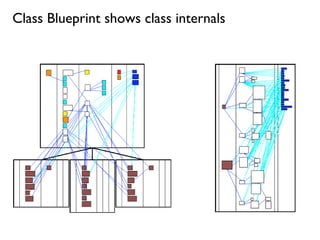
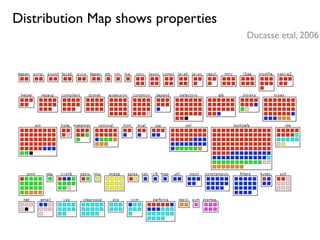
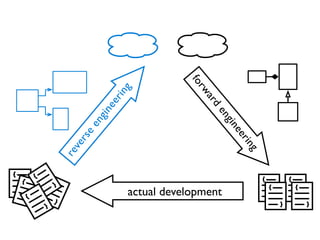
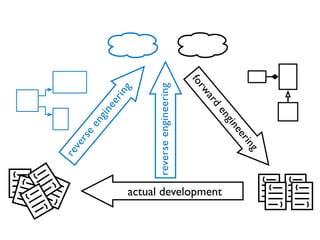
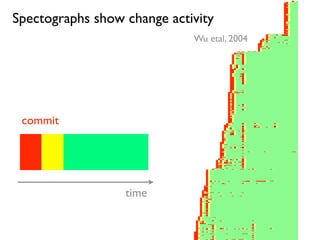
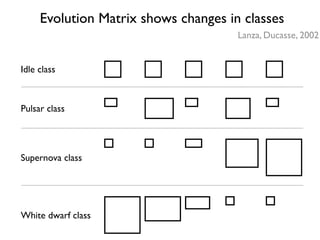
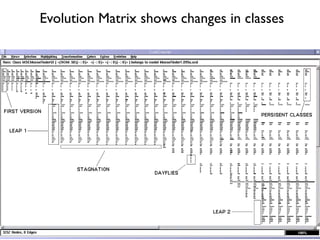
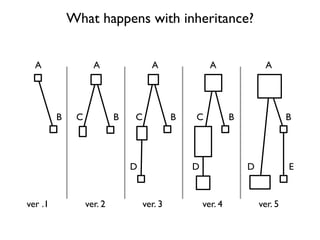
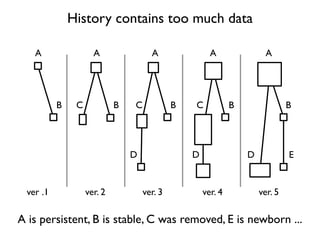
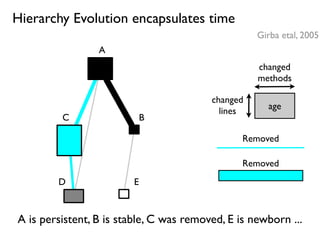
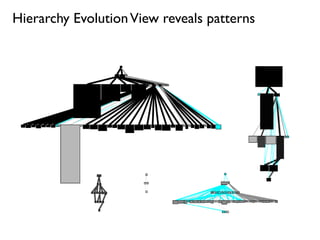
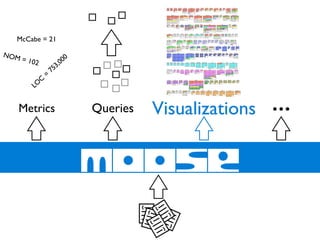
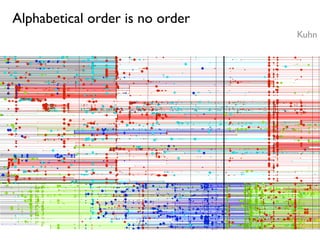
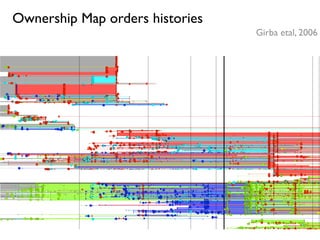
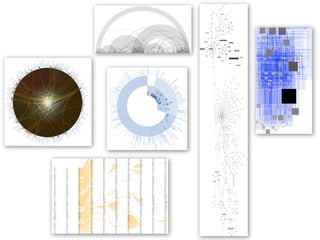
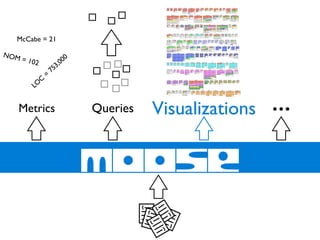


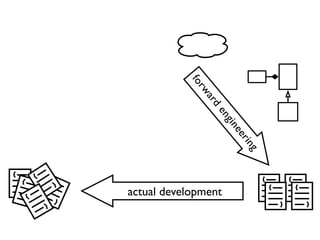
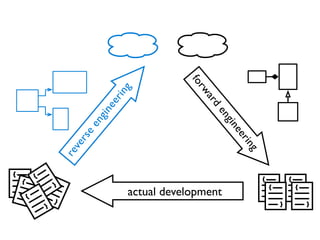
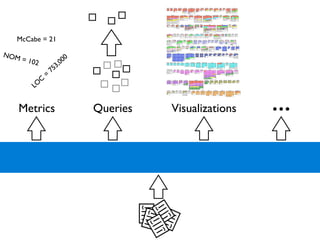
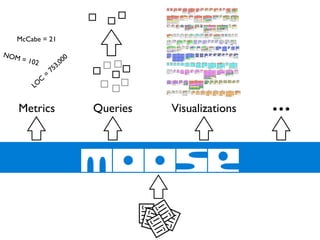
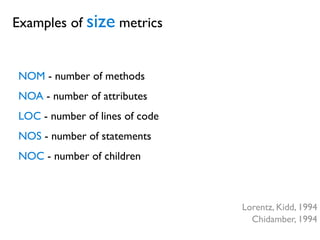
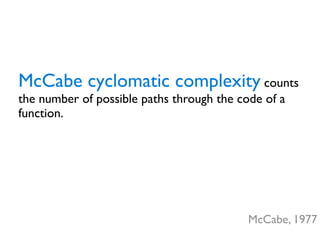
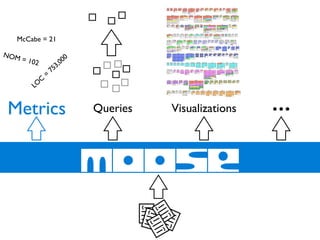
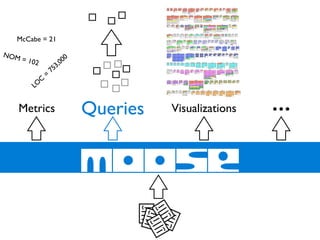
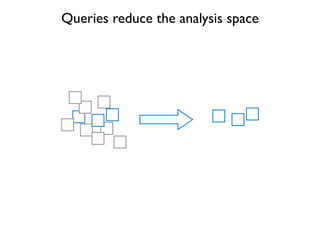
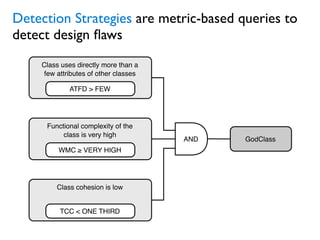
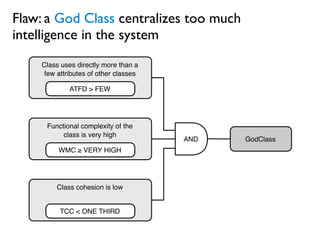
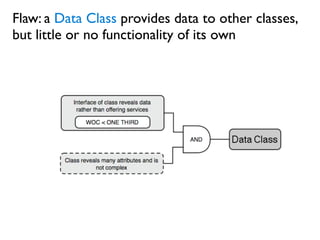
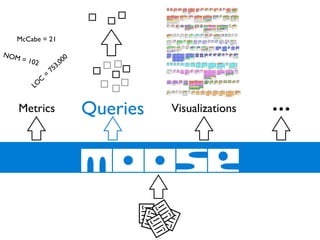
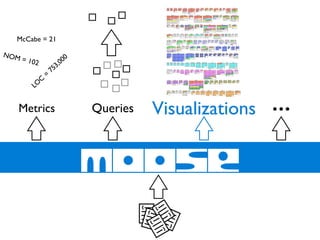
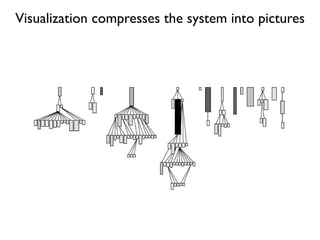
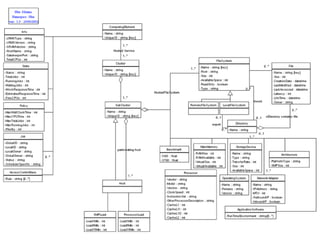
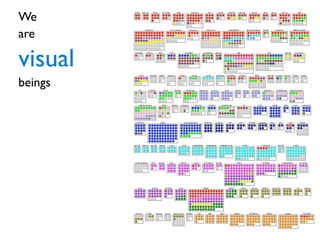
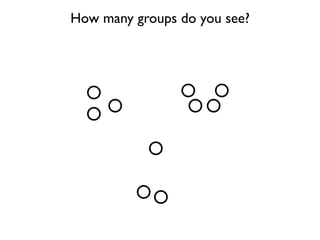
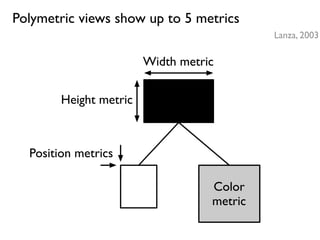
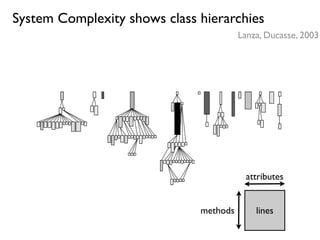
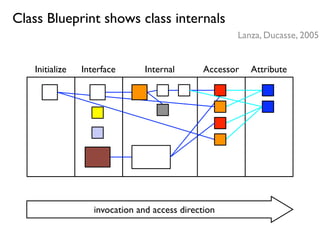
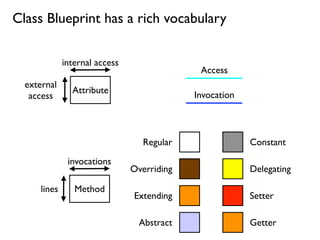
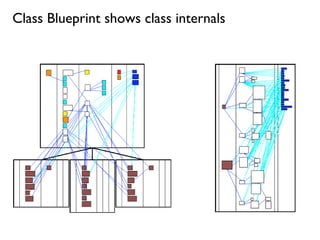
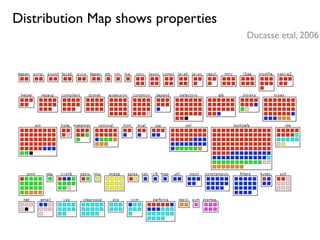
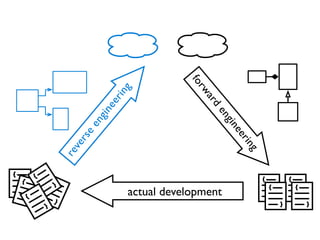
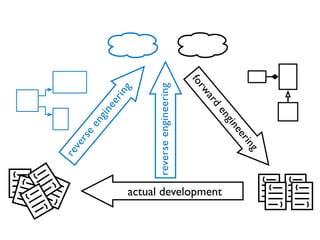
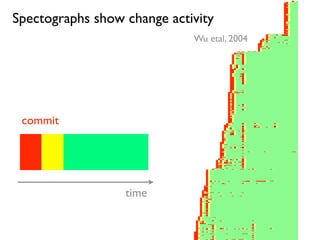
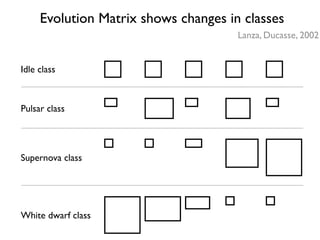
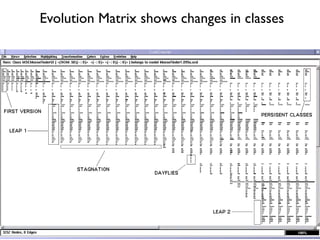
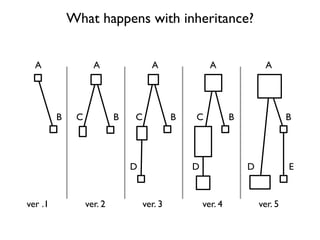
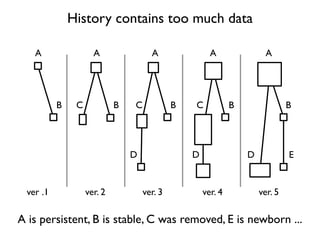
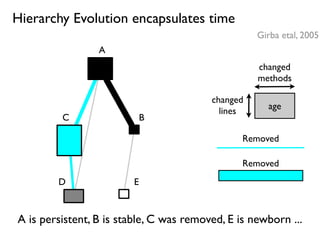
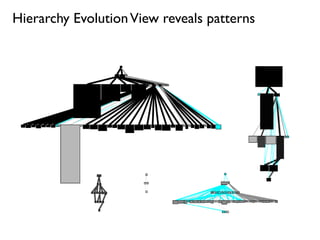
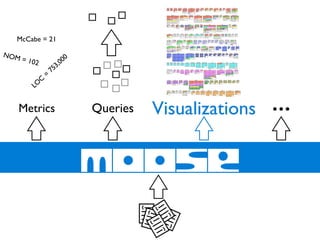
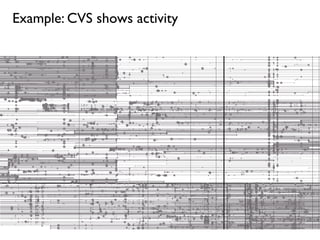
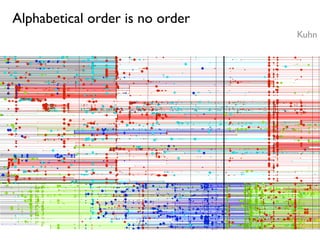
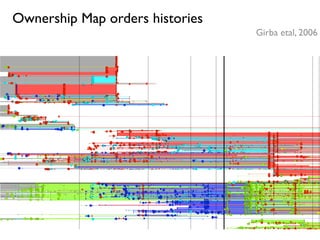
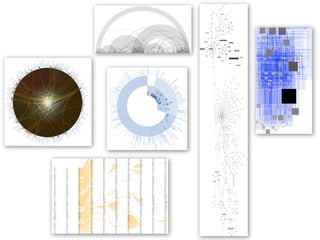
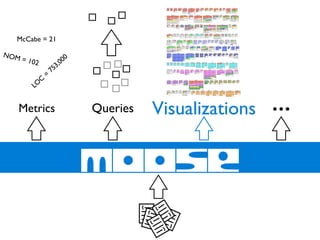
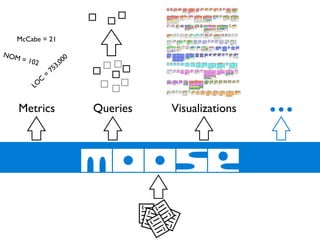
Reverse engineering techniques involve metrics, queries, and visualizations to analyze software systems. Metrics compress a system into measurable properties like lines of code and complexity. Queries detect patterns and flaws through metric-based rules. Visualizations compress a system into graphical representations like UML diagrams and polymetric views to show relationships and changes over time.