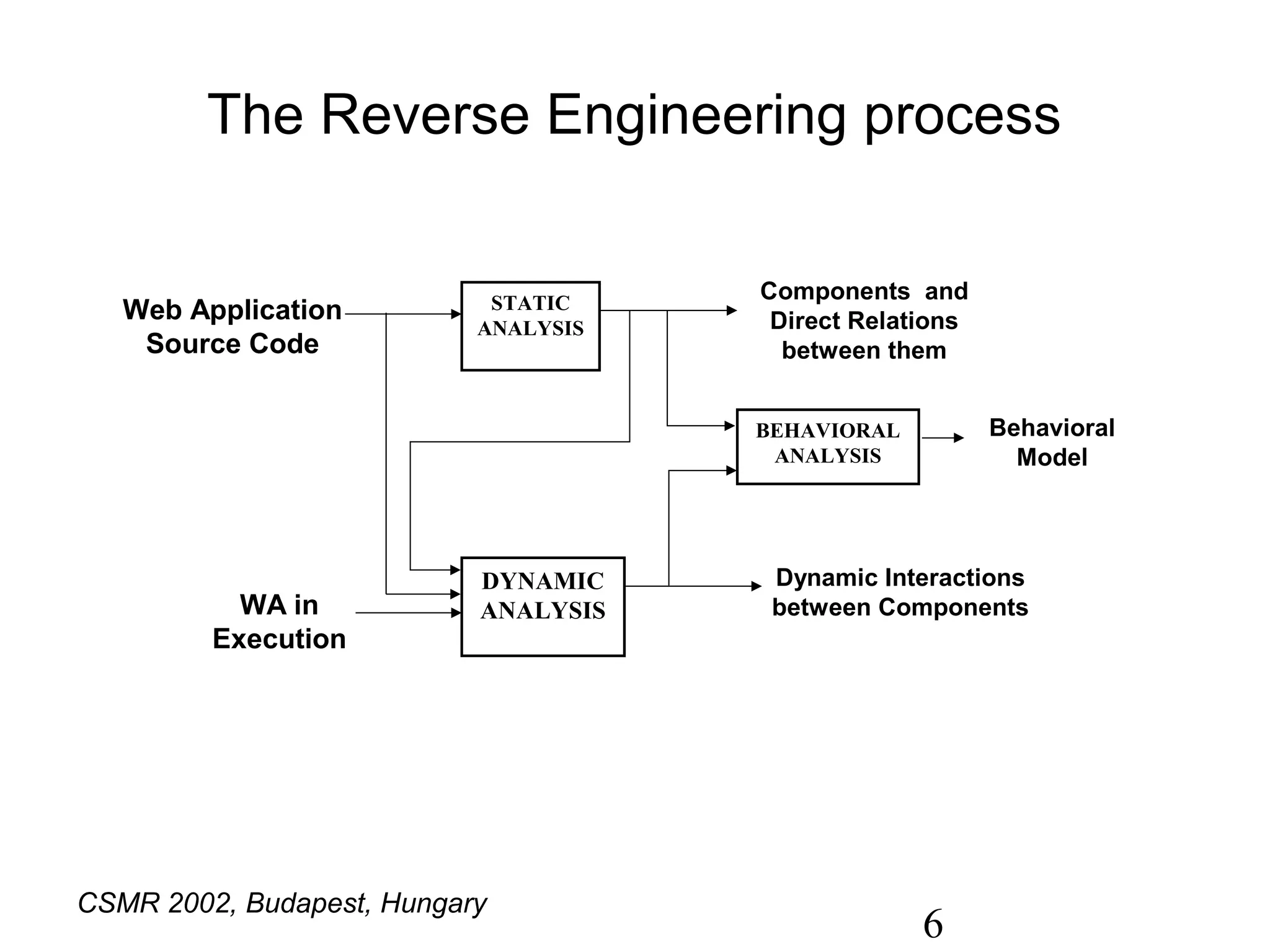
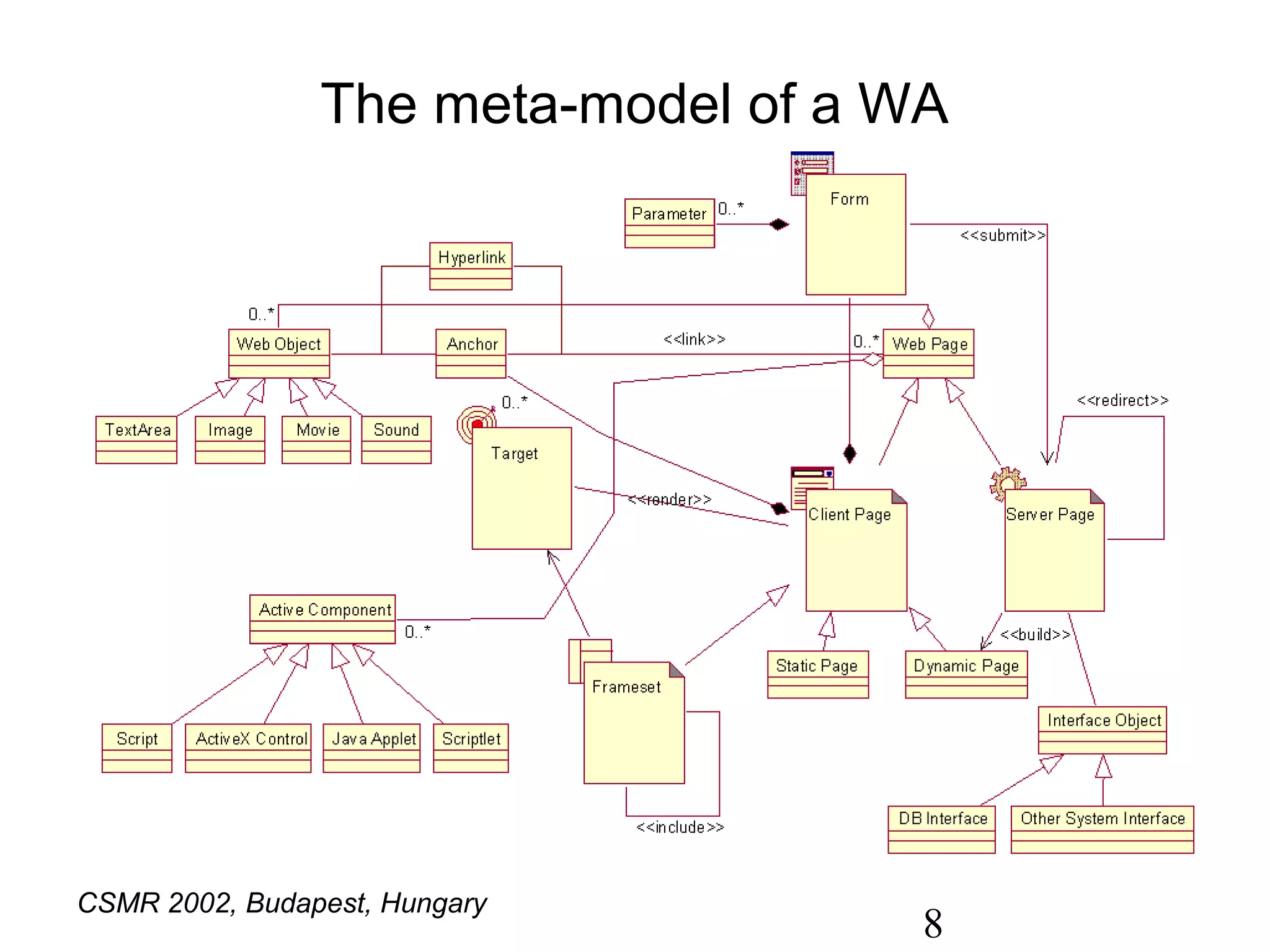
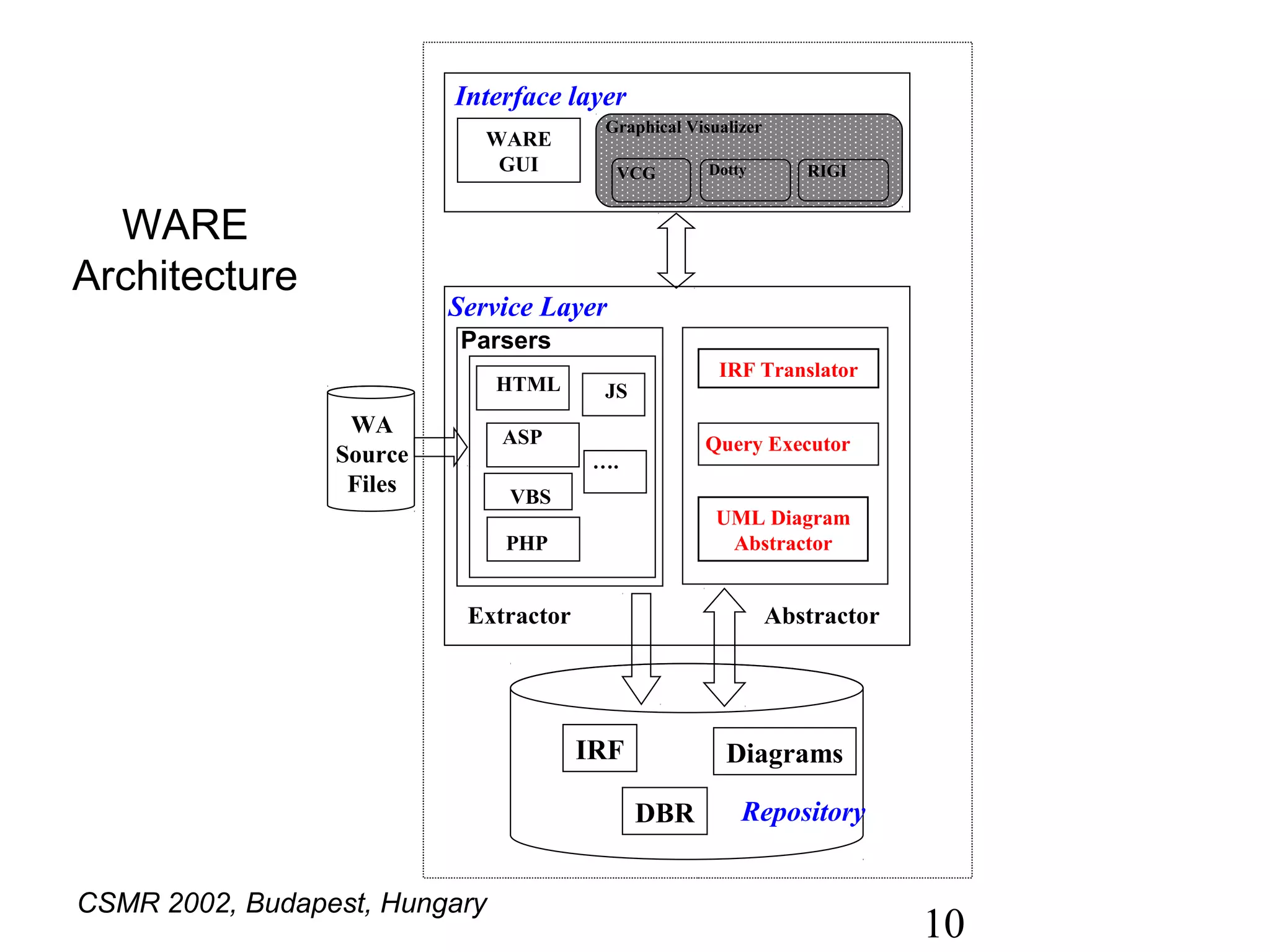
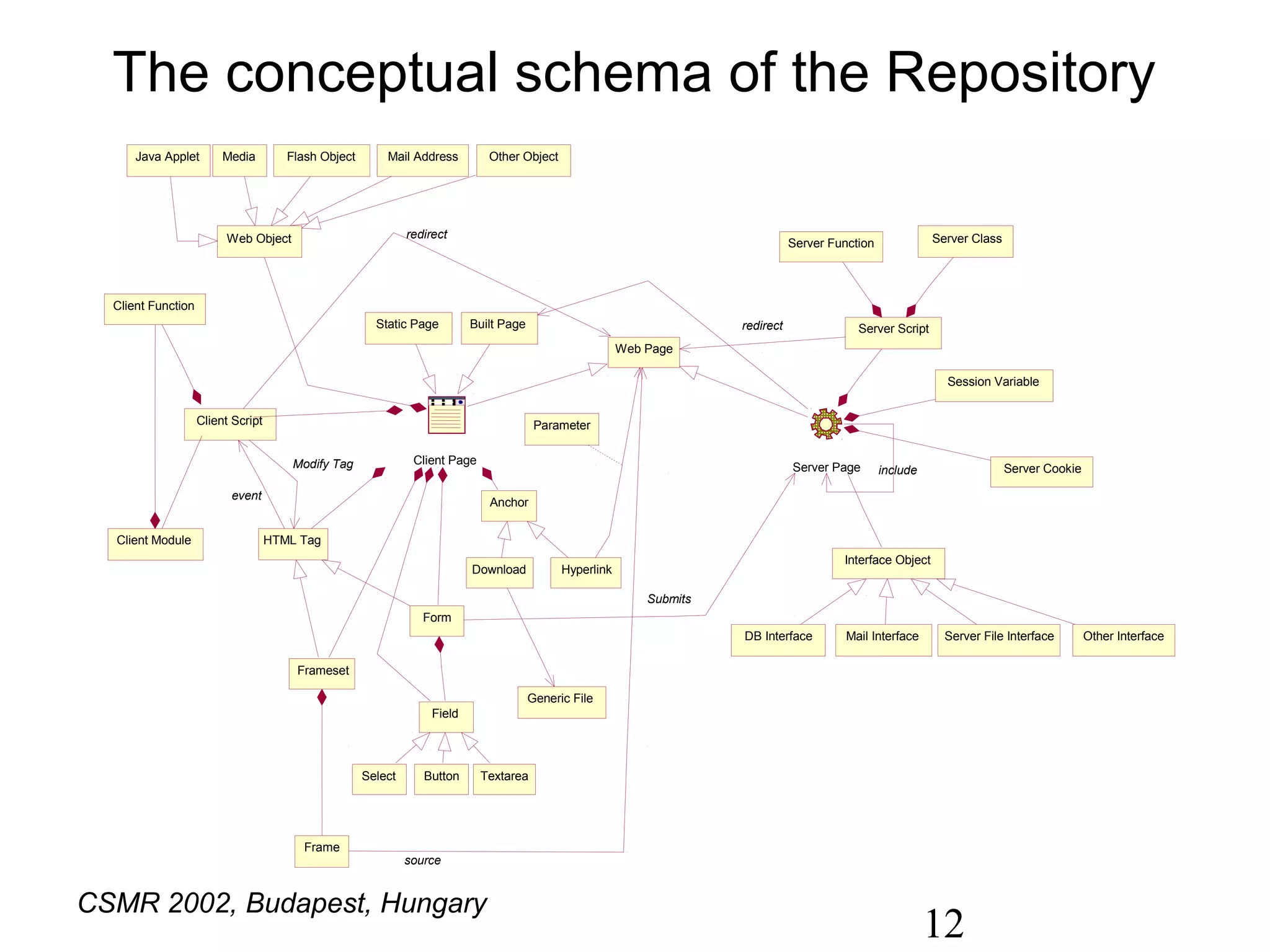
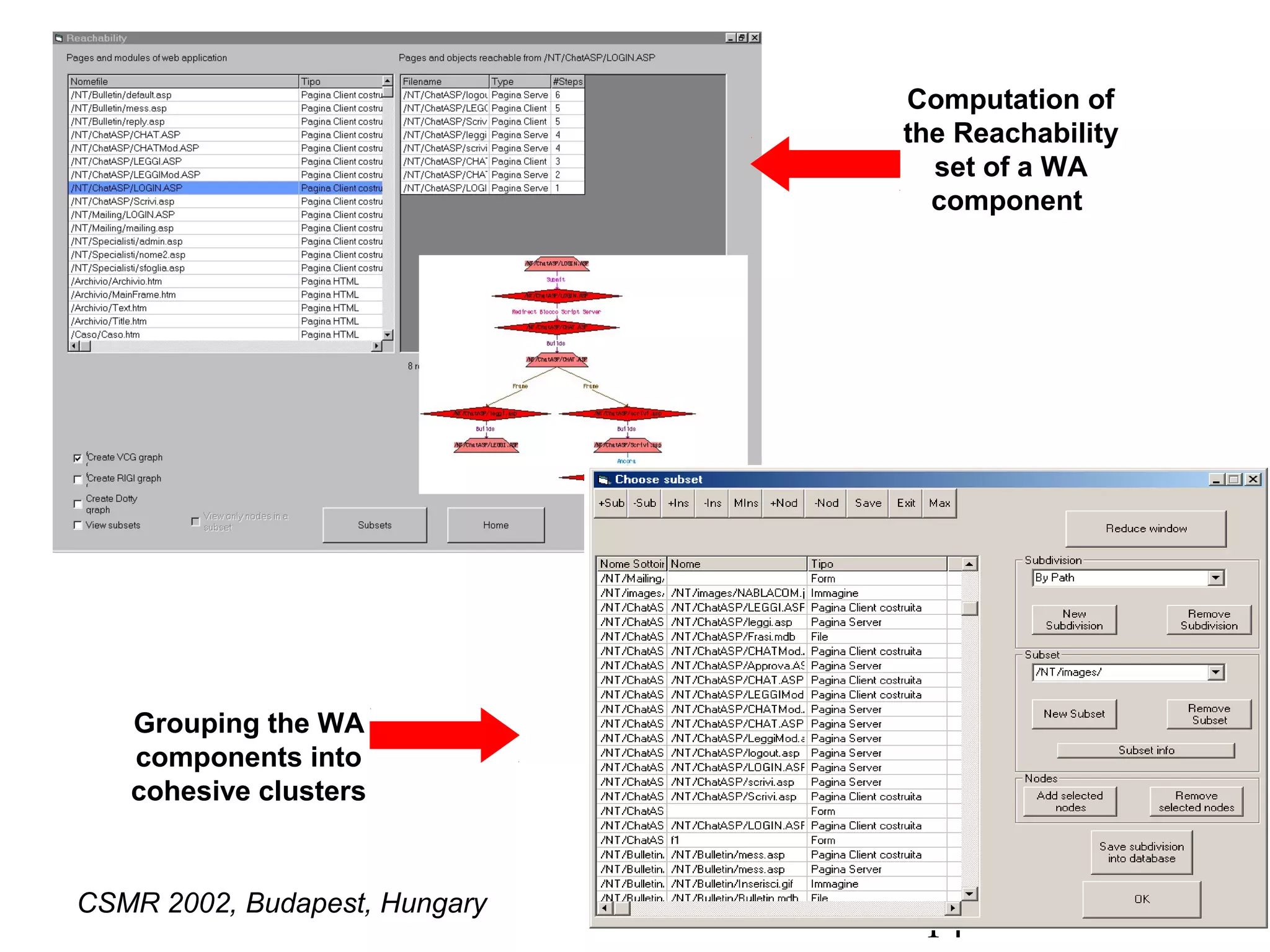
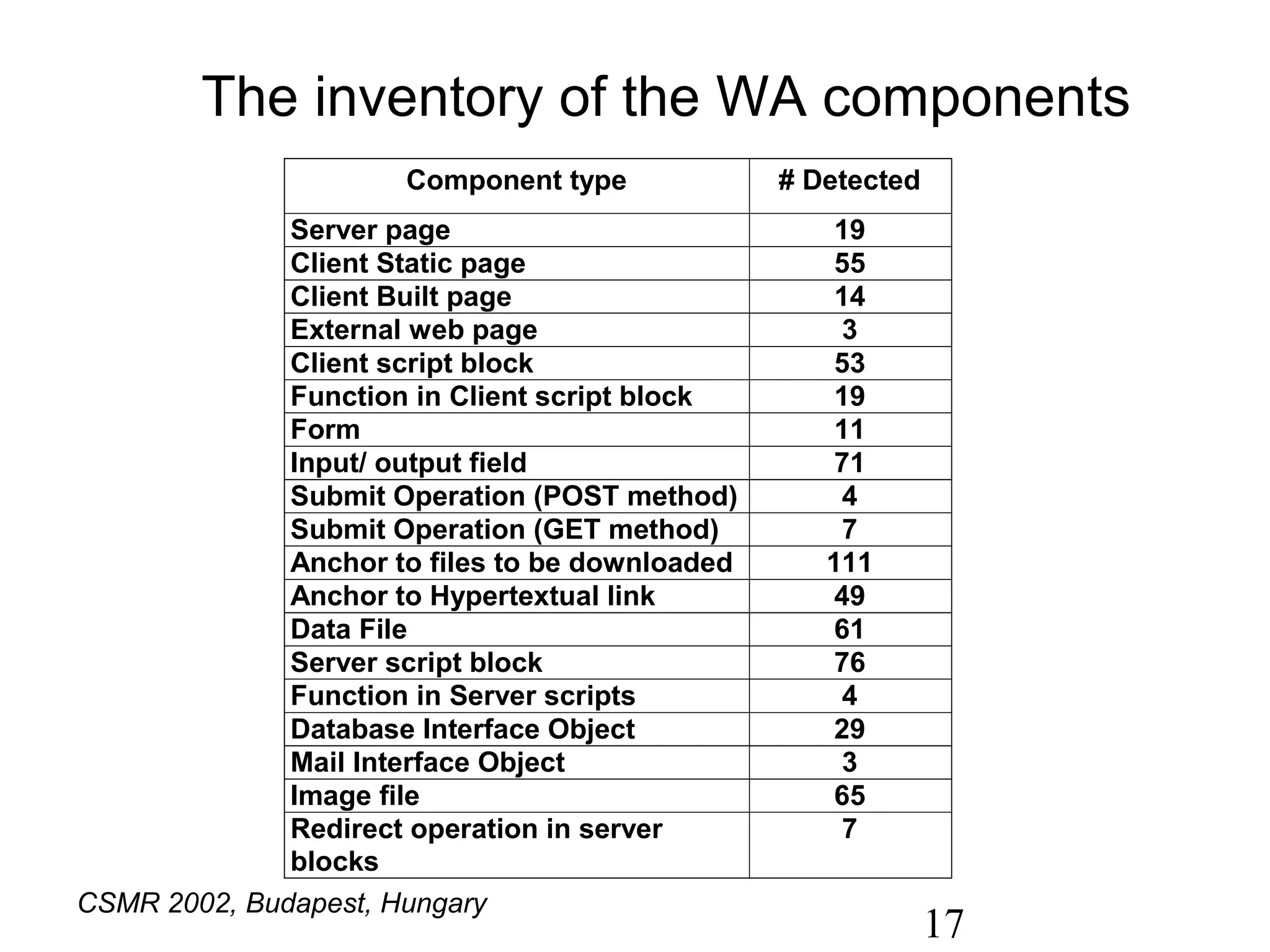
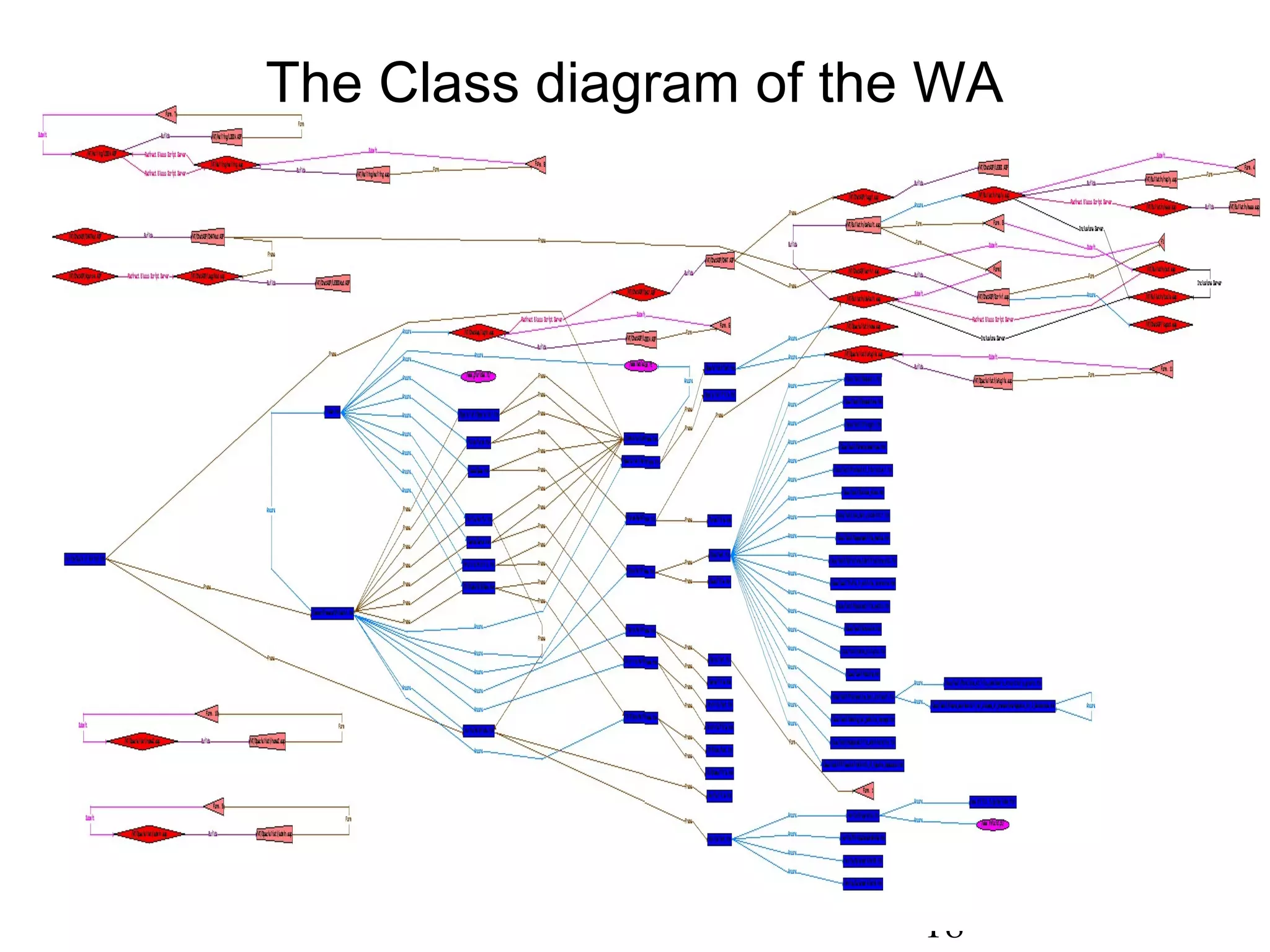
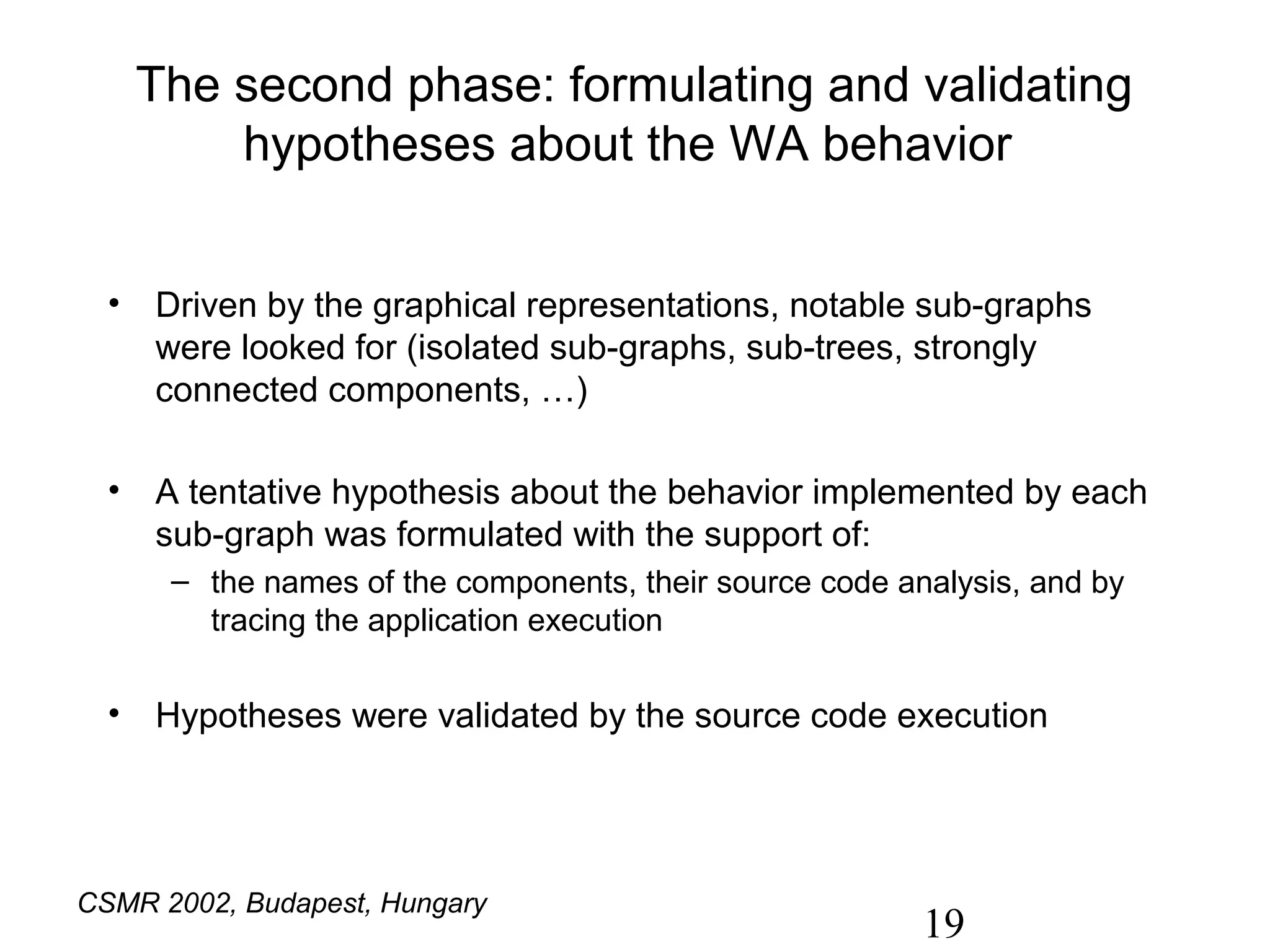
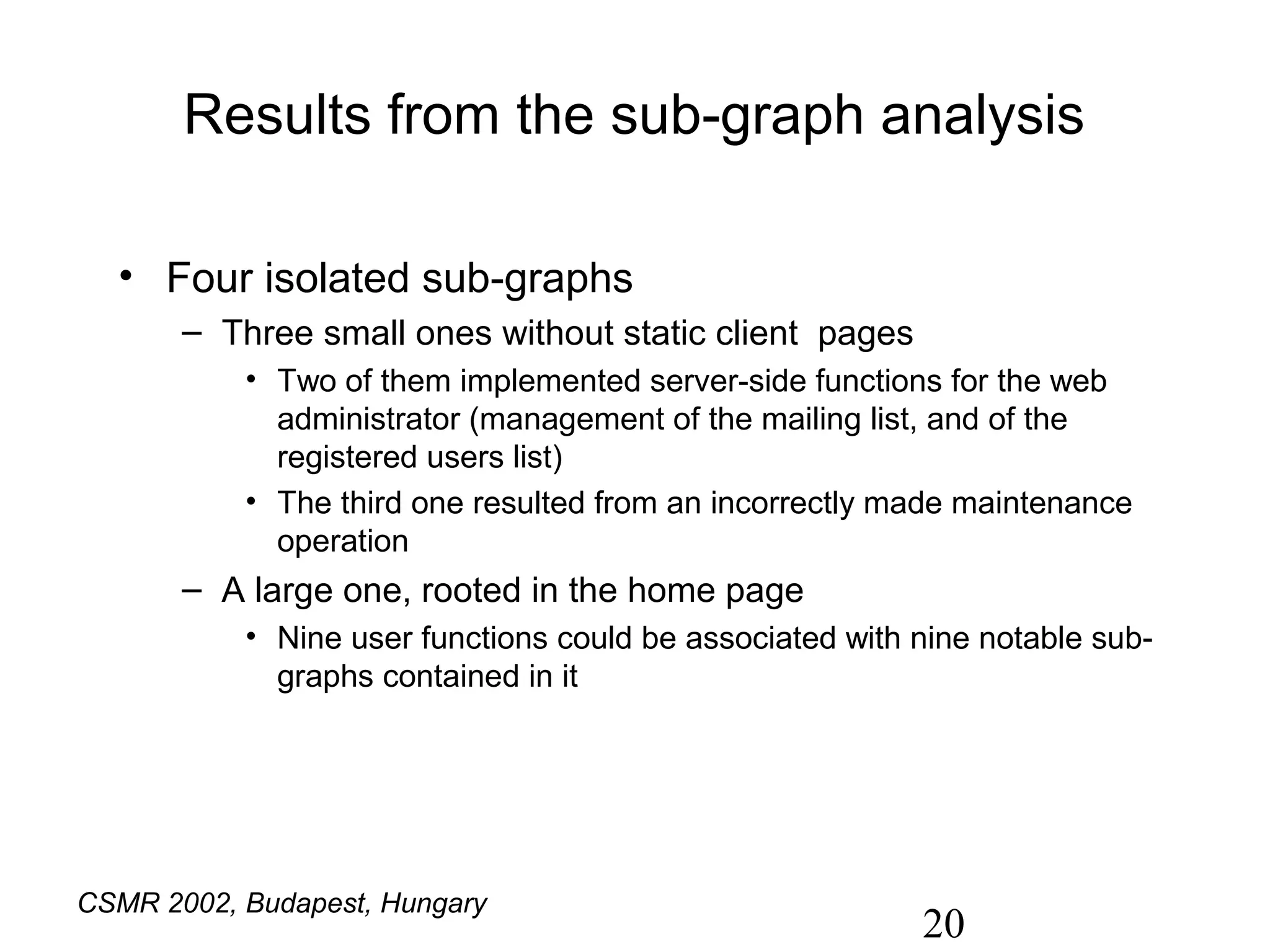
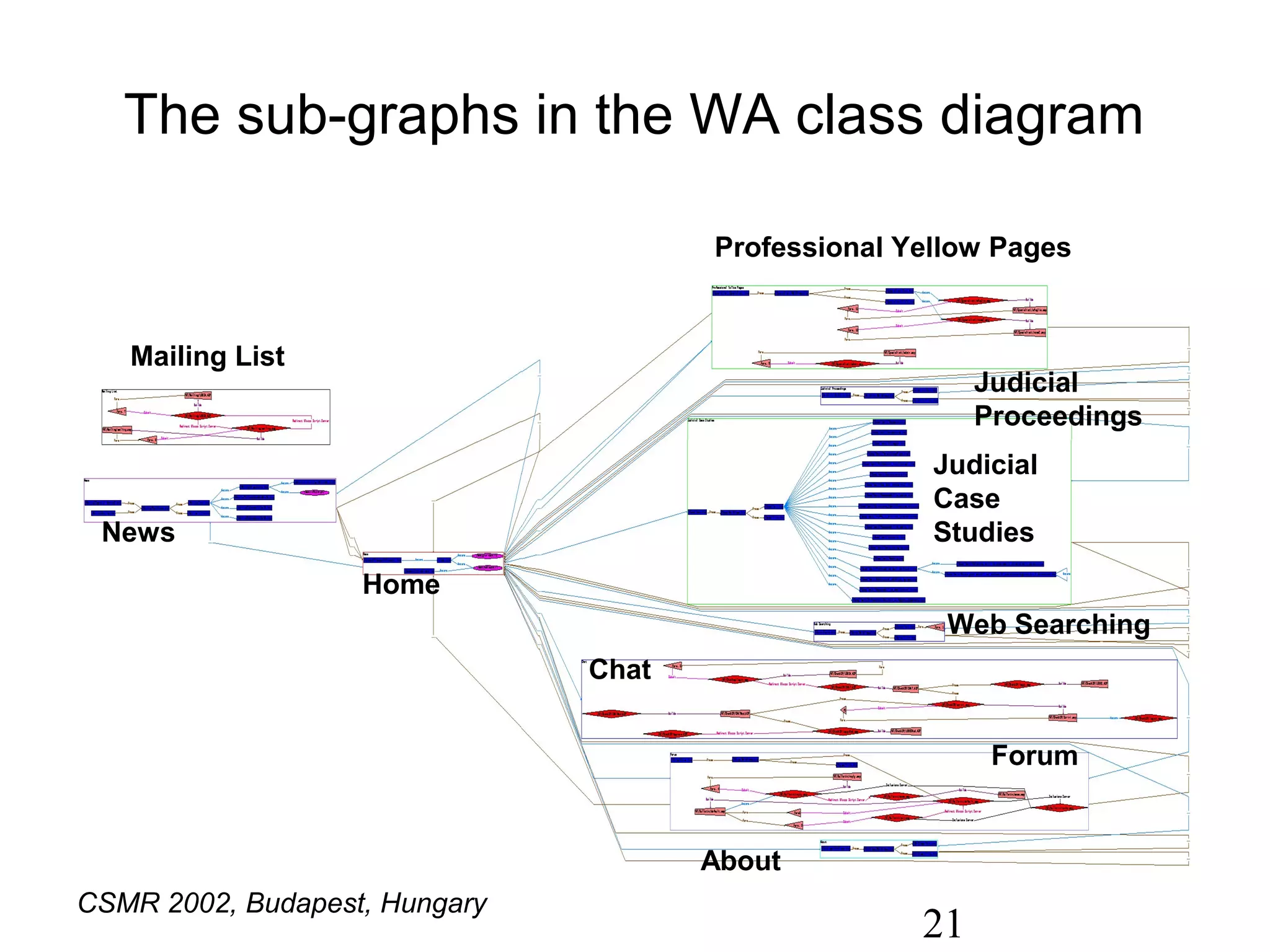
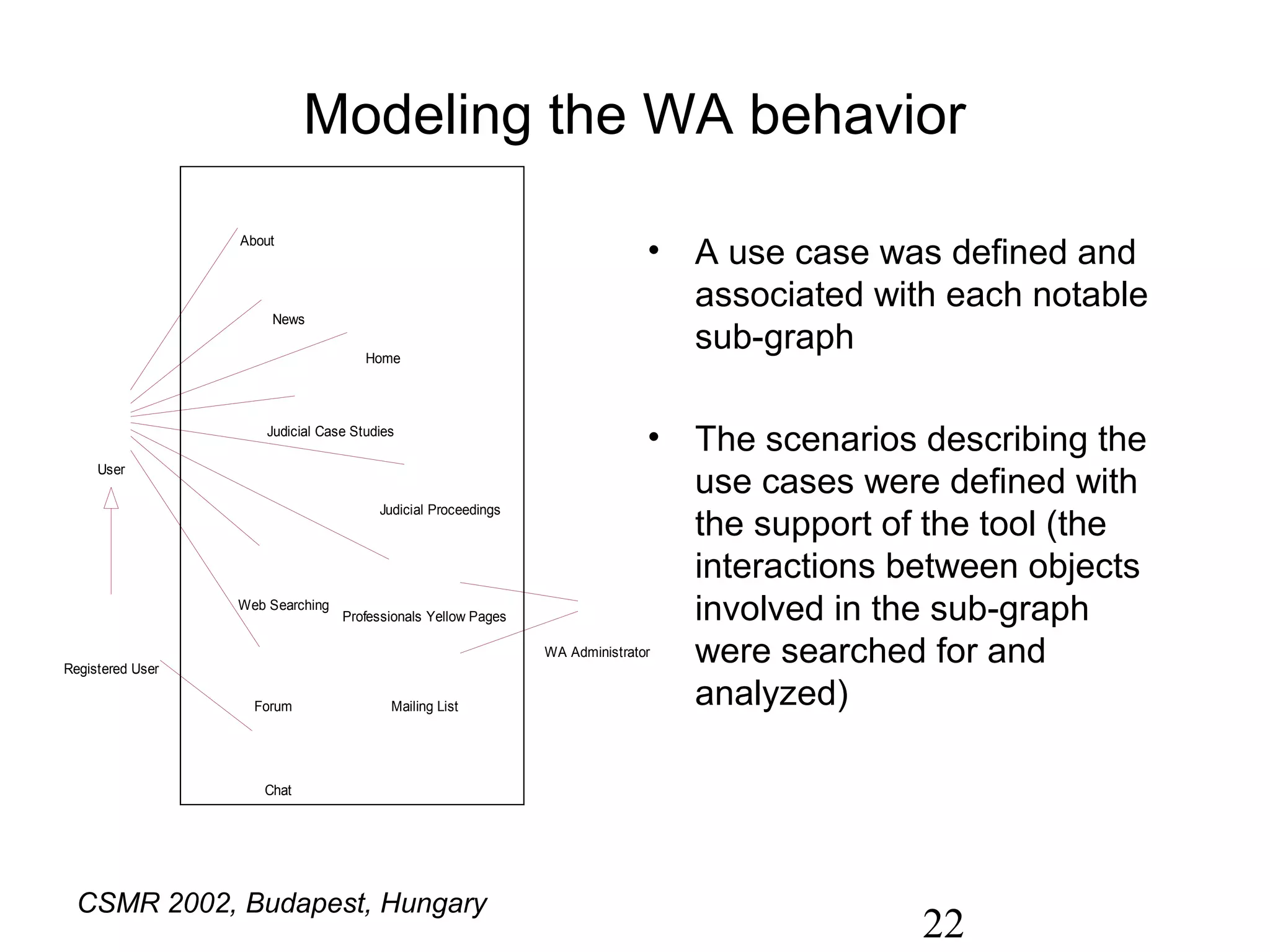
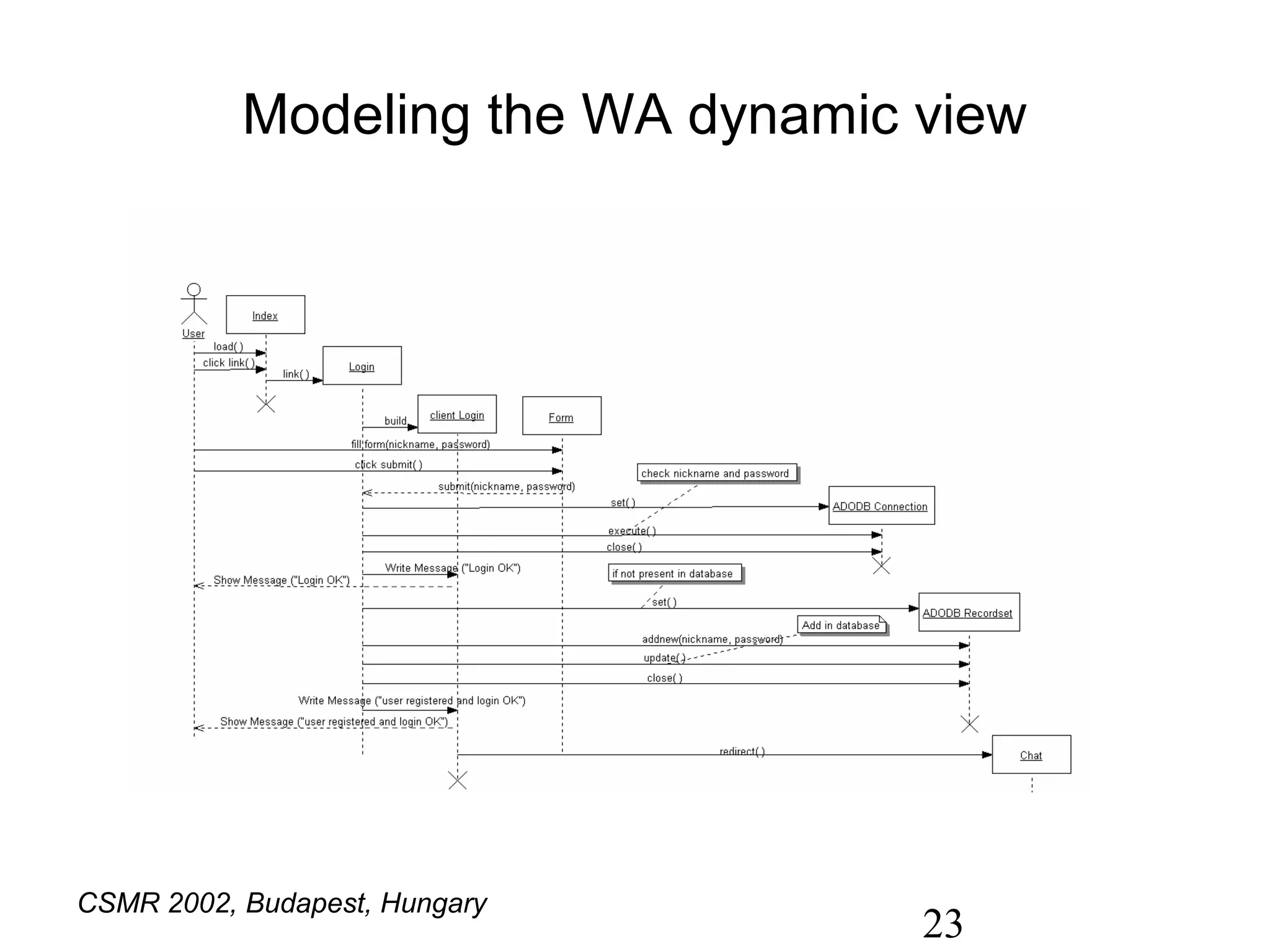
The document discusses 'ware', a reverse engineering tool for web applications which addresses challenges in understanding, maintaining, and evolving dynamic web applications due to their complexity and the variety of technologies used. It details the reverse engineering process, including static and dynamic analysis, and describes the tool's components designed for parsing source code, generating UML diagrams, and supporting user interactions with the application components. The experiments conducted demonstrate the tool's effectiveness in aiding the maintenance of undocumented web applications by automatically producing various UML representations and providing insights into system behavior.