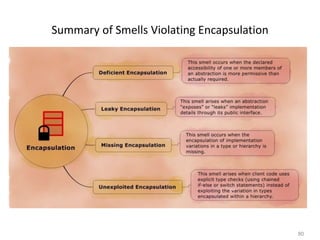
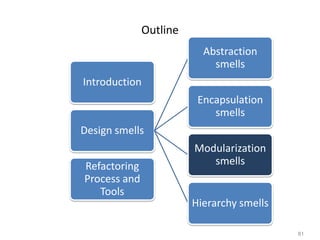
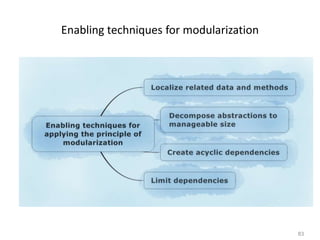
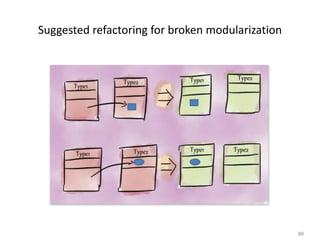
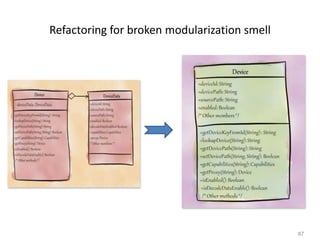
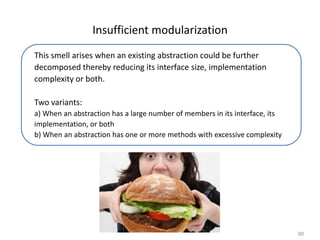
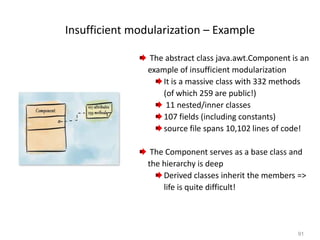
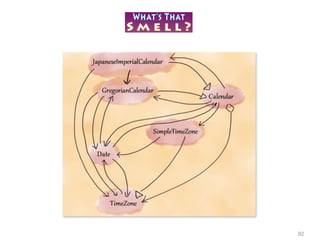
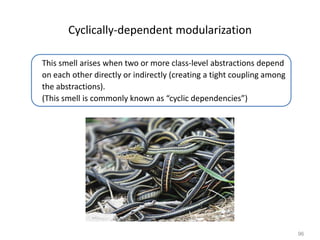
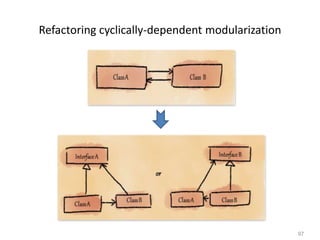
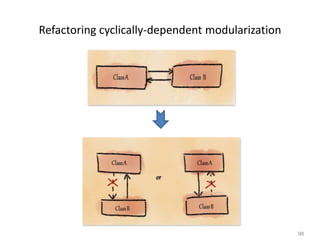
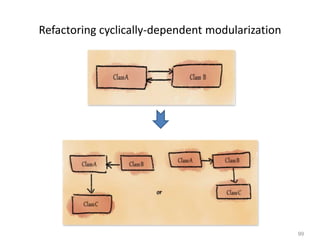
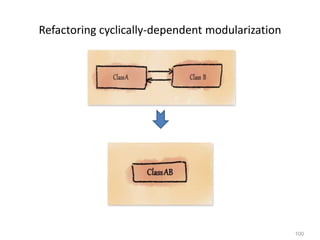
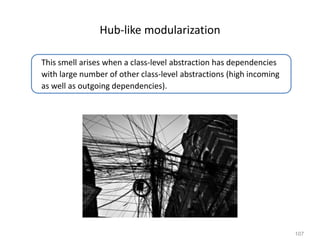
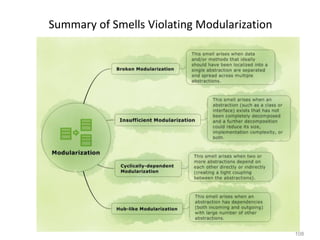
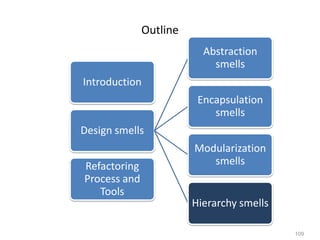
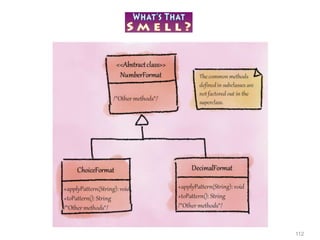
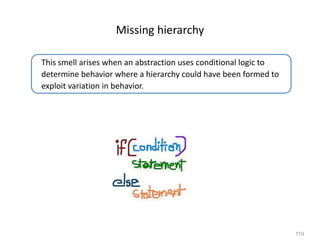
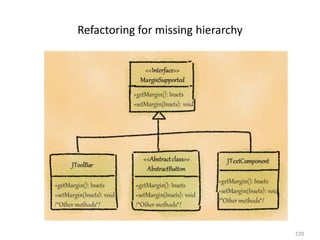
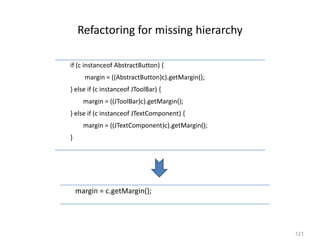
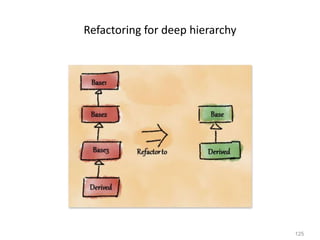
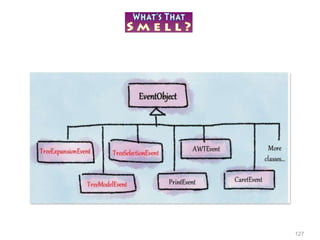
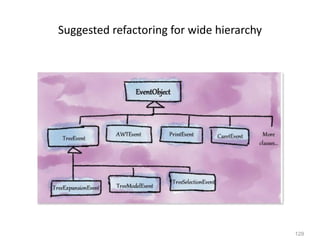
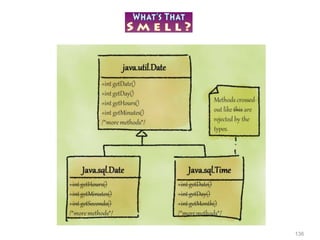
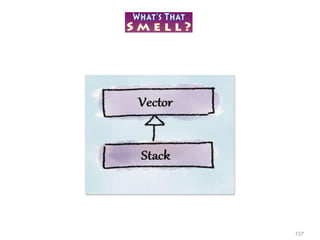
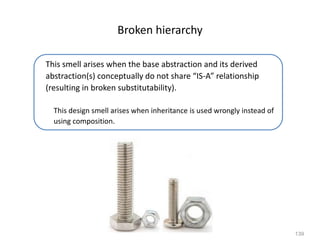
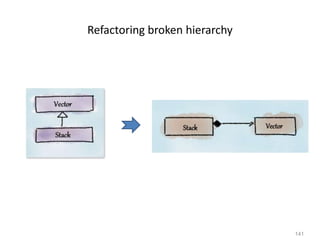
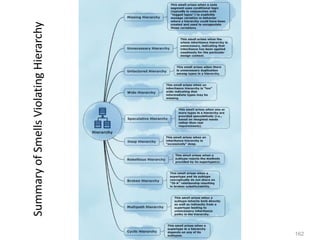
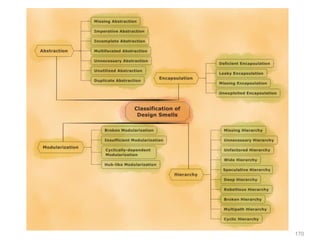
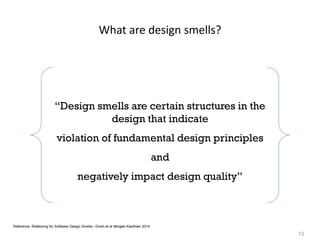
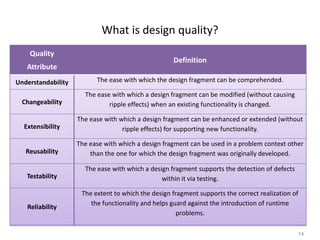
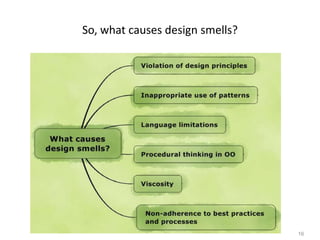
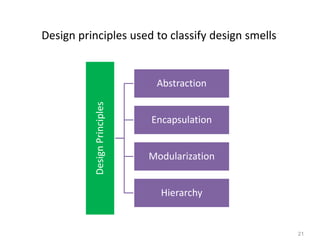
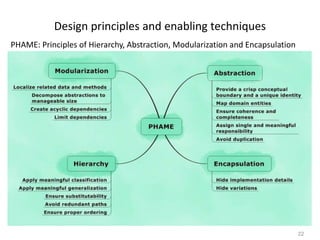
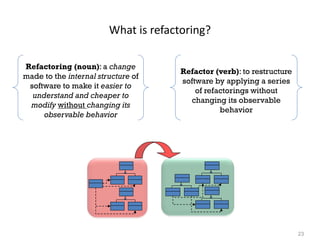
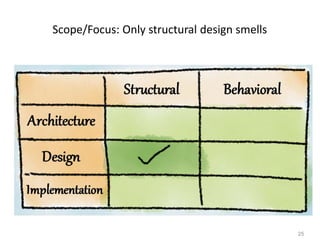
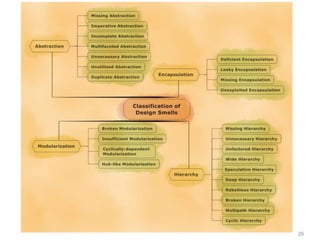
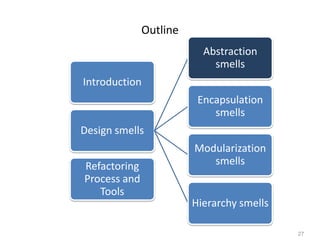
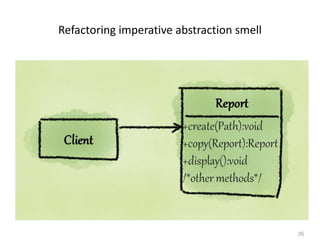
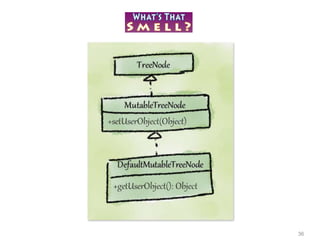
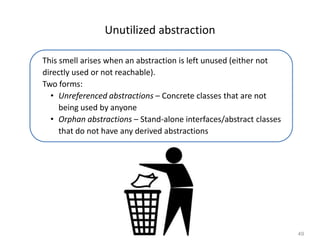
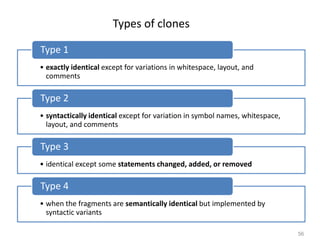
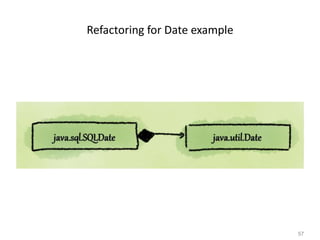
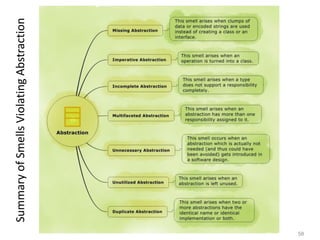
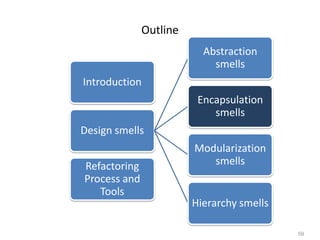
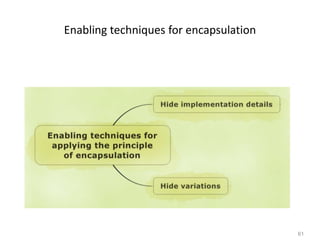
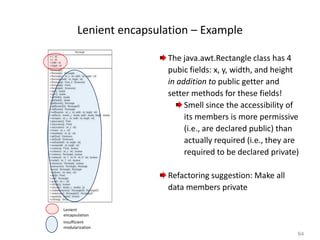
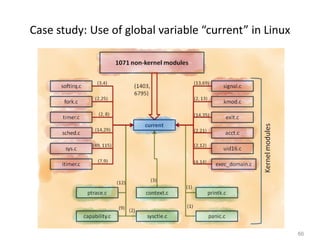
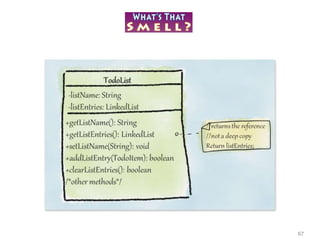
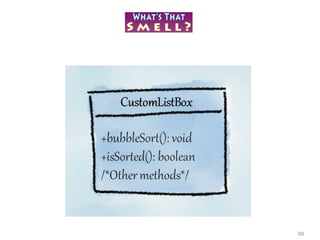
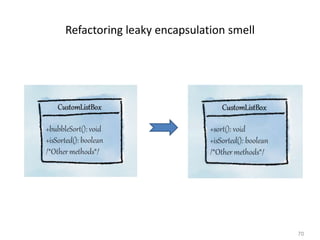
The document discusses various design smells that negatively impact software quality attributes like reusability, changeability, understandability and extensibility. It covers different categories of design smells including abstraction smells, encapsulation smells and modularization smells. Some examples of specific smells discussed are missing abstraction, leaky encapsulation, broken modularization etc. The document emphasizes the importance of addressing design smells through refactoring to improve design quality and reduce technical debt.


![32
Refactoring for missing abstraction smell
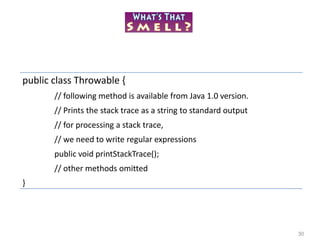
public class Throwable {
// following method is available from Java 1.0 version.
// Prints the stack trace as a string to standard output
// for processing a stack trace,
// we need to write regular expressions
public void printStackTrace();
// other methods omitted
}
public class Throwable {
public void printStackTrace();
public StackTraceElement[] getStackTrace(); // Since 1.4
// other methods omitted
}
public final class StackTraceElement {
public String getFileName();
public int getLineNumber();
public String getClassName();
public String getMethodName();
public boolean isNativeMethod();
}](https://image.slidesharecdn.com/refactoring-ieeecsblrchapter-workshop-150629063555-lva1-app6891/85/Refactoring-for-Software-Design-Smells-1-day-Workshop-32-320.jpg)

![77
switch (transferType) {
case DataBuffer.TYPE_BYTE:
byte bdata[] = (byte[])inData;
pixel = bdata[0] & 0xff;
length = bdata.length;
break;
case DataBuffer.TYPE_USHORT:
short sdata[] = (short[])inData;
pixel = sdata[0] & 0xffff;
length = sdata.length;
break;
case DataBuffer.TYPE_INT:
int idata[] = (int[])inData;
pixel = idata[0];
length = idata.length;
break;
default:
throw new UnsupportedOperationException("This method has not been "+ "implemented
for transferType " + transferType);
}](https://image.slidesharecdn.com/refactoring-ieeecsblrchapter-workshop-150629063555-lva1-app6891/85/Refactoring-for-Software-Design-Smells-1-day-Workshop-77-320.jpg)
![79
Refactoring unexploited encapsulation smell
protected int transferType; protected DataBuffer dataBuffer;
pixel = dataBuffer.getPixel();
length = dataBuffer.getSize();
switch (transferType) {
case DataBuffer.TYPE_BYTE:
byte bdata[] = (byte[])inData;
pixel = bdata[0] & 0xff;
length = bdata.length;
break;
case DataBuffer.TYPE_USHORT:
short sdata[] = (short[])inData;
pixel = sdata[0] & 0xffff;
length = sdata.length;
break;
case DataBuffer.TYPE_INT:
int idata[] = (int[])inData;
pixel = idata[0];
length = idata.length;
break;
default:
throw new UnsupportedOperationException("This method
has not been "+ "implemented for transferType " +
transferType);
}](https://image.slidesharecdn.com/refactoring-ieeecsblrchapter-workshop-150629063555-lva1-app6891/85/Refactoring-for-Software-Design-Smells-1-day-Workshop-79-320.jpg)