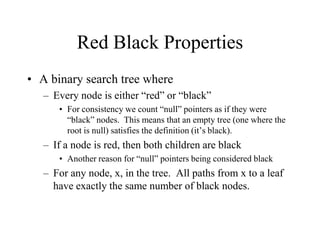
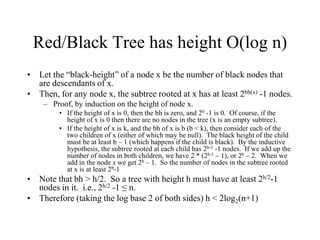
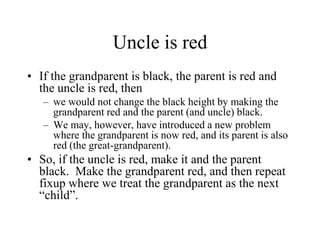
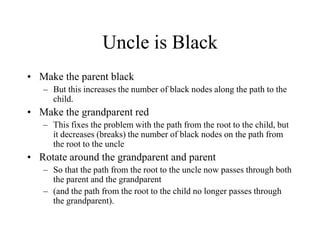
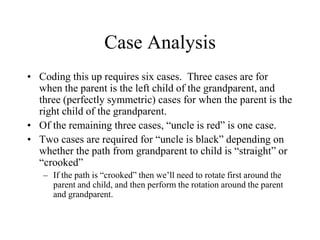
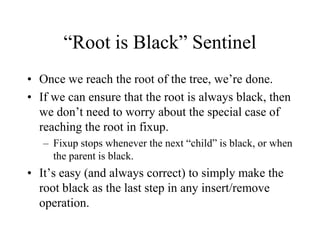
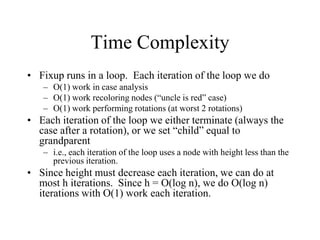
This document discusses red-black trees, which are self-balancing binary search trees. It explains that red-black trees ensure a height of O(log n) through properties such as every node being red or black, paths from any node to leaves having the same number of black nodes, and rotations being used to fix violations after insertions or removals. The document analyzes the time complexity of insertions in red-black trees, showing that rebalancing after each insertion takes O(log n) time through a series of case analyses and rotations.