Pre-Cal 40S Slides April 25, 2007
•
1 like•477 views
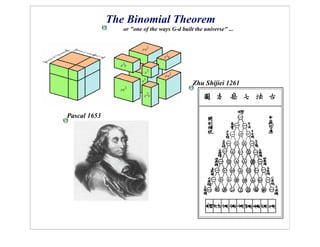
The document discusses Pascal's triangle and the binomial theorem. It notes that Zhu Shijiei first wrote about the binomial theorem in 1261 and that Pascal expanded on it in 1653 by adding more rows to the triangle. The document then lists five patterns that can be found in Pascal's triangle and the binomial theorem, such as the coefficient of each term and the exponents of a and b relating to the overall exponent n.
Report
Share
Report
Share
Download to read offline
Recommended
Recommended
Difference of Two Squares

A powerpoint presentation on Difference of two squares based on DEPED Module Standard
Inverse Trigonometry QA 5

JEE Mathematics/ Lakshmikanta Satapathy/ Inverse Trigonometry QA part 5/ Question on sin inverse cosine inverse and tan inverse solved with the related concepts
Factoring the difference of two squares

A powerpoint presentation of factoring difference of two squares
Factoring Reviewed

Factoring for non-math lovers. This slide presentation is designed to help remove some of the stress out of factoring at t he Algebra 2 level.
Factoring difference of two squares

This shows not only the topic but also a review on some concept and exercises to master the concept.
Factoring the difference of two squares

A powerpoint presentation of factoring the difference of two squares with Math Quiz Show as the motivation
More Related Content
What's hot
Difference of Two Squares

A powerpoint presentation on Difference of two squares based on DEPED Module Standard
Inverse Trigonometry QA 5

JEE Mathematics/ Lakshmikanta Satapathy/ Inverse Trigonometry QA part 5/ Question on sin inverse cosine inverse and tan inverse solved with the related concepts
Factoring the difference of two squares

A powerpoint presentation of factoring difference of two squares
Factoring Reviewed

Factoring for non-math lovers. This slide presentation is designed to help remove some of the stress out of factoring at t he Algebra 2 level.
Factoring difference of two squares

This shows not only the topic but also a review on some concept and exercises to master the concept.
Factoring the difference of two squares

A powerpoint presentation of factoring the difference of two squares with Math Quiz Show as the motivation
What's hot (20)
Pythagorean theorem and distance formal power point

Pythagorean theorem and distance formal power point
Viewers also liked
Diario de una elaboración

Esquema del proceso de elaboración de los alumnos de estudiaenologia.com utilizado para el blog"diario de una elaboración"
The Policy, Planning and Pragmatic Reasons

The Policy, Planning and Pragmatic Reasons for the Massachusetts Move into OpenDocument
Viewers also liked (20)
Similar to Pre-Cal 40S Slides April 25, 2007
Pre-Cal 40S May 11, 2009

Pascal's Triangle, the Fibonacci sequence, The Golden Ratio, The Binomial Theorem.
Patterns in numbers

Stress your brain to search the innumerable patterns hidden in numbers which we usually overlook in Maths.From Sierpinski Triangle to Pandiagonal Magic Square, Fibonnaci Numbers to Hockey Stick Pattern.Explore how they are used in daily life, in espionage.....?? technology and glare at the inventories.
THE BINOMIAL THEOREM 

THE BINOMIAL THEOREM shows how to calculate a power of a binomial –
(x+ y)n -- without actually multiplying out.
For example, if we actually multiplied out the 4th power of (x + y) --
(x + y)4 = (x + y) (x + y) (x + y) (x + y)
-- then on collecting like terms we would find:
(x + y)4 = x4 + 4x3y + 6x2y2 + 4xy3 + y4 . . . . . (1)
1 Assignment #2 MAC 1140 – Spring 2020 – Due Apr.docx

1
Assignment #2
MAC 1140 – Spring 2020 – Due: April 7, 2020
1. We are given the polynomial 𝑓(𝑥) = 𝑥7 − 𝑥6 − 11𝑥5 + 11𝑥4 + 19𝑥3 − 19𝑥2 − 9𝑥 + 9.
(a) What is the degree of this polynomial? How many zeros does it have? Do these zeros have
to be real and/or distinct?
(b) What is the behavior of the polynomial as 𝑥 → +∞ and 𝑥 → −∞? Explain your answer.
(c) Describe, in your own words, the rational zero theorem. Taking into account the form of the
polynomial, can we use the rational zero theorem to find if the polynomial has rational
zeros? If yes, what are the possible zeros?
(d) Describe in your own words Descartes’ rule of signs. Using this rule, what is the possible
number of positive zeros of the polynomial, and what is the possible number of negative
zeros?
(e) Calculate the following values:
𝑓(−3) = ________ 𝑓(−2) = ________ 𝑓(−1) = ________ 𝑓(0) = ________
𝑓(1) = ________ 𝑓(2) = ________ 𝑓(3) = ________
𝑓(−4) = ________ 𝑓(4) = ________
2
(f) Describe in your own words the Factor Theorem. Using this theorem show that 𝑓(𝑥) =
(𝑥 + 3)(𝑥 + 1)(𝑥 − 1)(𝑥 − 3) ⋅ 𝑔(𝑥).
(g) Using long division, find 𝑔(𝑥). Show all your work.
(h) Calculate the following values:
𝑔(−1) = ________ 𝑔(1) = ________
(i) Using the Factor Theorem and synthetic division, factor 𝑔(𝑥). Show all your work.
(j) Describe the multiplicity of all the zeros of 𝑓(𝑥), and describe the behavior of the graph of
𝑓(𝑥) at these zeros (i.e., is the graph crossing the 𝑥-axis at these zeros or touches and turns
around?).
3
(k) What is the maximum number of turning points of 𝑓(𝑥)?
(l) Graph 𝑓(𝑥).
4
2. We are given the polynomial 𝑓(𝑥) = 4𝑥5 + 4𝑥4 + 𝑥3 − 2𝑥2 − 2𝑥 + 1.
(a) What is the degree of this polynomial? How many zeros does it have? Do these zeros have
to be real and/or distinct?
(b) What is the behavior of the polynomial as 𝑥 → +∞ and 𝑥 → −∞? Explain your answer.
(c) Describe, in your own words, the rational zero theorem. Taking into account the form of the
polynomial, can we use the rational zero theorem to find if the polynomial has rational
zeros? If yes, what are the possible zeros?
(d) Describe in your own words Descartes’ rule of signs. Using this rule, what is the possible
number of positive zeros of the polynomial, and what is the possible number of negative
zeros?
(e) Calculate the following values:
𝑓(−2) = ________ 𝑓(−1) = ________ 𝑓(0) = ________
𝑓(1) = ________ 𝑓(2) = ________
(f) Describe in your own words the Intermediate Value Theorem. Based on the results in (e)
above, and the possible rational zeros described in (c), show that 𝑥 −
1
2
is a factor of 𝑓(𝑥).
Clearly describe your reasoning.
5
(g) Describe in your own words the Factor Theorem. Using this theorem show that 𝑓(𝑥) =
(𝑥 + 1)(2𝑥 − 1) ⋅ 𝑔(𝑥
Similar to Pre-Cal 40S Slides April 25, 2007 (20)
1 Assignment #2 MAC 1140 – Spring 2020 – Due Apr.docx

1 Assignment #2 MAC 1140 – Spring 2020 – Due Apr.docx
More from Darren Kuropatwa
Behind Their Eyes v1

Behind Their Eyes - making thinking visible is not enough
Walk into any classroom and watch the breakneck pace at which teachers are working hard to help students learn. Mind you, if we don’t uncover what students are thinking while learning, they may be running down the wrong path. OK, so we need ways to make student thinking visible. Seeing their thinking is important, but we also need to create the time and space for teachers to absorb, reflect, and act on what their students thinking reveals. This workshop shares strategies both for making student thinking visible and for creating time and space for teachers to meaningfully act on what they learn about what’s going on behind their eyes.
Leading Change v1

“If you really want to understand something, try changing it.” - Kurt Lewin
As the Director of Learning for a school division made up of 18 schools, my job is to help lead the largest change initiative ever undertaken in our school community. One of the most important, difficult, messy things any school leader does is lead change. While we can learn from the change leadership of others, copying their work most often leads to failure. Success is more likely to come from adapting others work to our own context. In this workshop I share the journey we’ve undertaken collectively in our schools; how we developed a shared vision, cultivated collaborative cultures, maintained a focus on deep learning, and wrestle with the nuances of accountability. Informed by the latest research on change management in education, we also model strategies for fostering deep learning conversations in your schools. We’ll engage in some deeper learning conversations together and take back a wealth of ideas you can adapt to your own context. Developing collaborative cultures is careful and precise work that has profound impact when carried out well. So how do you do that? Come, let’s learn together. Good people are important, but good cultures are moreso.
Providing Permission To Wonder v2.1

In a world where knowledge is more a verb than a noun how do we foster deep learning in our students? Good questions cause thinking. Unfortunately, many of the questions regularly asked in classrooms focus on knowledge as a noun. This presentation will explore inquiry as a pedagogical stance and the effective use of thinking and learning tools in the classroom. We will work together to model teaching practices that lead to students co-constructing a networked (real world) rather than hierarchical (artificial) understanding of their world regardless of grade level or discipline.
Participants will leave this workshop with a toolkit of research based questioning and thinking strategies they can begin using with their students tomorrow.
Things That Suck About Digital Citizenship v1

This participatory session will engage attendees in some meaningful dialogue around several aspects of digital citizenship. We'll explore some hot-button topics and consider their impact on the work we do as educators. This session will provide clarification around a number of key digital citizenship issues and will also highlight a valuable model for engaging your students in classroom conversations. There’s a fair bit of fear mongering disguised as digital citizenship online. Our kids need more models of empathy and empowerment – so do we. We’ll share some of those models too.
Digital Storytelling for Deeper Learning v1

Presented at the Riding the Wave Conference in Gimli, Manitoba. May 2017.
In two words, you remember the whole story: glass slipper, sour grapes, cold porridge. You remember more than facts, you recall relationships & deeper connections between characters. Some of the powerful ways we leverage digital for deeper learning includes challenging sources of information (fake news), exploring bias (developing empathy through multiple perspectives), and creating powerful feedback loops that foster deeper learning.
Powerful narratives, in a word or two, bring to mind a wealth of ideas & relationships; more than just facts. How can we find stories that make our teaching sticky and help kids find, and more importantly tell, stories that make learning stick? This workshop will equip teachers with the skills & knowledge to foster deeper learning across the curriculum by intentionally leveraging digital tools to foster deeper learning.
Tales of Learning and the Gifts of Footprints v4.2

Presented at the Richmond District Conference, Feb 2017.
Why does digital learning matter? In a society that is increasingly technophilic what are the new literacies we need to be aware of for our own learning and that of our students? How does this impact the way we think about and teach our children to become empowered and empathetic responsible citizens? Answers to these questions and more are shared through a series of powerful tales of learning.
The Fourth Screen v4.2

Presented at the Richmond District Conference, Feb 2017.
A series of stories woven together to start a conversation with middle and high school students, teachers, and parents about living our lives on and offline (on The Fourth Screen) more thoughtfully.
This talk focuses primarily on the ideas of Empathy, Empowerment & Persistent Kindness and shares resources teachers can use to lead these sorts of conversations with their own students.
Making Student Thinking Visible v4

Slides to support a master class on making student thinking visible through practical hands-on activities and structured around Dylan Wiliam's work on formative assessment and active learning. Held at the BYTE Conference 2017 in Portage la Prairie, Manitoba.
Learning is at BYTE 2017

A group of educators from the BYTE Conference 2017 (Build Your Teaching Experience) share their ideas about learning as a series of visual metaphors they found on their phones.
Leveraging Digital for Deeper Learning

Slides to support a Keynote presentation to Early Years and Middle Years teachers in Hanover School Division on 3 February 2017.
We Learn Through Stories at PRIZMAH17

Slides to support a master class at the PRIZMAH Conference in Chicago, IL. 5 Feb 2017.
How can we make learning sticky using powerful storytelling frameworks that tap into peoples' emotions? How do we involve all students in creating digital content that doesn't also create hours of content for teachers to assess? This interactive session will showcase Digital Storytelling activities teachers can use in class tomorrow! Document student learning & foster reflective ways for students to share their learning. 1st: we play! Then we'll discuss how to practically adapt these ideas, make them your own, and figure out what sort of infrastructure needs to be in place to support these kinds of powerful learning experiences. We’ll learn how to exercise your students' & your own creativity muscles and share simple strategies for collecting & publishing student work.
Providing Permission to Wonder v3

In a world where knowledge is more a verb than a noun how do we foster deep learning in our students? Good questions cause thinking. Unfortunately, many of the questions regularly asked in classrooms focus on knowledge as a noun. This presentation will explore the effective use of thinking and learning tools in the classroom. We will work together to model teaching practices that lead to students co-constructing a networked (real world) rather than hierarchical (artificial) understanding of their world regardless of grade level or discipline.
Participants leave this workshop with a toolkit of research based questioning and thinking strategies they can begin using with their students tomorrow.
The Fourth Screen v4.1

A series of stories woven together to start a conversation with middle and high school students about living our lives on and offline (on The Fourth Screen) more thoughtfully.
This talk focuses primarily on the ideas of Empathy, Empowerment & Persistent Kindness and shares resources teachers can use to lead these sorts of conversations with their own students.
Making Student Thinking Visible v3.7

Slides to support a master class on making student thinking visible through practical hands-on activities and structured around Dylan Wiliam's work on formative assessment and active learning.
Learning is at AUHSD

A group of educators from the Anderson Union High School & Redding School Districts and share their ideas about learning as a series of visual metaphors.
Providing Permission to Wonder v2

In a world where knowledge is more a verb than a noun how do we foster deep learning in our students? Good questions cause thinking. Unfortunately, many of the questions regularly asked in classrooms focus on knowledge as a noun. This presentation will explore the effective use of thinking and learning tools in the classroom. We will work together to model teaching practices that lead to students co-constructing a networked (real world) rather than hierarchical (artificial) understanding of their world regardless of grade level or discipline.
Participants leave this workshop with a toolkit of research based questioning and thinking strategies they can begin using with their students tomorrow.
The Fourth Screen v4

A series of stories woven together to start a conversation with middle and high school students about living our lives on and offline (on The Fourth Screen) more thoughtfully.
This talk focuses primarily on the ideas of Empathy, Empowerment & Persistent Kindness and shares resources teachers can use to lead these sorts of conversations with their own students.
Learning is at BLC16

A group of educators at the Building Learning Communities Conference share their ideas about learning as a series of visual metaphors.
We Learn Through Stories v4 (master class)

Slides to support a master class at the Building Learning Communities Conference in Boston, MA. 18 July 2016.
How can we make learning sticky using powerful storytelling frameworks that tap into peoples' emotions? How do we involve all students in creating digital content that doesn't also create hours of content for teachers to assess? This interactive session will showcase Digital Storytelling activities teachers can use in class tomorrow! Document student learning & foster reflective ways for students to share their learning. 1st: we play! Then we'll discuss how to practically adapt these ideas, make them your own, and figure out what sort of infrastructure needs to be in place to support these kinds of powerful learning experiences. We’ll learn how to exercise your students' & your own creativity muscles and share simple strategies for collecting & publishing student work.
Deep Learning Design: the middle ring

Slides in support of a professional learning day for administrators in Hanover School Division focused on developing a common language & understanding of Deep Learning Design.
More from Darren Kuropatwa (20)
Tales of Learning and the Gifts of Footprints v4.2

Tales of Learning and the Gifts of Footprints v4.2
Recently uploaded
Accelerate your Kubernetes clusters with Varnish Caching

A presentation about the usage and availability of Varnish on Kubernetes. This talk explores the capabilities of Varnish caching and shows how to use the Varnish Helm chart to deploy it to Kubernetes.
This presentation was delivered at K8SUG Singapore. See https://feryn.eu/presentations/accelerate-your-kubernetes-clusters-with-varnish-caching-k8sug-singapore-28-2024 for more details.
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, Product School
Bits & Pixels using AI for Good.........

A whirlwind tour of tech & AI for socio-environmental impact.
UiPath Test Automation using UiPath Test Suite series, part 3

Welcome to UiPath Test Automation using UiPath Test Suite series part 3. In this session, we will cover desktop automation along with UI automation.
Topics covered:
UI automation Introduction,
UI automation Sample
Desktop automation flow
Pradeep Chinnala, Senior Consultant Automation Developer @WonderBotz and UiPath MVP
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head of Product, Amazon Games
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scalable Platform by VP of Product, The New York Times
To Graph or Not to Graph Knowledge Graph Architectures and LLMs

Reflecting on new architectures for knowledge based systems in light of generative ai
Elevating Tactical DDD Patterns Through Object Calisthenics

After immersing yourself in the blue book and its red counterpart, attending DDD-focused conferences, and applying tactical patterns, you're left with a crucial question: How do I ensure my design is effective? Tactical patterns within Domain-Driven Design (DDD) serve as guiding principles for creating clear and manageable domain models. However, achieving success with these patterns requires additional guidance. Interestingly, we've observed that a set of constraints initially designed for training purposes remarkably aligns with effective pattern implementation, offering a more ‘mechanical’ approach. Let's explore together how Object Calisthenics can elevate the design of your tactical DDD patterns, offering concrete help for those venturing into DDD for the first time!
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Presented by Suzanne Phillips and Alex Marcotte
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

The IoT and OT threat landscape report has been prepared by the Threat Research Team at Sectrio using data from Sectrio, cyber threat intelligence farming facilities spread across over 85 cities around the world. In addition, Sectrio also runs AI-based advanced threat and payload engagement facilities that serve as sinks to attract and engage sophisticated threat actors, and newer malware including new variants and latent threats that are at an earlier stage of development.
The latest edition of the OT/ICS and IoT security Threat Landscape Report 2024 also covers:
State of global ICS asset and network exposure
Sectoral targets and attacks as well as the cost of ransom
Global APT activity, AI usage, actor and tactic profiles, and implications
Rise in volumes of AI-powered cyberattacks
Major cyber events in 2024
Malware and malicious payload trends
Cyberattack types and targets
Vulnerability exploit attempts on CVEs
Attacks on counties – USA
Expansion of bot farms – how, where, and why
In-depth analysis of the cyber threat landscape across North America, South America, Europe, APAC, and the Middle East
Why are attacks on smart factories rising?
Cyber risk predictions
Axis of attacks – Europe
Systemic attacks in the Middle East
Download the full report from here:
https://sectrio.com/resources/ot-threat-landscape-reports/sectrio-releases-ot-ics-and-iot-security-threat-landscape-report-2024/
DevOps and Testing slides at DASA Connect

My and Rik Marselis slides at 30.5.2024 DASA Connect conference. We discuss about what is testing, then what is agile testing and finally what is Testing in DevOps. Finally we had lovely workshop with the participants trying to find out different ways to think about quality and testing in different parts of the DevOps infinity loop.
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

In this session I delve into the encryption technology used in Microsoft 365 and Microsoft Purview. Including the concepts of Customer Key and Double Key Encryption.
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase Enterprise-Wide Efficiency by VP Data Platform, American Express
Securing your Kubernetes cluster_ a step-by-step guide to success !

Today, after several years of existence, an extremely active community and an ultra-dynamic ecosystem, Kubernetes has established itself as the de facto standard in container orchestration. Thanks to a wide range of managed services, it has never been so easy to set up a ready-to-use Kubernetes cluster.
However, this ease of use means that the subject of security in Kubernetes is often left for later, or even neglected. This exposes companies to significant risks.
In this talk, I'll show you step-by-step how to secure your Kubernetes cluster for greater peace of mind and reliability.
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

91mobiles recently conducted a Smart TV Buyer Insights Survey in which we asked over 3,000 respondents about the TV they own, aspects they look at on a new TV, and their TV buying preferences.
JMeter webinar - integration with InfluxDB and Grafana

Watch this recorded webinar about real-time monitoring of application performance. See how to integrate Apache JMeter, the open-source leader in performance testing, with InfluxDB, the open-source time-series database, and Grafana, the open-source analytics and visualization application.
In this webinar, we will review the benefits of leveraging InfluxDB and Grafana when executing load tests and demonstrate how these tools are used to visualize performance metrics.
Length: 30 minutes
Session Overview
-------------------------------------------
During this webinar, we will cover the following topics while demonstrating the integrations of JMeter, InfluxDB and Grafana:
- What out-of-the-box solutions are available for real-time monitoring JMeter tests?
- What are the benefits of integrating InfluxDB and Grafana into the load testing stack?
- Which features are provided by Grafana?
- Demonstration of InfluxDB and Grafana using a practice web application
To view the webinar recording, go to:
https://www.rttsweb.com/jmeter-integration-webinar
Recently uploaded (20)
Accelerate your Kubernetes clusters with Varnish Caching

Accelerate your Kubernetes clusters with Varnish Caching
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, P...
UiPath Test Automation using UiPath Test Suite series, part 3

UiPath Test Automation using UiPath Test Suite series, part 3
FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf

FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...
To Graph or Not to Graph Knowledge Graph Architectures and LLMs

To Graph or Not to Graph Knowledge Graph Architectures and LLMs
Elevating Tactical DDD Patterns Through Object Calisthenics

Elevating Tactical DDD Patterns Through Object Calisthenics
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Assuring Contact Center Experiences for Your Customers With ThousandEyes
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

State of ICS and IoT Cyber Threat Landscape Report 2024 preview
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

Encryption in Microsoft 365 - ExpertsLive Netherlands 2024
FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf

FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase E...
Securing your Kubernetes cluster_ a step-by-step guide to success !

Securing your Kubernetes cluster_ a step-by-step guide to success !
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf
JMeter webinar - integration with InfluxDB and Grafana

JMeter webinar - integration with InfluxDB and Grafana
Monitoring Java Application Security with JDK Tools and JFR Events

Monitoring Java Application Security with JDK Tools and JFR Events
Pre-Cal 40S Slides April 25, 2007
- 1. The Binomial Theorem or "one of the ways G-d built the universe" ... Zhu Shijiei 1261 Pascal 1653
- 2. Expand and simplify ... a+b
- 3. Find a pattern, add two more rows to the triangle ... 1 1 1 1 2 1 1 3 3 1 1 4 6 4 1
- 4. Evaluate each term ...
- 5. Pascal's Triangle How many different patterns can you find in the triangle? SYMMETRY Counting Numbers Sum of COUNTING numbers triangular numbers Sum of Triangular numbers
- 6. Pascal's Triangle How many different patterns can you find in the triangle?
- 7. Pascal's Triangle How many different patterns can you find in the triangle?
- 9. The Binomial Theorem ... Algebraically Combinatorically Notice the patterns ... (1) The coefficient of the term is: (2) The exponent on a is given by: [n - (i - 1)] (3) The exponent on b is given by: i (4) This relation holds for each term in the expansion: [exponent on a] + [exponent on b] = n (5) The number of terms in any binomial expansion is: n + 1
