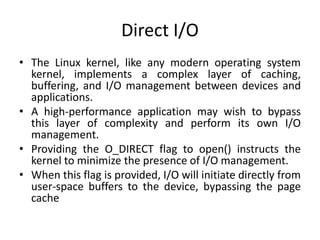
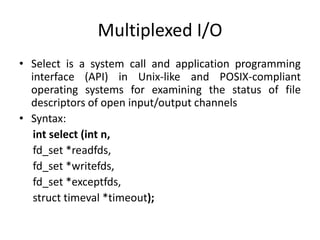
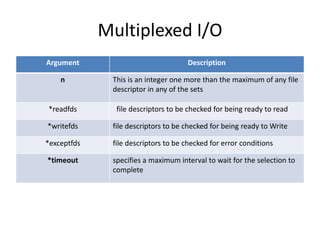
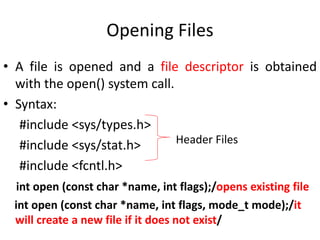
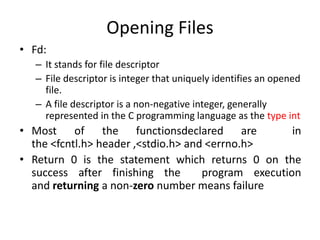
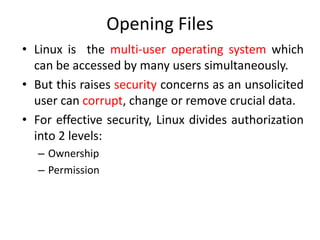
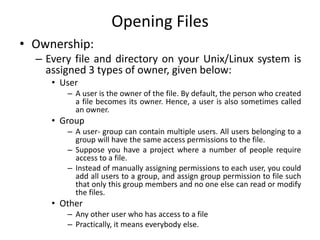
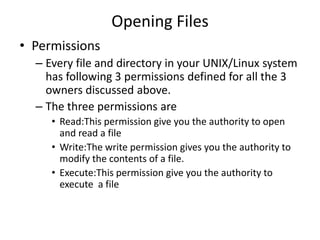
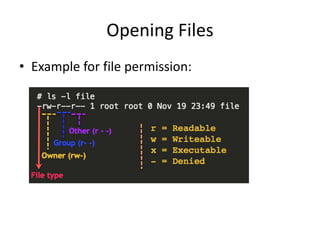
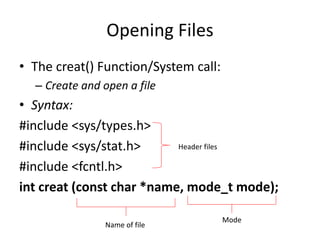
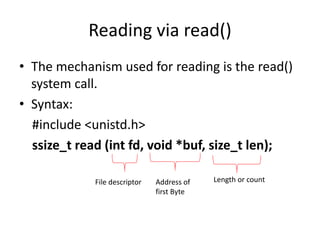
This document discusses various concepts related to file input/output (I/O) in Linux system programming. It covers opening, reading from, writing to, closing, seeking within, and truncating files using system calls like open(), read(), write(), close(), lseek(), ftruncate(). It also discusses related topics like file descriptors, blocking vs non-blocking I/O, synchronized I/O, direct I/O, and positional reads/writes.
![Synchronized I/O
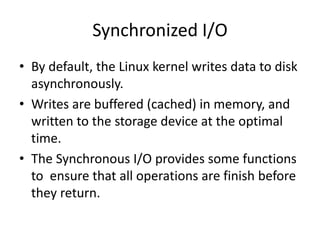
• Sync System call:
– The sync system call forces an immediate write of all
cached data to disk but it doesn’t wait to complete.
– This call initiates the process of committing all buffers
to disk.
• Syntax:
sync [OPTION] [FILE]...
• Examples:
1. sync -d: This option sync only file data not
metadata
2. sync -f: This option will sync the file systems
which contains the files.](https://image.slidesharecdn.com/unit-1-210305200512/85/Linux-System-Programming-File-I-O-31-320.jpg)