Embed presentation
Download to read offline

![TWO TYPES
Ordinary pipes
int pipe(int filedes[2]);
Named pipes](https://image.slidesharecdn.com/pipe-170306141034/85/Pipe-3-320.jpg)

![READER
#include <fcntl.h>
#include <stdio.h>
#include <sys/stat.h>
#include <unistd.h>
#define MAX_BUF 1024
int main()
{
int fd;
char * myfifo = "/tmp/myfifo";
char buf[MAX_BUF];
fd = open(myfifo, O_RDONLY);
read(fd, buf, MAX_BUF);
printf("Received: %sn", buf);
close(fd);
return 0;
}](https://image.slidesharecdn.com/pipe-170306141034/85/Pipe-6-320.jpg)


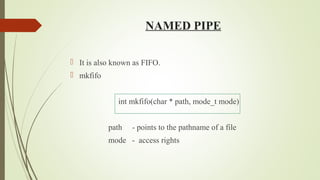
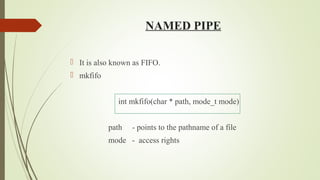
The document discusses two types of pipes in programming: ordinary pipes and named pipes (FIFO). It provides example code for creating a named pipe using mkfifo, as well as examples for writing to and reading from the pipe. The document concludes with a demonstration of the reader output.

![TWO TYPES
Ordinary pipes
int pipe(int filedes[2]);
Named pipes](https://image.slidesharecdn.com/pipe-170306141034/85/Pipe-3-320.jpg)

![READER
#include <fcntl.h>
#include <stdio.h>
#include <sys/stat.h>
#include <unistd.h>
#define MAX_BUF 1024
int main()
{
int fd;
char * myfifo = "/tmp/myfifo";
char buf[MAX_BUF];
fd = open(myfifo, O_RDONLY);
read(fd, buf, MAX_BUF);
printf("Received: %sn", buf);
close(fd);
return 0;
}](https://image.slidesharecdn.com/pipe-170306141034/85/Pipe-6-320.jpg)
