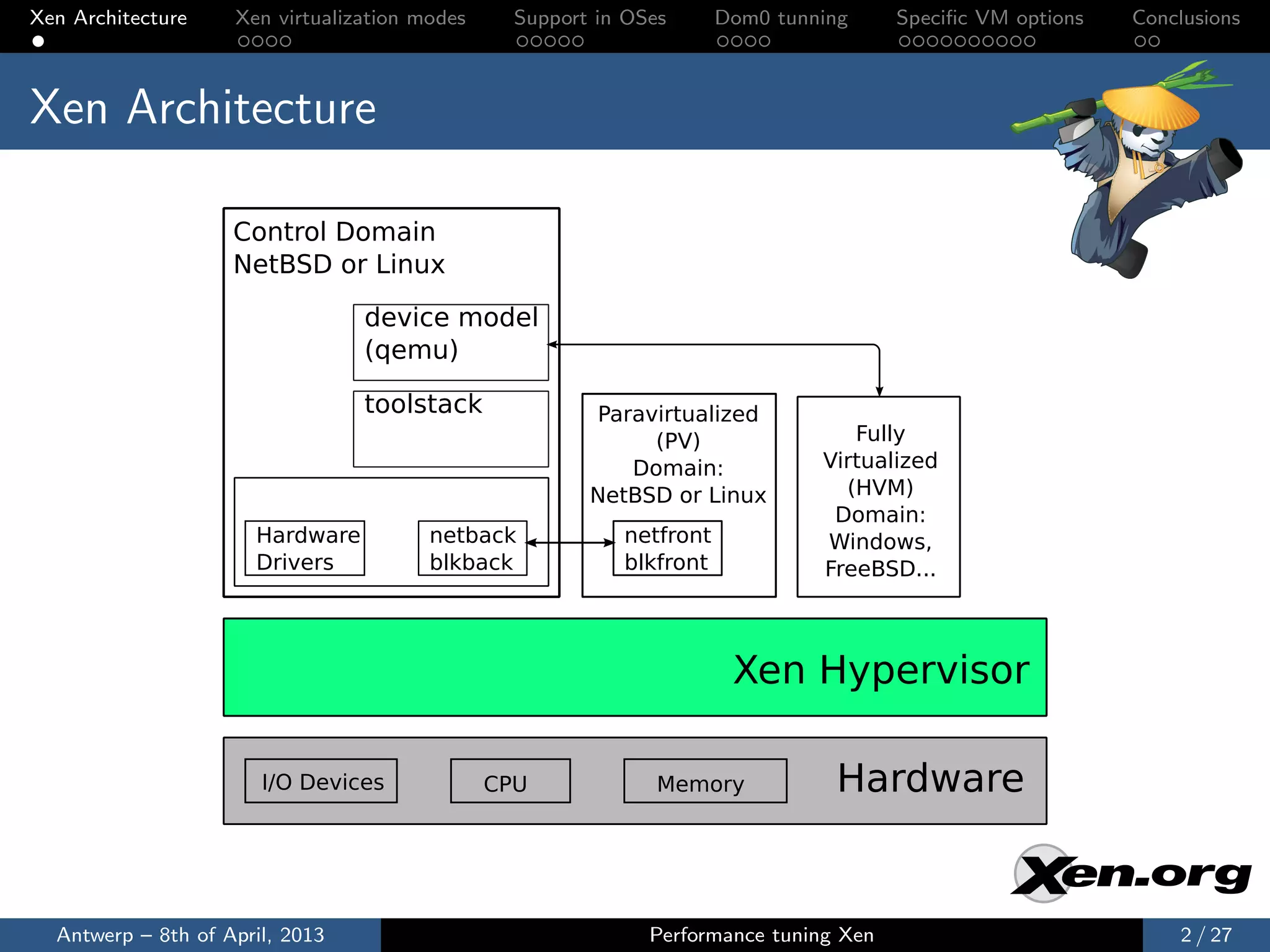
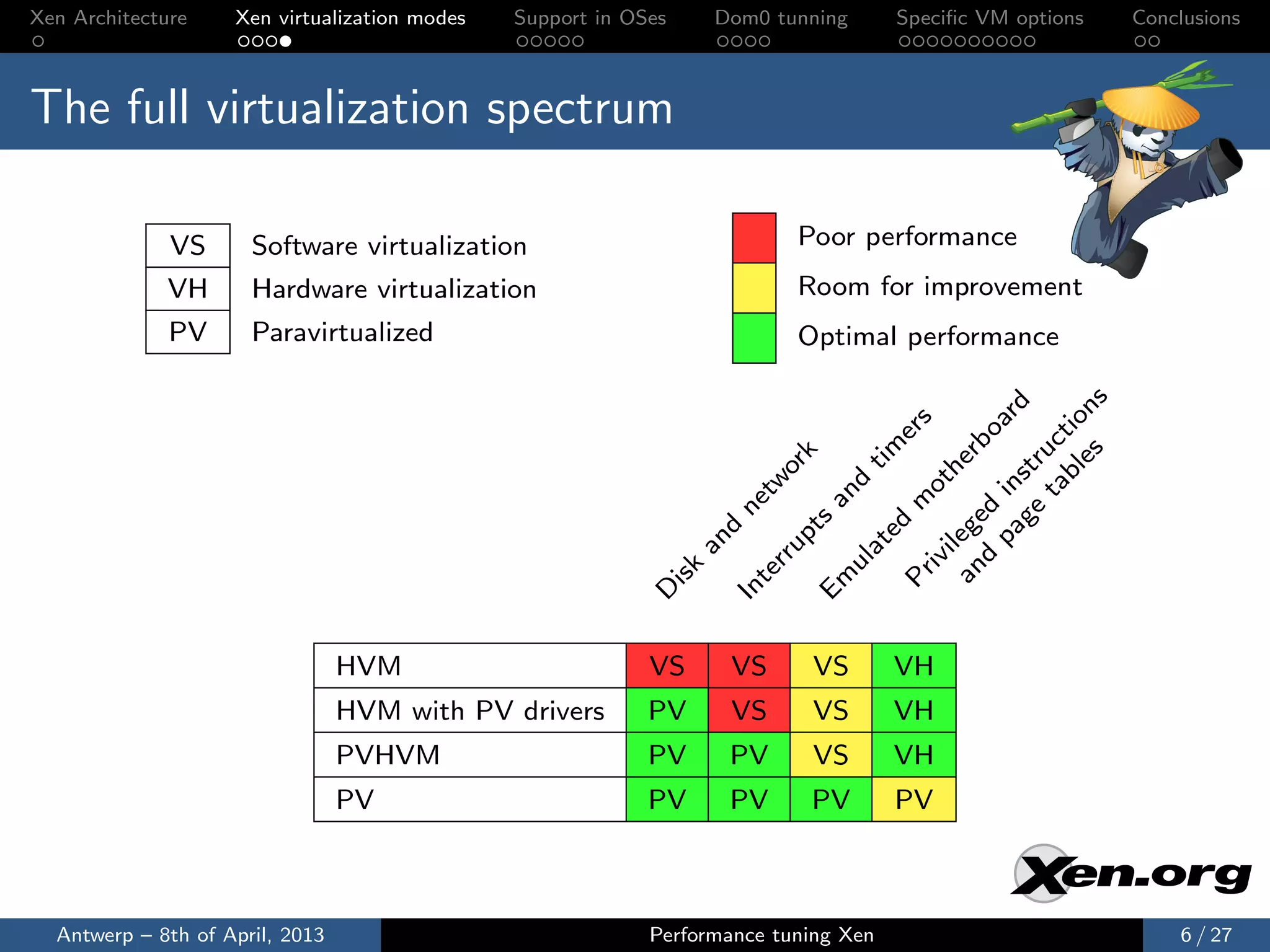
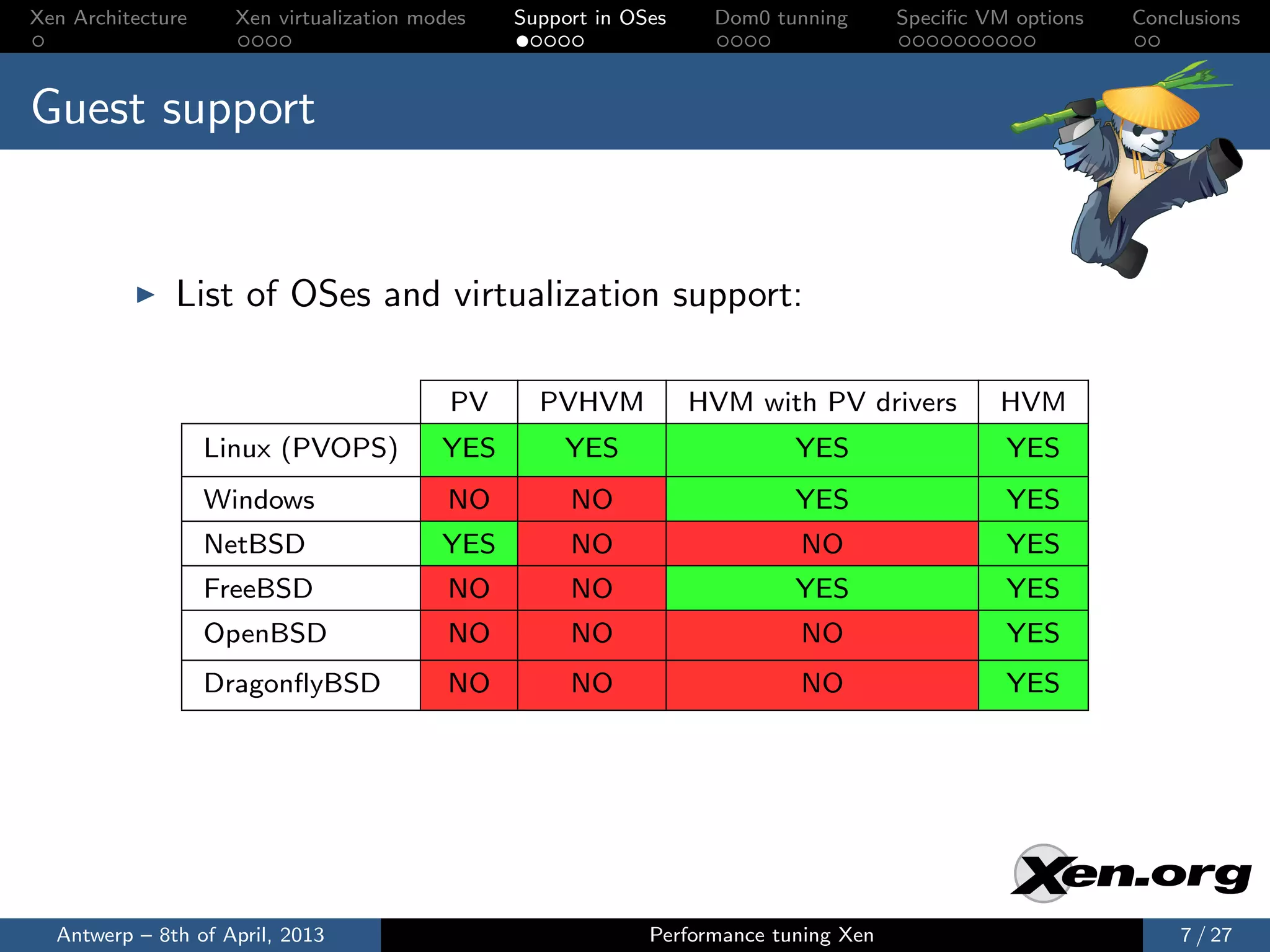
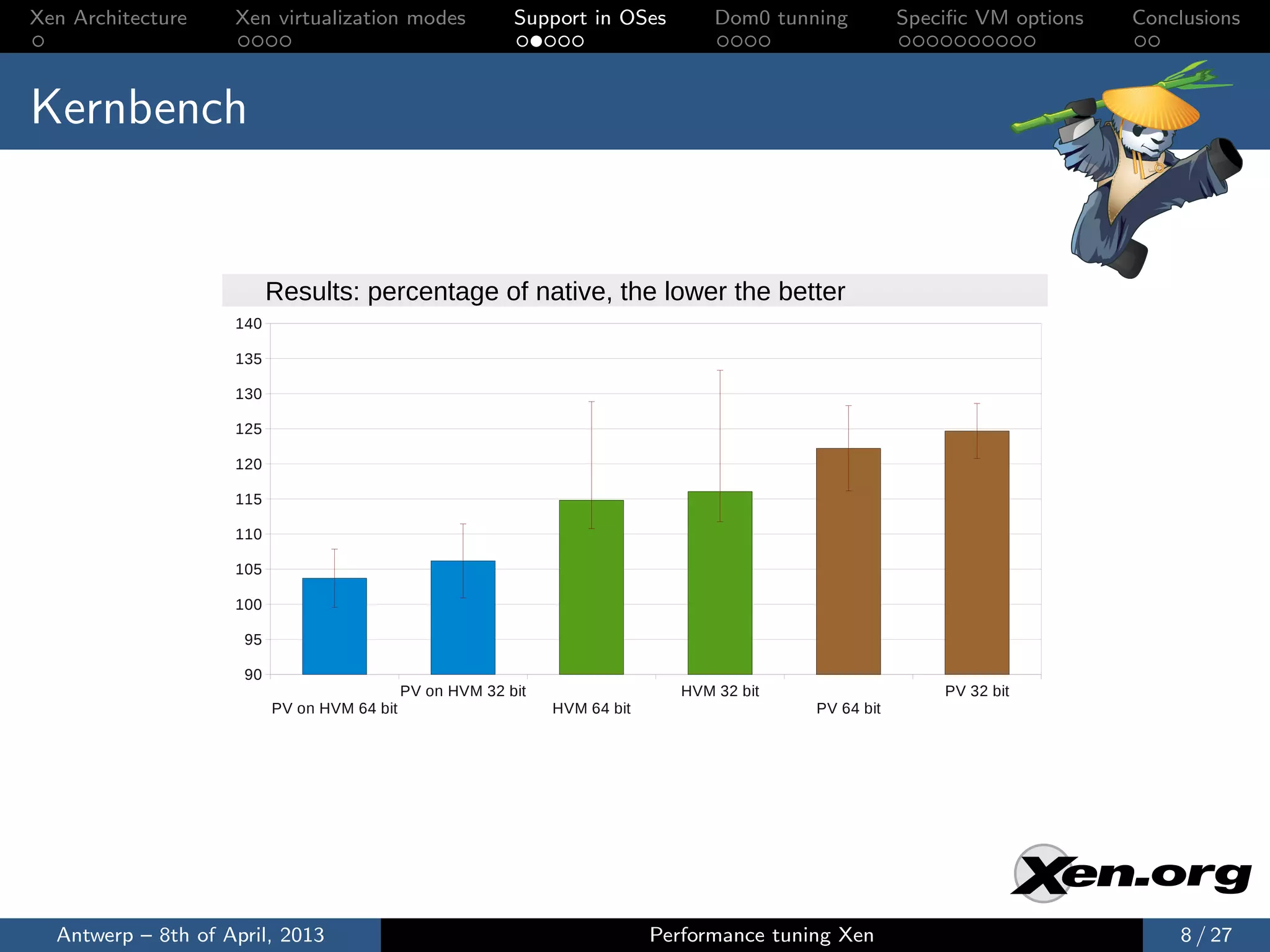
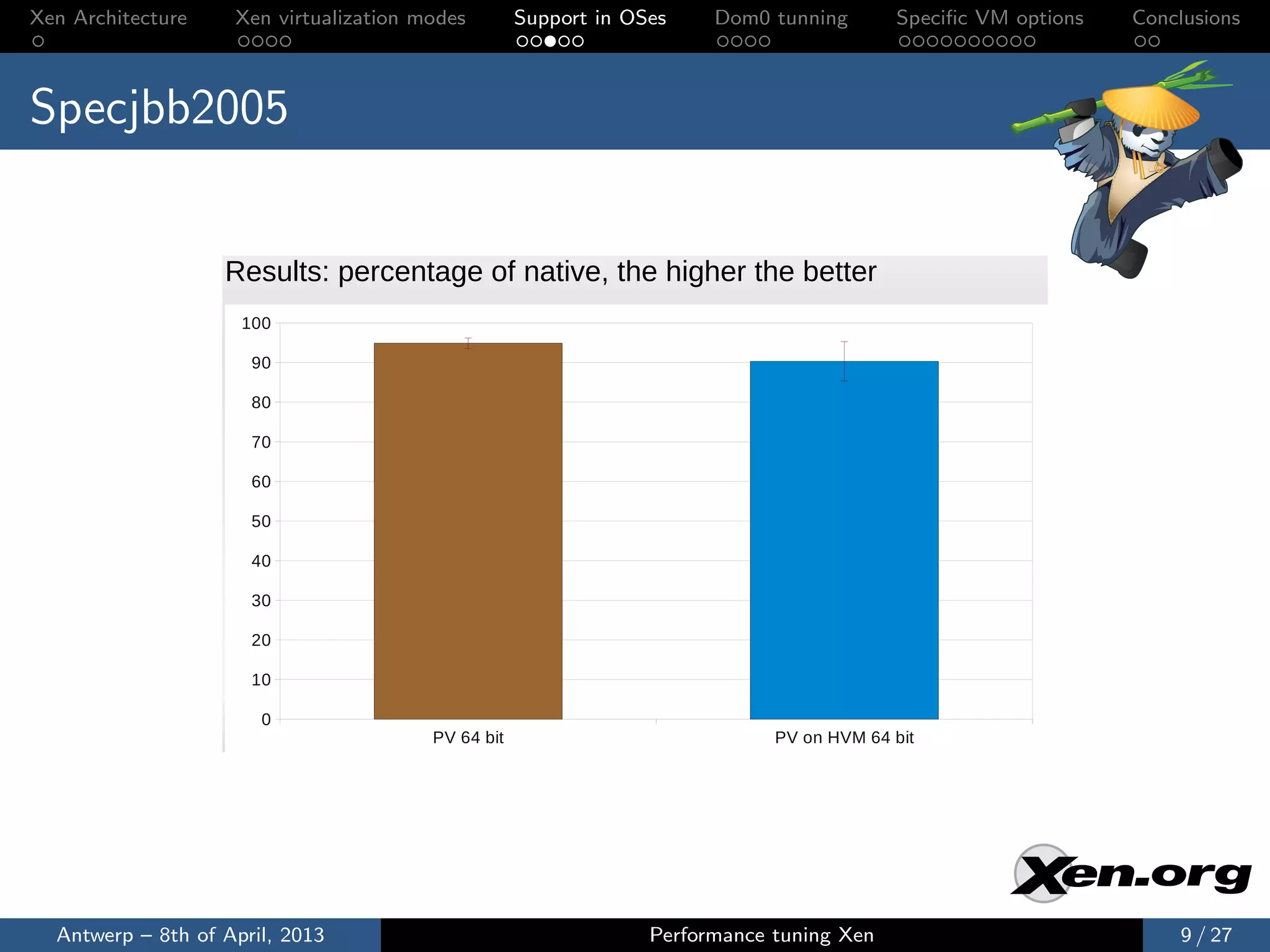
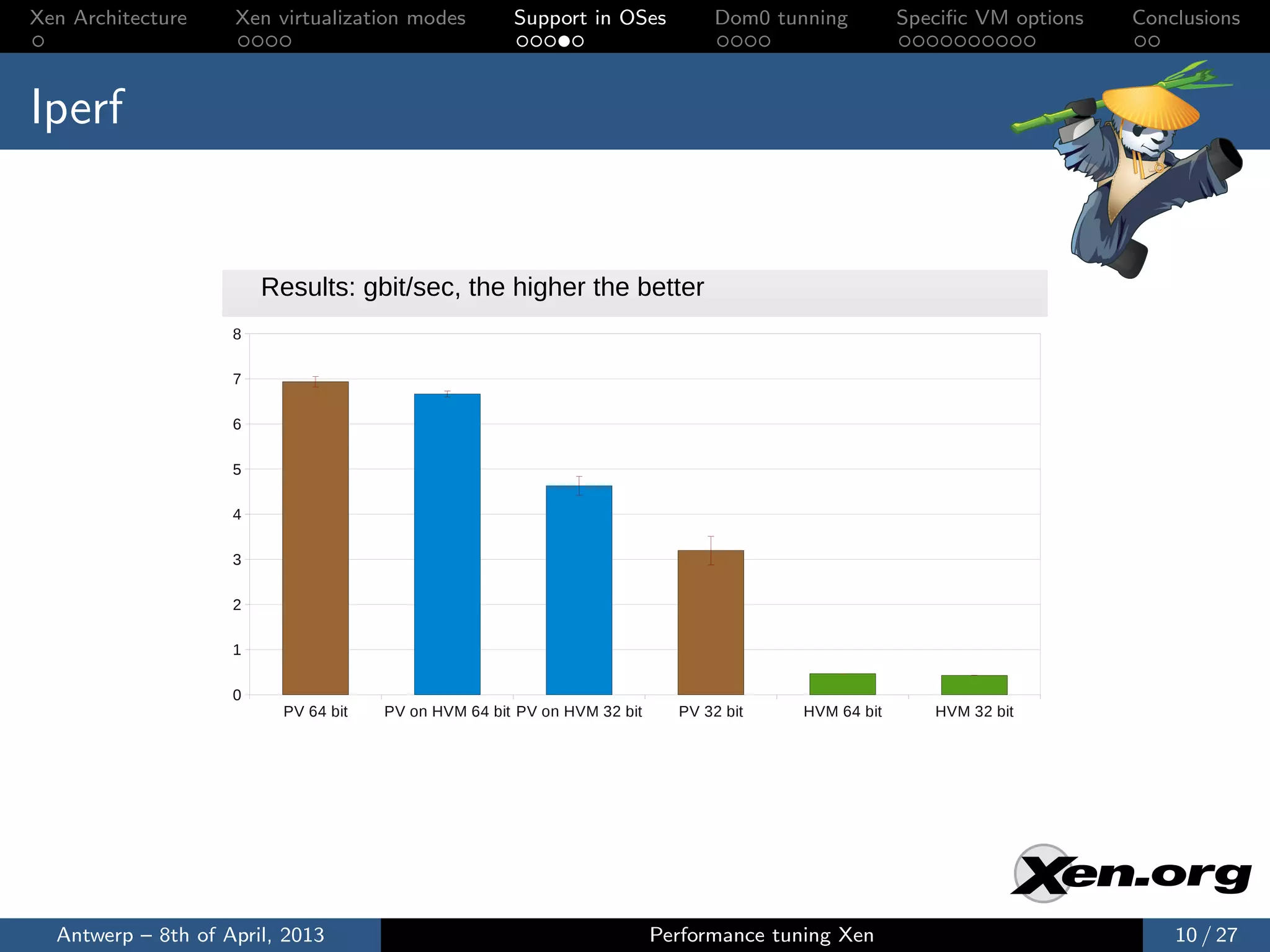
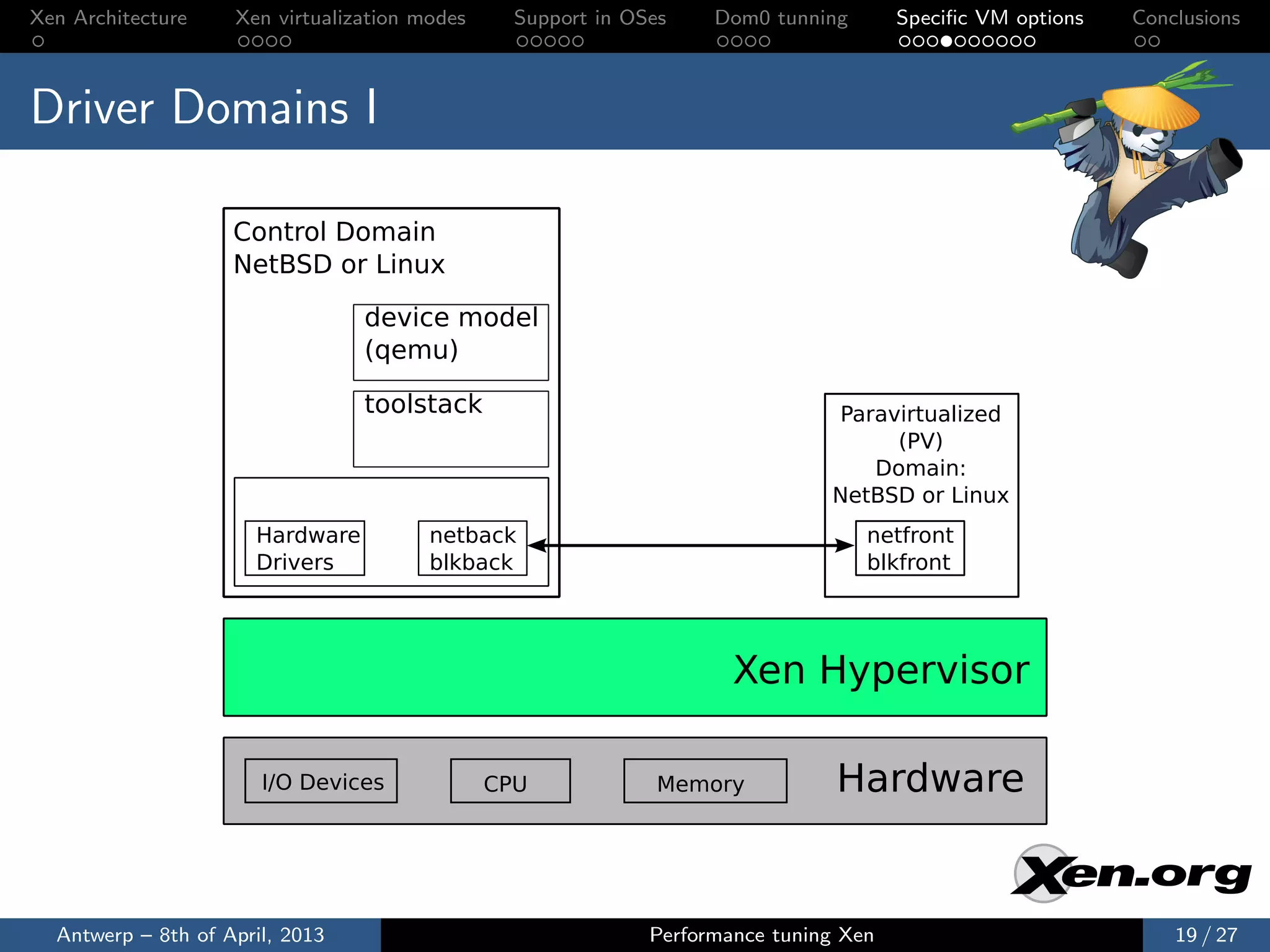
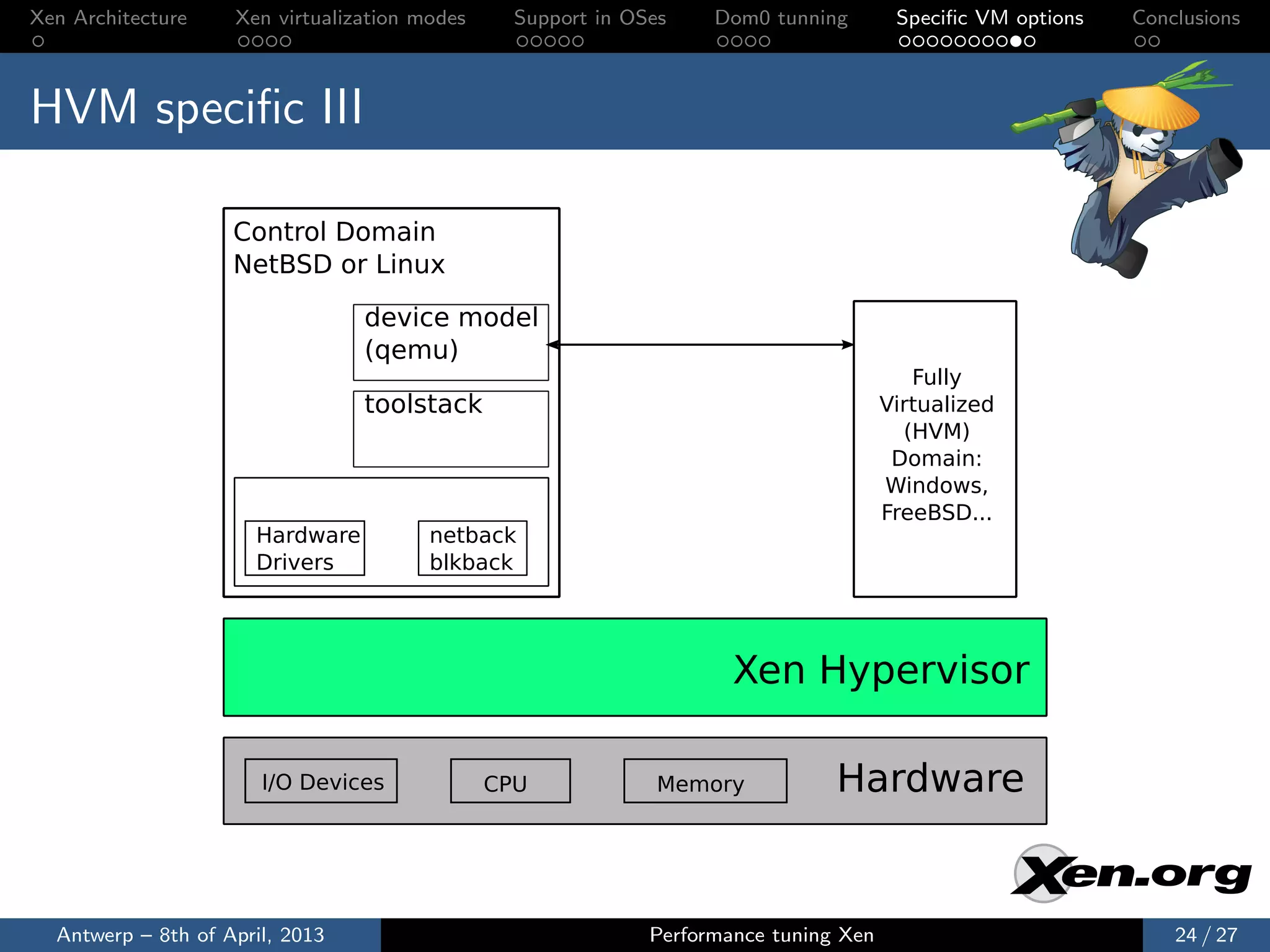
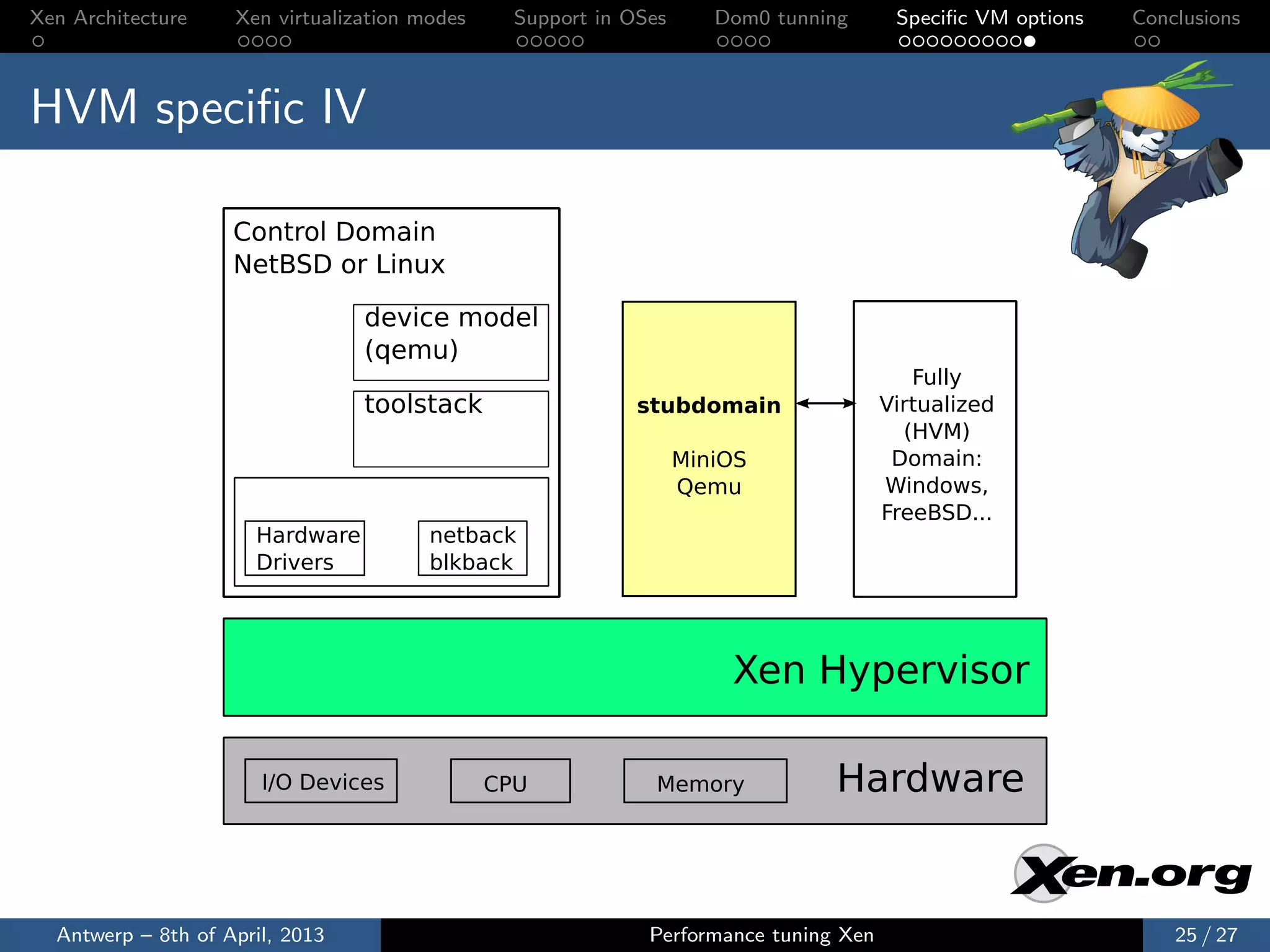
The document discusses performance tuning in Xen virtualization, detailing its architecture, virtualization modes, and the importance of selecting the right mode based on workload. It emphasizes the role of the control domain (dom0) and various performance tuning options for domains, including memory management and CPU pinning. The conclusion highlights the necessity of experimenting with different modes for optimal performance and staying updated on enhancements.