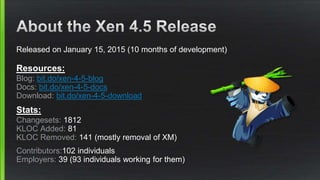
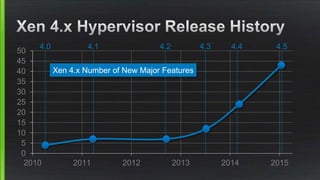
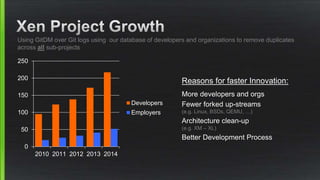
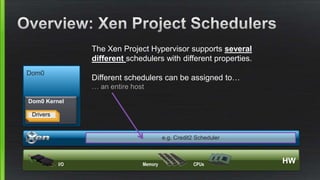
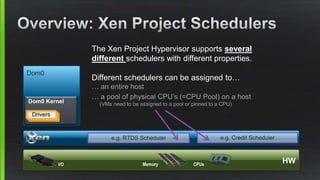
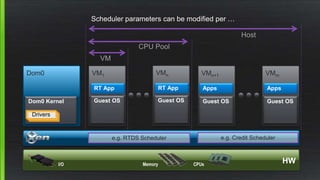
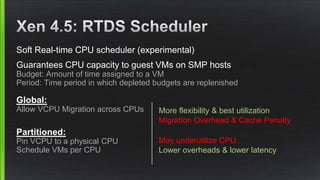
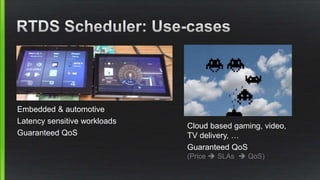
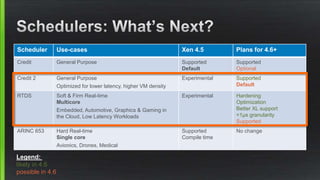
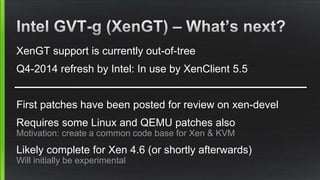
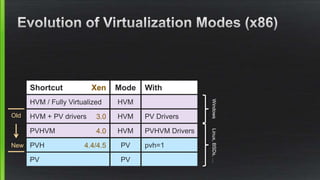
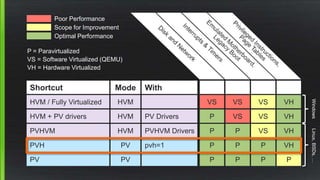
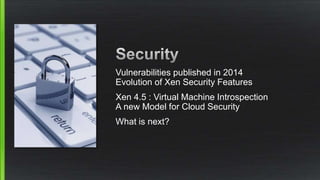
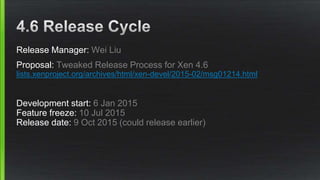
Xen 4.5 was released on January 15, 2015, bringing major updates such as the removal of xend/xm and the introduction of xl as the default interface, improved libvirt integration, and enhanced scheduler capabilities for better performance. The development process saw contributions from 102 individuals, highlighting a significant increase in collaboration and innovation among developers. Future plans include further enhancements for real-time scheduling, virtualization performance, and robust security features as the project proceeds towards its next release, Xen 4.6.