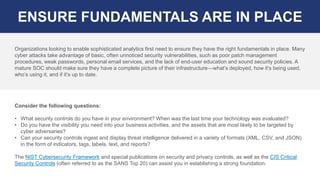
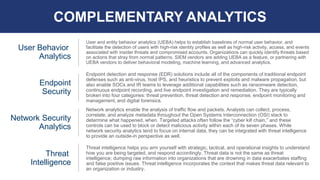
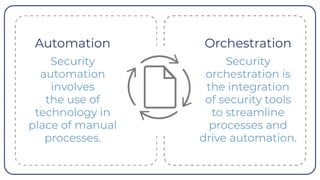
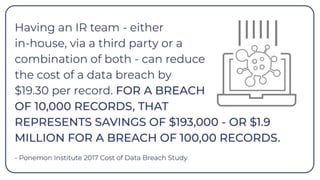
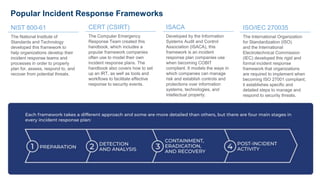
The document discusses the optimization of security operations, highlighting the challenges organizations face due to a shortage of cybersecurity skills and overwhelming alerts. It outlines five keys to improving security operations: evaluating SOC models, implementing advanced analytics, integrating controls and automating processes, boosting incident response, and measuring performance. A well-run Security Operations Center (SOC) is emphasized as crucial for effective cyber defense, with recommendations for frameworks and technologies to enhance incident detection and response.