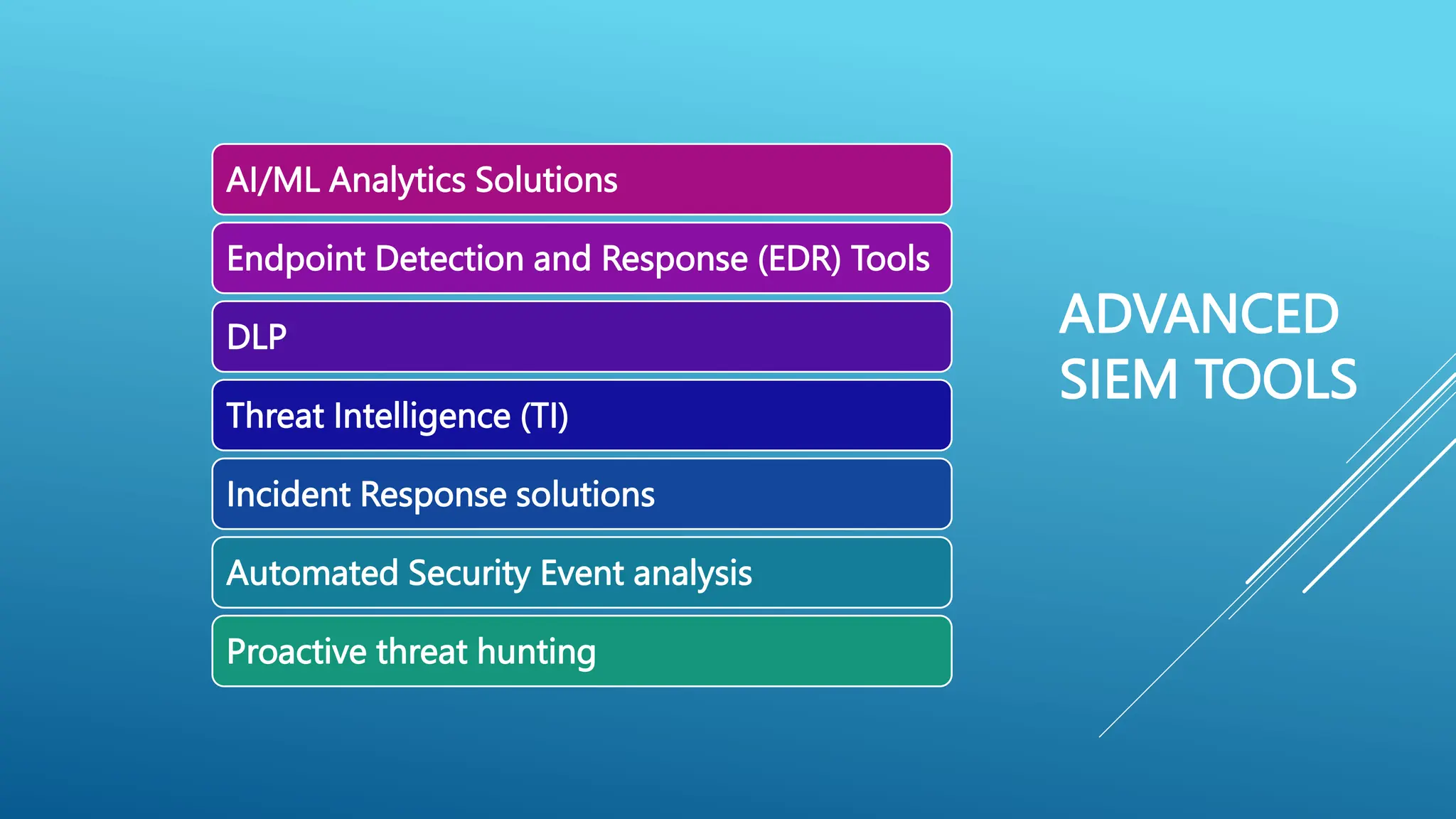
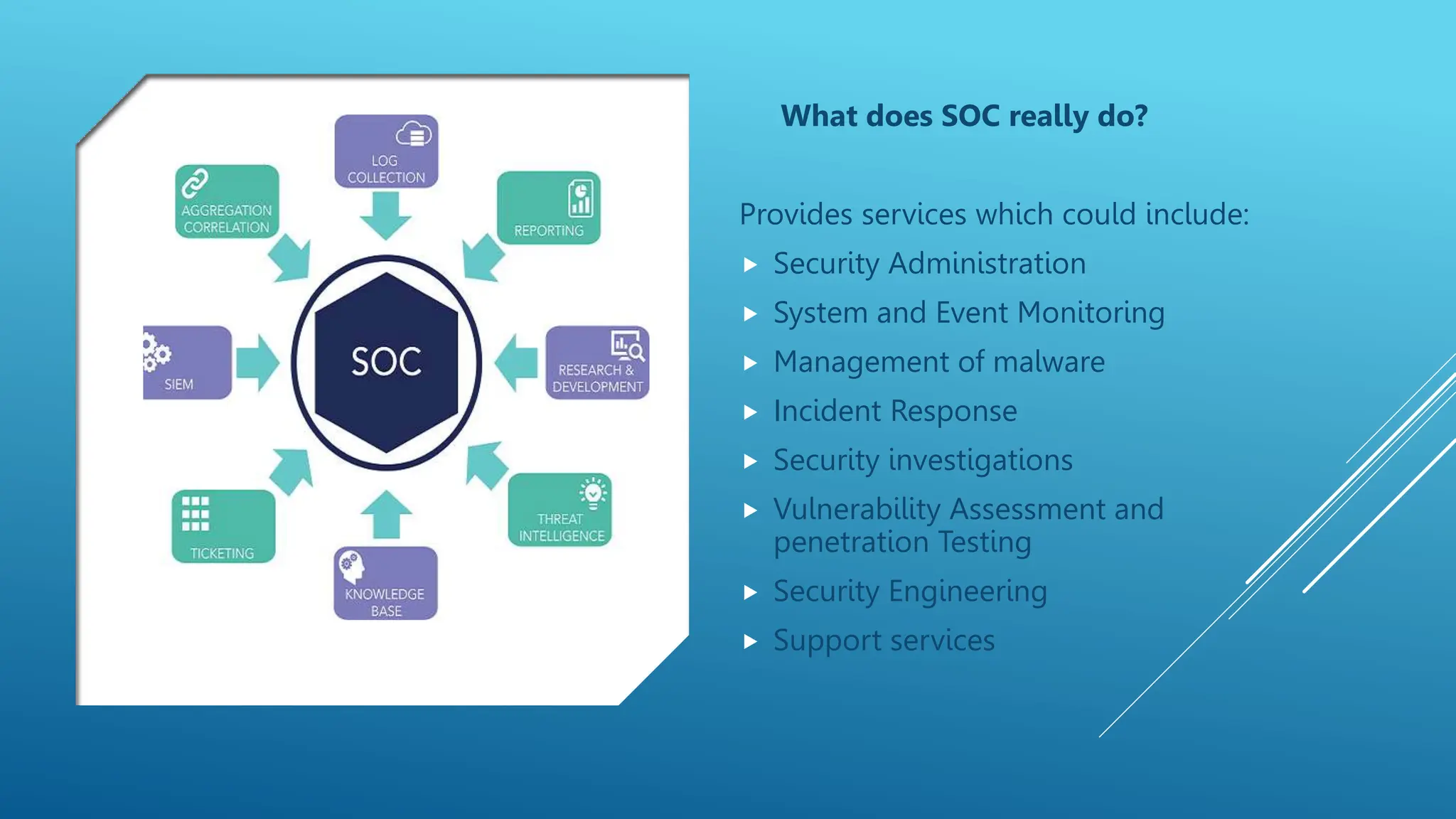
1. Next-gen intelligent SOCs use advanced tools like AI/ML analytics, EDR, and threat intelligence to monitor entire networks including cloud, mobile, IoT devices. This provides more comprehensive security visibility.
2. Key elements of next-gen SOCs include cloud-based analytics for monitoring cloud workloads, managed security services to alleviate staffing pressures, open architectures integrating data from multiple tools, automation/orchestration of security processes, and machine learning for improved threat detection and investigations.
3. Adoption of next-gen SOC technologies is driven by the need to more effectively handle growing data volumes and security alerts, and to address staffing challenges through automation and outsourcing of certain functions.