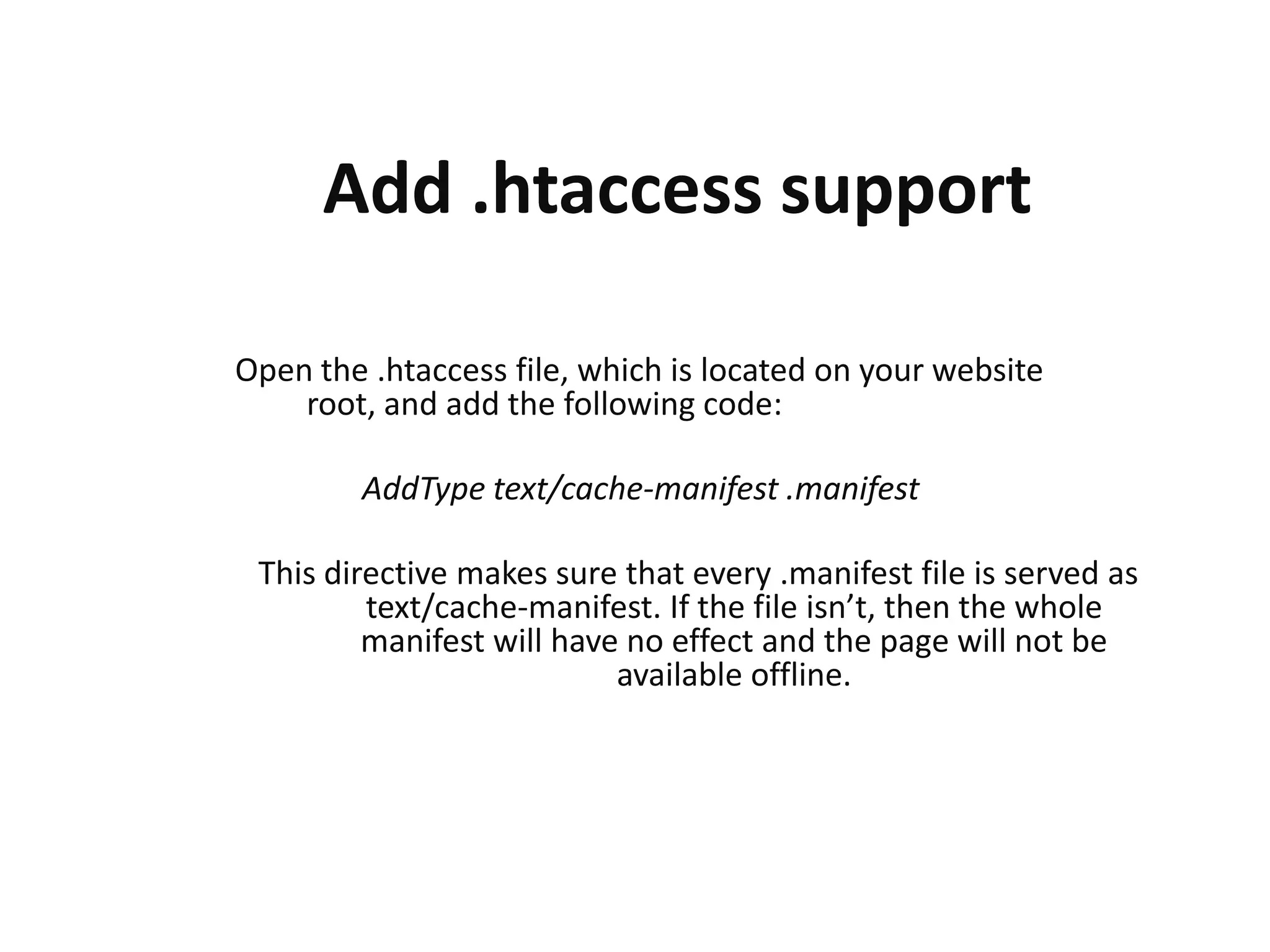
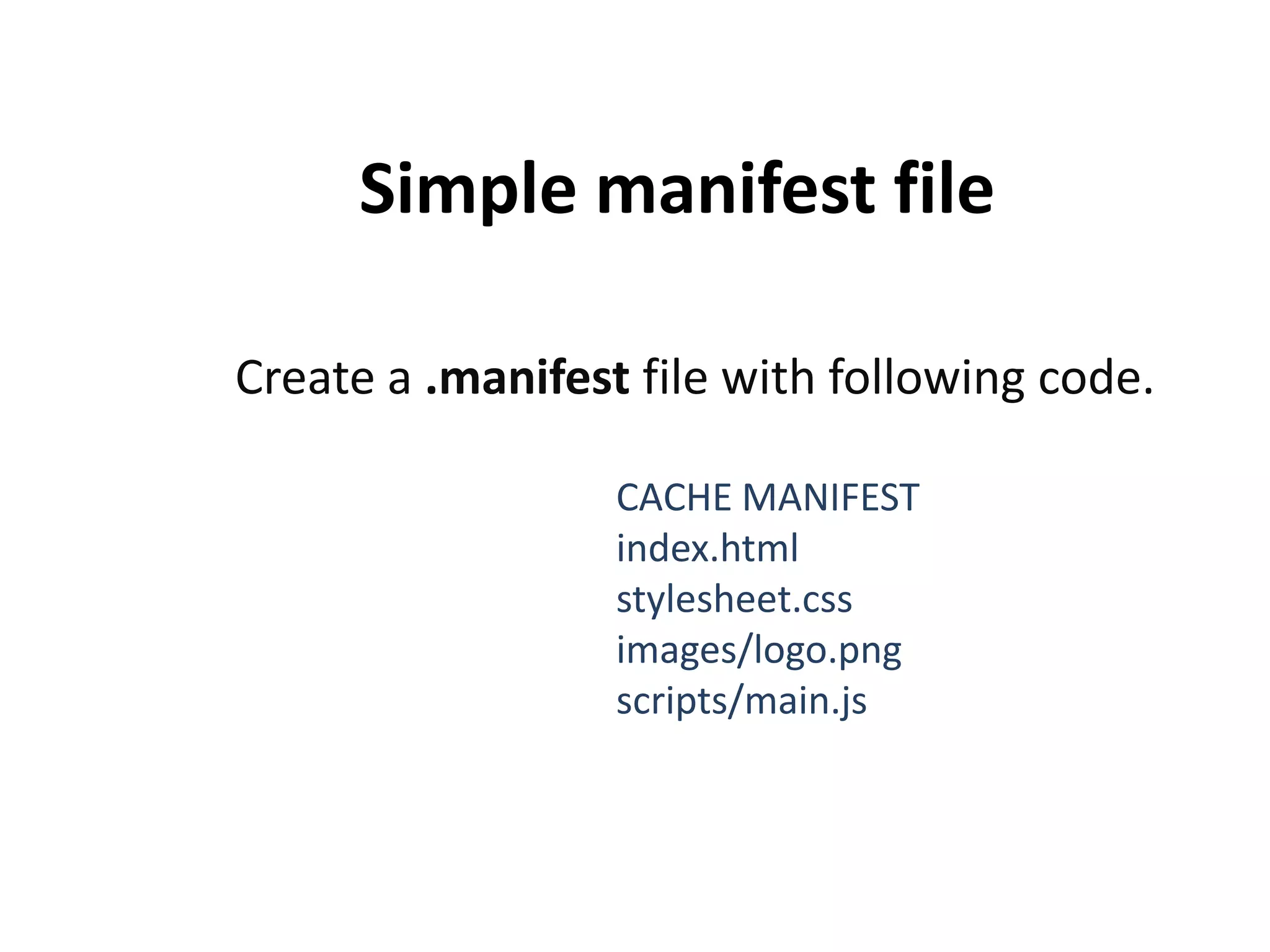
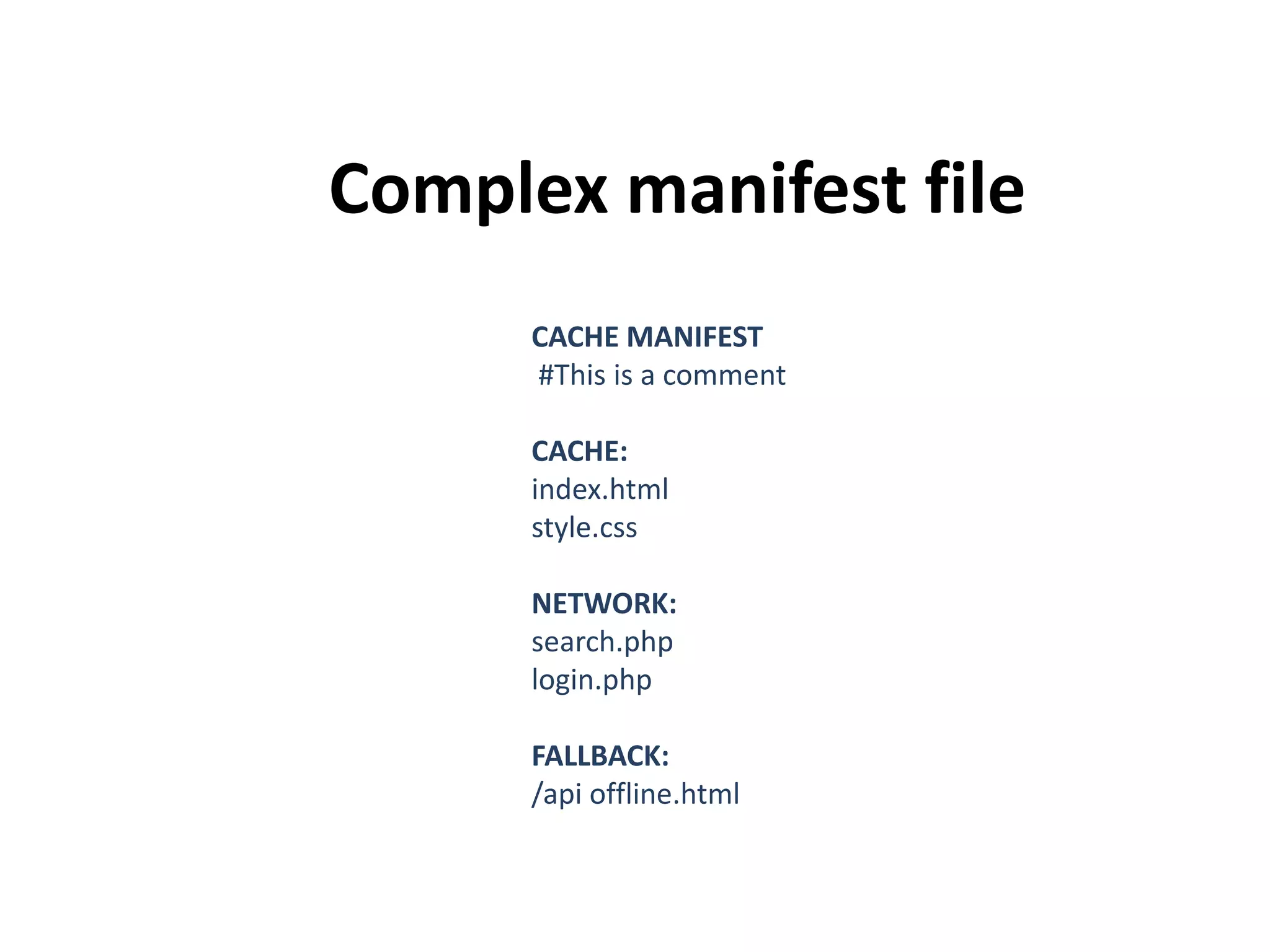
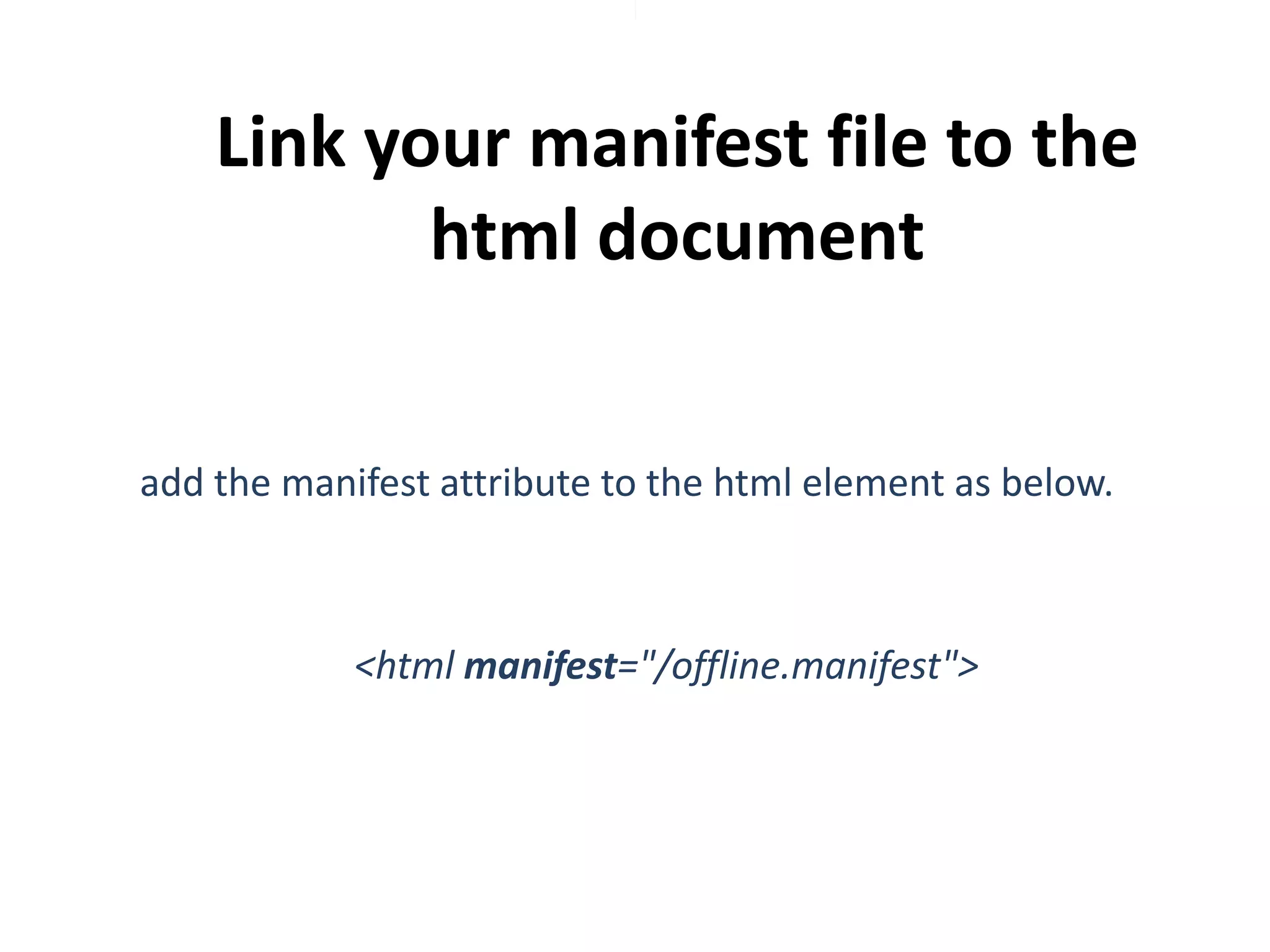
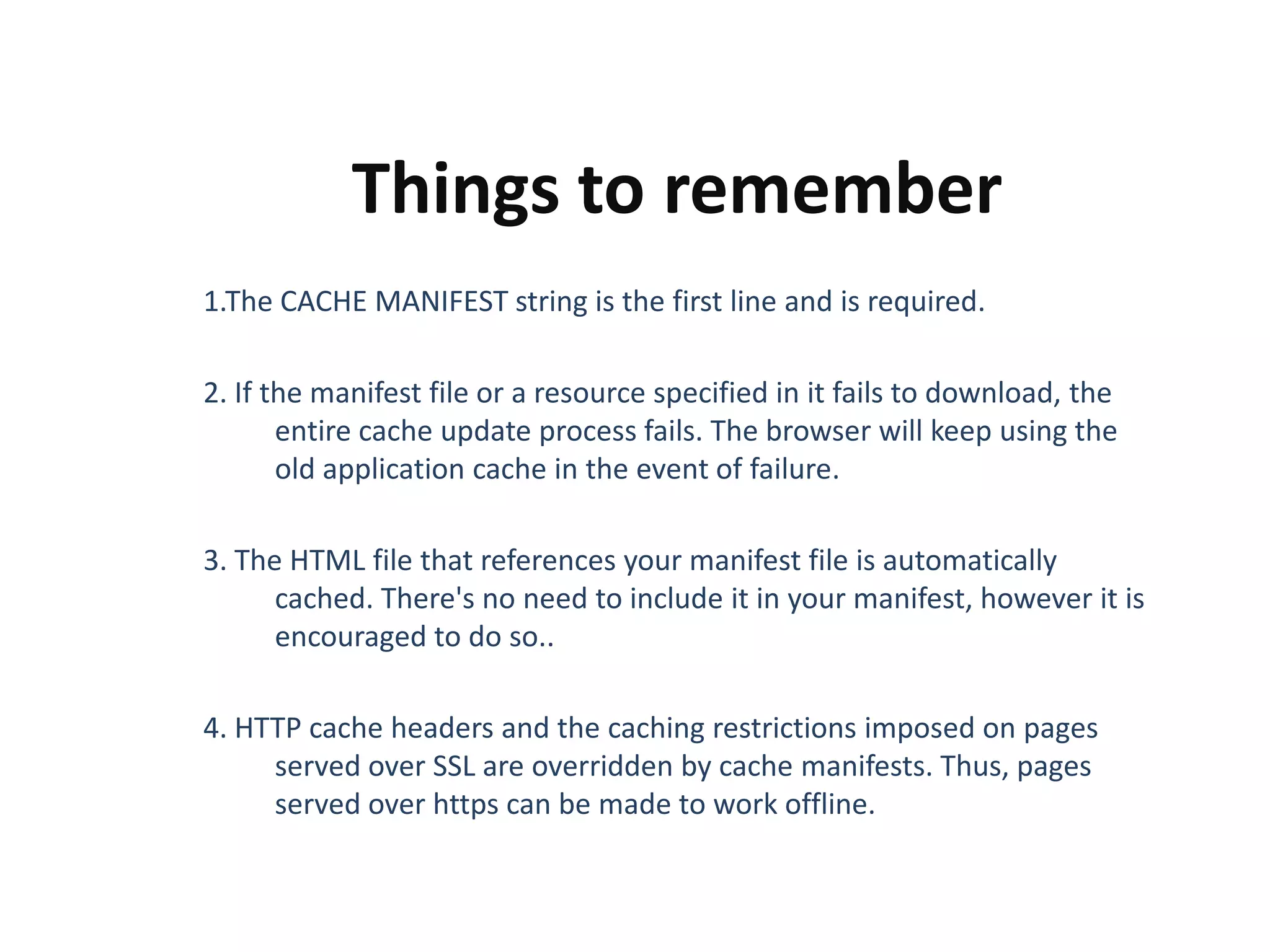
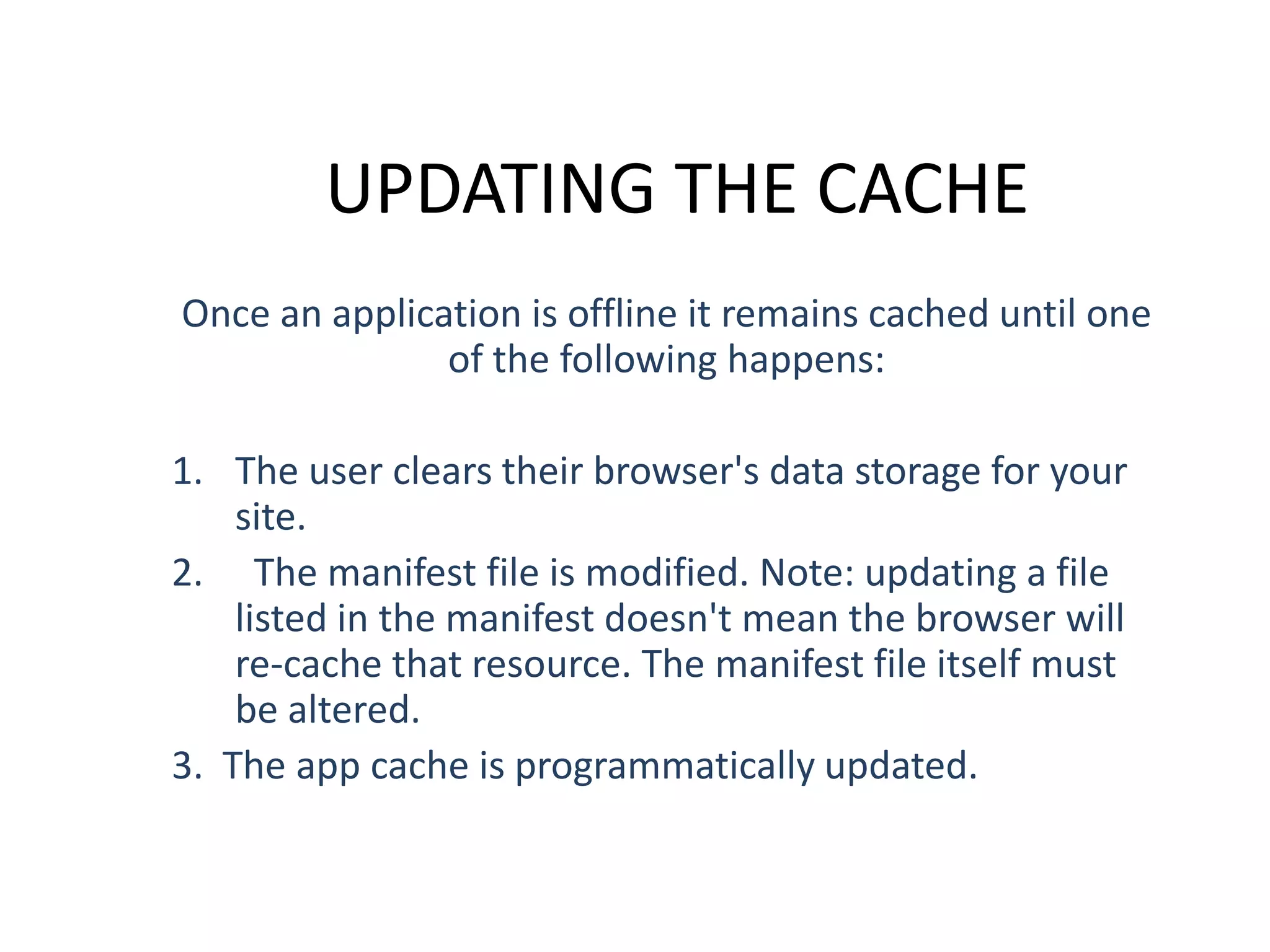
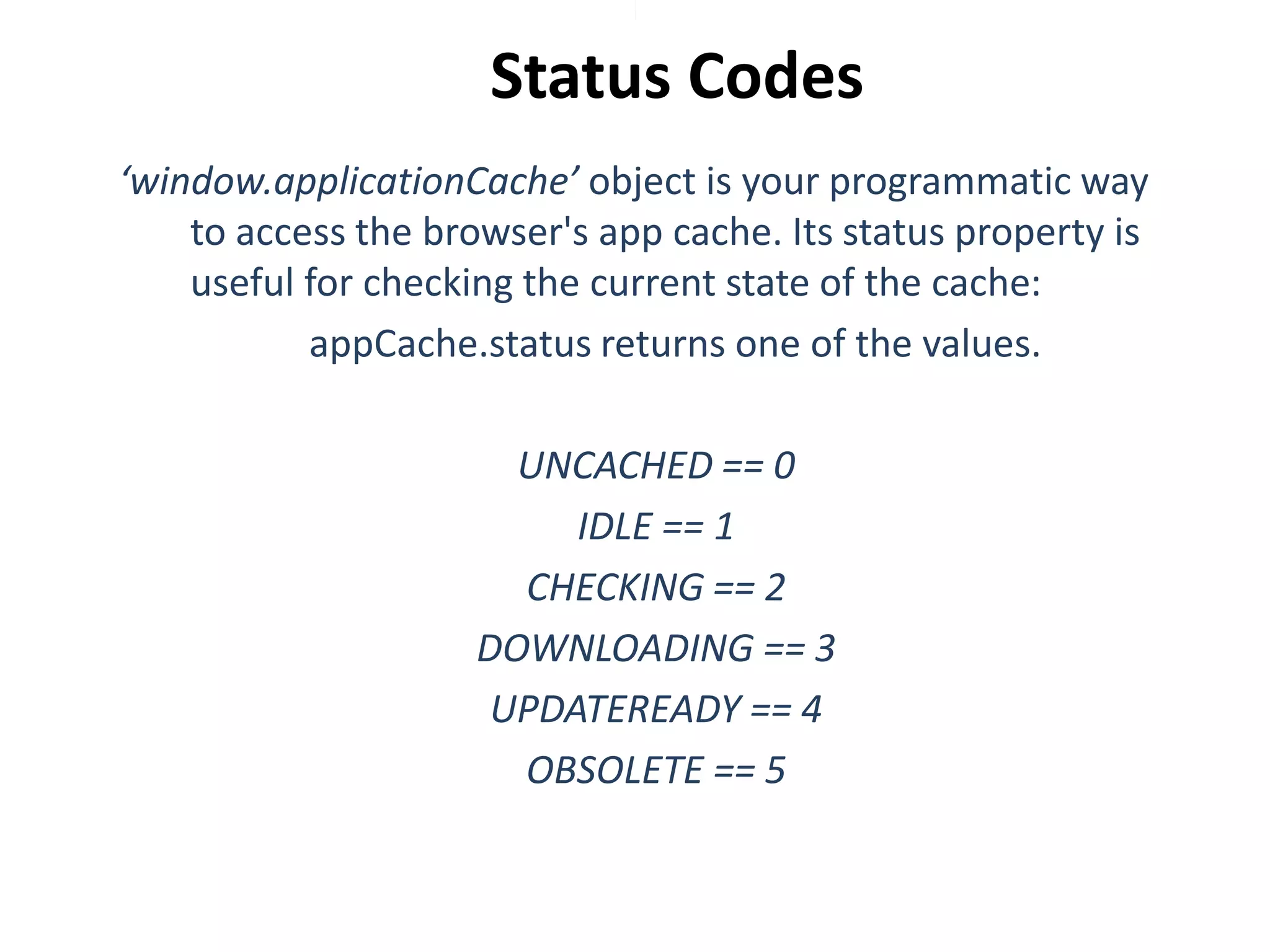
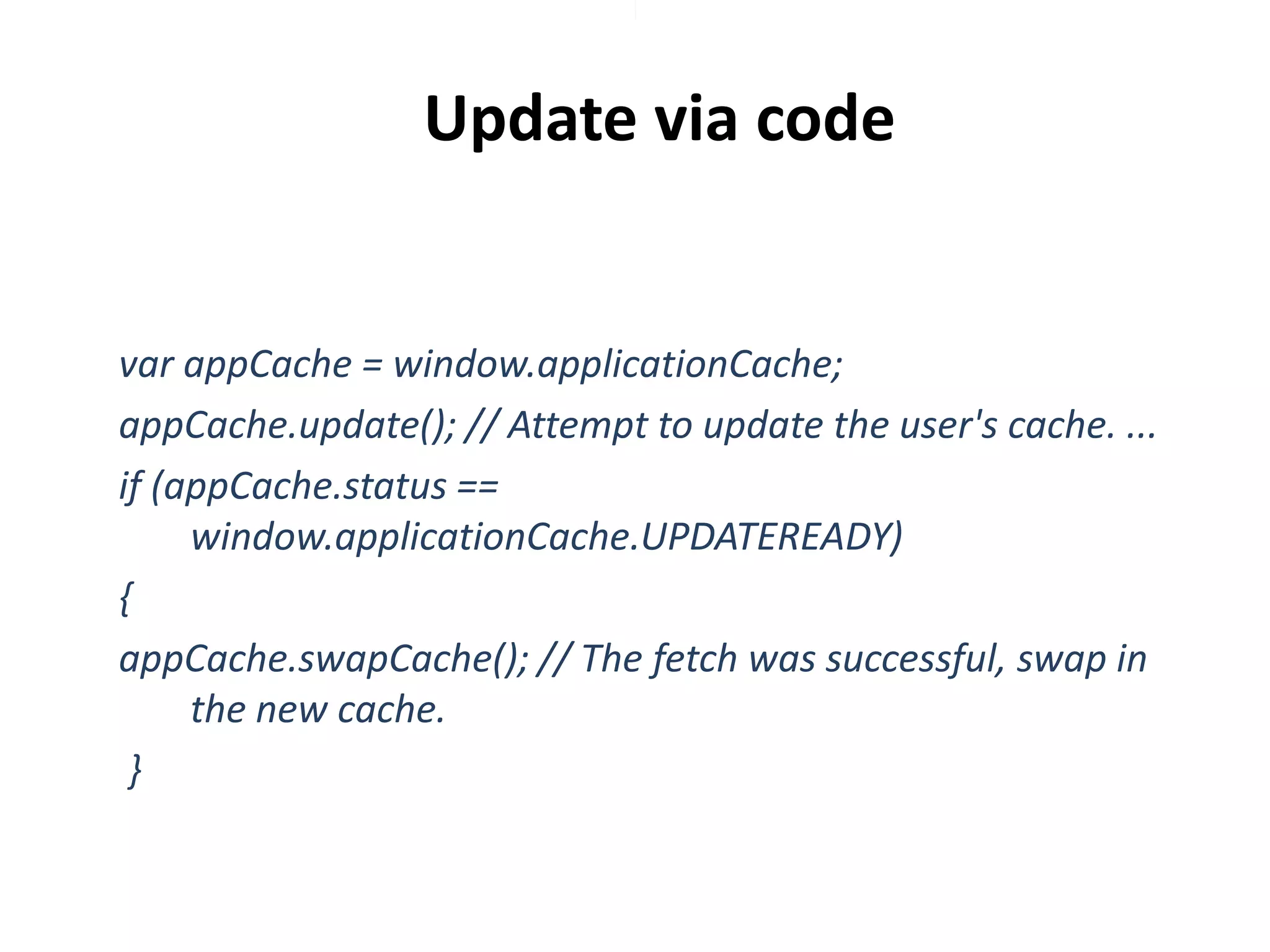
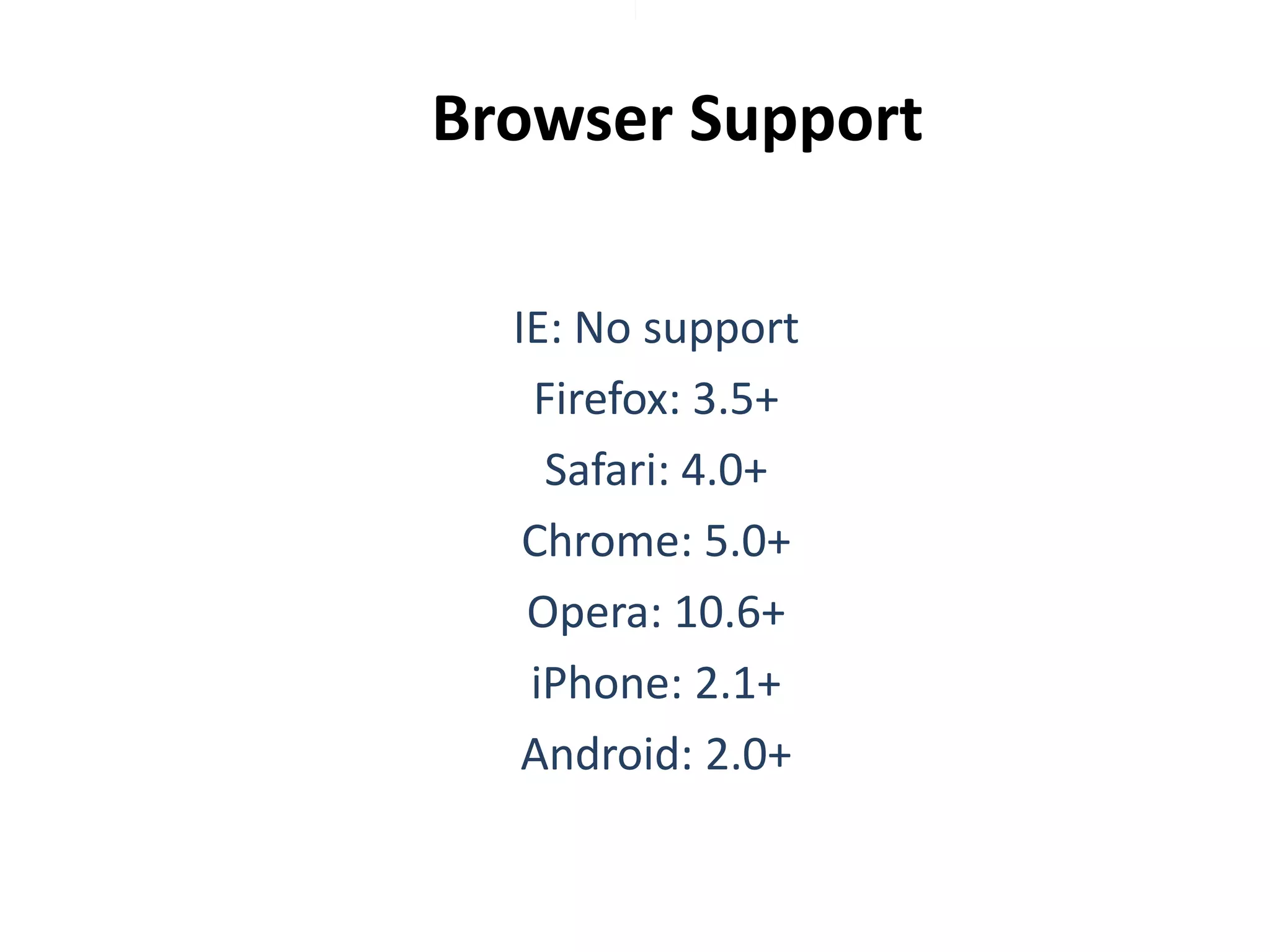
The document describes how to implement offline capabilities in HTML5 web applications using the application cache (appcache) interface, allowing developers to specify which files are cached for offline usage. It outlines steps like adding .htaccess support, creating and linking a manifest file, and important considerations for cache update processes. Additionally, it provides information about browser support and references for further reading.