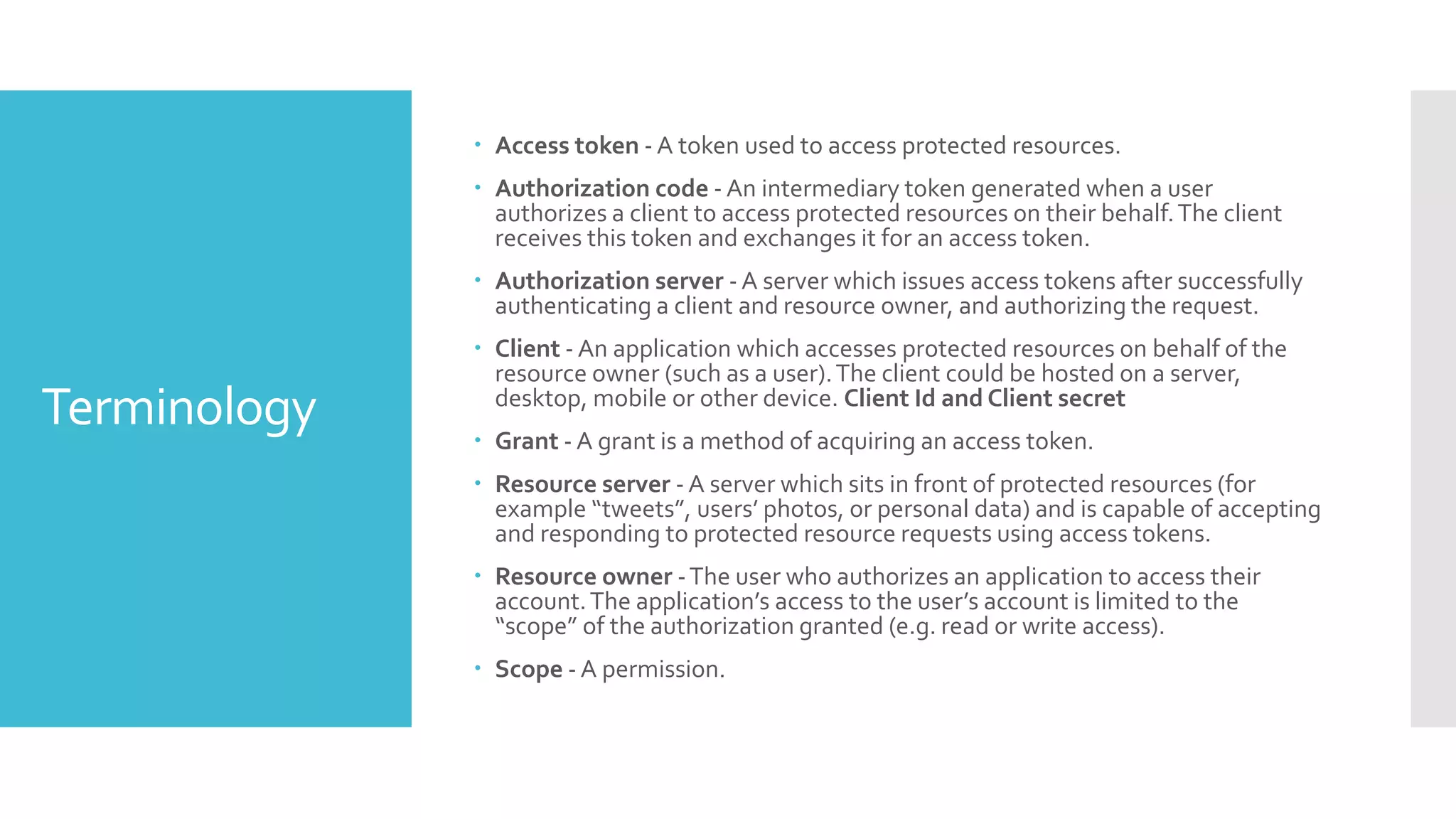
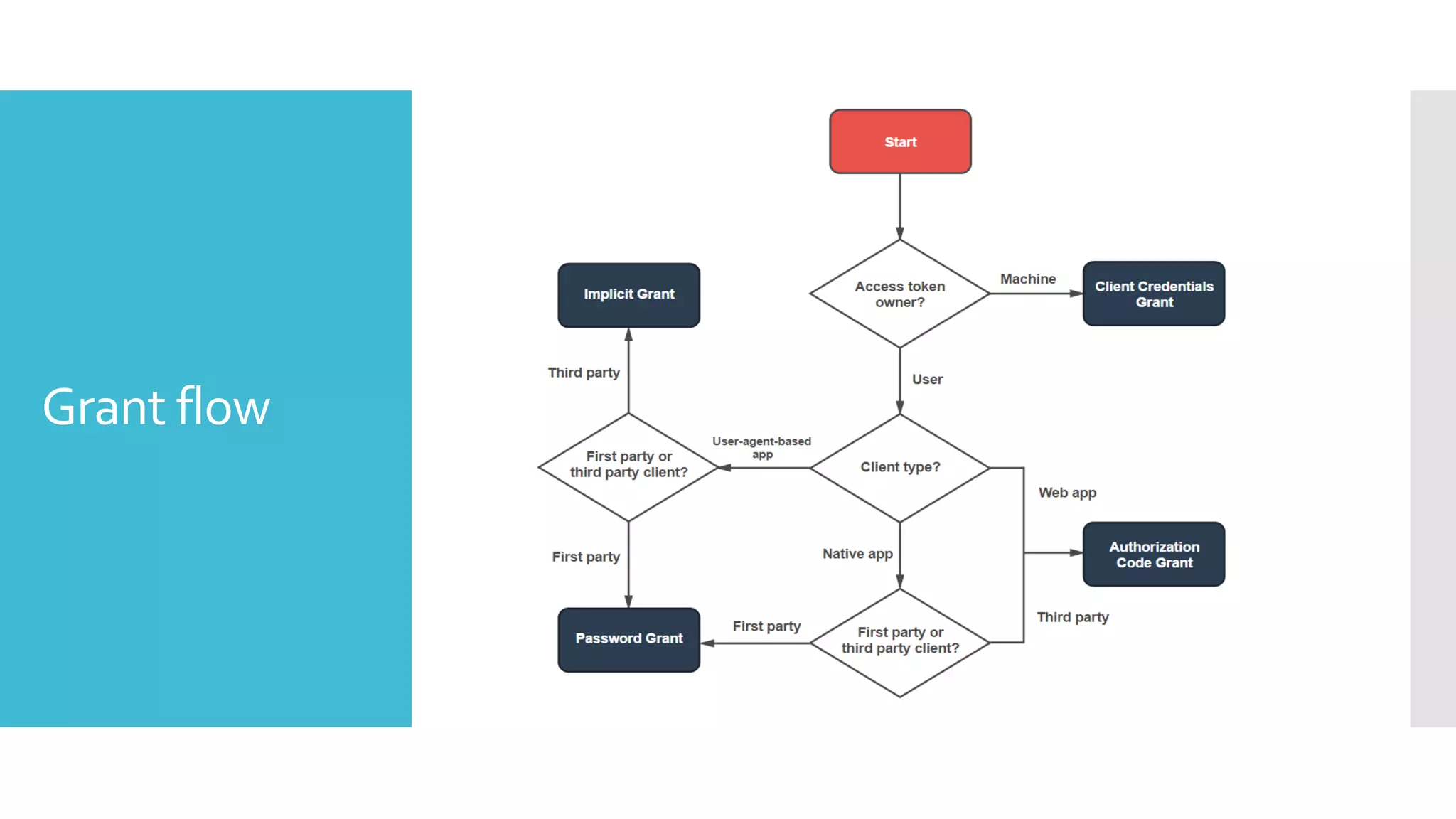
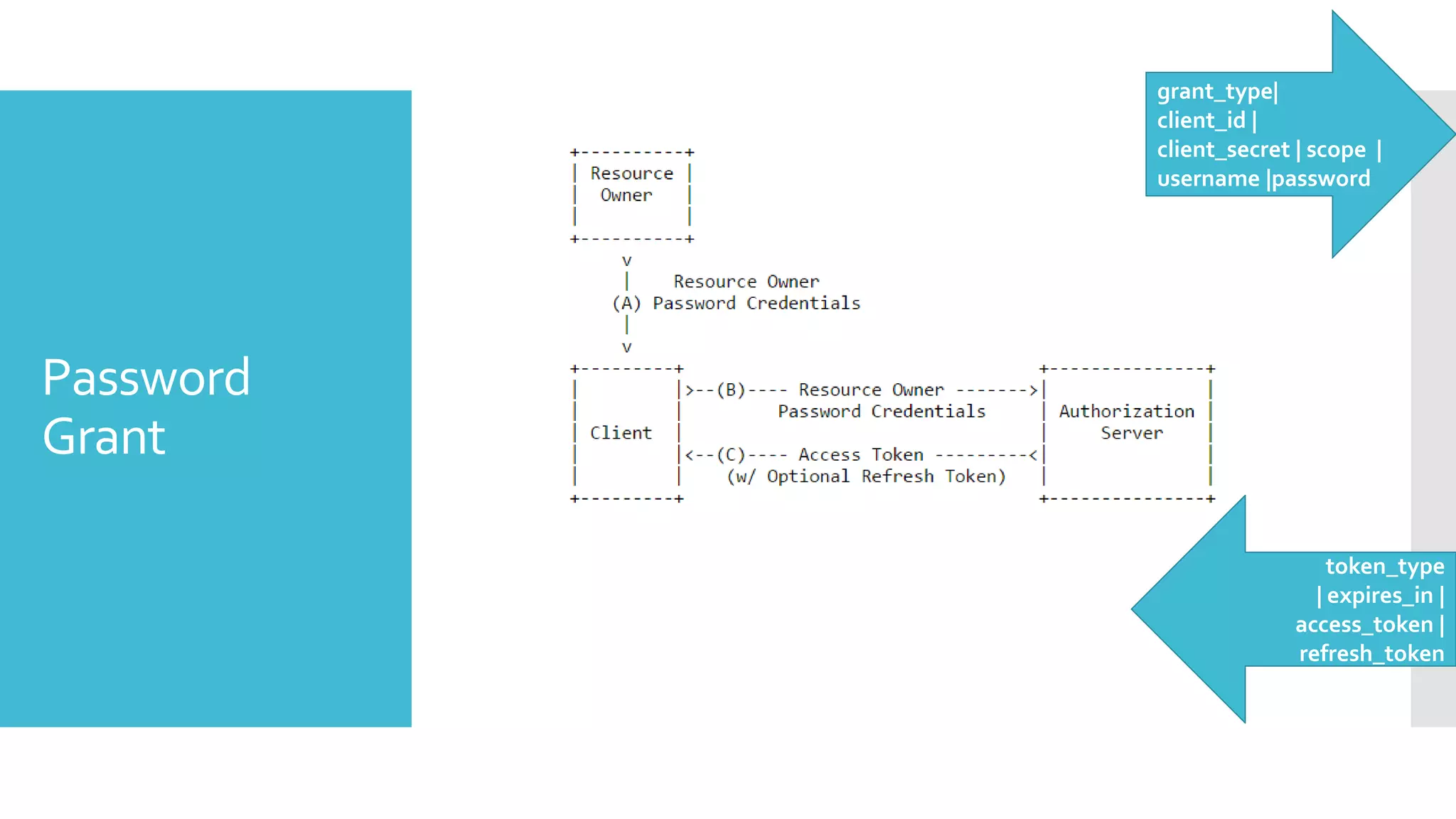
OAuth 2.0 is an authorization framework that allows third-party applications to obtain limited access to a user's data on another service, either on behalf of the user by facilitating an approval interaction or by obtaining access on its own behalf. It addresses the issue of sharing user credentials by introducing an authorization layer and separating the client from the resource owner. The client requests access to resources controlled by the resource owner and hosted by the resource server, and is issued a token rather than the user's credentials.